What Is CSIRT? The Computer Security Incident Response Team Complete Guide

Key takeaways
- A CSIRT (Computer Security Incident Response Team) is a dedicated, cross-functional group responsible for managing the full incident lifecycle — preparation, detection, analysis, containment, eradication, recovery, and post-incident review — to minimize damage and ensure business continuity.
- Effective CSIRT operations require qualified personnel, clear policies and procedures, appropriate tools and technologies (such as SIEM), and seamless collaboration among IT, security, legal, communications, and business stakeholders.
- Ongoing readiness — through regular training, tabletop exercises, real-time monitoring, continuous threat intelligence sharing, and refinement of playbooks — is essential for rapid, coordinated responses to evolving cybersecurity threats.
If you are a fan of superhero movies like me, the assembling of the Avengers or Justice League at a pivotal moment to take on the villains is one exhilarating experience. That the collective strength, rather than individual brilliance, saves the day is a common them in most films of this genre.
The same applies to any organization facing a major cybersecurity incident, such as an enterprise-wide ransomware attack or a massive DDoS attack—teams step in and save the day.
Today’s digital villains are not causing only digital damage. In fact, the individuals, entities, and nation-states that perpetrate cybercrime and instigate cyber insecurity are currently ranked among the top global risks, according to the World Economic Forum. Dealing with such occurrences requires multi-skilled experienced teams that offer the best bet for:
- Minimizing the impact.
- Restoring normality quickly and decisively.
Such a capability that operates at a high level within an enterprise or a government is the Computer Security Incident Response Team (CSIRT). Let’s take a look.
What are CSIRTs or CERTs?
NIST Special Publication 800-61 Revision 2 defines the CSIRT as a capability set up for the purpose of assisting in responding to computer security-related incidents.
Sometimes referred to as CERT (Computer Emergency Response Team), the CSIRT is a service organization responsible for receiving, reviewing and responding to computer security incident reports and activity raised by any user, company, government agency or organization. They provide a reliable and trusted single point of contact for reporting computer security incidents and disseminating important incident-related information.
A country designates national CSIRTs to protect its cybersecurity. A list of national CSIRTs is available.
Before discussing further on how CSIRT works, let's look at the key contributions from experts and global organizations.
Who released the first CSIRT framework?
Forum of Incident Response and Security Teams (FIRST) released the FIRST CSIRT service framework, which is a widely adopted CSIRT operation guideline.
FIRST ensures that response teams are coordinated globally and promotes the best practices for incident management. CSIRT helps companies to develop, standardize, and improvise CSIRT services across governments and industries.
Dedicated leadership, collaboration with cybersecurity professionals, and continuous improvement ensure the success of CSIRT initiatives. A program manager who oversees the development efforts of CSIRT takes care to ensure the success of CSIRT.
Program manager of the CSIRT project
The CSIRT Services Framework Program Manager of FIRST manages the CSIRT project. The program manager is responsible for refining the CSIRT guidelines, overseeing the development, and ensuring that the framework aligns with evolving cyber threats. To enhance the effectiveness of CSIRT, the program manager collaborates with policymakers, international security teams, and industry leaders.
(Understand the relationship between vulnerabilities, threats and risk.)
How the CSIRT works: 4 phases of incident response lifecycle
The CSIRT is primarily involved in the four phases of the incident response lifecycle, and we’ll look at each phase:
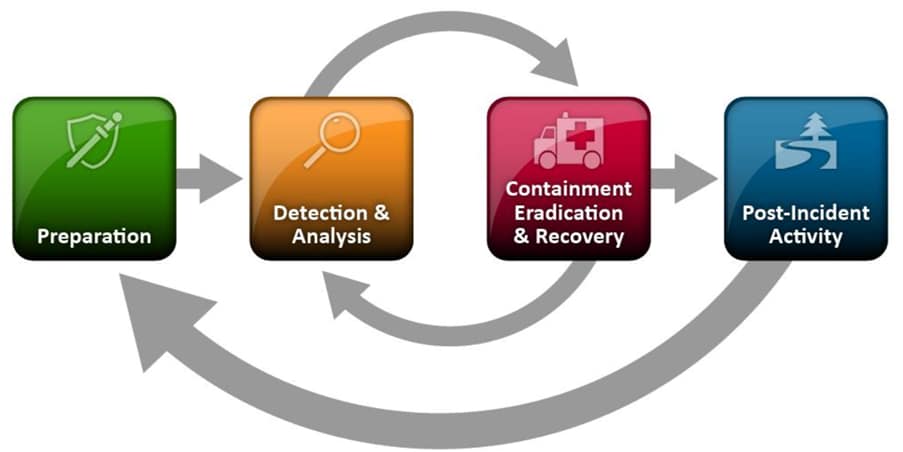
The Incident Response Lifecycle per NIST (Image source)
1. Preparing for the incident
The CSIRT would be governed through an appropriate cyber security policy framework which includes topic specific policies covering the rest of the incident management process. A mission statement for the CSIRT would provide direction in terms of:
- The constituency (body of people) the team serves.
