Better Detections and Cloud Coverage with Splunk Enterprise Security 6.4
Security teams are in a difficult position: they continue wrestling with persistent problems, such as overwhelming alert volumes and staff shortages, while confronting new ones driven by the abrupt shift to remote work. For instance, attaining real-time, deep visibility into cloud environments may have been on SOC roadmaps before 2020, but the capability is now a pressing need.
With Splunk Enterprise Security 6.4, we’re proud to bring you new features that solve critical problems — old and new — for your SOC.
 Streamline Your Detections and Investigations with Risk-Based Alerting
Streamline Your Detections and Investigations with Risk-Based Alerting
SOCs receive an overwhelming volume of alerts. What often gets overlooked, though, is that “alerting issues” don’t exist in a vacuum: if your security team has an alert fatigue problem, it likely also has an alert suppression problem; an alert abandonment problem; an analyst turnover problem; and a mean-time-to-respond problem, among others. An alerting problem is a security posture problem.
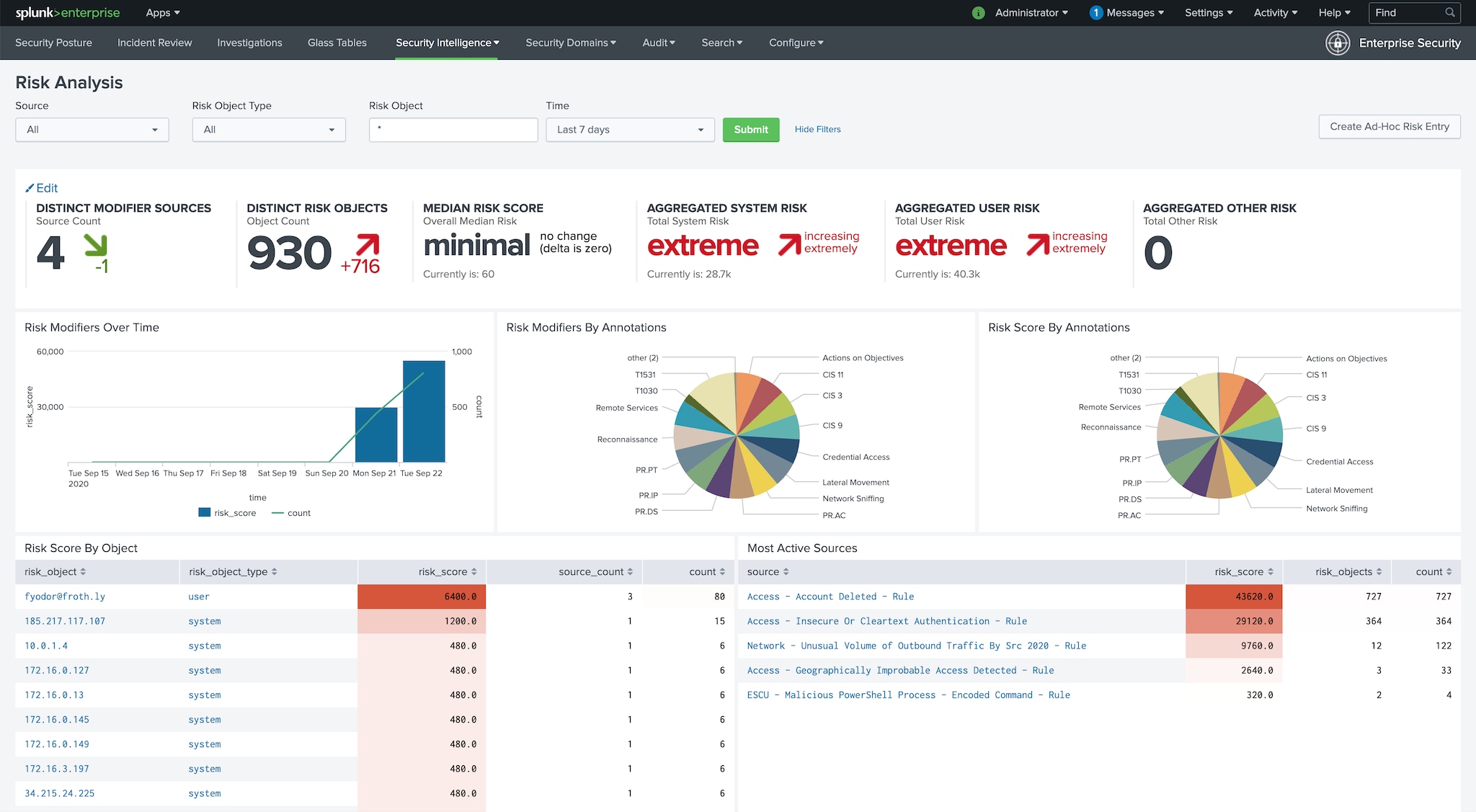
In Splunk Enterprise Security 6.4, we’re introducing new features that help customers take a new, attribution based approach to alerting. This approach, which we call risk-based alerting, helps you radically reduce alert volumes, giving your analysts back hours each week to focus on real threats, not rule tuning.
