
Digital Resilience Pays Off
Download this e-book to learn about the role of Digital Resilience across enterprises.
Greetings and happy new year!
 In early December 2019, I published a blog on the upcoming DoD Cybersecurity Maturity Model Certification (CMMC), “Getting a Head-start on CMMC.” This post covered a range of topics including: what CMMC is, who it impacts, why it matters for US National Supply Chain Security, negative implications for organizations that are unprepared for the certification, and recommendations for organizations to proactively drive readiness ahead of their first CMMC audits.
In early December 2019, I published a blog on the upcoming DoD Cybersecurity Maturity Model Certification (CMMC), “Getting a Head-start on CMMC.” This post covered a range of topics including: what CMMC is, who it impacts, why it matters for US National Supply Chain Security, negative implications for organizations that are unprepared for the certification, and recommendations for organizations to proactively drive readiness ahead of their first CMMC audits.
Since my last post, the DoD Office of the Under Secretary of Defense for Acquisition & Sustainment (OUSD (A&S)) has continued to mature the draft CMMC guidance and incorporated feedback received from their “CMMC listening tour.” As a result, I wanted to highlight some of what has changed for readers out there who are proactively crafting a plan of action to achieve their Cybersecurity Maturity Model Certification later this spring.
During an information session with an industry trade association on Dec. 16, 2019, Director of Cybersecurity Maturity Model Certification Policy, Stacey S. Bostjanick, offered insights into how OUSD A&S is thinking about the initial organizations that will be subject to the CMMC, perspective on a phased roll-out more generally, and clarified the scope of the CMMC as it applies to systems, system boundaries, and organizational infrastructure writ large.
During this industry outreach session, Ms. Bostjanick mentioned that “the original plan was to have most companies [CMMC] certified by Fall [2020].” Ms. Bostjanick went on to explain that, DoD’s thinking about the roll-out has evolved and they are now “focusing on [approximately] 1500 [priority] companies going through the process this year,” with additional companies going through the certification process in 2021 and so on.
All large Federal Systems Integrator (FSI) maintain a complex set of systems, boundaries, overlaps, interdependencies, corporate infrastructure and industrial control systems (e.g., building automation and control networks and ICS product/capability development labs). This inherently presents an understandably daunting challenge for organizations seeking to present a clear and auditable evidentiary package that substantiates their cybersecurity maturity. In response to a question from an industry representative highlighting this challenge, Ms. Bostjanick offered the following concise and easily understandable perspective on certification scope and system applicability:
“CMMC Level 1 applies to the entire company and covers basic cyber hygiene. If organizations will be handling Controlled Unclassified Information (CUI), the minimum CMMC requirement will be Level 3. [The] Level 3 certification applies to the network that the CUI will transit.”
Ms. Bostjanick went on to provide an additional example, stating that “if an organization uses an enterprise-wide email system and CUI will transit that email system, then that email system will have to be CMMC Level 3 as well.”
As a point of clarification, OUSD A&S has stated that, once CMMC v1.0 is published, the level of certification required for each procurement will be specified in the corresponding RFIs and RFPs upon release.
These certification requirements will provide industry with clear expectations on the CMMC levels that must be obtained prior to contract award on these solicitations. Prime contractors should also be aware that they must flow down the appropriate CMMC requirements to any subcontractors that they would seek to utilize for delivery on contracts containing Cybersecurity Maturity Model Certification prerequisite requirements
Stated More Concisely:
One other interesting note to be aware of relates to the concept of contractor “products.” OUSD A&S recently added a clarification to their website stating that “Phase 1 of the CMMC [roll-out] only applies to the contractor's networks and does not apply to their products.”
My general observation here is that this is a helpful general distinction. Having said that, my immediate second thought is that this introduces considerable subjectivity.
Read as: Proceed with caution, this creates room for misinterpretation and disagreement on the precise definition of what a “product” is.
