What is Identity Access Management?

Identity and Access Management (IAM) is the name for any framework of technology, policies and processes that authenticate and authorize a user in order for that user to access and consume an organization’s resources.
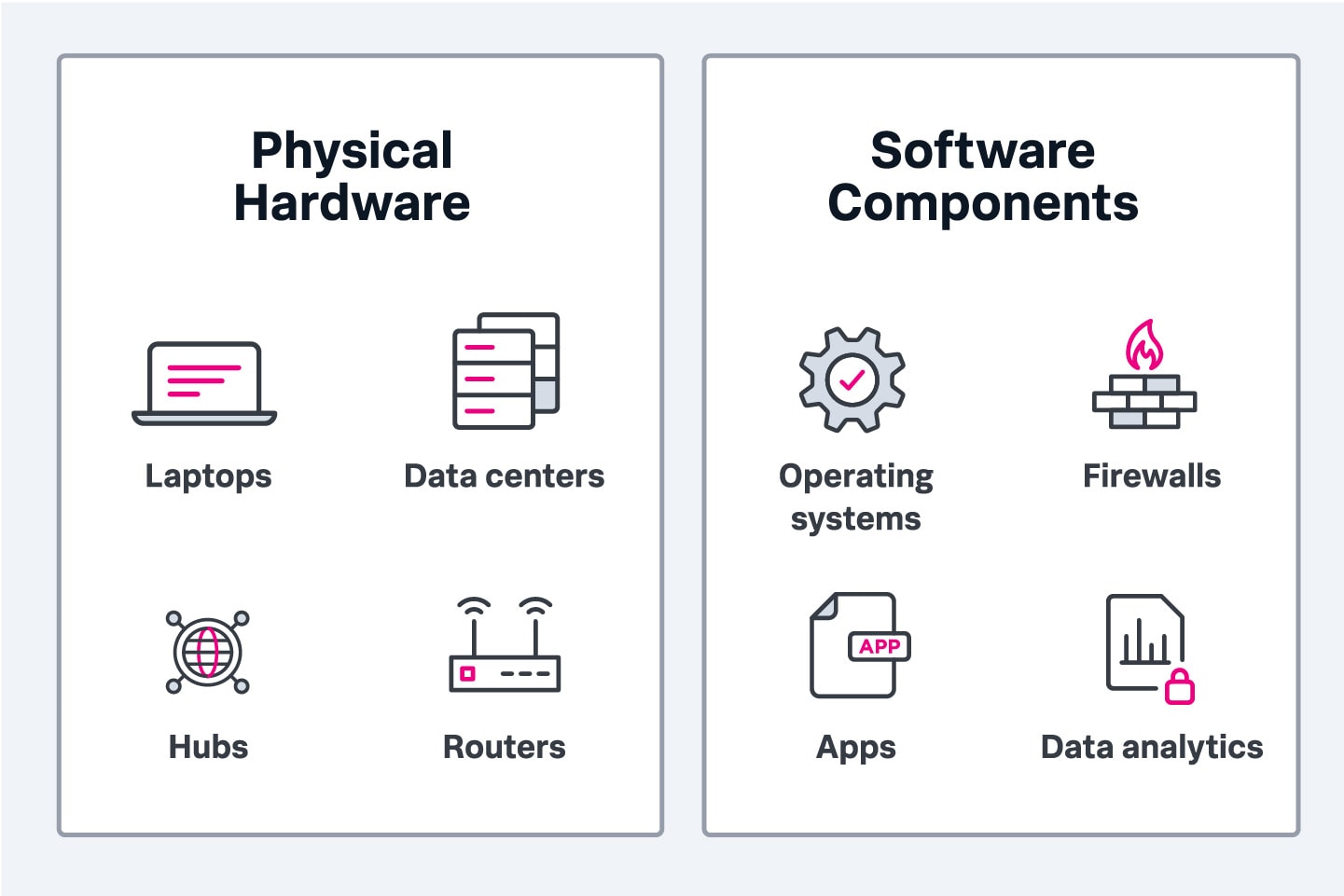
Managing user identities and granting appropriate user access helps protect your assets. These assets can include digital access to sensitive information, intellectual property, data and application workloads, network access or perimeter access to the physical data center location.
