Splunk + Cisco = Endpoint Monitoring With No Added Installs

For the past four years, I’ve been on a crusade.
Not the medieval military kind of crusade that involved horses and armor in support of the Byzantine Empire. No, my crusade has been far less lethal than that—I’ve been crusading for the indexing of granular endpoint data in Splunk to support varied security detection use cases. I’ve spoken about this topic for four years running at our annual user conference, .conf. Because year after year, we're reminded that the endpoint is the weakest link in our defenses and where security incidents often begin.
However, speaking of Byzantine situations, Splunk security customers regularly tell us, “We know endpoint data is critical to the security of our organization, but we simply can’t get our endpoint administrators to consider any sort of additional agent technology across the fleet. So instead, we’ll go cry over bubble tea at the local poke bar and write cool Splunk searches on our iPhones. Against non-endpoint data.”
Okay, fine. When you come back from lunch, how about trying out a “plus one” technology? How about leveraging something that already may exist on your endpoints to gather—in near-real time—some very useful security-detection-enhancing information about ports, processes and traffic generated from your Windows and Mac endpoints? How could the Bobs say no to that?
Enter the Cisco AnyConnect Network Visibility Module, or Cisco NVM for short. NVM is a feature of Cisco’s AnyConnect VPN client and runs on Windows and Mac platforms. There are 130,000,000+ endpoints around the world running AnyConnect VPN—so there’s a good chance you run it in your organization.
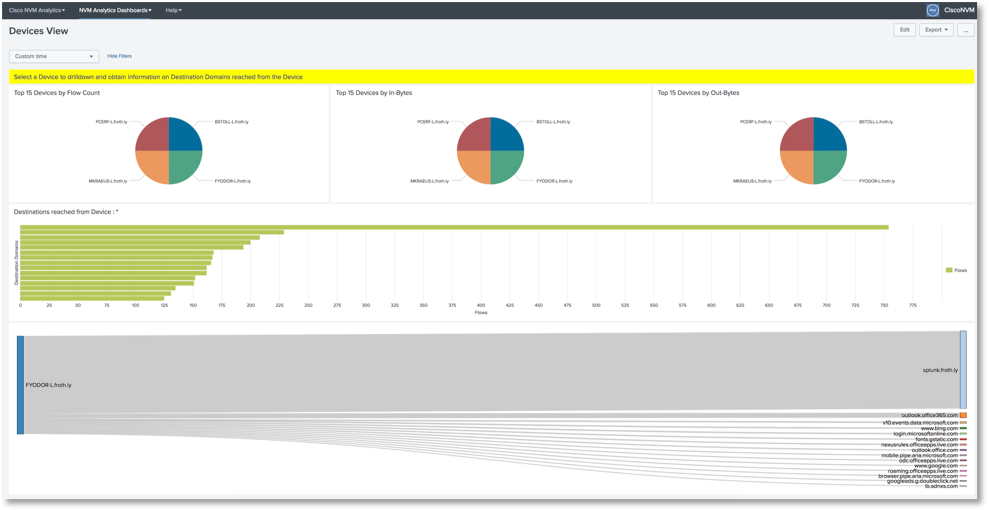
When NVM is enabled, it gathers IPFIX data from all traffic-generating processes on the system—regardless of whether or not the system has an active path to the NVM collector. When it does have a connection to a trusted network, it sends some pretty cool process execution details into your Splunk instance: process names, process hash values, parent process information, source and destination addresses and ports, and several other key bits of data. (Data collected during offline status is cached and delivered upon connection). It also regularly delivers endpoint inventory data into Splunk, so it can be used for asset tracking, too. There are lots of great details on NVM along with resource links in Scott Pope’s recent blog post "A Cisco & Splunk Security Integration Everyone Should Be Using," including this short video featuring Splunk!
We were interested enough in the power of NVM that we used it as a data source in our annual Boss of the SOC (BOTS) competition this year, which debuted at .conf18. BOTS is a major milestone for the Splunk security team every year, and we try and showcase new and interesting data sources in each new version.