During the US Chamber of Commerce industry outreach I mentioned earlier, Ms. Bostjanick shared some insights into ongoing activities that the CMMC team was still driving forward towards completion.
Most notably, Ms. Bostjanick shared that the CMMC team was “working feverishly to stand up the industry accreditation body [in January 2020].” As a reminder, this body will be responsible for accrediting the CMMC 3PAOs (C3PAOs) who would then be responsible for assessing contractor CMMC packages, issuing recommendations for CMMC accreditation levels to DoD, and conducting audits of contractor networks within 12 months of accreditation.
Ms. Bostjanick provided additional insight into the roll-out timeline by sharing that “by mid-June 2020, DoD will issue RFIs for programs that are coming up in the Fall that will [contain] CMMC requirements.” When these solicitations are released, contractors should expect to see the required CMMC levels for contract award clearly specified.
If you’re still reading, hopefully you are thinking about what can be done today to ensure that your organization is well-prepared to achieve a Cybersecurity Maturity Model Certification level that positions your organization to win an “unfair share” of upcoming contracts. I offered quick-start recommendations in my last post on the CMMC to help you begin preparing. Please take a look if you need help getting started.
My last post also mentioned that my development team was working on a CMMC-specific solution that we would release shortly after CMMC v1.0 is released. Given that we are already into January, I’ll offer a little more detail on how we are thinking about the solution, the current development status, and when we expect to make it generally available to the public.
When I think about the “Splunk for CMMC” solution itself, I’m viewing it through two perspectives: the Contractor perspective (primary) and the C3PAO perspective (secondary).
From the Contractor perspective, I envision organizations leveraging the solution to automate the self-evaluation of their cyber security maturity, identification of gaps, and generation of the bulk of their technical evidentiary package for C3PAO auditors to use in their evaluation and Cybersecurity Maturity Model Certification audit and accreditation process. There is, of course, the obvious additional benefit of leveraging this solution for continuous monitoring of security posture with respect to the controls put forward in the CMMC guidance as well. In either case, a Splunk for CMMC solution consultant can help organizations ensure that they are effectively and efficiently ingesting the appropriate data sources, in an automated fashion, to ensure a robust and comprehensive cyber security maturity package is available for C3PAO auditors.