Because identity theft and data breaches are on the rise globally, more people are paying more attention to IAM. Stolen or misused credentials are the easiest way for attackers to gain access to your company information — and a successful breach can include severe financial losses, damaged reputation and regulatory penalties.
With successful IAM, your organization can:
- Better manage access to your information systems.
- Safeguard information.
- Track user and system activities.
Let’s take a look at this important business function. In the following sections, we’ll look at the roles IAM plays within organizations, the benefits it offers and the kind of problems it can detect and prevent. We’ll also explain what to look for in an IAM solution and how to get started.
IAM basics: The purpose of identity & access management
Business organizations are compelled to limit employee access to these systems beyond what is required by their job routines — this helps reduce all sorts of risks, and it has knock-on effects in terms of limiting resource consumption, too.
This idea follows the Principle of Least Privilege, which guides strong security controls for authorizing access. IAM is tightly coupled with the governance structure and security policies facing the organization, driven by:
- Applicable compliance regulations
- Cybersecurity risks
- The business value associated with every data asset, application and network component
Goals and objectives
The goal of an IAM system is to establish an optimal tradeoff between strong security against unauthorized access — with the flexibility to provision resource access without violating the security policies or exposing undue security risks.
The latter is particularly challenging. Most enterprises operate a complex infrastructure that runs highly dependent application components. Isolating these resources by static policies defined by user roles and resource types becomes virtually impossible.
In the context of IAM, a “user” can be a human, a device or a service. IT administrators assign a single digital identity to each user. This identity indicates who or what the user is and what level of access they are allowed to have in the organization’s applications and systems — from least privilege to most.
Because users’ roles change over time in the organization, their privileges continuously have to be managed, monitored and modified. An IAM platform gives IT administrators the tools to modify a user’s role, monitor their activity, ensure compliance with policies and regulations, and otherwise regulate access to the organization’s assets.
IAM has several objectives that together help mitigate security risks, ensure compliance and improve operational efficiencies. These objectives include:
- Ensuring that legitimate users have the appropriate level of access to the right resources in the right context.
- Preventing unauthorized users from accessing the network by limiting access to specific groups and roles and verifying their identities.
- Monitoring user activities to detect unauthorized access and hacking attempts — and revoking access as soon as employment is terminated or changed.
- Preventing fraud committed by users who abuse their access privileges.
- Meeting various regulatory criteria for customer identification, suspicious activity detection and identity theft prevention.
Challenges that IAM can detect & prevent
IAM offers several benefits, including secure access, reduced risk, better user experience, fewer insider threats, easier compliance, reduced IT workload, easier provisioning and deprovisioning and even easier auditing and reporting.
From an offensive security standpoint, IAM can detect and prevent a range of cyberattacks, including:
- Phishing & spear phishing
- Keyloggers
- Credential stuffing
- Brute force and reverse brute force attacks
- Man-in-the-middle (MITM) attacks
- Insider threats
Each of these cyberattacks involves the use of co-opted account credentials. IAM can prevent them by enforcing strong password policies and requiring multiple authentication factors to gain access to an account.
In the event an attacker does gain access to the targeted system, IAM’s adherence to least-privileged access can limit their access to high-value data and mitigate the damage they can do.
