Corporate Espionage: What You Need To Know
Learn Muhammad RazaWhen it comes to protecting sensitive business information and trade secrets, most business execs believe that sophisticated cybersecurity solutions and a strong mechanism for security governance are enough.
The reality is that establishing multiple layers of security defense forms a strong security fortress against external threats — but that’s not where most corporate espionage originates. Instead, attempts at corporate espionage often stem from:
- A disgruntled employee
- A planted spy
- A business partnership designed for intelligence gathering
These entities exploit the weakest links in the security chain: people. In terms of access to sensitive business secrets, research shows that an internal human element is responsible for 95% of all data breach incidents. Let’s take a look at corporate espionage.
Gathering intelligence…corporate espionage?
Who is gathering intelligence? Business organizations spy on their competitors. Some reverse engineer your products, some hire your previous employees. Some downright spy by exploiting internal members of the workforce or vulnerable machines running business sensitive applications and data workloads.
This intelligence is commonly used to guide trade policy, research and development, understand consumer behavior and evaluate the state of market competition by acquiring trade secrets, business intelligence, intellectual property, market and business strategies and technology solutions used to run a business.
This act of spying and intelligence gathering activity by using unauthorized and illegitimate means is known as corporate espionage, also called industrial or economic espionage. The scope of corporate espionage is limited to financial or commercial gains with a malicious intent. In recent years however, corporate espionage has also gained a strategic political intent. We have seen rival countries planting backdoors in processing chips shipped abroad and used by large multinational business organizations.
(Read about spyware, software able to capture certain information.)
The impact of corporate espionage
The immediate cost to the target of corporate espionage can impact in many ways:
Opportunity cost
The value of an opportunity may depend on the unique knowledge of it, to organizations with a first-mover advantage in discovering it through ongoing efforts and investments.
Innovation cost
An intellectual property or technology solution may take years of research and development before reaching a stage where the innovation is adopted and generates tangible ROI or business benefits.
Security cost
Business organizations are forced to invest significant resources toward deploying multiple layers of security defense. While this rarely offers immediate ROI, it is designed to protect against corporate espionage and cybersecurity threats.
Brand reputation
When a business organization loses sensitive consumer data and business information subject to stringent compliance regulations, it faces an immediate cost of lost business opportunity and legal penalties.
However, the long cost associated with the impact to brand reputation for failure to protect sensitive consumer data can be devastating. It takes years to build customer trust and considering the market competition in the digital era, consumers don't hesitate to switch to another brand that offers better data security and consumer privacy.
Protecting against corporate espionage
Corporate espionage affects everything, as it runs across all dimensions of the business organization:
- Trade secrets, documents and perimeter access in the physical world
- Software, sensitive consumer data and R&D documentation in the digital world
- Internal expertise and knowledge that comes from years of collaborations and training among employees
So how do you protect against corporate espionage across all dimensions of the business? The following security best practices can help against corporate espionage:
Strong Identity and Access Management (IAM)
Enforce the Principle of Least Privilege across all employees. Use Attribute Based Access Control (ABAC) IAM controls to ensure that employees can only access the information they need to perform their job, and not more.
(Read our IAM primer.)
Data security
Adopt end-to-end encryption for sensitive business information, especially when it is stored in the cloud and transmitted over the Internet. Develop a robust disaster recovery plan that guarantees business continuity in event of a ransomware cyberattack demanding access to sensitive data.
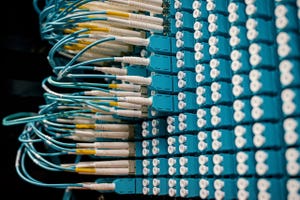
Network and physical security
Limit physical access to authorized personnel, especially at on-site data centers where servers store sensitive business information. Monitor your IT network for anomalous activities.
Train, build trust, reward loyalty.
Incentivize loyalty at the workplace. Develop a peoples-first workplace culture that encourages employees to hold high standards of cyber security awareness and responsibility when exposed to corporate espionage risks.
Train and educate employees on the risks associated with corporate espionage, what it means to the future of the business organizations, the markets as well as the individual careers of every employee.
Governance flexibility vs control
Instead of tightly controlling all aspects of the organization, develop a governance mechanism with adequate flexibility that allows your employees to perform their jobs comfortably. Tight controls such as a rigid governance mechanism against procuring new SaaS tools can encourage employees to adopt shadow IT activities, which only opens the door to corporate espionage.
Real-time monitoring
Understand how information is accessed and moved across your corporate network. Adopt technology solutions capable of proactively detecting anomalous user behavior and Website traffic. Set up a mechanism to isolate and contain damages in event of a cyber-attack.
FAQs
Related Articles

CAP Theorem & Strategies for Distributed Systems
SysAdmins: System Administrator Role, Responsibilities & Salary
