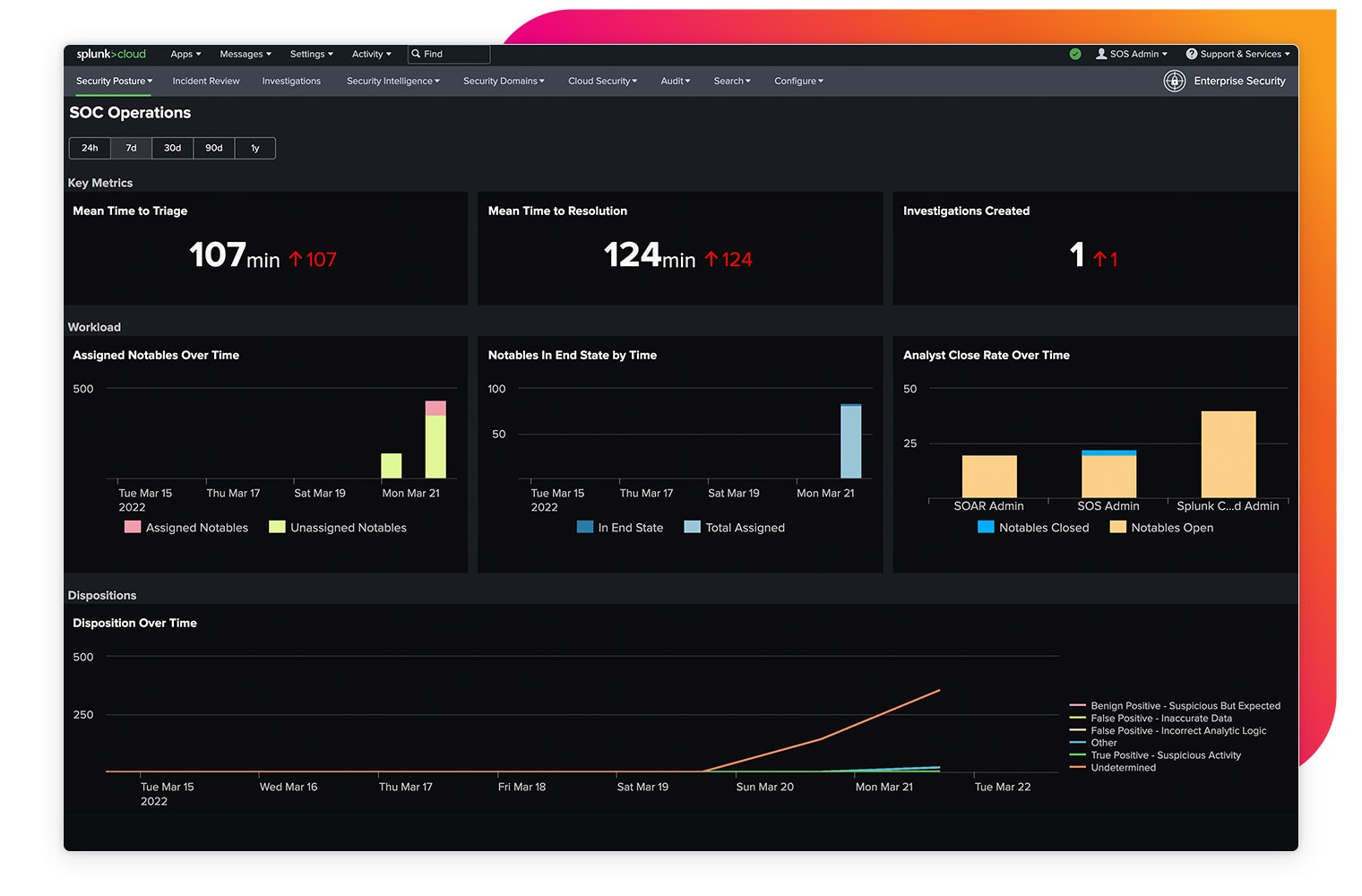
Detect network and host activity that might indicate an advanced threat. Collect, index, correlate and analyze all data and monitor activity patterns. Create complex searches with user-defined thresholds.
