Find the Ultimate Truth in the Wire. Even the most granular logs are not enough to be the truth

SIEMs are being deployed in more organizations today from larger to smaller enterprises. It is playing a critical role in consolidating most of the security events, so it can detect symptoms of various infrastructure security problems.
SIEMs are good in detecting problems by scanning the surface of data for key indications like how burglary alarm works for your homes. It is a basic security measure you would put into your infrastructure to detect the first line of intrusion. In order for SIEMs to do this, there are common ways of processing data to map different technologies into predefined data structures so it could apply contextual rules or conditions to detect different patterns of behaviors. This requires normalizing the data to support common correlations rules.
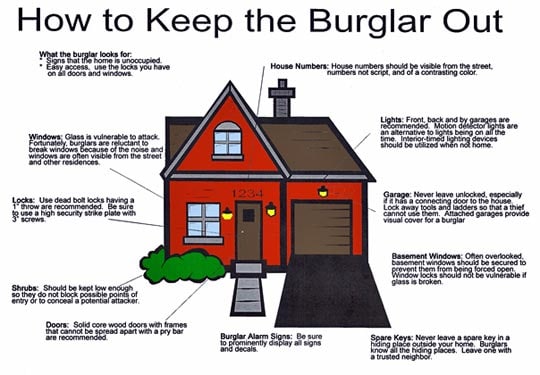 But the problem is having these fundamental measures sometimes doesn’t necessarily reduce the chance of being broken into because often times we are dealing with adversaries who knows these data limitations in SIEMs. Especially root-cause attacks from these adversaries with a definite answer on what happened can be difficult because many of organization don’t have the technology that could validate the intrusion and/or don’t have the skills to do it. It’s like if your house is burglarized and you get an alert for a window that was broken open, but you don’t know what is missing until you go through all the things you have in the house to figure out what’s missing. So now you install sensors in the rooms to detect movement to get a better idea of what to look for in SIEMs. It would be equivalent to implementing higher fidelity rules. Even if you have SIEMs that are tuned to get high fidelity alerts, many times your security operations still may not know what has happened in the infrastructure.
But the problem is having these fundamental measures sometimes doesn’t necessarily reduce the chance of being broken into because often times we are dealing with adversaries who knows these data limitations in SIEMs. Especially root-cause attacks from these adversaries with a definite answer on what happened can be difficult because many of organization don’t have the technology that could validate the intrusion and/or don’t have the skills to do it. It’s like if your house is burglarized and you get an alert for a window that was broken open, but you don’t know what is missing until you go through all the things you have in the house to figure out what’s missing. So now you install sensors in the rooms to detect movement to get a better idea of what to look for in SIEMs. It would be equivalent to implementing higher fidelity rules. Even if you have SIEMs that are tuned to get high fidelity alerts, many times your security operations still may not know what has happened in the infrastructure.
Data in traditional SIEM just lacks the details
SIEMs operates in the layer of data typically normalized, where the details of information get stripped off. This limits security analysts from getting detailed context on attacks. SIEMs operate in the layer of data typically normalized, where the details of information got stripped off.
Even the detailed sources of logs are preserved, it isn’t enough to be the source of truth
Logs definitely provide more context since it preserves the original details and give more granular traces of activities but still, it's just another layer of service/application information. It’s like having better hints but still not the answer.
Validation is often left out
While the logs tell good stories they are not the absolute answer. Further, validation is impossible most times because the majority of security operations have no data to go deeper.
In cybersecurity, there is not debate on defining “network/packet forensics” as the source of truth, it would be a synonym for DVRs in the home or physical security.
But, how could having the source of truth at your fingertips change how you defend against the adversaries? What could it mean to have the most powerful SIEM on the market closely integrated with full network/packet forensics capability?
Introducing Splunk Enterprise Security (ES) with full network/packet forensics capability at your fingertips. What are you getting with these combinations?
AUGMENT SECURITY DATA SOURCES FOR MORE GRANULAR MONITORING
Full packet/wired data provides additional dataset, and is in CIM compliant, if you don’t have all the luxuries to invest in a variety of sensor technologies; like proxy, firewalls or IDS, IPS that would feed ES. A great benefit that will pump events into ES, so ES can detect higher fidelity alerts.
- This screen shows Stream rules to monitor HTTP populates CIM Web data-model as well as ability search the stream HTTP raw events.
ULTIMATE POWER TO DEFINE ABSOLUTE RULES
You can now alert on PCAP decoded information, allowing rules to be created from network to application layer conditions. A great example would be monitoring SQL transactions to a critical database server from the wire. How about application layer messages in corporate applications? Also, there is a great use of wired data in looking at DNS activities. This opens the door for many additional use cases that will make your infrastructure more secure.
Also, additional enrichment like threat Intel, other domain data source correlations will significantly enhance the fidelity of detection.
- Alert detected on a host visiting a malicious domain (from threat intel) and downloads suspicious assets like PDF, word or even exe.
ABILITY TO GO DEEP TO FULLY VALIDATE THREATS
With ES and Stream integration, notables are associated with captured PCAP artifacts, so it can be easily accessed, in the context of the particular alert or incident. This allows the power of deep dives at your fingertip, so you don't waste time looking for massive amounts PCAP data specifically related to the event.
- Download/View PCAP and the download extracted file option is added to the notable event “Actions” drop down allowing single click access.
A single click downloads the PCAP to your desktop and opens in Wireshark. If there are any attachments or downloads like PDF, DOC, EXE; these are separately extracted (reassembled), so if you think there are important classified documents sent via SMTP, you will be able to open them to see what that file was in order to validate the content.
- When the “Download PCAP file” button is pressed, Wireshark session is opened on the local desktop automatically.
- When the “Download extracted file” button is pressed, the PDF downloaded from a malicious site is opened in preview app for information validation. It is extremely handy for insider threat use-case, for information security use-cases.
If you have Splunk ES, don't miss out on what ES and Stream 7.1 integration can do for you!
----------------------------------------------------
Thanks!
Young Cho
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