This new paradigm centers on attributing risk — risk scores, relevant cybersecurity framework components, or custom risk attributions — to users and systems, and generating alerts when risk and behavioral thresholds are exceeded, e.g., when a system’s risk score exceeds 100 or when multiple Mitre ATT&CK tactics are observed across a single entity. Our customers who’ve already adopted this attribution-based approach have seen a 60-80% reduction in alert volumes, along with other benefits such as:
- Increased True Positive Rates
Along with a dramatic reduction in overall alert volumes, customers report a significant increase in their true positive rate. One customer’s true positive rate increased from below 10% before implementing risk-based alerting to over 30% within a few months of implementing this new approach. Another customer reported a true-positive rate increase from below 50% to above 90% in just a few months.
- Detection of More Sophisticated Threats
Several customers reiterate how risk-based alerting not only decreases alert volumes and increases alert fidelity, but also that it helps them detect threats they would struggle to detect with traditional correlation search approaches. This is because risk-based alerting takes events that would traditionally yield isolated, low fidelity alerts and places them in context of related risky behavior that may indicate a threat. The result is the ability to detect low-and-slow attacks that you previously may have missed.
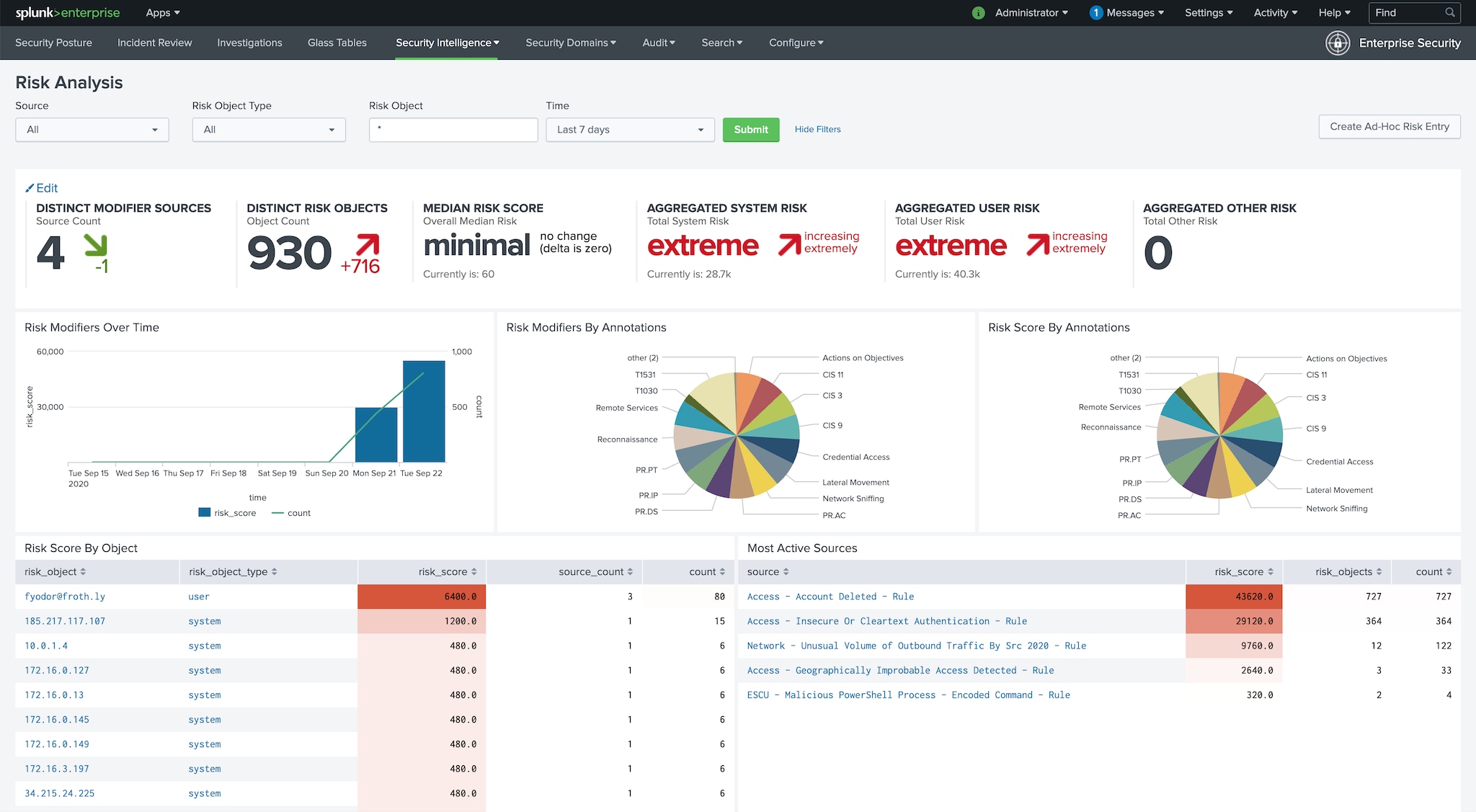
- Tighter integration of Security Frameworks Into Day-to-Day Operations
Enhancements to our user interface allow you to easily annotate detections with their relevant Mitre ATT&CK tactic, CIS 20 or NIST control, or elements from a custom risk framework. This allows you to embed the value of cybersecurity frameworks into your detections, taking them from valuable concepts to foundational to your team’s operations. It also allows you to quantify your coverage of frameworks, e.g. how many tactics your detections cover, and allows you to track your progress toward your desired future state of framework coverage.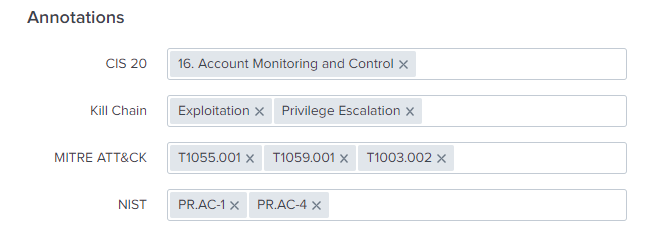