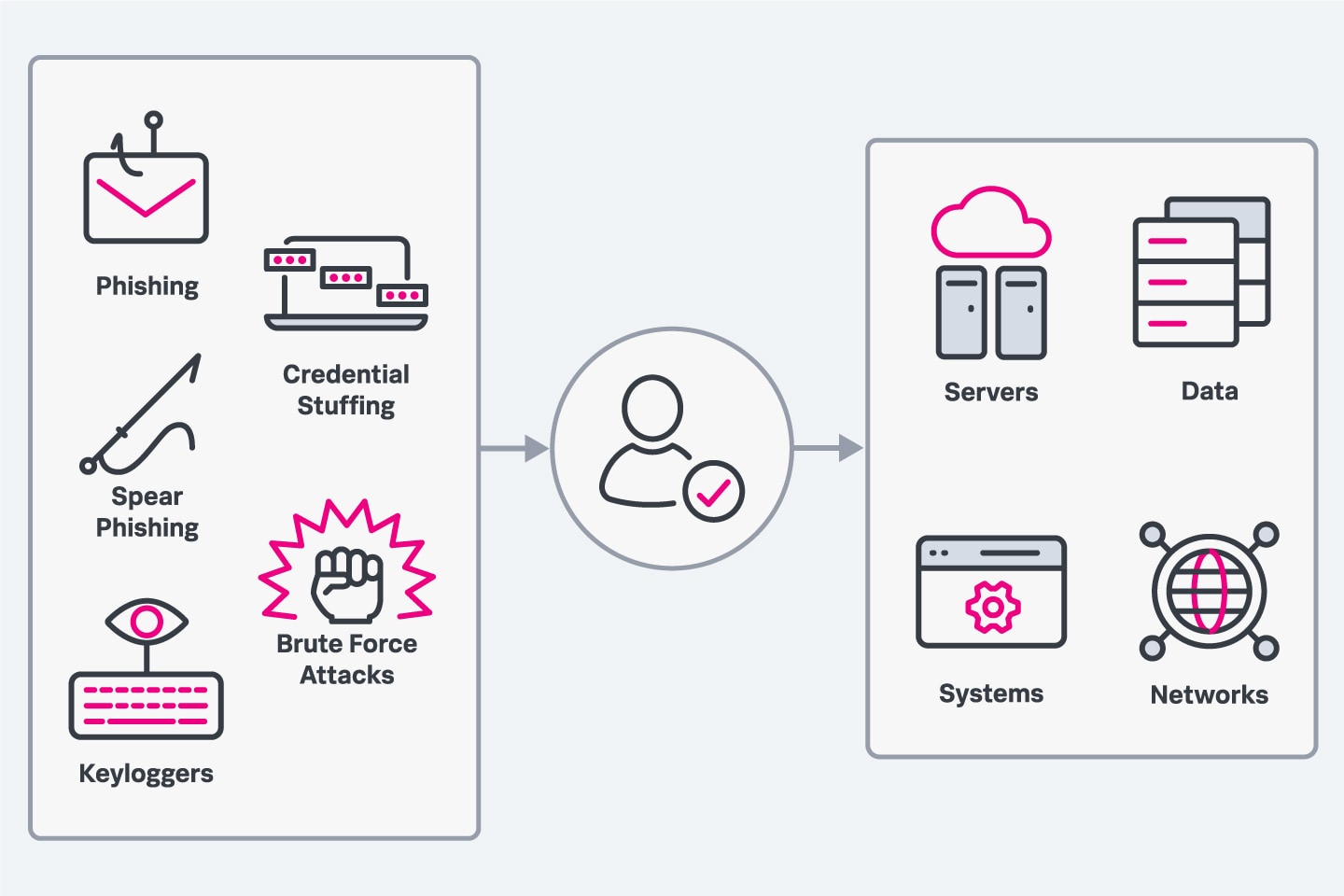
IAM can help prevent and detect numerous threats, including phishing attacks, keyloggers, brute force attacks and insider threats.
Managing identity & access: how IAM works
So how do you manage the IAM lifecycle of the organization? Let’s break this into two simple questions, and I’ll hopefully provide clear answers.
