CISA Top Malware Summary
Security Splunk Threat Research TeamSplunk is committed to using inclusive and unbiased language. This blog post might contain terminology that we no longer use. For more information on our updated terminology and our stance on biased language, please visit our blog post. We appreciate your understanding as we work towards making our community more inclusive for everyone.
This blog summarizes the Splunk Threat Research Team’s (STRT) recent review of the CISA Top 10 Malware strains for the year 2021 report. While many of these payloads have been covered in our past and present research (available at research.splunk.com), these malware families are still active in the wild. Notably, five malware families we analyzed in this article can still be seen in the ANY.RUN Malware Trends Tracker.
Malware, viewed through the lens of marketable software, continually evolve to add features which make them less visible, more feature rich and more resilient to reverse engineering. In particular, some of these features are clearly focused on exfiltration of sensitive information — especially personal or financial. Notably, some of these families through this evolution have been in constant use for over a decade (e.g., Qakbot).
To follow this thread of evolution, the Splunk Threat Research Team analyzed and developed analytics for five well-known malware families listed in the CISA 2021 Top Malware: Trickbot, Remcos, Azorult, AgentTesla and Qakbot.
Trickbot
A popular crimeware carrier that allows malicious actors to deliver multiple types of payloads. STRT has identified the presence of specific tools designed to inject malicious code into victims’ browsers, known as Web Injects, which work as custom elements that allow attackers to perform operations on top of the victim's web session while seeming legitimate. The delivery of this payload is usually via hyperlinks embedded in emails. This malware is also a carrier of other payloads, which are usually associated with Ryuk or Conti.

Remcos
Sold as a remote computer monitoring tool, Remcos provides a wealth of features which allow an operator to perform multiple operations against a compromised system. Remcos can be delivered by hyperlinks in emails as well. This particular malware is advertised as fully undetectable and is frequently used by malicious actors.

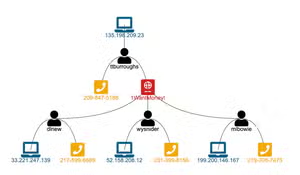
(For a larger resolution of this diagram visit this link)
Azorult
Azorult loader is a classic “Trojan Horse” that contains several components including the Azorult malware itself and additional embedded files to enable remote access and data collection. This loader is an AutoIt compiled executable that contains a self-extracting stream in its resource sections along with several files.
Azorult loader presents a particular feature where it uses Microsoft Windows AppLocker as a means to block and blacklist antivirus and defenses that may block its execution. Among many of the components within Azorult, there is a payload that imports its own AppLocker policy to deny the execution of several antivirus components as part of its defense evasion.

(For a larger resolution of this diagram visit this link)
Agent Tesla
Agent Tesla is a remote access trojan (RAT) written for the .NET framework that has been observed operationally since 2014. This malware leverages many different methods to deliver its payload over time, including macro enabled Word documents, various Microsoft Office vulnerabilities, OLE objects and most recently compiled HTML help files.
Agent Tesla has been in the top 10 most submitted samples in known open malware source repositories in cyber security communities like Malware Bazaar and Any.run. It is a full-featured RAT with multiple exfiltration methods (e.g., keylogging, screen captures, credential stealing).

Qakbot
This malware, also known as QBot or Pinkslipbot, is a multi stage/modular malicious payload that started as a banking trojan and has incorporated lateral movement and data exfiltration features. It is also becoming a popular tool of trade for criminals, and can be delivered by emails, files or images.

(For a larger resolution of this diagram visit this link)
Table 1 is the list of MITRE ATT&CK navigator JSON layers developed to map the STRT analytic detections coverage in MITRE ATT&CK Navigator to each malware family in this article.
Table 1
Commonalities by MITRE ATT&CK ID
To support SOC analysts, blue teamers and security researchers STRT visualized the overlap of our developed content against these 5 malware families.
As of the time of writing Splunk provides analytic detection coverage for these 5 malware families with 184 analytic detections. We took these 184 detections and grouped them by MITRE ATT&CK ID to easily identify and visualize commonalities across these malware families.
Figure 1.1 and Figure 1.2 show a summary table of all techniques relative to its MITRE ATT&CK ID in each malware family. Both figures show which techniques were seen in all or partial malware families.

Figure 1.1. (For a larger resolution of this diagram visit this link)


Figure 2 helps to visualize the coverage of techniques that are common across these 5 malware families. We can see that they use the same Defense Evasion techniques like disable or modify security tools (impair defense) and masquerading. In terms of Initial Access tactics, spear phishing attachments are the most common technique and also script execution as part of its malicious behavior.
The table “Detection Count per MITRE ATT&CK ID” shows the Splunk analytic detection counts per MITRE ATT&CK ID used by each malware family. One outlier data we can notice in this table is the big number analytic detections for Azorult in terms of T1562 technique (Impair Defenses).

