A Day in the Life: Secrets of a Top Splunk Security Analyst

At Splunk, we’re proud to employ some of the top security analysts in the industry. On any given day, they’re investigating security incidents, triaging alerts and identifying threats so our systems and data — as well as those of our customers — remain secure.
But what, exactly, do security analysts do? And what are some of their biggest challenges? We sat down with Risi Avila, a Staff Security Specialist at Splunk, who shared his experiences and some well-earned wisdom to those following in his footsteps.
Why did you become a security analyst?
Twenty years ago, I was working in Belize at the country’s only telecom company. We had a team of four who were working as internet technicians, and we ran the internet for the entire country. We had a bunch of dial-ups, no DSL. One of the DNS servers got hacked — someone dumped a bunch of software and malware onto the system, and we didn’t know it until we got a report from someone in the U.S. We had to bring in a consultant who triaged the breach. It turned out that one of the packages wasn’t up-to-date, which allowed the hackers to break into the DNS server.
After that, we decided that we needed to have someone focus on security. I volunteered. For a year, I was the designated security person, investigating how hackers would break in. It was like playing cops and robbers on the internet and I found that intriguing. But the deeper I got, the more I realized I didn’t know a lot about protocols and how they worked. I had an associate degree in math, but I decided to go back to school for a bachelor’s degree in networking technologies at DePaul University in Chicago. After that,I went to graduate school at DePaul for information security and continued to hone my skills in networking, telecom and security operations.
What is a typical day like for you as a Splunk analyst?
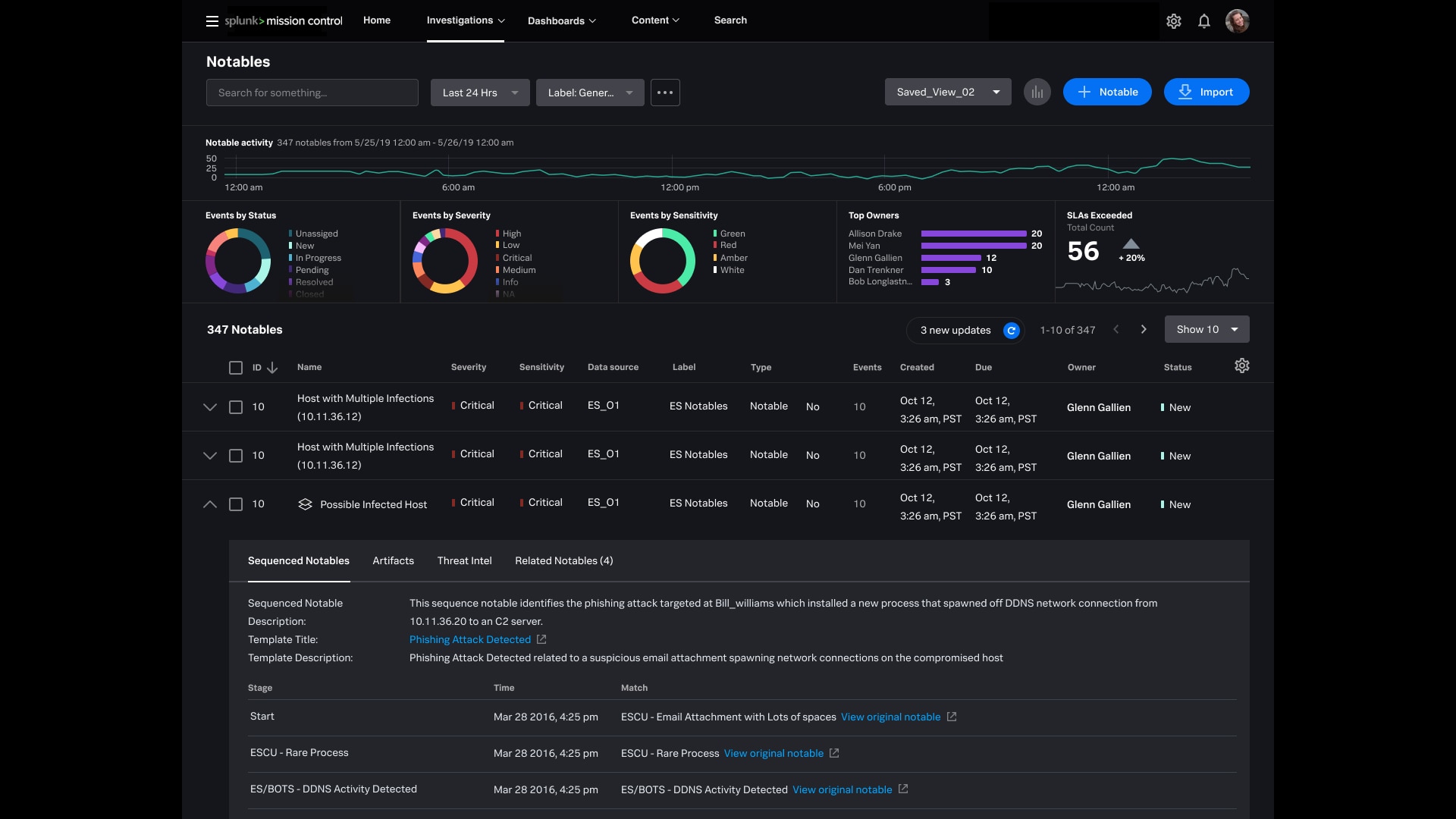
Half the day, it’s cyber operations and operational tasks, and making sure systems are up and performing. I also make sure those systems are feeding the SIEM properly and the system is available. The other half of the day, it’s a combination of triaging alerts, dealing with notable events and correlation rules, and ensuring that we addressed the most critical incidents.
What excites you most about your job?