From the C3PAO perspective, auditors will benefit from the standardized user interface / presentation of the data across systems and sub-organizations (this also makes auditor training easier and more scalable). This standard presentation of the data will ultimately make the evaluation and audit of contractor packages more efficient and consistent across accreditations.
My development team is actively building out the technical search, visualization, and create/read/update functionality into the Splunk for CMMC beta solution.
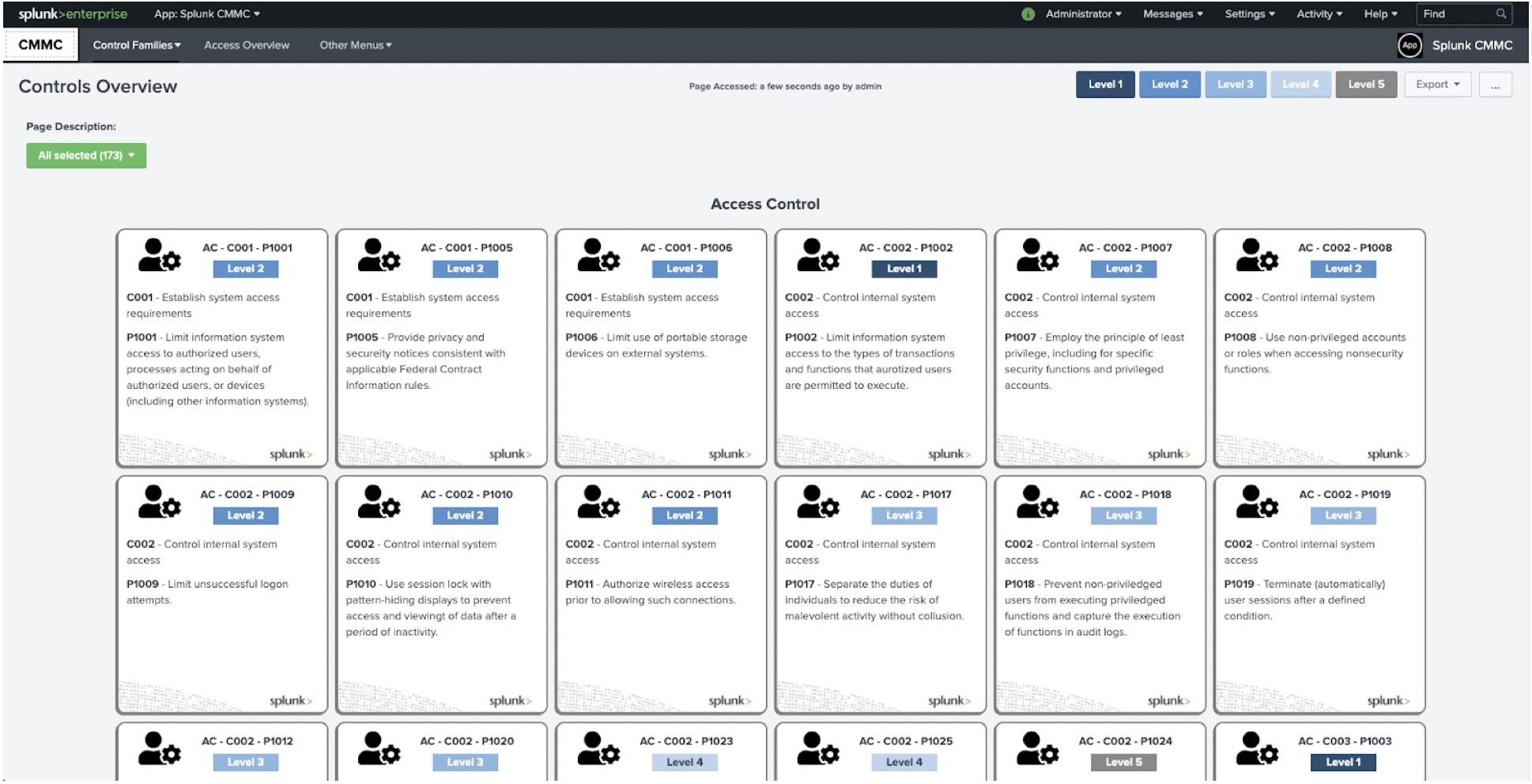
Given the overly long length of this post and since a picture is generally work a thousand words, I’ll share a couple of pictures of the current beta application here:
Fig.1: Preliminary Control Overview Dashboard Layout
Fig 2: Preliminary Dashboard for Practice 1211 - Sensors Responsible for Malicious Code Detection
If you are in the greater Washington D.C. area, please plan to join us at our annual Public Sector-specific GovSummit event at the Marriott Marquis in Washington DC on March 4th 2020.
I will be providing a live pre-launch overview and demonstration in one of the GovSummit breakout sessions and my development team will be available for deep dives and technical Q&A on all of our Public Sector-specific solutions throughout the day in the exhibit area.
The Splunk for CMMC solution will become generally available following the official launch webinar, tentatively slated for late March 2020. Stay tuned here for more details on the launch webinar and build progress once the CMMC v1.0 is officially released.
Thanks for reading, reach out to us at splunk_cmmc@splunk.com if you have questions or need help.
We’ll be hosting a Splunk for CMMC Solution Webinar on March 25, 2020 where we'll discuss how the CMMC solution is built on Splunk Enterprise and can be applied to your existing Splunk deployment, or used in conjunction with a new deployment, to accelerate your path to certification. Don't miss out and register here — happy Splunking!
----------------------------------------------------
Thanks!
Anthony Perez
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.