Splunk SOAR Playbooks: TruSTAR Indicator Enrichment

 SOAR use cases come in all shapes and sizes, but almost all of them rely on threat intelligence to determine the risk posed by the various indicators in the event. Our two new community playbooks leverage Splunk Intelligence Management (previously TruSTAR) to gather intelligence about indicators and enable rapid manual response by an analyst within a single prompt. Unlike our other threat intelligence integrations, SOAR playbooks can pass all types of indicators into a single “indicator reputation” action in TruSTAR, which prevents the need to manage several different code paths in the playbook for different indicator types. TruSTAR also aggregates threat intelligence data from a wide variety of sources, such as open source, premium intelligence, and internal historical data, and produces a single normalized priority score for each indicator.
SOAR use cases come in all shapes and sizes, but almost all of them rely on threat intelligence to determine the risk posed by the various indicators in the event. Our two new community playbooks leverage Splunk Intelligence Management (previously TruSTAR) to gather intelligence about indicators and enable rapid manual response by an analyst within a single prompt. Unlike our other threat intelligence integrations, SOAR playbooks can pass all types of indicators into a single “indicator reputation” action in TruSTAR, which prevents the need to manage several different code paths in the playbook for different indicator types. TruSTAR also aggregates threat intelligence data from a wide variety of sources, such as open source, premium intelligence, and internal historical data, and produces a single normalized priority score for each indicator.
These two playbooks rely on the newly introduced playbook “input” and “output'' functionality in Splunk SOAR. The playbook, “threat_intel_investigate”, uses playbook tags and custom functions to identify all applicable enrichment playbooks in the event, and then it dynamically executes any appropriate input playbooks.
The input playbook “trustar_indicator_enrichment” is one example of an enrichment playbook that can be plugged into this use case. This tagging system allows playbook developers to quickly implement new modular enrichment playbooks without any changes to the “threat_intel_investigate” playbook. The only requirements are that the input playbook has an input that is a list of indicators and an output that provides a note to the analyst about the outcome of the enrichment.
The Playbooks
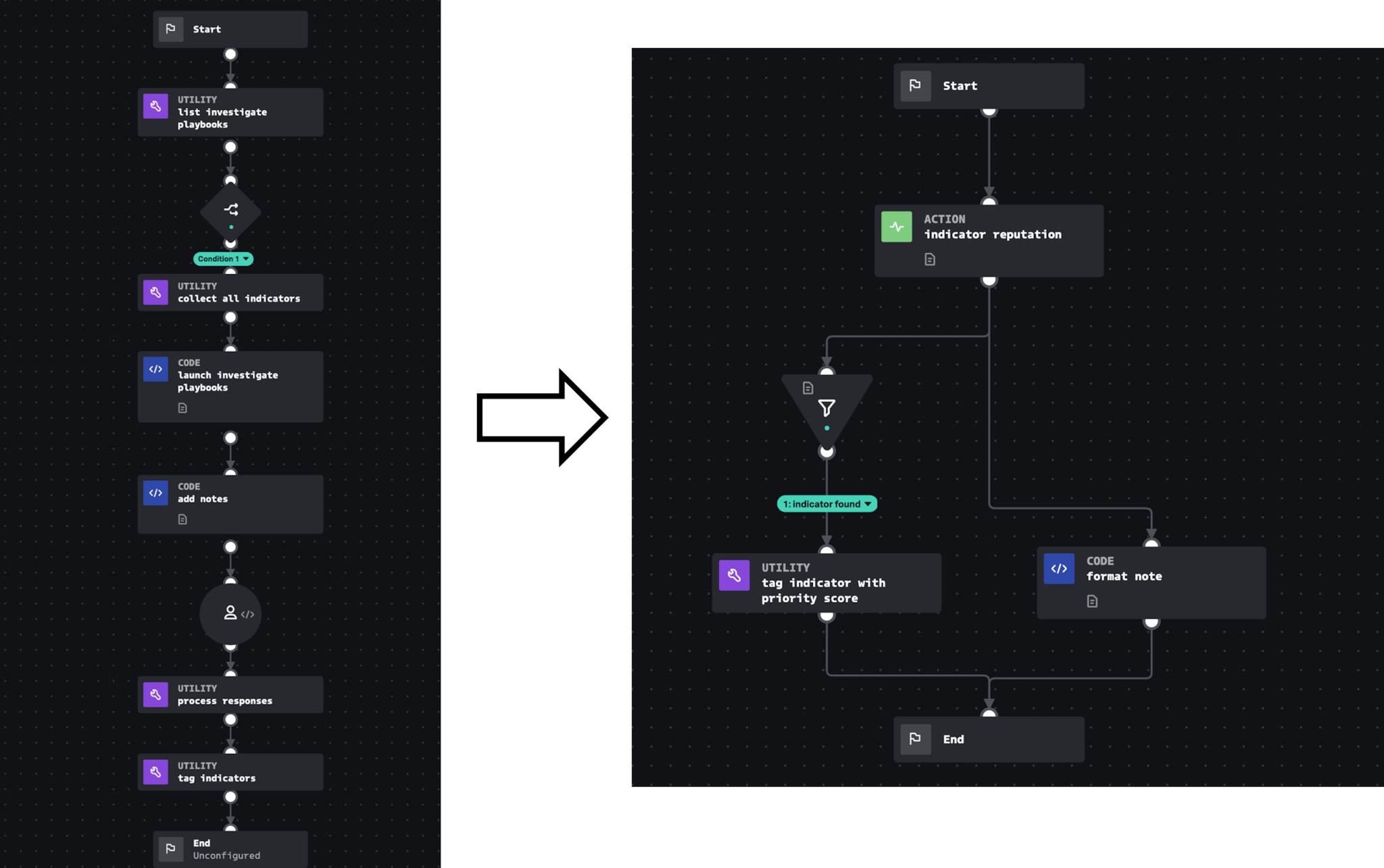
The main playbook is called “threat_intel_investigate”. This playbook lists all input playbooks with the tags “investigate” and “threat_intel”. Next, the custom function “indicator_collect” is used to gather all indicators in the source event. The output of that custom function is matched with the listed playbooks, and each eligible playbook with an indicator input type matching the collected indicators is executed with those indicators as input.
