2025 Gartner® Magic Quadrant™ for SIEM
Splunk named a Leader 11 times in a row.
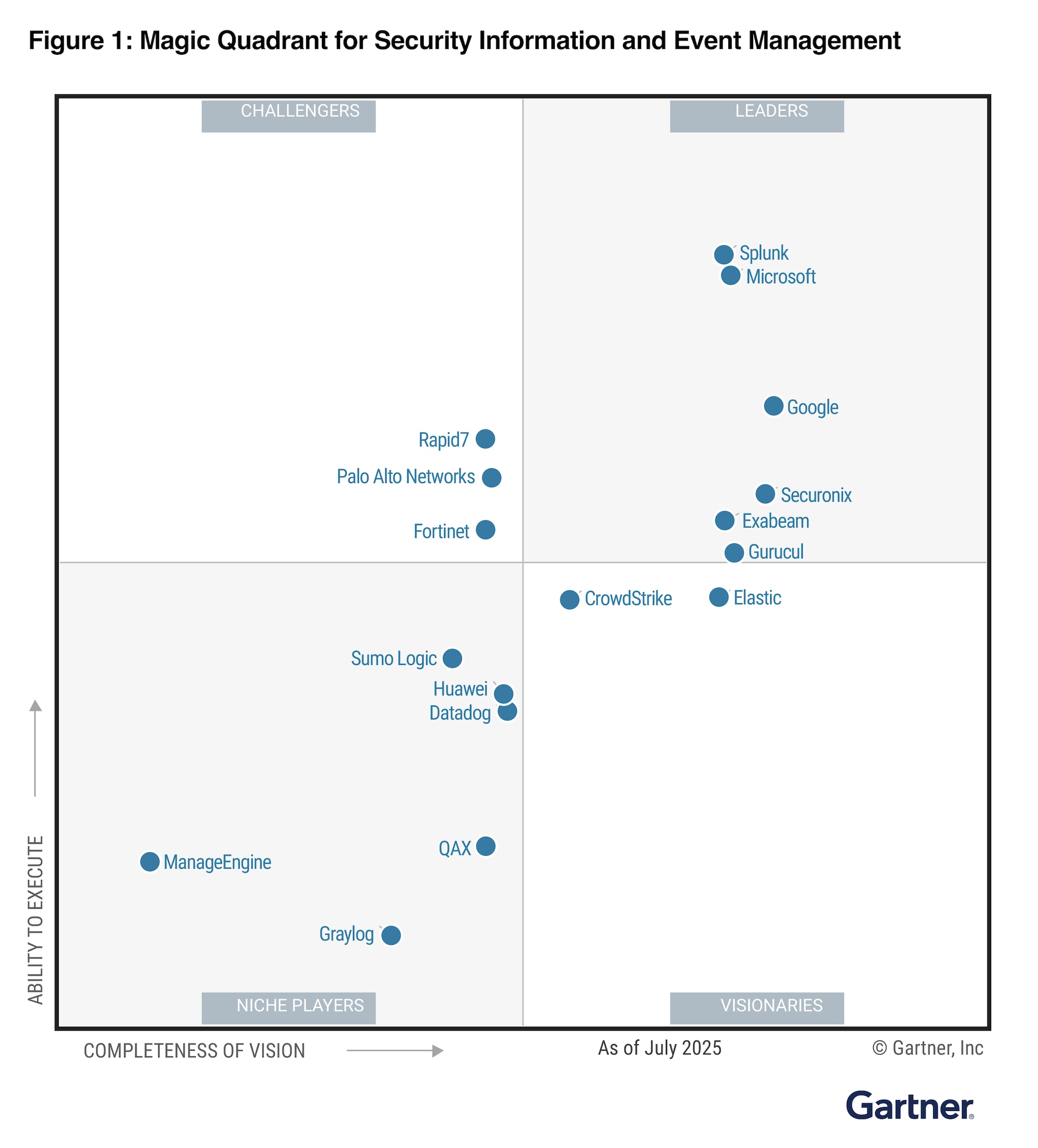
For the eleventh consecutive time, Splunk is proud to be named a Leader in the 2025 Gartner Magic Quadrant for Security Information and Event Management (SIEM). Gartner defines SIEM as a configurable system of record that collects, aggregates and analyzes security event data from on-premises and cloud environments. SIEM assists with response actions to mitigate issues that cause harm to the organization and satisfy compliance and reporting requirements.
Download your complimentary copy of the report to learn about:
- Must-have, standard, and optional capabilities for this market.
- How vendors in the report are evaluated based on their Completeness of Vision and Ability to Execute.
- The strengths and cautions of recognized vendors in the SIEM space.
Thousands of organizations worldwide rely on Splunk Enterprise Security as their SIEM to rapidly detect and respond to critical events so they can stay ahead of emerging threats and maintain cyber resilience. With the ability to perform a wide range of security analytics and operations use cases, organizations can remain flexible and agile in the face of evolving threats and business needs.
Watch our on demand webinar to learn how to end SOC analyst fatigue with the reimagined Splunk Enterprise Security. Don’t miss out!
Gartner, Magic Quadrant for Security Information and Event Management, Andrew Davies, Eric Ahlm, Angel Berrios, 8 October 2025.
GARTNER is a registered trademark and service mark of Gartner and Magic Quadrant is a registered trademark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and are used herein with permission. All rights reserved.
This graphic was published by Gartner, Inc. as part of a larger research document and should be evaluated in the context of the entire document. The Gartner document is available upon request from Splunk.
Gartner does not endorse any vendor, product or service depicted in its research publications and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s research organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.