- The authority or directive under which the team operates.
Appropriate tools and resources for handling incidents need to be prepared which includes (but not limited to):
- Communication facilities, such as phones, email, chat, social media, etc.
- Physical facilities, such as a dedicated war room
- Hardware and software including digital forensics workstations and software, secure storage devices, packet sniffers, protocol analyzers, clean OS images and software.
2. Detecting & analyzing the incident
Detection of incidents would take place through many sources. Primarily, the CSIRT would have access to IDS/IPS, anti-malware and log analysis tools that can identify sources of cyberattacks. Information from users, other CERT teams, and technology vendors also enhances detection efforts.
Analysis of the incident involves different techniques depending on the type of attack. The CSIRT analyzes the incident to determine three things:
- The scope: which users, systems and services are being impacted)
- The origin: who or what caused the incident
- The occurrence: which attack methods are being used or vulnerabilities exploited
Next, the CSIT team documents and communications the output of the analysis to key stakeholders. This facilitates prioritization and planning for the next course of action.
3. Containing, eradicating, & recovering from the incident
Containment approaches vary depending on the type of security incident. The right decision needs to be taken to limit the impact, which might include:
- Isolating or shutting down affected systems
- Diverting traffic away from them
This decision also affects evidence collection, which may be necessary for legal, regulatory, or research purposes. Teams must document evidence properly, store it securely, and maintain a formal chain of custody.
After containment, teams eradicate the incident source from IT systems using various techniques, including:
- Deleting malicious files
- Disabling breached accounts
- Scrubbing impacted devices
- Patching to mitigate the exploited vulnerabilities
Recovery actions can take place after containment and in parallel with eradication. They would include reviving affected systems, restoring data from backups or failing over to disaster recovery sites. Automation of containment, eradication and recovery can reduce the time of incident impact, but care must be taken in evidence handling.
4. Recovering post-incident recovery
Once things are back to normal, it is crucial that the CSIRT members review the incident event and handling, together with stakeholders. CSIRT team members should document and share lessons learned in order to:
- Quicken future responses.
- Enhance existing security controls.
In addition, metrics related to response time and impact containment should be reported to support improvement initiatives. In fact, the CSIRT might be required to collaborate with law enforcement agencies in tracing sources of attacks, analyzing evidence, as well as providing testimony during legal proceedings.
Deciding how to build a CSIRT: 5 models
When determining the operating model of the CSIRT, you’ll need to consider certain factors including the sourcing approach (internal vs external) and the location (centralized vs distributed). The Carnegie Mellon University Software Engineering Institute (CMU SEI) lists five generic organizational models for a CSIRT:
- Security team
- Internal Distributed CSIRT
- Internal Centralized CSIRT
- Internal Combined Distributed & Centralized CSIRT
- Coordinating CSIRT
Let’s look at each model.
1. Security team
Here, no group or section of the organization has been given the formal responsibility for all incident-handling activities. Instead, you’re likely to follow an ad hoc approach to constituting a team of IT personnel to tackle a security incident. The team reports to internal stakeholders within the organization.
(Compare a SOC to a network operations center.)
2. Internal Distributed CSIRT
This model consists of a formally chartered “virtual” distributed CSIRT responsible for handling incident response activities. The organization utilizes existing staff to constitute this team, who may carry out CSIRT activities, in addition to their other regular job roles. This CSIRT coordinates with both internal and external stakeholders.
3. Internal Centralized CSIRT
This model includes a team fully dedicated to CSIRT activities, operating from a central location within the organization. They are the single point of contact for incident handling, coordinating with all stakeholders.
4. Internal Combined Distributed and Centralized CSIRT
This model combines the previous two models and maximizes the utilization of distributed staff to provide context for the centralized unit when tackling incidents across a widely distributed organization.