The second input playbook, “trustar_indicator_enrichment” is executed in this way, and within that playbook the TruSTAR Indicator API gathers reputation information about each indicator. From there, the playbook builds an analyst note and passes it back to the parent playbook as output. The main playbook creates a prompt for each indicator, displays the enrichment and normalized indicator score from TruSTAR, and gives the analyst the ability to manually tag each indicator appropriately based on the enrichment provided. After tagging the indicators, these playbooks do not take any further action, but additional playbooks can be used to read the indicator tags and take response actions.
See it in Action
Watch this video to see a demonstration of the running playbooks and a walkthrough of the key blocks in each playbook:
Deployment Steps
Step One: Find the appropriate Enclave GUID, client ID, and client secret within TruSTAR.
- Navigate to https://station.trustar.co/workflows/ and either create a new workflow with the desired intelligence sources, or select an existing one.
- From the expanded workflow view, press the “Get API Credentials” button.
- Copy the Enclave GUID, client ID, and client secret for use in the next step.
Step Two: Configure the TruSTAR app on Splunk SOAR.
- In Splunk SOAR, navigate to Home>Apps>Unconfigured Apps>Search for TruSTAR>Configure New Asset.
- Give the asset a name such as “trustar”, use the URL https://api.trustar.co, and provide the three unique values collected from TruSTAR for the Enclave GUID, client ID, and client secret.
- Save the asset and use the “Test Connectivity” button to ensure the asset is functioning.
Step Three: Configure and activate the parent playbook.
- Navigate to Home>Playbooks and search for “threat_intel_investigate”. If it’s not there, use the “Update from Source Control” button and select “community” to download new community playbooks.
- Click on the playbook name to open it.
- Resolve the playbook import wizard by selecting the newly created TruSTAR asset (if you used a different asset name).
- Set the labels to whichever labels the playbook should operate on.
- Set the playbook to “Active.”
- Save the playbook to the local repository.
Step Four: Activate the second playbook.
- Navigate to Home>Playbooks and search for “trustar_enrich_indicators”.
- Click on the playbook to open it.
- Save the playbook to the local repository (no changes are needed). The parent playbook only finds playbooks in the local repository, so copy the TruSTAR playbook to the local repository to allow the parent playbook to find and execute it.
Taking it Further
While these two playbooks provide a strong foundation for utilizing threat intelligence in SOAR, there are multiple configurations and subsequent playbook actions that can be done after they have been deployed. In addition to TruSTAR, other sources of intelligence such as an Alexa domain search, a PassiveTotal DNS history search, or an executable sandbox execution could all be useful to expand on the enrichment. Going beyond investigation, additional playbooks can be added to take the indicators that are marked for block and launch actions against them, such as a Carbon Black hash blocking playbook or a zScaler URL blocking playbook.
This blog is part of a series called “SOAR in Seconds,” where our distinguished Splunk SOAR experts guide you through how to use out-of-the-box playbooks and other features to automate repetitive tasks.
This article was co-authored with Steven Chamales, Product Manager, Splunk Intel Integrations.
----------------------------------------------------
Thanks!
Philip Royer
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.