It was a night and day difference between what our current sandboxes were doing and what Splunk Attack Analyzer was doing for us.


When we’re dealing with something weird and nebulous and unknown, Attack Analyzer is one of the first tools in the tool belt that we use to help clear up the fog.
Features
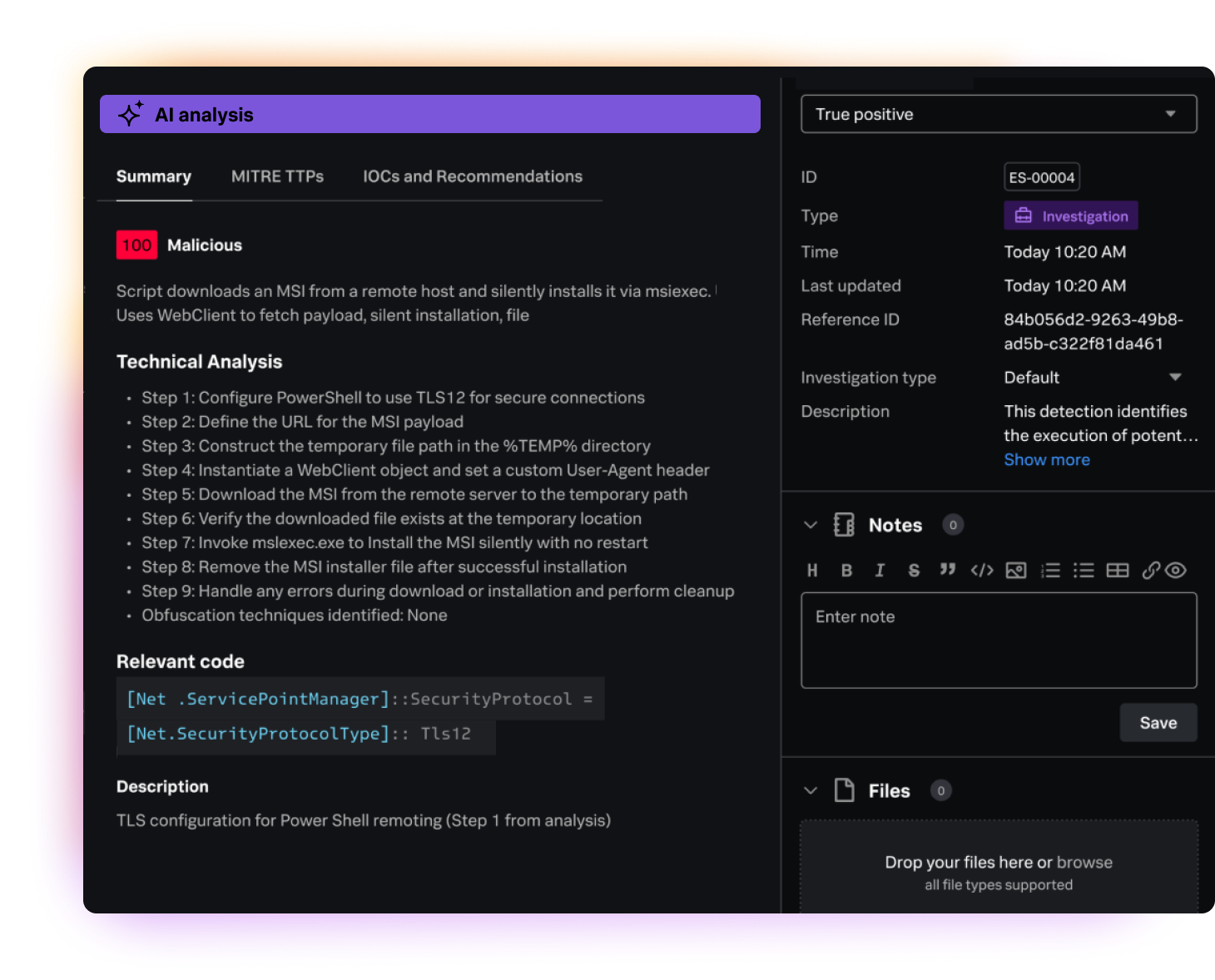
Reduce investigation and response times
Give analysts the context they need to quickly understand the full scope of an incident and determine the appropriate response.
