Denmark’s Largest Utility Company Accelerates Incident Response

A s Denmark’s largest power, utility and telecommunications company servicing 1.5 million customers, Norlys understands the need for fast response to security alerts. When the company first started, the Norlys security team built their own log analytics and incident response capabilities from the ground up. This homegrown approach presented challenges, including manual workflows, too many repetitive tasks and difficult-to-maintain processes.
s Denmark’s largest power, utility and telecommunications company servicing 1.5 million customers, Norlys understands the need for fast response to security alerts. When the company first started, the Norlys security team built their own log analytics and incident response capabilities from the ground up. This homegrown approach presented challenges, including manual workflows, too many repetitive tasks and difficult-to-maintain processes.
Automate with Security Orchestration, Automation and Response
We spoke with Tibor Földesi, security automation analyst at Norlys, to hear why Norlys chose Splunk Enterprise Security (ES) as its SIEM tool, and Phantom as its security orchestration, automation and response (SOAR) platform.
Földesi told us that Splunk Enterprise Security has helped Norlys to combat threats with actionable intelligence.
“If we have suspicious activity on an endpoint, we go to that specific dashboard in ES and can see all of the movements,” says Földesi. “ES lets you see everything going on in your environment to find the bad guys.”
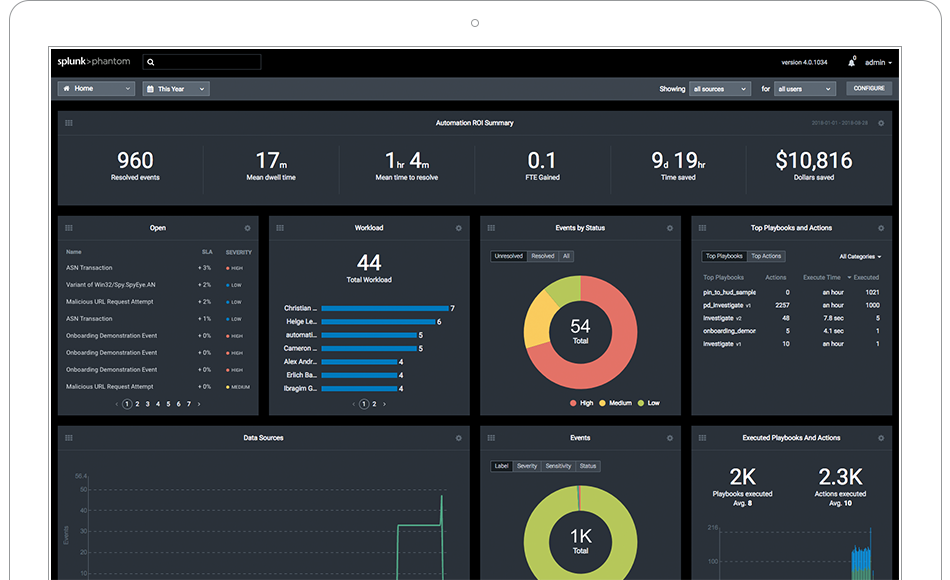 After seeing the benefit of ES — and receiving support from the experts at Splunk Professional Services — Norlys learned they could get even more immediate value out of ES by automating opening tickets between systems with Splunk Phantom. With Phantom, Földesi first created a specific playbook for responding to an antivirus alert. Upon receipt of the alert, the Phantom playbook automatically triggers an endpoint detection and response (EDR) tool to analyze the endpoint for suspicious activity, retrieve the quarantined file, submit it to a malware sandbox for detonation and analysis and then generate a report for the security analyst.
After seeing the benefit of ES — and receiving support from the experts at Splunk Professional Services — Norlys learned they could get even more immediate value out of ES by automating opening tickets between systems with Splunk Phantom. With Phantom, Földesi first created a specific playbook for responding to an antivirus alert. Upon receipt of the alert, the Phantom playbook automatically triggers an endpoint detection and response (EDR) tool to analyze the endpoint for suspicious activity, retrieve the quarantined file, submit it to a malware sandbox for detonation and analysis and then generate a report for the security analyst.
“This capability in Phantom saves us 35 hours per week — about five hours per day,” says Földesi. “In Denmark, that’s almost one full-time employee.”
With Splunk implemented in day-to-day workflows, Norlys security analysts have been able to save time and money, and better protect their organization.
“Automation is changing how teams traditionally use a SIEM,” says Földesi. “We heavily rely on Phantom and Enterprise Security. They complement each other in a very good way and allow us to improve security capabilities for the entire company.”
See the full story on how Norlys accelerated incident response to save 35 hours every week with Splunk Phantom here. If you’re eager to try Phantom, download the free community edition.
----------------------------------------------------
Thanks!
Olivia Courtney
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