How to manage identity: Authentication
The IAM system authenticates the identity of the requesting entity, which may be an individual user, a group or a role depending on your access control policy. Factors used for authentication include:
- What you know: username, email address, passwords, passcode, pincode, passphrase and security questions
- What you are: Biometrics such as fingerprints, voice, hand geometry and Iris recognition
- What you have: smart keys, smart cards, tokens, mobile devices, phone number, email accounts
The IAM system authenticates the source of a request to determine the identity of the user, user group and roles. The authentication system is tightly coupled by the governance of the identity database and its consumption in the entity authentication protocols.
The authentication process itself does not determine whether the request is approved — it simply verifies the claimed identity of the requesting party and is corroborated by the fact that the requesting entity is active, alive and a member or partner of the organization.
The IAM also extends the verification process to data authentication via API requests from an integrated set of third-party cloud-based services that may request access to your corporate network. Data authentication verifies the originating source of data and also authenticates the integrity of that data (that is, the data has not been modified by an unauthorized source).
How to manage access: Authorization
The IAM system is designed to reduce the security risk exposure of your data by managing access controls over the lifecycle of the identified entity. It denies all requests by default — with the exception of requests that comply with the access control mechanism.
The IAM system is used to associate policies to IAM identities or third-party resources. These policies determine the list of permissions that can be attributed to these IAM identities. These permissions are then used to approve or deny a request to access the network or data resources.
(Related reading: authorization complete guide.)
Common access management approaches
Some of the common schemes to manage permissions and employ appropriate access controls for IAM identities include:
- Access Control Lists (ACLs) are a legacy feature that are simplistic in today’s digital environment.
- Role Based Access Controls (RBAC). These are identity-based access control policies that assign a set of permissions to individual entities, including users, their roles and groups.
- Attribute Based Access Controls (ABAC). This authorization strategy defines the permissions based on the attributes associated with the request. The role of the IAM identity itself can be considered an attribute, but the ABAC brings a holistic view to this concept. Attributes can include an exhaustive decision criterion including environment variables, subject parameters, actions requested and IAM resource objects that describe the identities and groups.