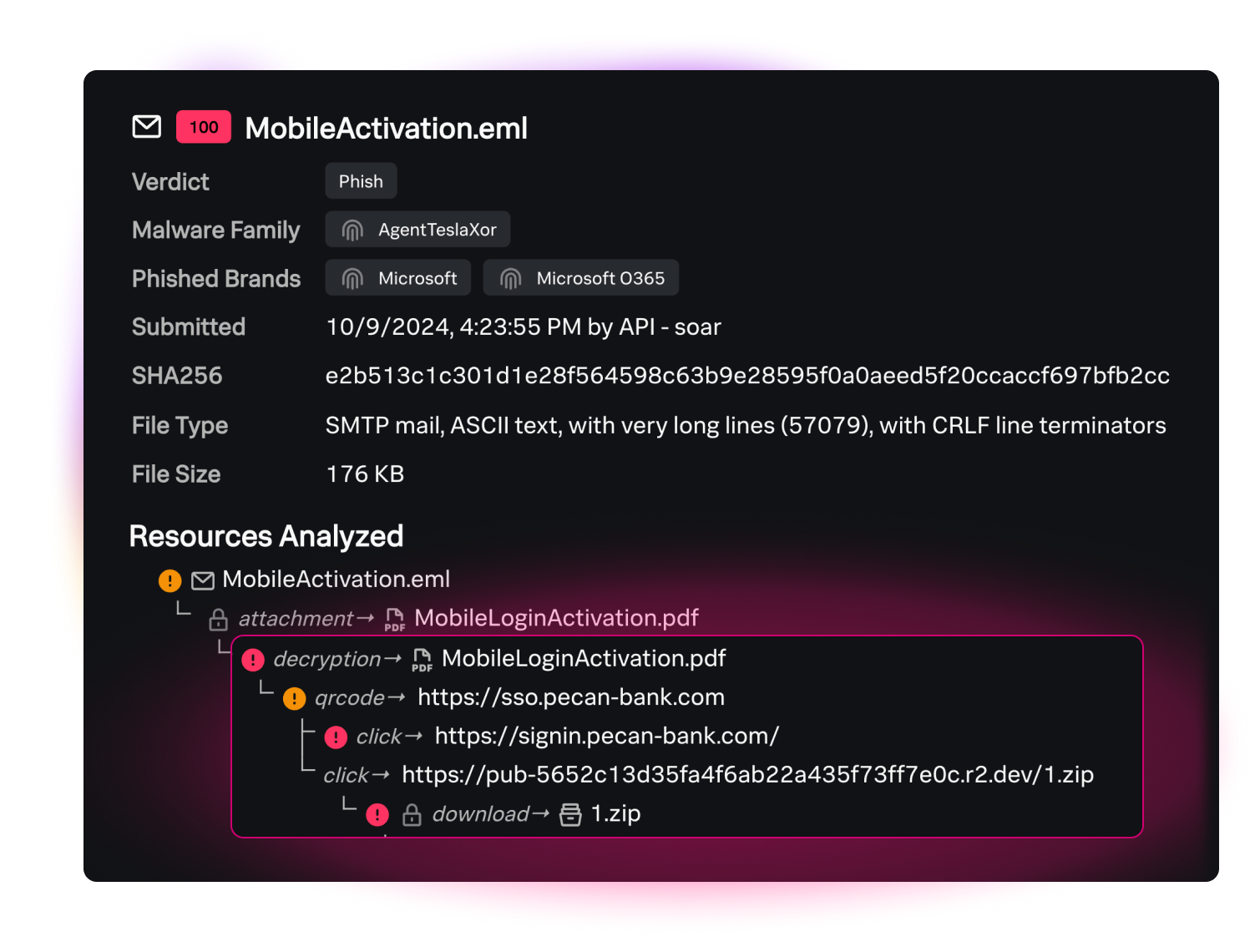
Follow and analyze complex attack chains
Visualize the attack chain without requiring security analysts to conduct manual work.
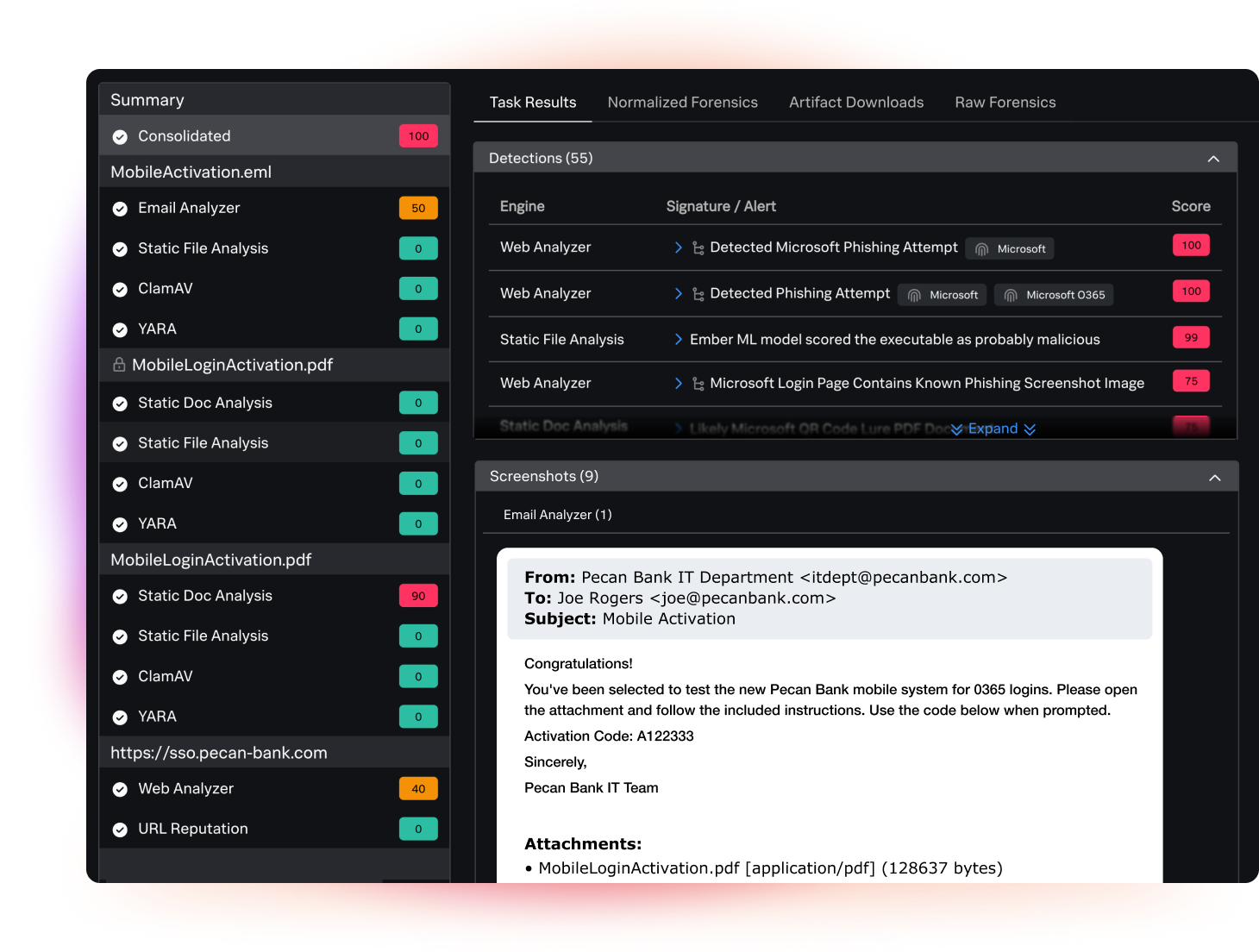
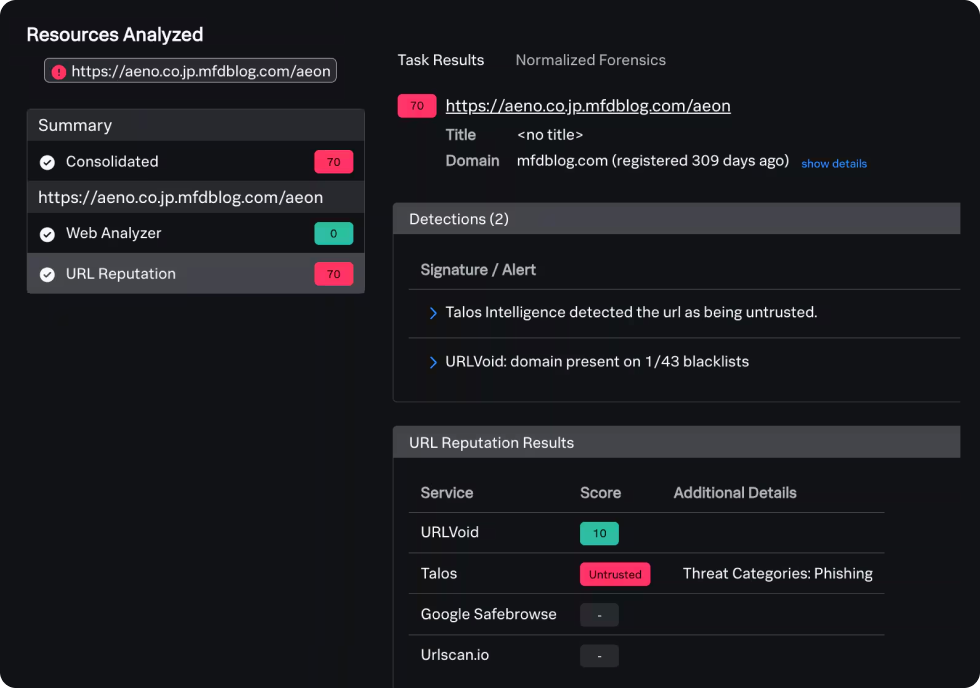
View detailed threat forensics
Access the technical details of attacks, including a point-in-time archive of threat artifacts from the time of reporting.
Interact with malicious content
Seamlessly generate dedicated, non-attributable environments within Splunk Attack Analyzer to access malicious content, URLs, and files — without compromising the safety of the enterprise.
Integrate directly with Splunk SOAR
Fully automate a complete end-to-end threat analysis and response workflow.
Access a comprehensive API
Integrate threat data into other platforms.
INTEGRATION WITH CISCO TALOS THREAT INTELLIGENCE
Detect ephemeral threats with Cisco Talos intelligence
Splunk Security
Strengthen digital resilience by modernizing your SOC with unified threat detection, investigation, and response.