The Easy Guide to Adding COVID-19 Context to Any Process

Recently, my colleagues Ryan Kovar and Lily Lee created TA-covidIOCs, which is a Splunk TA designed for ingesting IOCs related to COVID-19. Per usual, I immediately saw this as an opportunity to hitch a ride on their coattails and benefit from their hard work. The product of this effort is a Splunk Phantom playbook uncreativly titled, "COVID-19 Indicator Check."
The playbook is a simple, self-contained set of actions that takes MD5 file hashes, IPs, domains, and URLs as input. It then leverages the lookups in Splunk provided by TA-covidIOCs to determine if the indicators from the Phantom event are COVID-related. That's it.

Now, you may be asking yourself, "why not build it into a more common playbook or use case like Phishing Investigation?" Initially, I had intended to do precisely that. However, as I started putting hands on keys, a flood of different phishing use cases accumulated from four years of working in the SOAR space came surging back into my mind. Considering this some more, I realized that if I created a COVID-19 specific phishing playbook, it would likely only apply to a tiny subset of people. So the question was, how do I build the perfect playbook?
Building the “Perfect” Playbook
While disappointed that my initial grand designs for a playbook of epic proportions were dashed, this process did help me solidify two goals for this project:
- Make it for everyone; and
- Make it easily extensible.
Making It for Everyone
I thought long and hard about what "make it for everyone" means. At first, I thought it meant, consider all the possible things someone would want to do with it, and try to accommodate all of those things with tons of branching logic. And, that may have worked, but it's in direct conflict with my second goal of making it easily extensible, and it sounded like a ton of work. In self-serving fashion, I decided that making it for everyone means making it simple. The idea being, the fewer things that it actually does means there are fewer points for people to want it to do something differently. I also decided that making it for everyone means making it modular so that it can be seamlessly dropped into any process.
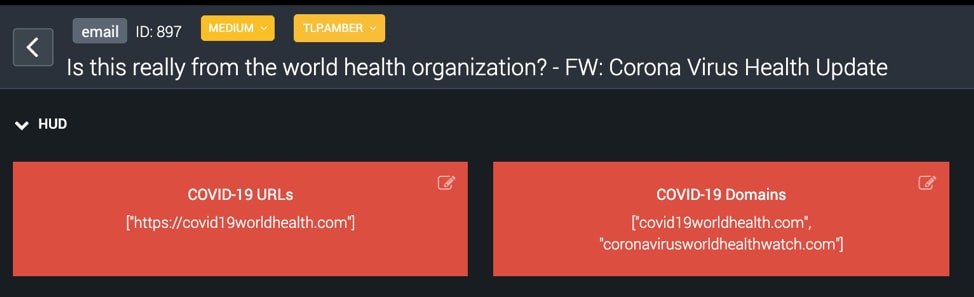
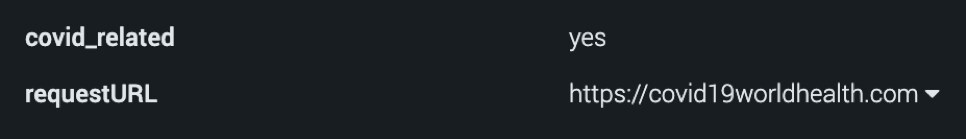
Immediately I knew that making it modular meant making it usable as a sub-playbook, which was no problem at all. I built the playbook to grab the event IOCs I wanted to lookup, query them against the Splunk COVID lookups, and add them to Phantom's HUD, providing immediate context for analysts reviewing the event. The trick, though, was making the results of the lookups available in the parent playbook to incorporate them into a broader process. To do this, I added a key/value pair to the Phantom artifacts from which the IOCs came - covid_related = yes. In so doing, I ensured that the results of the playbook could easily be used in the parent playbook as a mechanism for taking further actions. Goal number one accomplished!
Making It Extensible
As with the release of any solution, I knew the first question I would get about this playbook would be "why doesn't it work for such-and-such indicator type/field?" I also knew that "because I'm not a mind reader," would probably not be an acceptable answer. That's what drove "making it easily extensible" to be such an important goal.
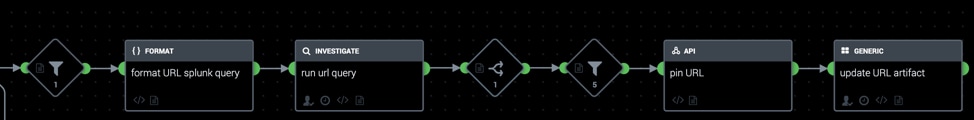
The good news was that with goal number 1 out of the way, I really didn't need to do anything else. Each indicator branch in the playbook (there's one for IPs, domains, URLs, and MD5 hashes) acts as a blueprint for extending the playbook to accommodate other IOCs. Thus, when you, dear reader, want to add a new indicator field that I didn't think of, you should be able to do so... easily. Goal number two accomplished!
Let’s See It in Action!
Finally, after all that, what did I decide to do? Take my modular playbook and incorporate it into a Phishing use case of course! The purpose of doing this was not to build the world's most all-encompassing Phishing playbook, but instead to act as a proof of concept that this modular playbook could easily be dropped into an existing process and provide immediate value. In keeping with the theme of doing as little work as possible I enlisted my good friend and colleague Tim Frazier to record a short video and demo of this in action:
How Can I Use It?
The "COVID-19 Indicator Check" playbook, including detailed instructions on how to operationalize it, can be found on the Phantom Community Github repo here.
New to Splunk Phantom? We've got you covered. Download our free Splunk Phantom Community Edition to get started.
----------------------------------------------------
Thanks!
Ian Forrest
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