The explicit policies generated by the RBAC, ABAC or another access control scheme override the default request denial of the IAM system.
The ABAC model allows organizations to scale permissions in a complex IT infrastructure environment, where it may be difficult to federate sensitive data assets and network components based on the roles and identity of the user. Instead, the attribute tags assigned to users and the resources can be used to establish granular permissions that do not overlap.
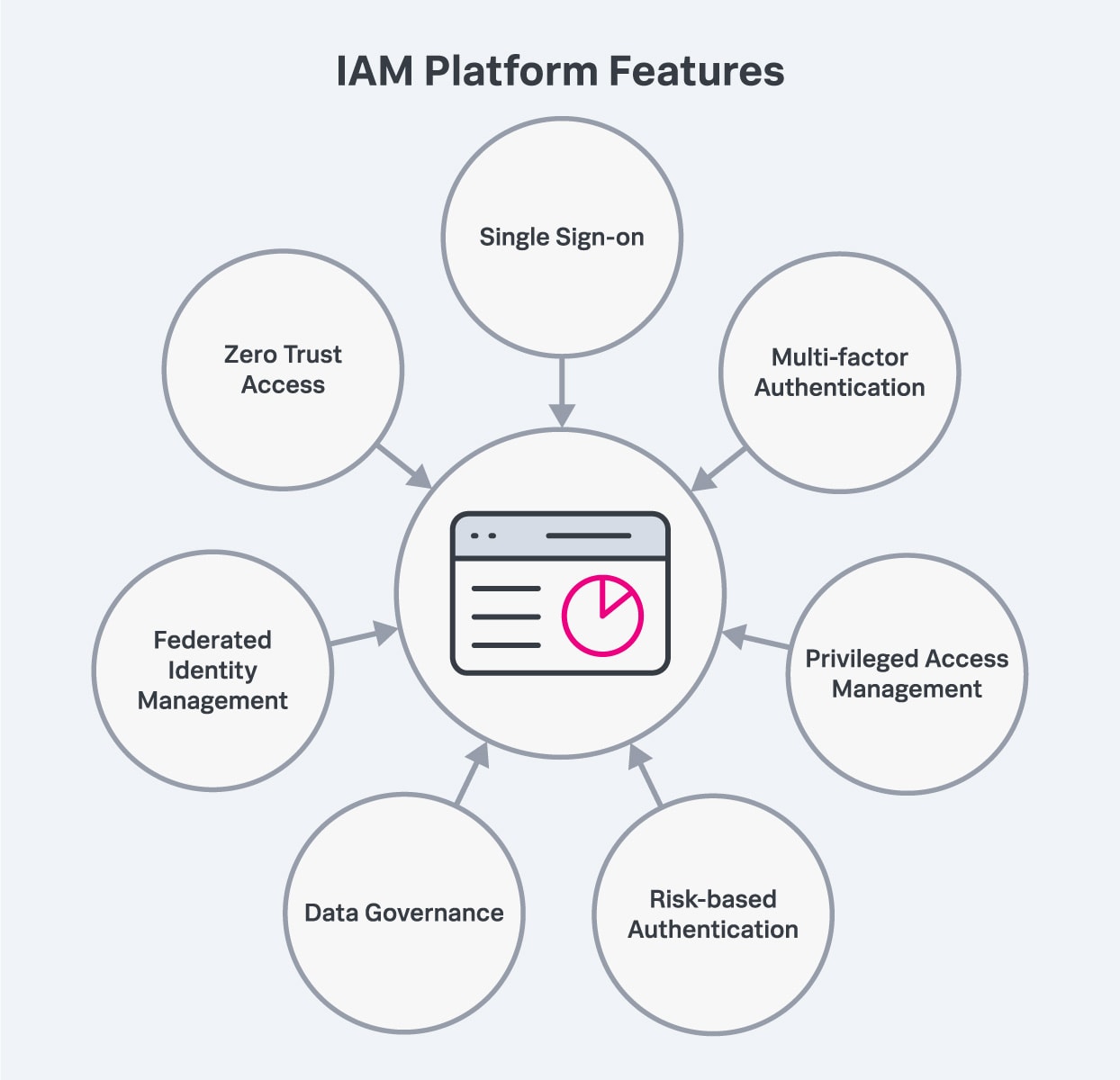
Common IAM features to look for include single sign-on, privileged access management, data governance, and multi-factor authentication, among others.
Features of an IAM platform
An IAM platform is a solution that lets IT administrators assign, maintain, monitor and modify user identities and access-level privileges. An IAM platform comprises multiple systems and components. Let’s review some of the common and in-demand features.
Single sign-on
Most IAM platforms support single sign-on (SSO). This method of access control lets users authenticate themselves across multiple systems and applications with one set of login credentials. SSO improves an organization’s security by:
- Eliminating unsafe password management practices.
- Reducing the size of the attack surface.
- Improving identity protection.
Multi-factor authentication
Multi-factor authentication (MFA) requires users to enter multiple credentials to verify their identity and access a system. Some IAM platforms support adaptive MFA, which utilizes contextual information such as IP address, location and device type, along with administrative policies to determine authentication factors that should be required by a particular user and situation.
Privileged access management
Privileged access management protects an organization from data breaches and other security threats by assigning higher permission levels to user accounts with administrator-level controls and access to high-value assets.
Risk-based authentication
Risk-based authentication considers a user’s IP address, location, current device and other contextual factors when they attempt to log into a system or application. It uses this information to assess risk level and determine whether to request additional authentication factors or to allow or deny the user access.
Data governance
Data governance is a framework of policies and procedures for managing the availability, integrity, security and usability of an organization’s data, ensuring it’s consistent, accurate and protected. Data governance is an increasingly important part of IAM, especially for an IAM platform that relies on AI and machine learning to monitor user activity, detect breaches and increase efficiencies.