- Faster Investigations
Risk-based alerting has helped several customers reduce their investigation times from days or hours to minutes. This is because risk-based alerting surfaces the ‘story’ at the outset: when a SOC analyst sees an alert generated using this approach, she can see each risk event that contributed to that alert in the alert’s Risk Message. Analysts no longer need to spend hours manually associating events — risk-based alerting aggregates all relevant events that contributed to an alert and presents them to analysts front and center.
The underlying collection of attributions from which risk-based alerting drives detection and investigation improvements has broader applications in the SOC. Threat Hunting, Threat Intelligence, Automation & Orchestration, and many other security functions benefit greatly from those attributions. Spunk is excited to detail those benefits in more depth in the near future.
To learn more about risk-based alerting, be sure to watch the .conf20 session, “Streamlining Analysis of Security Stories with Risk-Based Alerting,” by Haylee Mills from Charles Schwab, as well as the session “Full Speed Ahead with Risk-Based Alerting (RBA)” by Splunkers Jim Apger and Kyle Champlin.
 Seamlessly Bring Cloud Data Into Your Existing Detections and Investigative Workflows
Seamlessly Bring Cloud Data Into Your Existing Detections and Investigative Workflows
We know that our customers are moving more data to more clouds. While Gartner forecasts an 8% drop in global IT spend in 2020, it projects a 19% increase in public cloud expenditures. Additionally, in another recent Gartner survey of public cloud users, 81% of respondents said they are working with two or more cloud providers.
