Identify TTPs (like HAFNIUM) instantly using customized detections and risk-based alerting across an integrated data fabric.
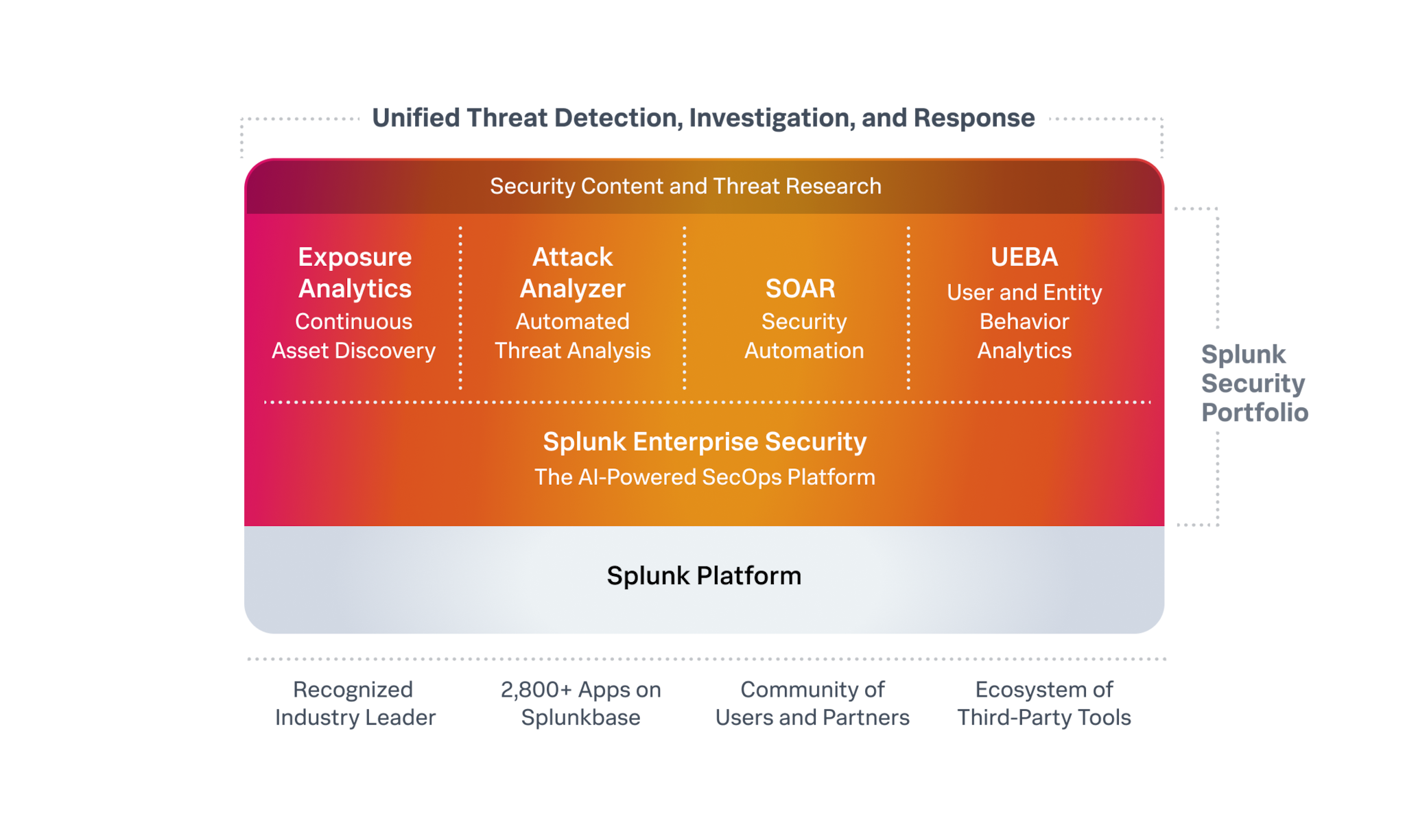
Unify security data, analytics, tools, and AI to automate routine tasks, surface complex insights, and proactively mitigate risk.
Scale operations with high-fidelity data
Turn high-volume data into high-fidelity visibility using an open data fabric with advanced pipelines and flexible federation.
Streamline detection and response
Focus on what matters by unifying threat detection, investigation, and response (TDIR) workflows in a leading SecOps platform.
