SIEM: The Steps Before "The First Steps"

We do a lot of work creating, describing and publishing security use cases to empower SIEM programmes - like a recent webinar with (ISC)2 on ‘20 SIEM Use Cases in 40 Minutes: Which Ones Have you Mastered?’ or sharing stories like Telia’s journey to tackle cybersecurity challenges. However, I thought it would be beneficial to step back from the ‘SIEM minutiae’ to take a better look at IT security strategy and governance. Here's a view of the groundwork to be laid before taking those first steps; reviewing what can aid your decision making on where to start, and which SIEM use cases you should prioritize when building a successful roadmap to support the business:
Before you start...
SIEM is THE technology that divulges an organization’s information security governance strengths and weaknesses, more so than any other technology in the security market space. It will showcase process maturity, reveal maturity gaps, as well as identify the state of employed security skills in your security operations team. In short, SIEM reveals the truth about the state of your organization’s IT security.
As an owner of your organization’s SIEM, you should study the Information Security Governance process. This will allow you to understand the risk appetite of different departments, the policies put in place to mitigate these risks, and what sanctions need to be applied when violations appear.
Does that sound boring?
Maybe, but it will enable you to make the call on which SIEM content makes the biggest impact, and foresee which situations people will show up to you saying “thanks for bringing this to our attention”. This ensures long-term success - which the business and management team will appreciate, rather than just creating noise to be heard.
The Security Steering Committee: Partner of the SIEM / SOC Team
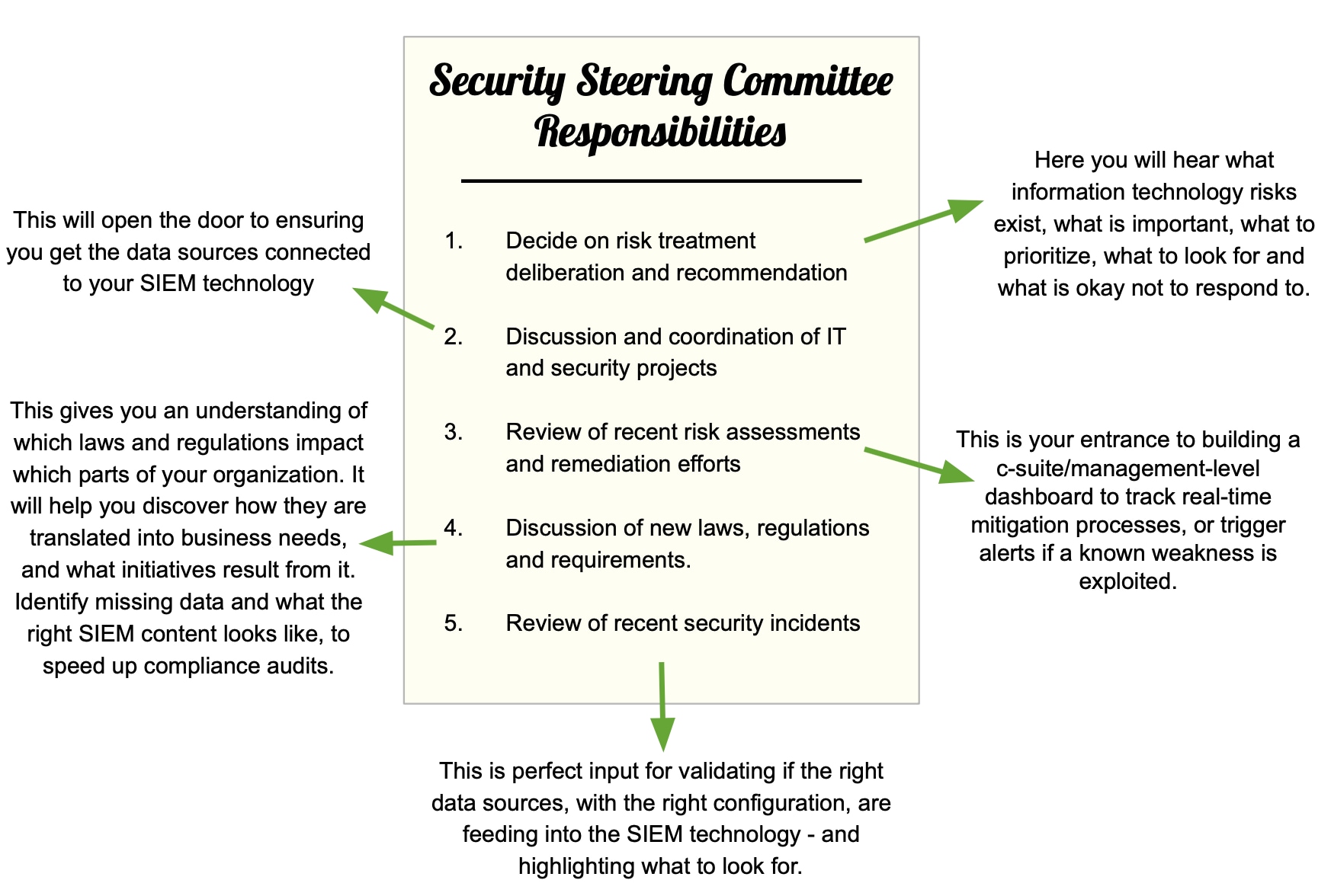
A Security Steering Committee should consist of stakeholders from multiple business units and departmental functions. They may have individual responsibilities - but in the end, they have to identify risks, resolve conflicts and maximize the effectiveness of the security programme whilst balancing with other business initiatives and priorities. You want to have a seat at the Security Steering Committee table, right next to the CISO and ISO. Here is how a Security Steering Committee can help you:
Start building a SIEM to support your organization
Ask for a seat at the Security Steering Committee table. If you don’t have a committee to join, then now is the time to create it! See how you can bridge the gap with NCSC’s “Board Toolkit” to help encourage essential cybersecurity discussions between your board and technical experts. We’ve got you covered when it comes to your SIEM requirements - but of all the options available, why Splunk? Because Splunk is built for a changing world. Find out more here.
Related Articles
About Splunk
The world’s leading organizations rely on Splunk, a Cisco company, to continuously strengthen digital resilience with our unified security and observability platform, powered by industry-leading AI.
Our customers trust Splunk’s award-winning security and observability solutions to secure and improve the reliability of their complex digital environments, at any scale.