Federated identity management
Federated identity management is a method for linking a user’s digital identity across separate identity management systems, allowing users to access the systems and services of multiple trusted business partners with the same authentication credentials.
Whereas SSO lets employees use a single set of login credentials to access multiple systems within a single organization, federated identity management lets users use their digital identities to access the systems of all the organizations within the federated group. This will let a vendor, for example, access the systems and services of one of its customers.
Zero trust access
A zero trust framework assumes that an organization’s network is always at risk and that no user should have access to everything without specific authorization. This is becoming increasingly important as IoT and endpoint devices expand the network perimeter. A zero trust IAM platform allows organizations to continually assess and verify user access and achieve complete visibility into who and what is connected to their network at any given time.
Compliance and audit performance
An IAM solution should make the compliance and audit process more efficient. Look for one that provides out-of-the-box reporting tools for standards and regulations.
Incident reporting
In the event of a data breach, an IAM solution should be able to tell you what user credential was involved and how it was used. Look for a tool that supports machine learning-powered user analytics and reporting tools. These will allow you to track and detect anomalies or suspicious activity, detect privilege abuse and provide deeper visibility into your environment’s critical identity risks.
Getting started with IAM
To get started with IAM, you’ll need an IAM solution. Choosing the right platform can be a daunting task, so it’s important to consider your organization’s needs before starting the procurement process.
Consider who the IAM solution is for. If you’re primarily concerned with B2C or B2B customers, there are customer IAM solutions that prioritize self-service and user-friendliness to provide the best possible customer experience. If you need a solution for employees, you’ll need to ensure your IAM solution can integrate with your organization’s internal systems.
An IAM solution that combines access control for both internal and external users will be the most efficient and cost-effective. Once you’re set up, the best practices remain the same:
- Limit privileged accounts: Users might need access to privileged accounts to perform some tasks, but they shouldn’t have regular access for day-to-day operations. Role-based access control can help mitigate the risk by granting privileged access to a user for a specified time, and then automatically revoking access once the time expires.
- Protect high-value assets: You can identify your most critical data by determining which would pose the biggest threat to the organization if it were compromised. Employee and personally identifiable customer information, intellectual property and trade secrets are some common examples of high-value assets that can be safeguarded by limiting access only to those who need it to do their jobs.
- Automate workflows: Manually performing tasks like creating accounts, changing passwords and provisioning access for each employee is impractical and prone to error. IAM tools can help automate tasks that can reduce help desk requests, increase productivity, decrease costs and ultimately make the organization more secure. Automation also simplifies logging, auditing and reporting on a regular schedule for compliance requirements, eliminating one of IT departments’ most time-consuming manual tasks.
- Conduct regular audits: Conducting routine audits of access logs will allow you to track user activity, ensure users still have the appropriate permissions for their role, and identify and disable inactive accounts.
Lastly, think about what applications your IAM solution will have to work with. Determine which apps your organization’s employees and customers use and which are most critical to track, then compare them to the applications each IAM vendor supports.
Continuously strengthen your security with IAM
As distributed systems become the norm, the security perimeter grows more fluid. Partners, contractors, vendors, customers and employees can access your organization’s network from anywhere. IAM allows you to control user access regardless of where they are or what device they’re using, ensuring they can use the resources they need without jeopardizing your organization’s security.
See an error or have a suggestion? Please let us know by emailing splunkblogs@cisco.com.
This posting does not necessarily represent Splunk's position, strategies or opinion.
Related Articles
About Splunk
The world’s leading organizations rely on Splunk, a Cisco company, to continuously strengthen digital resilience with our unified security and observability platform, powered by industry-leading AI.
Our customers trust Splunk’s award-winning security and observability solutions to secure and improve the reliability of their complex digital environments, at any scale.