5. Coordinating CSIRT
This model involves a CSIRT that coordinates and facilitates incident handling across a variety of organizations, including other CSIRTs. Coordinating CSIRTs usually have a much broader scope with a more diverse constituency but with little or no authority. Hence, their focus is more on coordinating communication and providing guidance.
Advanced skills for CSIRT teams
CSIRTs will differ in how they operate depending on the available staff, expertise, budget resources, and unique circumstances of each organization. Whatever the model, CSIRT members require advanced skills that may not be available to the usual information security teams within an organization.
These advanced skills include:
Incident handling and service management
For effective incident handling, team members must be well-versed in SLAs, ITIL frameworks, and structured response strategies. The team must manage problems and security breaches swiftly to minimize disruptions.
Handling the situation systematically with efficient service management will ensure rapid resolution, thus reducing business impact and strengthening the company's resilience against cyber threats.
Security knowledge and technical expertise
Teams should have in-depth knowledge of infrastructure, operating systems, and applications. Team members should have expertise in ethical hacking, cloud security, and log analysis to identify anomalies.
Threat intelligence
The key to proactive defense is understanding the tactics of the attacker. CSIRT teams should be able to use frameworks like MITRE ATT&CK to analyze cyber threat intelligence.
They should be able to anticipate and counteract sophisticated cyber-attacks by:
- Tracking emerging threats
- Recognizing attack patterns
- Sharing threat intelligence with industry peers
Digital forensics
Teams must dissect and analyze the behavior of malware. To develop countermeasures, they should perform reverse engineering and digital forensic techniques, which include disk analysis and memory forensics. These skills are important to trace threats and mitigate future risks.
(Related reading: digital forensics incident response).
Automation
Teams should be proficient in PowerShell, Python, or similar scripting languages to automate tasks. They can use security orchestration tools to integrate incident response workflows, threat intelligence, and real-time monitoring. This will reduce manual workload by streamlining incident detection and response protocols.
(Related reading: automated incident response.)
Communication and coordination
Clear communication with stakeholders, which may include regulators, legal teams, or executives, ensures effective incident management. The team must prepare reports by documenting security incidents and thus, coordinate efficient responses. Strong communication keeps external partners and internal teams aligned, minimizing confusion during a crisis.
Compliance and regulatory awareness
CSIRT teams must be well-versed in data privacy and cybersecurity regulations like NIST, GDPR, and ISO 27001. Sufficient knowledge of compliance will ensure proper data protection, breach reporting, and risk reduction. Adhering to compliance will also help organizations to maintain customer trust, avoid penalties, and implement robust security policies.
Crisis management
A well-structured crisis management plan ensures quick incident containment and recovery. CSIRT teams should have the skill to develop playbooks for various risk scenarios. Expertise in risk mitigation techniques and business continuity planning helps to keep the operation stable during cyber-attacks.
(See how Splunk solutions support the entire incident management practice.)
Best practices for creating CSIRTs
The approach to setting up a CSIRT will depend on the organizational context. Another publication by the CMU SEI, outlines key best practices to consider when creating a CSIRT, including the following steps. Note that these steps do not always follow a strict sequence, as teams may perform some actions simultaneously or adjust the order based on the situation.
- Obtain management support and buy-in.
- Determine the CSIRT strategic plan.
- Gather relevant information.
- Design the CSIRT vision.
- Communicate the CSIRT vision and operational plan.
- Begin CSIRT implementation.
- Announce the operational CSIRT.
- Evaluate CSIRT effectiveness.
Cybersecurity will only grow in importance, risk potential
CSIRTs play a crucial role, especially as the technology landscape evolves and cyberattack sources become more complex. Collaboration and knowledge sharing across industries, countries, and regions will go a long way in raising the level of effectiveness in handling information security incidents.
Supported by international legislation such as the NIS2 Directive, improving incident response and handling capabilities in CSIRTs must be a priority for all organizations and nation-states for as long as the risks of cybercrime persist.
See an error or have a suggestion? Please let us know by emailing splunkblogs@cisco.com.
This posting does not necessarily represent Splunk's position, strategies or opinion.
Related Articles
About Splunk
The world’s leading organizations rely on Splunk, a Cisco company, to continuously strengthen digital resilience with our unified security and observability platform, powered by industry-leading AI.
Our customers trust Splunk’s award-winning security and observability solutions to secure and improve the reliability of their complex digital environments, at any scale.