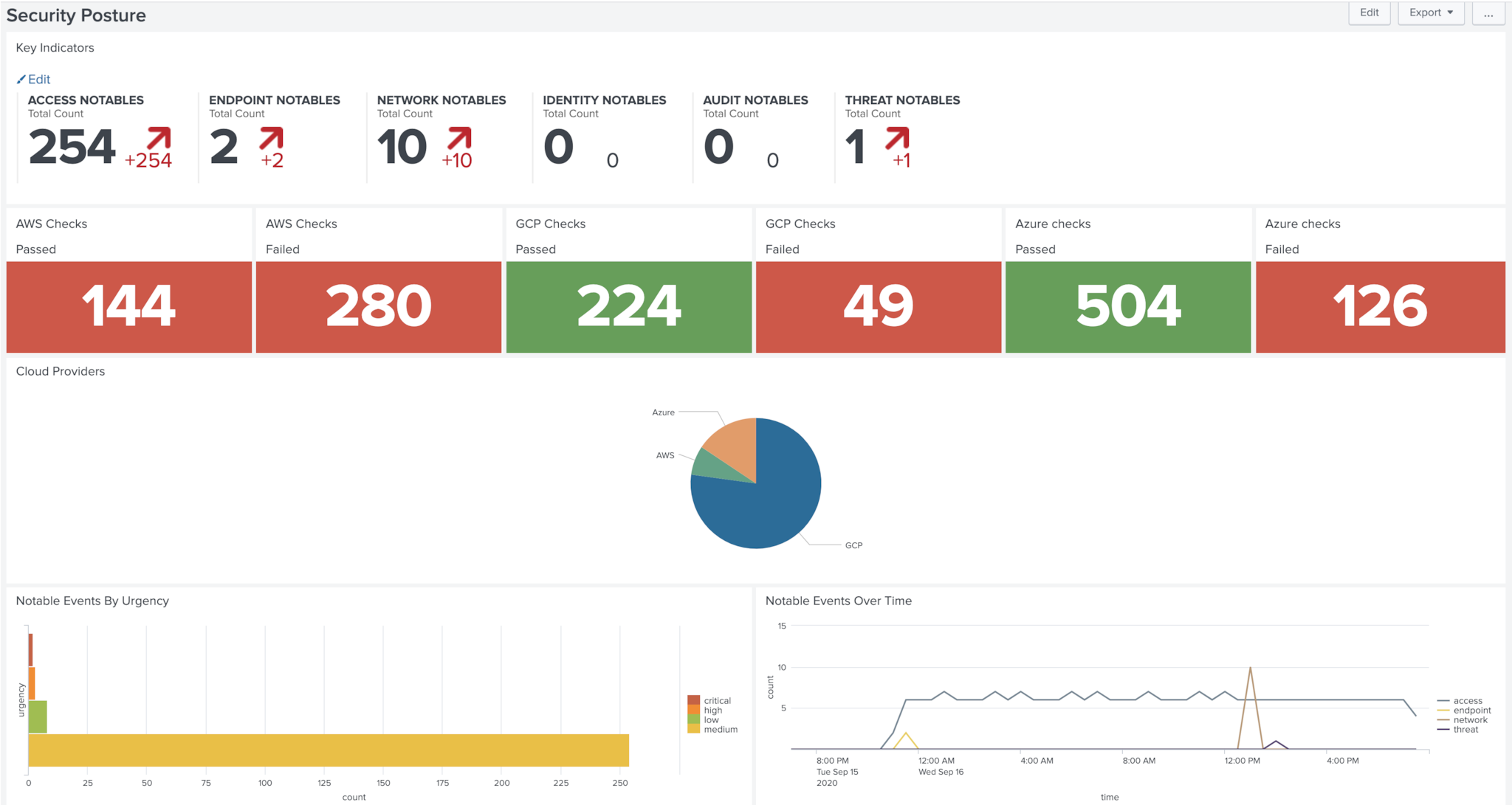
With Splunk Enterprise Security 6.4, we make it easy for our customers to onboard and analyze their data from AWS, Google Cloud Platform, and Microsoft Azure. All you need to get started are the latest free technical add-ons for these providers and Splunk’s free Common Information Model add on. Key cloud security monitoring benefits of this release include:
- Easy Onboarding of AWS, GCP, and Azure Assets and Identities
Now, to get assets & identities from these cloud providers into Splunk, just specify the cloud platform and the necessary SPL to execute the lookup will generate automatically for you. Your cloud assets and identities will quickly and cleanly populate your Splunk asset and identity tables going forward.
- Pre-Built Detections for AWS, GCP, and Azure
We’re also providing out-of-the-box detections for these cloud providers across authentication, network traffic, and configuration changes, as well as other data from your cloud providers, such as CSP native alerts. By mapping these cloud providers’ data models to Splunk’s Common Information Model, we’re making it seamless for you to bring cloud data into your existing detections and investigative workflows.
These features reinforce Splunk’s commitment to being a cloud neutral data platform. Splunk Enterprise Security is developed to monitor your data no matter the cloud provider, giving you the confidence to choose an IT infrastructure and application provider that makes the most sense for your business.
To learn more about the benefits of multicloud environments and how Splunk can help you secure them, check out our Brief Guide to a Secure Multicloud Environment.
----------------------------------------------------
Thanks!
Alex Spiliotes
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




