How it works
Built-in threat research and detections to fuel the modern SIEM
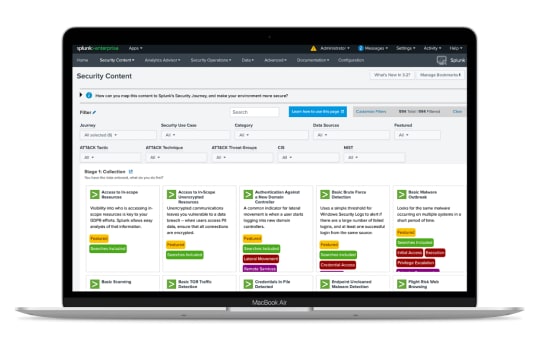
Expand your security coverage with pre-built detections
Integrate top-tier detections and defenses into your security — without needing to build them from scratch. Enable security content through Splunk Security Essentials or the Enterprise Security Content Update app. You can view the full repository of detections, use cases, and machine learning models on the Splunk Security Content site.

Stay ahead of the latest threats with cutting-edge security tools
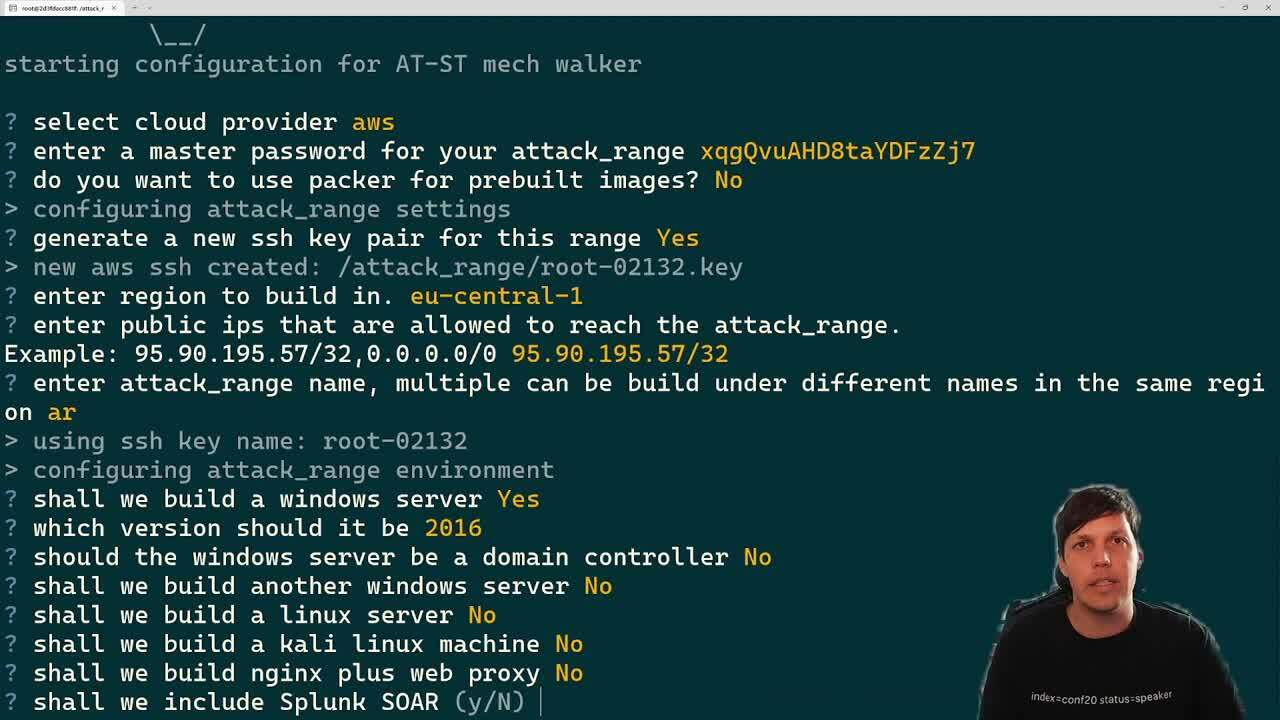
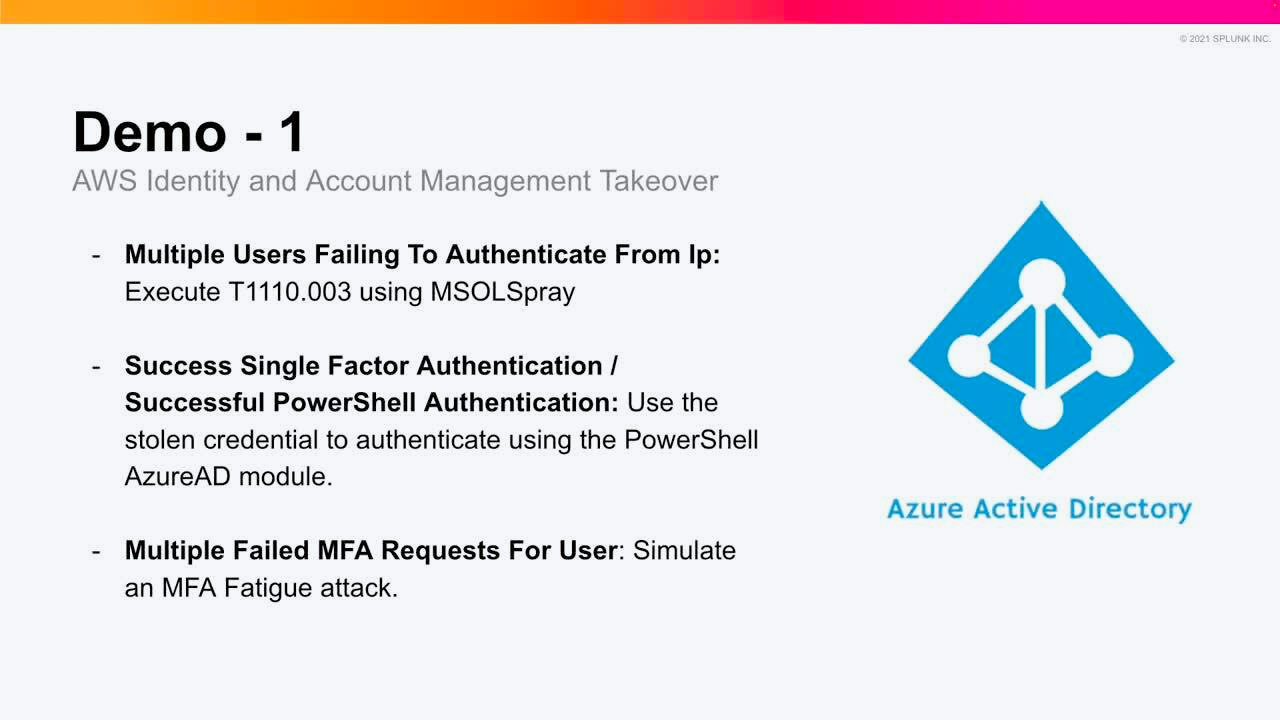
Equip your team with security tools and content to proactively defend against the newest observed tactics, techniques, and procedures in the wild. Test your detection searches against cyber attacks in a simulated environment utilizing open source tools from the Splunk Threat Research Team: Attack Range, Attack Data Repository and Melting Cobalt.
Supplement your team with trusted security advisors
Address your most pressing security challenges faster by tapping into the knowledge and experience of a team of industry-recognized experts. Read in-depth research authored by the Splunk Threat Research Team breaking down the latest threats and detection methodologies, and join the #security-research room in the Splunk Slack channel.

Splunk Detection Engineering Process
Learn how the Splunk Threat Research Team develops detections for Splunk security products.
