Launching Websites Rapidly, Without Compromise

 In the past few weeks, financial firms and governments have had to build and launch websites in a hurry — for a multitude of reasons including the emergency loan programmes that have been backed by various governments around the world including the USA and Europe.
In the past few weeks, financial firms and governments have had to build and launch websites in a hurry — for a multitude of reasons including the emergency loan programmes that have been backed by various governments around the world including the USA and Europe.
In 2020, launching a website should be a simple matter, but when that website represents the front door to a bank and people are depending upon it to facilitate funding for their business then the expectations are high — and the chances of the system being abused are also high.
Firms hosting websites need to consider many factors:
- Will it scale to the anticipated number of users and beyond?
- Is it simple to use, and sympathetically designed?
- Has it been built using a common security methodology, and tested according to that framework?
- Is it susceptible to fraud or other types of financial crime, and how can it be defended?
- Can it be monitored in a comprehensive way so that the teams running it can troubleshoot issues?
The last point sounds obvious, but monitoring a website is harder than it sounds. The only way to really understand what has occurred during a visit to a website is by analysing the logs produced by the web server. These logs vary depending on the route that a user takes through the website, and keep on changing as new content is added. They do, however, include clues about how the site is being used, how long certain steps take, and if anything is taking too long. Those clues also include details of the device that a user has used to log in, the browser version used, and the IP address of the location where the user logs in from.
When analysed in context, these logs can give great insight into the legitimacy of a transaction, and can raise flags when something looks suspicious.
When the logs are analysed in conjunction with the data from the other aspects of the web environment, such as the database, application server, networks, hardware, etc., the tech teams can usually diagnose the root cause of a problem, detect a security breach, or investigate a potential fraudulent activity.
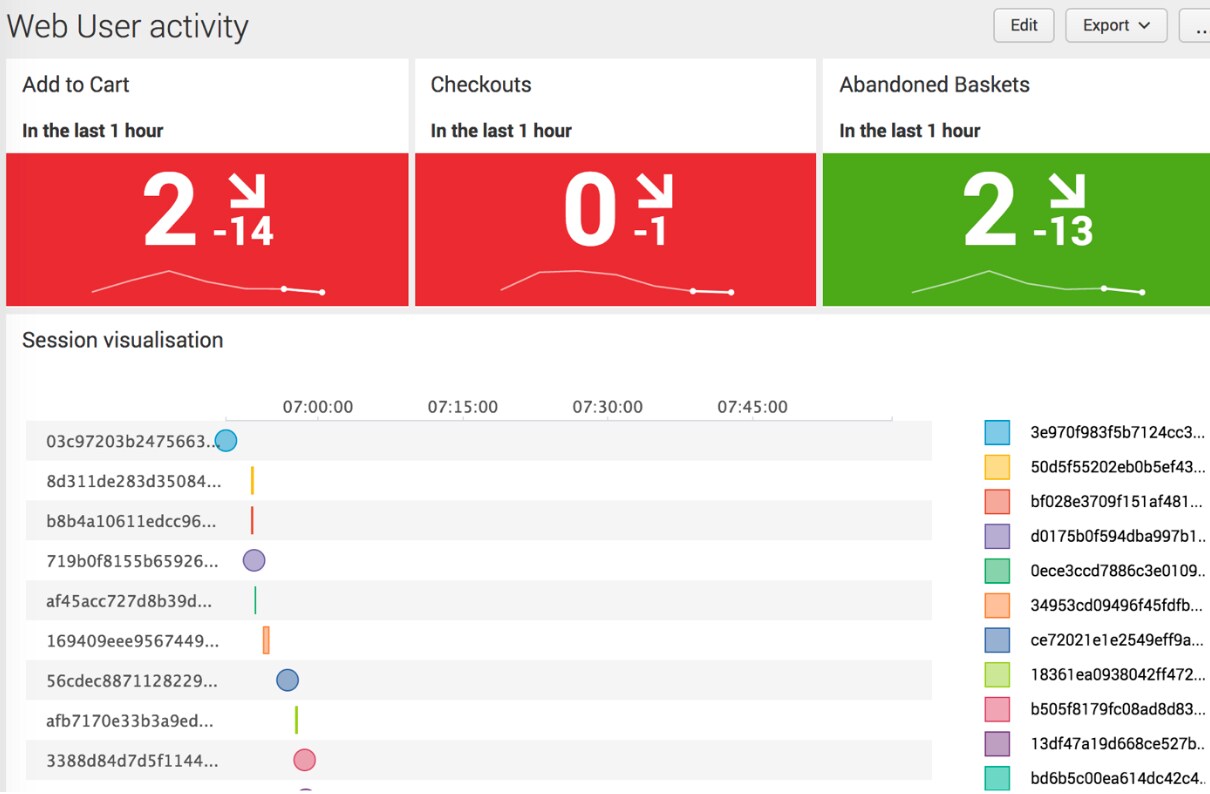 At Splunk, this is one of the core capabilities we are called upon to deliver for many of our customers, as monitoring logs in context with multiple other sources of information is precisely the type of problem that Splunk was designed to solve. It is why so many security teams depend on Splunk to rapidly respond to potential threats. It’s why Fraud teams use Splunk to investigate suspicious activities, and it’s why IT teams use Splunk to monitor the entire web environment from discs to firewalls.
At Splunk, this is one of the core capabilities we are called upon to deliver for many of our customers, as monitoring logs in context with multiple other sources of information is precisely the type of problem that Splunk was designed to solve. It is why so many security teams depend on Splunk to rapidly respond to potential threats. It’s why Fraud teams use Splunk to investigate suspicious activities, and it’s why IT teams use Splunk to monitor the entire web environment from discs to firewalls.
My colleague Johan Bjerke wrote this blog on the technical aspects of web analytics, and offers some suggestions on how all kinds of businesses can use Splunk to manage their websites, and keep them running effectively at scale.
Learn more about how you can monitor and protect your web environment in the links below:
- No Fighting in the War Room: Two Steps Reduce Mean Time to Resolution with Modern Monitoring
- Speed: A Security Analyst’s Best Friend
----------------------------------------------------
Thanks!
Duncan Ash
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




