“Are We Secure?” Lessons Learned From The CISO Of A Leading Saudi Bank

This week we have been in Dubai for Gartner’s Security Risk and Management Summit, where leaders across the middle east region came together to prepare their organizations for the future.
“Are We Secure?"
Rasha M. Abu AlSaud, SVP – Chief Information Security Officer, from a Leading Bank in Saudi Arabia explained how they overcame the challenge to report up to senior management, when they ask that tough question “Are we secure?”

The Challenge
Back in 2012 after the Saudi Aramco hack, a major shift happened within Saudi Arabia. Rasha mentioned the difference in attitude before the hack and now – forcing cybersecurity to mature, and a need for further capabilities to be established to keep digital services secure as well as ensure customer trust and satisfaction. To do so, Rasha’s team knew that many answers were hidden in their log data, but their SIEM solution only provided limited visibility as it wasn‘t designed for the volume and variety of data generated. The operations team maintaining the SIEM had concerns each time an additional system was on-boarded, due to the potential impact on performance.
The Evaluation
In 2014 Rasha and her team didn‘t want to just purchase the market leader in the region to refresh their program. Her team took their time, analyzed their requirements, defined use cases, and researched the market for the best fit. As the team came across Splunk, they got excited about the ease of onboarding new data, scaling the system and the ability to apply simple and advanced analytics, just like a clever Google search.
The Rollout
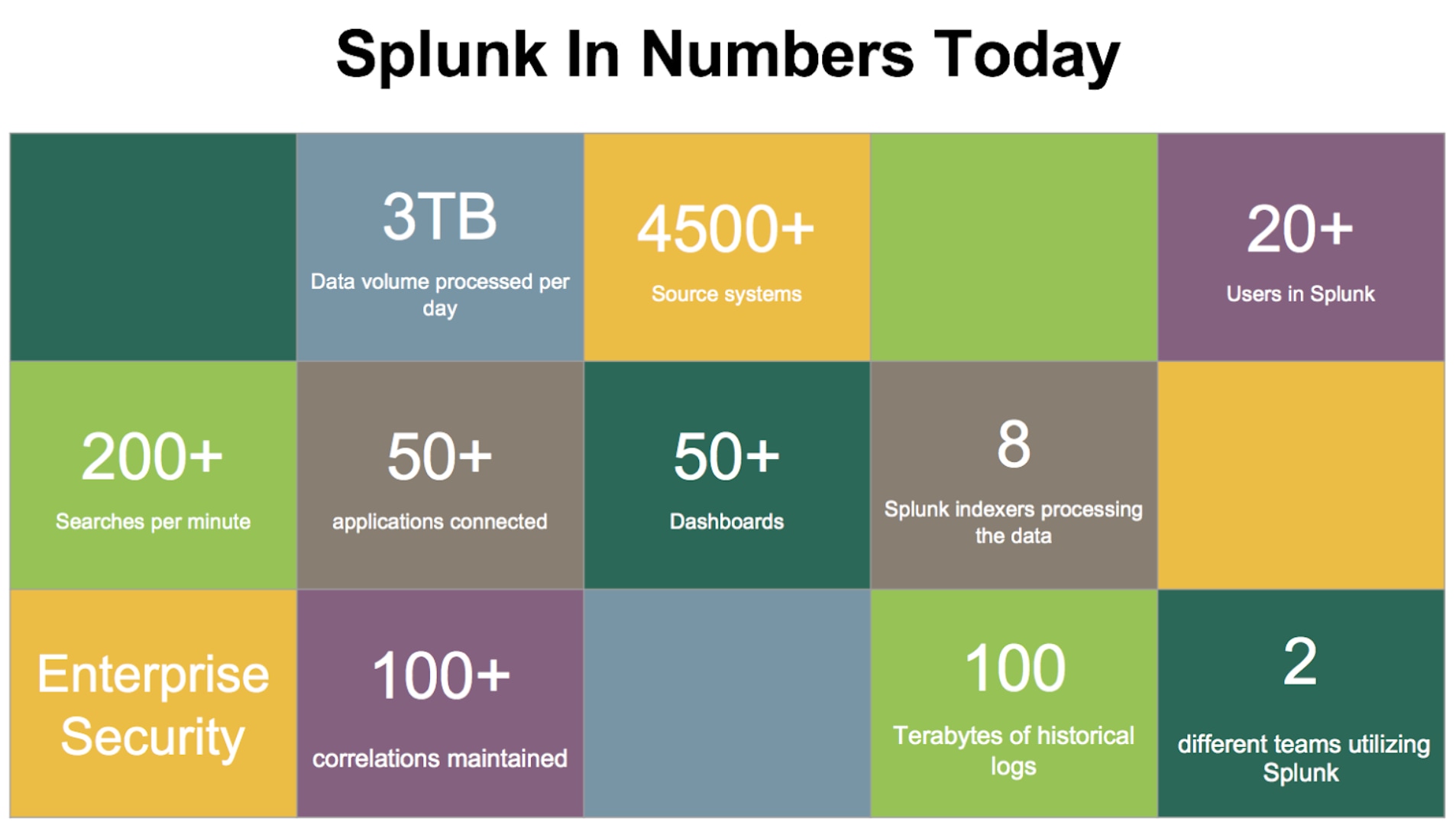
Within a year the team went through Splunk training, established a scalable Splunk architecture, and on boarded 100% of their network infrastructure devices and all Server OS data. The bank got rid of their old SIEM and multiple other departmental log repositories.
One year in, they have completely changed the way they worked. Conversations are either “We’ve seen this in Splunk” or “It’s not in Splunk, so we don‘t know”. Whatever threat comes up, whatever tactics are used - Rasha‘s team is now able to answer the question: “Are we secure?”
The team didn’t stop at finding success for security. Knowing that there is so much more they can do with the data, they started to onboard machine data generated from their business applications. In a digital banking world, where your credit card can be printed on demand, there‘s a huge benefit for the business to gain visibility, utilize this data and deploy security monitoring at the core of the business. Rasha gave the following advice to the CISO community at Gartner: “The business understands the value you bring to them with application logs“
While understanding application data requires subject matter expertise - Rasha’s team mastered that along with the business and it brought the two teams closer together.
Collaboration with IT-Operations
Rasha encountered a mind-changing experience as her organization faced a major outage. The Head of IT reported that the issue was due to an application and not within the infrastructure. Rasha asked him how he knew so quickly, and where he takes his confidence from. His response? “I looked in Splunk!” Within a matter of hours, they could identify the root cause and solve the interruption, a problem which previously would take days.
Lessons learned
As usual in IT projects – there are also challenges along the way. In the early stages, the team struggled to find the right technical resources available in the region. Rasha recommended to start with onboarding OS Level Logs – the rest will then come. Dividing the onboarding into phases allowed her team to have time to digest the events reported, and allowed time for stabilizing the platform. Most importantly; before onboarding an asset, evaluate what is being logged so you start with the right configuration.
Thanks a lot to Rasha for sharing her expertise, and to her extended team for their open mindset to do things differently, enabling them to become data-driven security specialists, supporting the business and contributing to corporate priorities.
Related Articles
About Splunk
The world’s leading organizations rely on Splunk, a Cisco company, to continuously strengthen digital resilience with our unified security and observability platform, powered by industry-leading AI.
Our customers trust Splunk’s award-winning security and observability solutions to secure and improve the reliability of their complex digital environments, at any scale.