Our fake homebrewing supply company at the heart of the BOTS competition, Frothly, has an almost-entirely mobile workforce based around the United States. Although many of their computing resources moved to cloud as the setup for this year’s competition, Frothly of course also has a legacy data center with some on-prem systems accessible via AnyConnect VPN. So we enabled NVM on AnyConnect and set up a Heavy Forwarder running the NVM collector (freely available in the Cisco NVM App for Splunk.) Within minutes, we had granular network flow data married to process execution data from all endpoints in our environment delivered efficiently into Splunk.
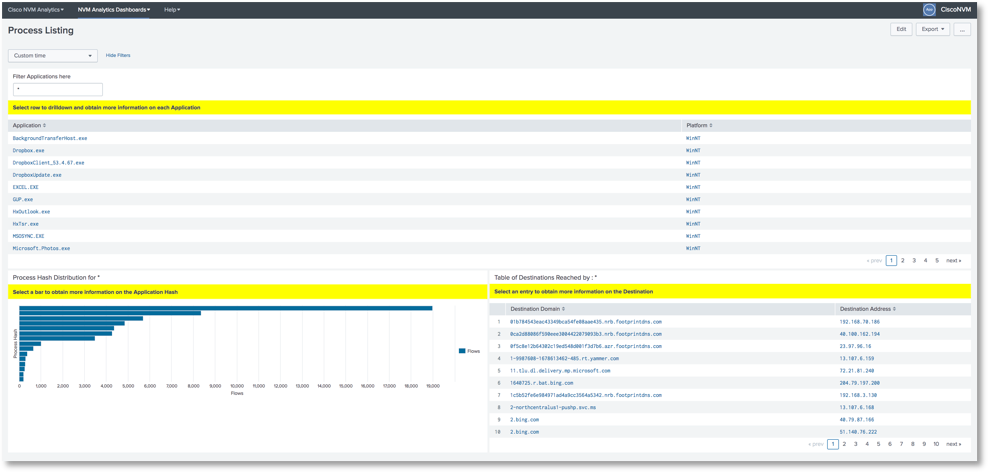
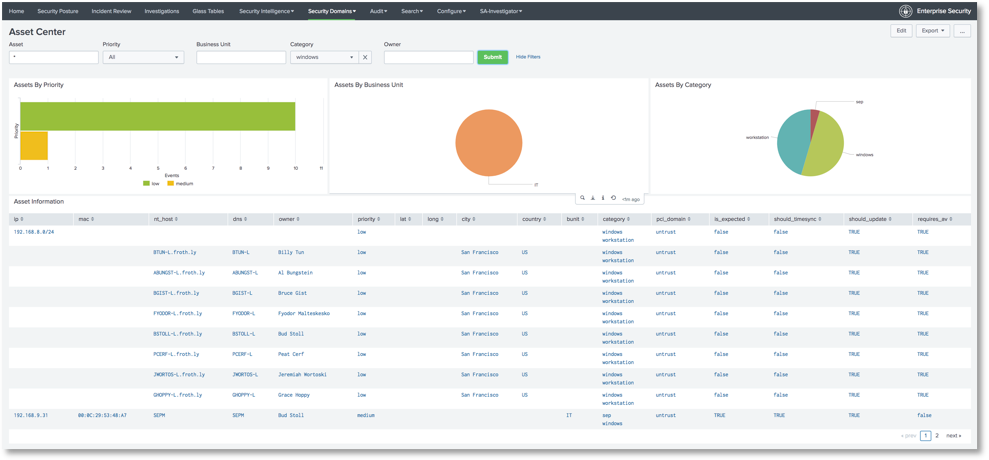
We even wrote a few questions against the NVM flow data for the BOTS competition surrounding malicious cryptocurrency mining activity, and used the NVM inventory data to add some context to the asset framework in Splunk Enterprise Security and asset inventory in Splunk User Behavior Analytics.
If you’re intrigued, please check out all of the Cisco resources, or simply download the NVM app, configure it and give it a whirl—no electronic license is needed to try it out and see what it does for you. We hope you find the data as useful as we did, and that your crusade against those pesky endpoint administrators is a successful one!
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