For me, it’s the constant change and the constant interaction. It’s understanding how the business works from a technical perspective — you have to understand the business to effectively protect it. You also have to be a good generalist. Belize is a much smaller country, and you have to do a lot of things to survive. In security, you can’t just focus on databases or firewalls, you have to know a lot about many different things. Later in your career, you can specialize. But knowing a little about a lot excited me the most.
 What are some of your biggest challenges? How do you overcome them?
What are some of your biggest challenges? How do you overcome them?
Cybersecurity is a three-legged stool — people, process, technology. Typically, the biggest problem you have is people — being able to avoid situations where it’s up to people to address things on their own. Automation is definitely helping with that. With Mission Control, there’s a checklist of things you should do if an alert comes in. The process is approved and repeatable — analyst I does the same thing as analyst II. But people are the weakest links in cybersecurity. And the greatest challenge is making sure people follow proper procedure.
What is the most surprising thing about your job?
Cybersecurity has only become more and more important. And now that everyone is working from home, it’s become that much more important for individuals as well as companies. The attack surface is enormous. But often companies miss the basics. In Belize, we have a saying that translates to, “you have to dance in your yard before dancing in someone else’s yard.” It’s recognizing you have to take care of the basics first. If you’re not doing the basics, you’re going to get owned.
Do you have any advice for aspiring security analysts?
Try to understand what you’re doing before you do it. Test, test and test some more. Once you put it into production, make sure that what’s coming into your SIEM and feeding those alerts are high value, high fidelity and actionable. If they’re not actionable, you’re just wasting your time.
 Ready to channel your inner analyst? Download "How to Uplevel Your Defenses With Security Analytics" and discover how to:
Ready to channel your inner analyst? Download "How to Uplevel Your Defenses With Security Analytics" and discover how to:
- Strengthen your defenses with real-time monitoring, user behavior analytics, security orchestration, automation and response (SOAR).
- Maintain and evolve SOC rules to better detect and respond to the changing threat landscape.
- Execute best practices for investigations, and automate effective response actions based on recommended guidance.
----------------------------------------------------
Thanks!
Oliver Friedrichs
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




