Detecting Malware and Watering Hole Attacks with Splunk UBA
You may be surprised to learn that a particular malware is responsible for data theft in over 20% of financial institutions and other verticals in 2019.
 Watering hole attacks involve a web server that hosts files or applications where the website or files on the site become weaponized with malware.
Watering hole attacks involve a web server that hosts files or applications where the website or files on the site become weaponized with malware.
While recent news cycles have shined a spotlight on ransomware and crimeware, malware is not a new concept. In fact, malware has been around for decades, and it is still an effective way for cybercriminals to wreak havoc.
Watering Hole Attacks in the Wild
Watering hole attacks are typically targeted attacks. An attacker will compromise a web server or web service and implant a malware-laden file, in hopes that their intended victim or victims will access it. Once the trap is set, the visitors to the website or service are infected, and often their devices are also compromised. When a device has become compromised, keyloggers, crimeware, and command-and-control (C2) connections can be leveraged to steal data or even control the device remotely.
How Can UBA Help Detect Watering Hole Attacks?
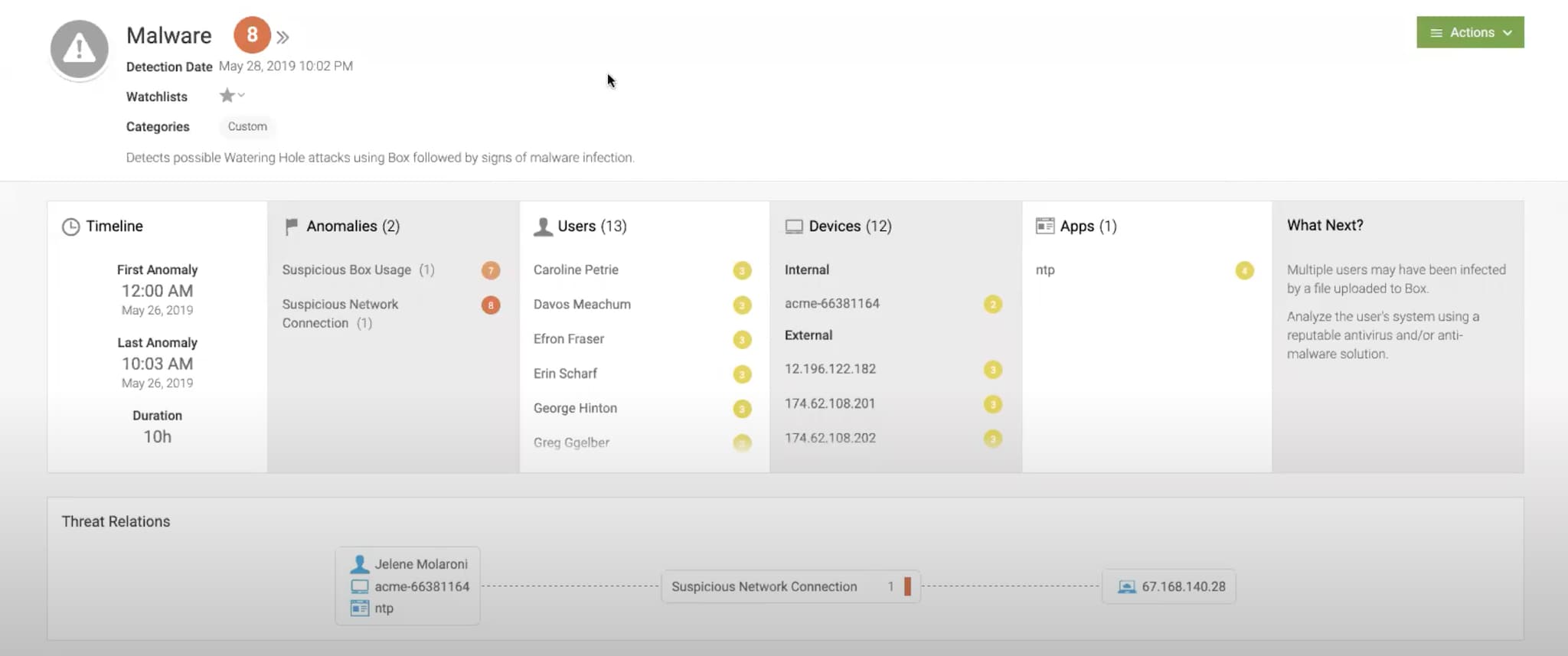
Splunk User Behavior Analytics (UBA) is able to monitor websites and cloud-based repositories such as Dropbox to look for examples of watering hole attacks. Splunk UBA can detect files uploaded to these environments from IP addresses outside of the corporate IP blocks, which users and devices were involved in the attack, and which device was responsible for uploading the weaponized content in the first place.
