IoT and Cybersecurity: What Are We Protecting?

We kicked off RSA Conference 2019 last week with bold plans for the future, including our innovation to improve efficiencies in securing futures, combating the opioid crisis and protecting critical infrastructure.
This year, we saw increased interest in operational technology (OT) security at our booth. Why connect this to the network? How can I identify the risk associated with it? Where would I get the data? These were just some of the questions we addressed in our theater presentation and demo around IoT cybersecurity.
Our story
IoT is extremely important in optimizing businesses’ operations, and it’ll become more important (particularly in OT environments) as a way to forecast things and predict failures. But security must be the focus in the process because failing to implement security controls could harm system availability and performance—the very things OT staff care most about.
Although there are differences in priorities between IT and OT, we’re seeing more and more IT and OT team members coming together as IT and OT technologies converge. Both teams see the need for securing their converged environment. The result is that IT staff is now focusing on monitoring the OT network to gain visibility and making sure that changes to systems are authorized so that OT folks can focus on production issues.
But both teams are still working in silos, looking at siloed data with a narrow focus. This will not help effectively protect OT environments. Part of the problem is that there has never been a common platform IT and OT practitioners could use to hold their data.
What we’ve learned is that OT production data is extremely relevant to the security of OT environments.
If organizations are going to securely and efficiently optimize industrial operations, they need to make production and security data transparent and shareable across a converged IT/OT architecture, from the Field Network to the IT Network.
Organizations will need a common data platform that can handle the data ingestion and the advanced correlation so that IT and OT teams can quickly access and analyze all security-relevant production data. Only then will they get the insights they need to improve operational efficiency, reliability and security.
With Splunk, all of this is possible, enabling genuine collaboration between IT and OT teams.
For production efficiency and industrial security, what types of data should be collected?
In a typical converged IT/OT network, there are SCADA systems, data historians and manufacturing execution systems (MES) that are often integrated with enterprise resource planning (ERP) and other key IT systems.
For production efficiency, most organizations are looking at data in historians for trends over a period of time. While data historians are best at presenting aggregate data, it’s at the lower levels where fine-grained production data is found. As the data gets aggregated and communicated to the upper levels, information in each layer is lost, so it’s necessary to look at data from PLCs, RTUs and sensors at the lower levels to do forecasting and predictive maintenance.
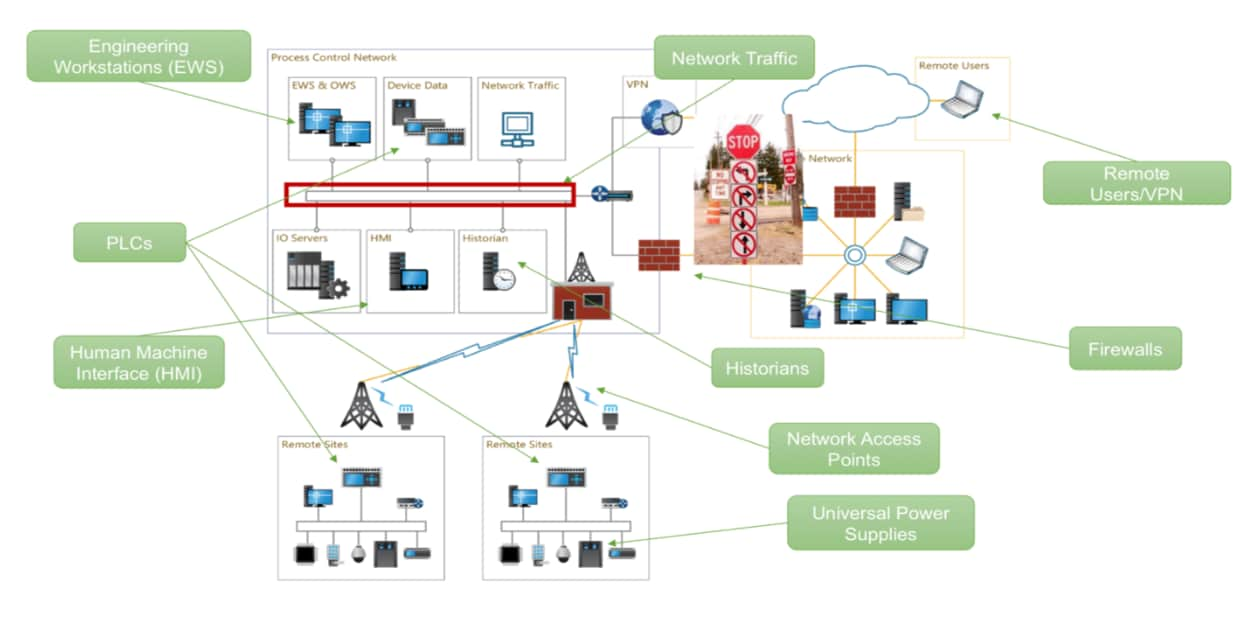
And the related security part of that is that it’s also not sufficient to just look at authentication and network traffic from Windows systems, firewalls and routers at upper layers. It’s necessary to monitor the right combination of systems in order to effectively and efficiently protect OT environments.
- Look at remote users and partners and monitor hacked credentials and unauthorized access.
- Engineering workstations are big targets of attacks. Since they have access and control over the OT infrastructure, it serves as a great place to launch attacks in OT networks.
- Historians are another big target as they communicate to most OT equipment to collect data. Gaining access to the historian provides access to a big portion of the OT network.
- Most industrial control systems have a Human Machine Interface (HMI) for operators to send commands to field or factory equipment. HMIs usually run Windows OS and are very difficult to patch and maintain security. Because of these vulnerabilities, they are often easy targets to hack and ultimately gain control over the control of equipment.
- PLCs are the actual interface for controlling the physical infrastructure. That means an adversary can stop processes or cause machines to malfunction.
So what can you do with all this data?
You can now find unexpected correlations to accurately assess your risks with Splunk. When unusual events happen, you can ask new questions and look at the data in new ways to get to the underlying cause of the problem.
For example, how do you know if a turbine failure was not due to a mechanical issue from a defective nozzle but rather to a cyberattack? You might ask, “Was there any authorized control setting pushed out to my electrical system?” You might also ask, “Were there any access attempts to HMIs?” and “Is this device known to be vulnerable?”
Looking for and analyzing the relationships between production and security events can help to find stealthy security incidents that you might miss if you were to look at them separately.
Final thought—what if you could automate detection and response of incidents in your OT environment?
Right now, there are lots of talks about automating and orchestrating security incidents to streamline detection and response activities. Splunk Phantom gives you the ability to fully automate certain actions or allows a human operator to approve changes before they are made.
What if you could trigger a validation alert whenever a certain configuration change is pushed down to a device? It’s not out of reach.
----------------------------------------------------
Thanks!
Mary Chen
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