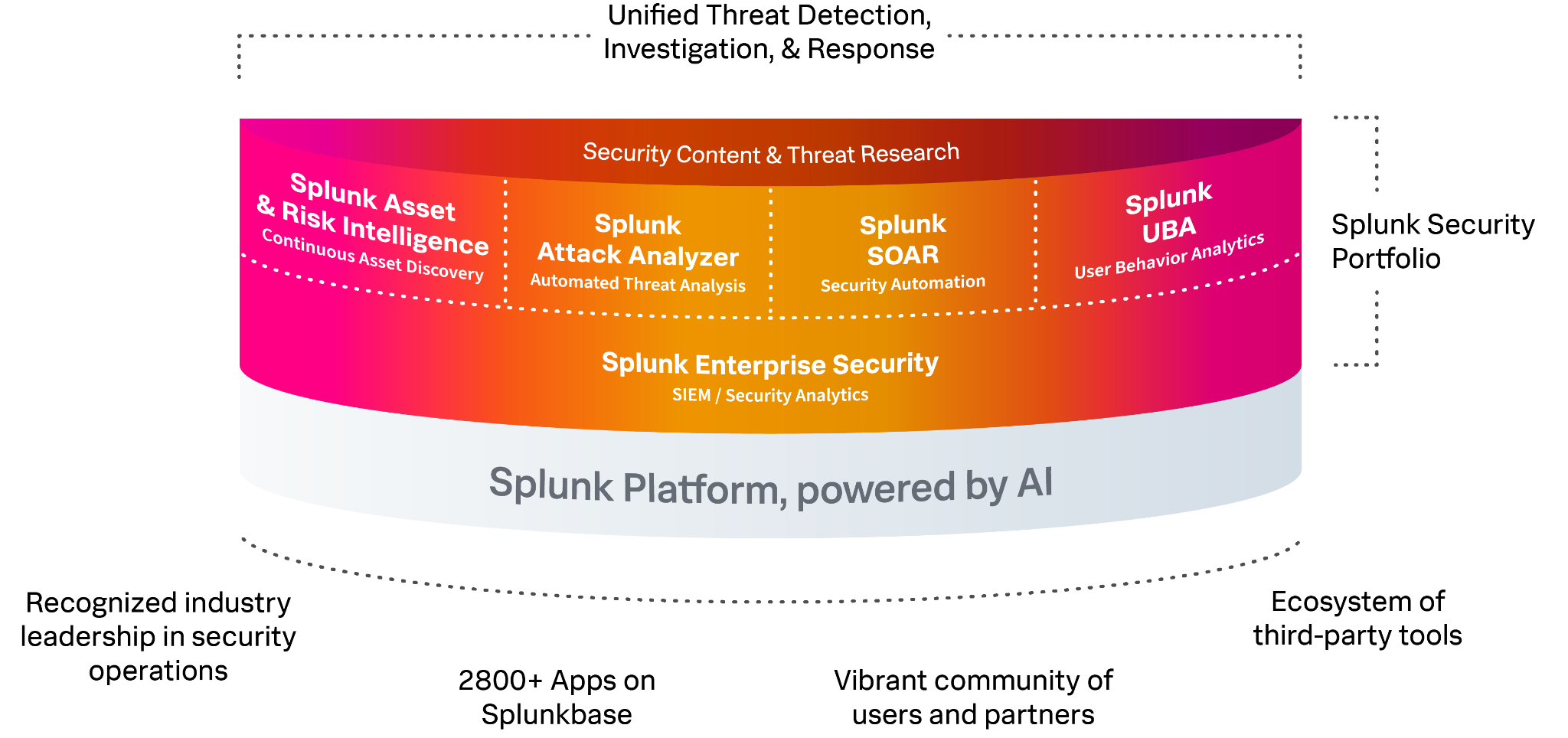
Detect Threats at Scale
Gain visibility and detection at scale to reduce business risk.
Unify Security Operations
Unify detection, investigation, and automated response for speed and efficiency.
Empower Security Innovation
Solve any use case with a vast user community, apps, and partner ecosystem.
See Splunk Observability in action: try an interactive, step-by-step tour and get a close look at the product UI and features.
See Splunk Observability in action: try an interactive, step-by-step tour and get a close look at the product UI and features.
Splunk is the best product for us based on efficiency and ease of use. Splunk is best-in-breed.