Zoom in on Security in a Remote Work World

Our world has been turned upside down by COVID-19. Whether it's strategically planning our grocery run decontamination process, or trying to keep the kids quiet for even one single moment while on a conference call — things are different. One very evident difference is the change in the way we meet with each other. And one technology enabling this change is Zoom.
From a security perspective, this uptick in the use of Zoom brings to light some concerns and situational awareness that may previously have been paid much less attention. Fortunately, Splunk recently announced Splunk Remote Work Insights (RWI) designed to provide real-time visibility into disparate, remote-work-enabling systems, like VPN, Microsoft 365, Okta, and, you guessed it, Zoom. Even better, getting data in with Zoom and the JWT Webhooks modular input couldn't be easier.
 Better still, this data allows security practitioners to answer a number of the basic security questions that organizations have when it comes to Zoom. Meeting information like meeting duration, meeting attendees, and scheduled meeting dates can all be mined and used for security use cases and operational dashboards. However, some questions remain unanswered, chief among them are:
Better still, this data allows security practitioners to answer a number of the basic security questions that organizations have when it comes to Zoom. Meeting information like meeting duration, meeting attendees, and scheduled meeting dates can all be mined and used for security use cases and operational dashboards. However, some questions remain unanswered, chief among them are:
- Are the meetings being secured properly?
- How can we take proactive measures to educate and enforce meeting security?
Enter the Zoom App For Phantom
 The Zoom JWT Webhooks provides a very low friction way to bring a great deal of rich meeting data into Splunk, but it only tells part of the story. To get the rest, we must use the Zoom API, which thankfully provides everything you could ever want to know about your meetings.
The Zoom JWT Webhooks provides a very low friction way to bring a great deal of rich meeting data into Splunk, but it only tells part of the story. To get the rest, we must use the Zoom API, which thankfully provides everything you could ever want to know about your meetings.
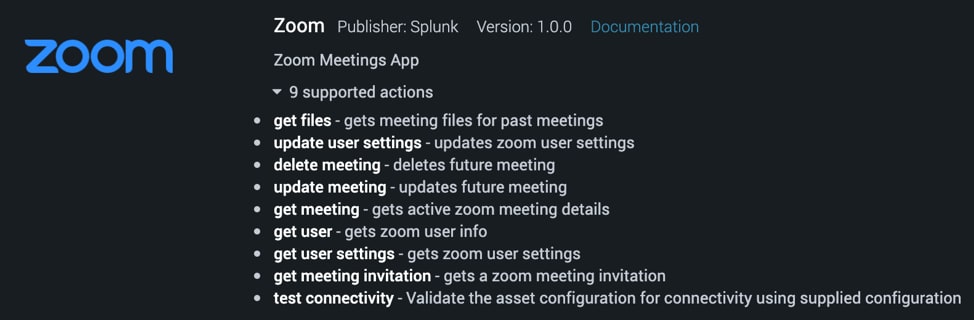
The new Zoom App for Phantom provides a simple, user-friendly interface to this API to facilitate a variety of useful actions:
Meeting Enrichment
With only a meeting ID, the app can identify if scheduled meetings or meetings in flight are password protected and have the "waiting room" functionality turned on. You can eEven get a transcript of files transferred during meeting chat.
Meeting Modification
Upon identifying meetings that aren't adhering to security best practices, meetings can be updated to require a password and enable the "waiting room" feature. Or, taking a more draconian approach, meetings can be removed from the schedule.
User Enrichment
Find out more about the hosts of meetings, and specifically what settings they have enabled.
User Setting Modification
Update user accounts to enforce meeting passwords for scheduled meetings, instant meetings, and personal meeting instances (PMI).
That's Great, But How Do We Operationalize It?
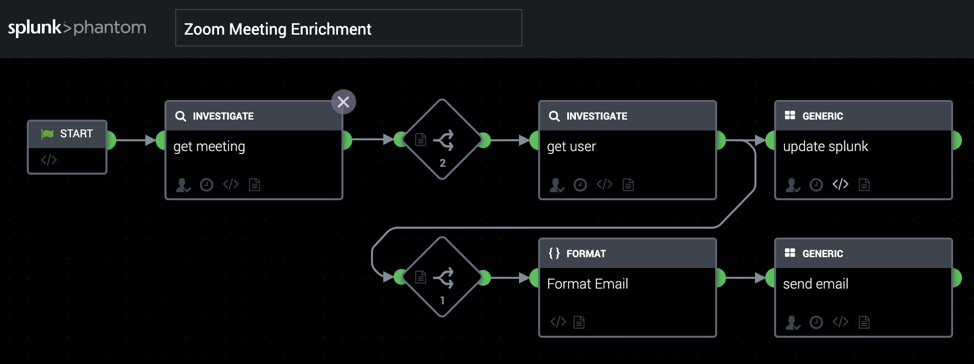
We've released a detailed operationalization guide covering how to configure the Zoom App for Phantom and how to configure the polling queries necessary to ingest the Zoom meeting create, start, and end events from Splunk. Additionally, we've published a series of playbooks to get you started.
 Scheduled Meeting Response
Scheduled Meeting Response
Find out if newly scheduled meetings are effectively protected. Provide options to enforce protection and send notification emails to the meeting host, informing them of the changes and/or educating the m on the dangers of unprotected Zoom meetings. Enrich Splunk with additional meeting details.
In Flight Meeting Response
Find out if currently running meetings are effectively protected. For unprotected meetings, send notification emails to the meeting host educating them on the dangers of unprotected Zoom meetings. Enrich Splunk with additional meeting details.
Update User Settings
Update user accounts to enforce meeting passwords and waiting rooms. Send a notification to the user of the changes made. Enrich Splunk with additional meeting details.
Meeting Post-Mortem
Find out what files were transferred during meeting chat. Send a log of meeting files to the meeting host, and enrich Splunk with the data.
Where Do I Start?
We’ve provided all the assets you need, as well as detailed instructions on installation and configuration on the Phantom Community Github.
New to Phantom? We’ve got you covered. Download our free, Phantom Community Edition to get started.
We're excited to bring these to you and looking forward to hearing about the novel and creative use cases you end up implementing. Happy (and safe) Zooming!
----------------------------------------------------
Thanks!
Ian Forrest
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