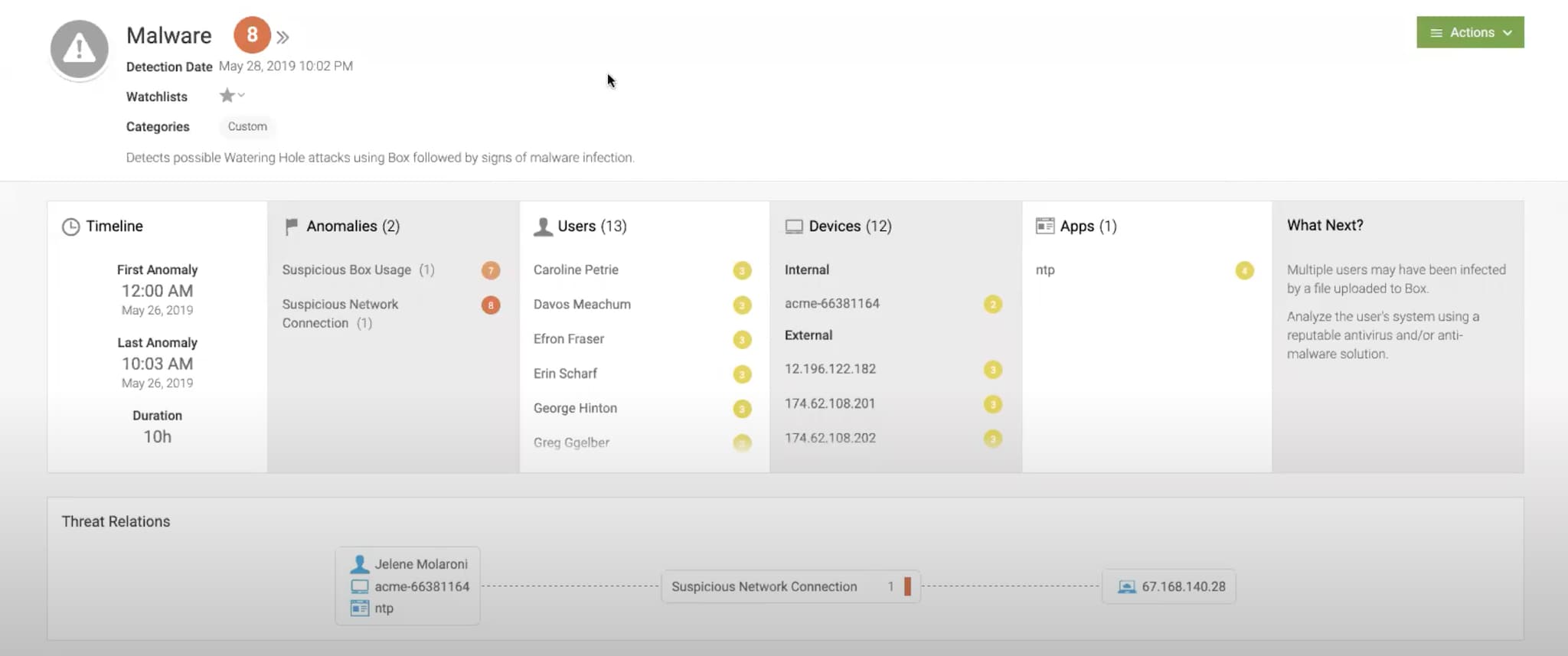
Splunk UBA leverages unsupervised machine learning in order to detect anomalies, and then automatically aggregates those anomalies into a threat. This threat is then sent to the Security Operations Center (SOC) to feed into Splunk Enterprise Security as a notable event for security analysts to review and remediate.
Since Splunk UBA works autonomously, without any human intervention for detecting these threats, the risk of missing these attacks is greatly reduced.
See It In Action
Check out this guided tour to learn how to:
- Secure against unknown threats through user and entity behavior analytics
- Harness the power of UBA to detect insider threats
- Accelerate threat hunting
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