In February 2022, Microsoft pushed an update to disable macros by default in Office products. Because of that, threat actors are trying to find ways to bypass this update.
Figure 3 shows interesting information about how the 4 active malware in the wild (Qakbot, Azorult, Remcos and Agent Tesla) shift to T1204.001 technique, which is the use of ISO or IMG files. Also the 4/5 malware families use scheduled tasks as part of its persistence and privilege escalation.

Figure 3 (For a larger resolution of this diagram visit this link)
Figure 4 shows Technique usage per malware family. Interestingly, three of the malware families are using registry run key and boot or logon autostart persistence techniques as well as credentials from password stores that are related to the TrojanSpy malware that steal browser information. We also observed malware that disables UAC as part of T1548 technique and process injection as part of defense evasion and privilege escalation.

We also grouped MITRE ATT&CK ID by all the Splunk security content analytic detections related to the 5 malware families to see which analytics can detect the techniques used by these malicious softwares. Figure 5 is a short snippet of the table showing this grouping of analytic detections.

For a larger resolution of these detection grouping by mitre attack id, please visit the link in the table below:
Commonalities by Detections
We also look at detections that can detect specific TTPs that are common in all or a subset of these malware families. Figure 6 shows a simple table describing these commonalities.
Observations:
- All 5 malware families used malicious macro code as part of their spear phishing techniques, which can be detected by office_document_executing_macro_code.yml and office_product_spawn_cmd_process.yml. Another set of detections that can detect all of these malware are the execution and file drop of its component in writable or public Windows Operating System directories.
- Another notable observation is that Microsoft disables macro code in Office documents by default, and most of the threat actors are using ISO or IMG files to bypass this security feature. In the table we can see that 4 of the malware families (Qakbot, Azorult, Remcos, and Agent Tesla) are using it. This event can be detected by windows_phishing_recent_iso_exec_registry.yml and windows_iso_lnk_file_creation.yml. We also notice that 4/5 of these malware families can be detected by scheduled_task_deleted_or_created_via_cmd.yml as the creation and deletion of scheduled tasks using schtasks.exe.
- Three out of five of these malware families can be detected by a Splunk analytic detection that looks for autostart registry, disabling remote UAC, accessing firefox browser user folder and disabling Windows Defender features.
- And lastly, two out of the five malware families, as we can see in the figure below, can be detected by the Splunk analytic detection that looks for LOLBIN execution (regsvr32.exe, rundll32.exe), powershell script, process injected, defense evasion in terms of services and use of wermgr.exe process as targeted process to inject malicious code that are known to Qakbot and Trickbot.

Detections

The Splunk Threat Research Team has curated analytic stories and tagged them to the malware families (Qakbot, Agent Tesla, Remcos, Azorult and Trickbot) to help security analysts detect adversaries leveraging these malware families. These analytic stories introduce 184 detections across MITRE ATT&CK technique.
For these analytic stories, we used and considered the relevant data endpoint telemetry sources such as:
- Process Execution & Command Line Logging
- Windows Security Event Id 4688, 7045, Sysmon, or any Common Information Model compliant EDR technology.
- Windows Security Event Lo
- Windows System Event Log
- Powershell Log
STRT Reference Blogs
Below are the Splunk Threat Research Team (STRT) blogs for malware analyzed from the CISA 2021 Top Malware list.
Why Should You Care?
The Splunk Threat Research Team (STRT) aims to enable security analysts, BLUE Teamers and Splunk customers to address 5 of the CISA 2021 Top Malware. This blog provides the community with tools to discover Tactics, Techniques and Procedures related to these threats and apply analytic detections that can detect a subset or all of these malware families. This blog also provides more insight into the commonalities between these 5 malware families in terms of TTP’s or techniques.
By understanding the behaviors and key indicators of these 5 malware families, the STRT was able to generate telemetry and datasets to develop and test Splunk detection analytics designed to defend and respond against these types of threats.
Learn More
You can find the latest content about security analytic stories on GitHub and in Splunkbase. Splunk Security Essentials also has all these detections available via push update.
For a full list of security content, check out the release notes on Splunk Docs.
Feedback
Any feedback or requests? Feel free to put in an issue on GitHub and we’ll follow up. Alternatively, join us on the Slack channel #security-research. Follow these instructions If you need an invitation to our Splunk user groups on Slack.
Contributors
We would like to thank the following for their contributions to this post: Teoderick Contreras, Rod Soto and Jose Hernandez.
Related Articles
Visual Link Analysis with Splunk: Part 2 - The Visual Part

Nothing PUNY About OpenSSL (CVE-2022-3602)