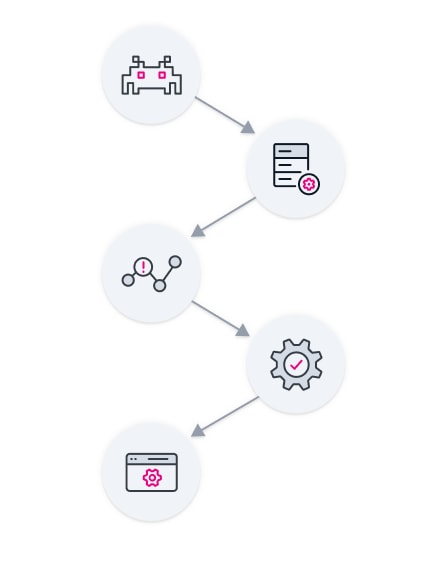
Study Threats
Identify emerging threats and understand how they operate
Generate Datasets
Collect data and use Splunk to parse the data and identify patterns that can be used to detect the threat
Build Detections
Build rules or queries designed to identify specific activity associated with the threat
Test Detections
Run queries against a dataset that simulates attacker behavior to improve accuracy and reduce false positives
Release
Package detections to deliver timely and effective protections against emerging threats to Splunk customers
Machine learning for security
Machine and deep learning detections to learn from data, identify patterns, and make decisions to help alert you to threats and anomalous behavior buried within vast amounts of data.
Related security products
Protect your business and elevate your security operations with a best-in-class data platform, advanced analytics and automated investigations and response.
Splunk Attack Analyzer
Automatically detect and analyze the most complex credential phishing and malware threats.
Splunk Enterprise Security
Industry-defining SIEM to quickly detect, investigate, and respond to threats.
Splunk SOAR
Work smarter by automating repetitive security tasks, respond to incidents in seconds, and increase analyst productivity and accuracy to better protect your business.
Splunk User Behavior Analytics
Secure against unknown threats through user and entity behavior analytics using machine learning.