Stop threats at machine speed
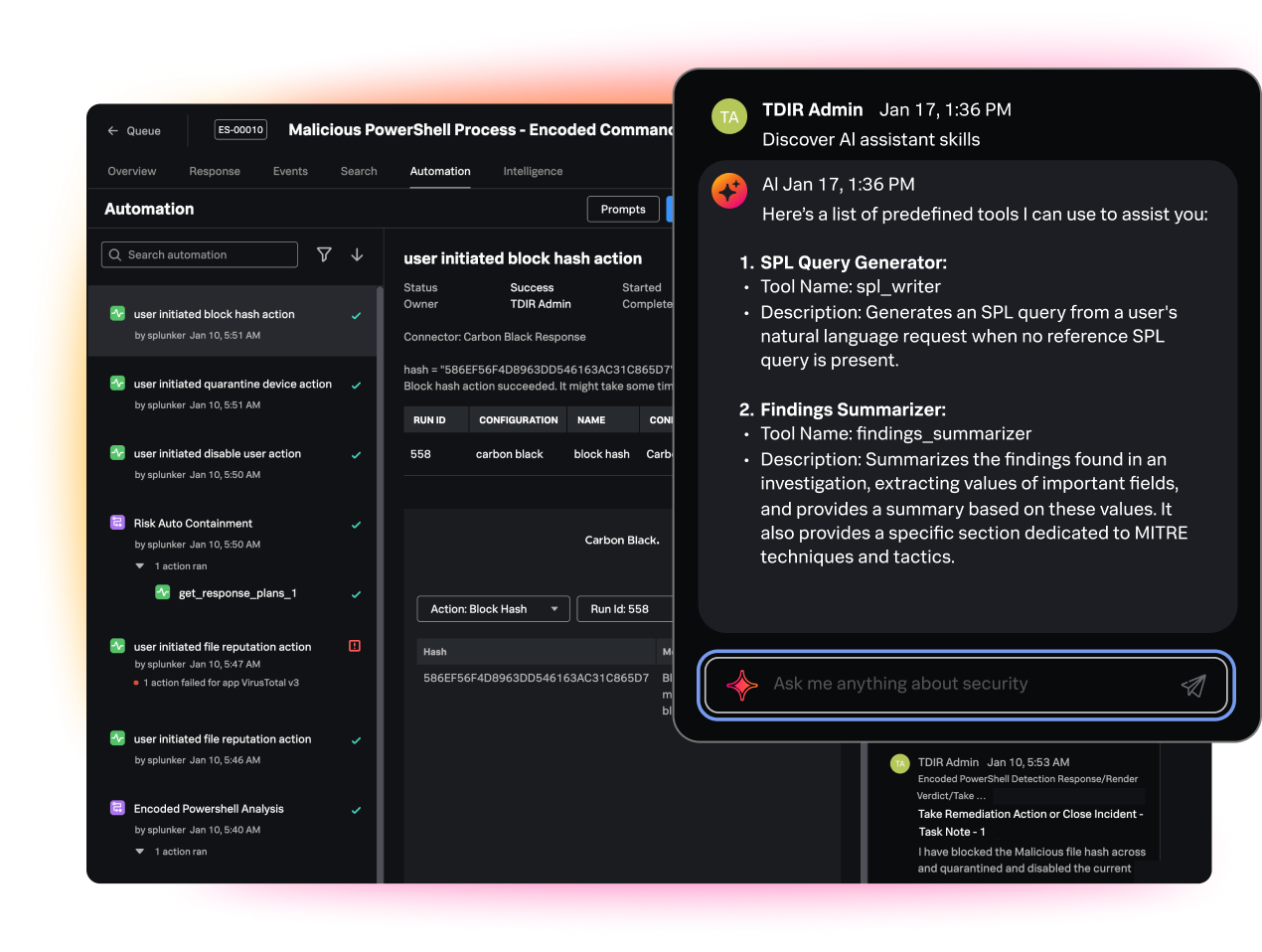
Infuse intelligent automation, generative AI, and purpose-built agents across every workflow to gain a durable advantage against adversaries.
For over two decades, Splunk has been a leader in the security industry, helping pave the way for the agentic SOC.
Splunk redefines security operations by integrating an open data fabric, powerful analytics, cohesive tools, and human-in-the-loop AI into a unified platform. With Splunk, you can:
For over two decades, Splunk has been a leader in the security industry, helping pave the way for the agentic SOC.
Splunk redefines security operations by integrating an open data fabric, powerful analytics, cohesive tools, and human-in-the-loop AI into a unified platform. With Splunk, you can:
See Splunk Security in action: try an interactive, step-by-step tour and get a close look at the product UI and features.
See Splunk Security in action: try an interactive, step-by-step tour and get a close look at the product UI and features.
Splunk is the best product for us based on efficiency and ease of use. Splunk is best-in-breed.