Speed: A Security Analyst’s Best Friend

 In so many ways, speed is a security analyst’s best friend. From threat detection to containment to response – the faster you are, the more secure your business will be. It’s exactly why metrics like dwell time, MTTD (mean time to detect) and MTTR (mean time to respond) exist. It’s a barometer for the strength of your organization’s security, and a gauge of success for any good security team.
In so many ways, speed is a security analyst’s best friend. From threat detection to containment to response – the faster you are, the more secure your business will be. It’s exactly why metrics like dwell time, MTTD (mean time to detect) and MTTR (mean time to respond) exist. It’s a barometer for the strength of your organization’s security, and a gauge of success for any good security team.
But let’s face it – average dwell time, MTTD, and MTTR across the industry is awful. There are plenty of obstacles that slow down a security team.
Manually Resolving Alerts Takes Time
To start, the sheer volume of attacks is overwhelming. Each attack can spawn multiple security alerts that your team must investigate, and depending on the type of alert, can take 10, 30, upwards of 40 minutes to resolve each one. Also, it always seems like there’s too many alerts and not enough time to investigate them all. Many alerts will be left unattended, allowing threats to run rampant – unnoticed for months.
Juggling Siloed Security Tools Can Slow You Down
Some security teams use so many different security products in their arsenal that it introduces complexity and slows them down. Teams spend a lot of time juggling products that aren’t interoperable and manually correlating information between them. You can easily become “the guy in the swivel chair.” You pivot from product to product, monitor to monitor, trying to make sense of all the information hurled at you from each security tool. You have to navigate multiple management interfaces to tell each product how to take action and when.
Lack of Repeatable Processes Introduces Confusion
Lack of established security workflows, process, and standard operating procedures can also slow you down. This may seem like an obvious one, but many security teams still lack the mature, repeatable processes for handling a wide, diverse array of security incidents. Or perhaps processes exist, but solely on a word document on one analyst’s laptop, or in the pages of a paper playbook – a 500-page behemoth that looks like a Gutenberg Bible. None of this is very scalable.
I think you get the point.
So how do we eliminate these obstacles, or at least evade them, so that we can increase the speed, and in turn the strength, of our security? Security orchestration and automation from a SOAR (Security Orchestration Automation & Response) platform can help in a few ways.
Automation to Reduce Dwell Time, MTTD, and MTTR
First, it can help drastically reduce dwell times, MTTD and MTTR using automated investigations and automated playbooks. When a security alert is fired from your SIEM or any of your other security products, an automated playbook can launch immediately with no need for human interaction. This instantly eliminates the lost time between when an alert fires and when an analyst can start the investigation. It gets better – the playbook then automatically executes a series of actions to investigate and/or respond in seconds vs. minutes or hours if done manually. The typical 30-40 minute phishing investigation just took under a minute. Seconds and minutes could mean the difference between being “secure” and being "breached."
Address Every Alert, Every Day
Now that you can resolve each alert faster, it means that you can address vastly more alerts per day. The “64% of security tickets generated per day that are not being worked”1 can now be addressed. Alerts won’t be left unattended – cyberthreats will no longer get a free pass. With alert triage now under control, this will free up more time for your team to focus on mission-critical tasks. Your team can go from reactive to proactive, from overwhelmed to in control.
Coordinate Processes and Workflows Across Your Team and Tools
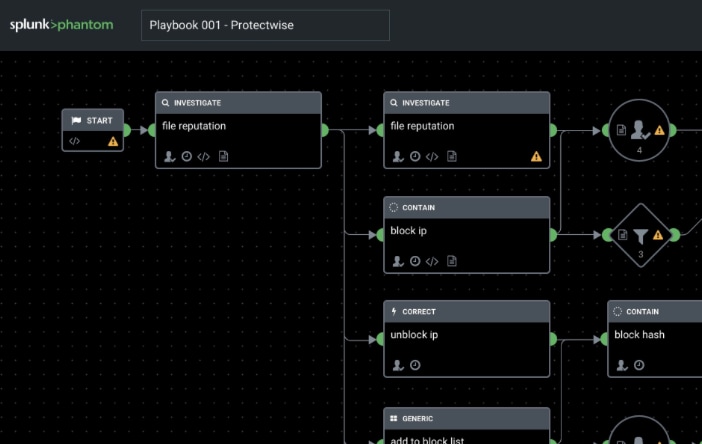 With a SOAR platform, your current security tools can start working together to resolve security incidents. Instead of static, siloed products working independently of each other, each security tool can actively participate in your defense strategy. Through APIs, a SOAR playbook can execute a series of actions – like detonating files, blocking web traffic, and quarantining devices – across multiple products in your security arsenal. You no longer have to pivot between multiple management interfaces when you respond to an incident. The SOAR platform does the work for you by codifying and coordinating complex workflows across your team and tools. And if your team didn’t have mature, repeatable processes before, deploying a SOAR platform will force you to establish them so that the platform can automatically execute actions, and know what workflow to follow.
With a SOAR platform, your current security tools can start working together to resolve security incidents. Instead of static, siloed products working independently of each other, each security tool can actively participate in your defense strategy. Through APIs, a SOAR playbook can execute a series of actions – like detonating files, blocking web traffic, and quarantining devices – across multiple products in your security arsenal. You no longer have to pivot between multiple management interfaces when you respond to an incident. The SOAR platform does the work for you by codifying and coordinating complex workflows across your team and tools. And if your team didn’t have mature, repeatable processes before, deploying a SOAR platform will force you to establish them so that the platform can automatically execute actions, and know what workflow to follow.
Splunk Phantom is a SOAR platform that can help you drastically increase the speed of your security operations in the ways outlined above. To see all of the different ways that Splunk Phantom can empower your team and help you decrease dwell time, MTTD, and MTTR, check out our interactive product tour.
[1] https://www.splunk.com/en_us/form/an-enterprise-management-associates-research-report.html
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




