Why Cybersecurity Depends on the CDM Integration Layer
 When you take a close look at the Continuous Diagnostics and Mitigation (CDM) function at the heart of a successful cybersecurity program, you quickly realize that it all depends on integration.
When you take a close look at the Continuous Diagnostics and Mitigation (CDM) function at the heart of a successful cybersecurity program, you quickly realize that it all depends on integration.
It isn’t that the individual components of the program aren’t absolutely essential. But with cyber-attacks gaining in number and sophistication, the true power of CDM is in the ability to overlay multiple datasets to create a single lens for tracking, assessing, and responding to threats.
The CDM tech stack tells the story. The tools and sensors in Layer A give hands-on operators the daily wherewithal they need to get the job done and keep their assets safe. The dashboards in Layers C and D provide the 10,000- and 30,000-foot views that analysts and stakeholders need.
That leaves Layer B as the all-important, often forgotten repository that holds all the other elements together. Too often, organizations treat the integration layer as a necessary evil, a pass-through to get data out from the front lines to the dashboards. So there are no prescriptive technical requirements for Layer B and, too often, no designated owner responsible for getting the most out of the wealth of data and analytics at their fingertips.
That’s a preventable but potentially hazardous error. Because without CDM integration, the rest of the system will fall short of its potential, leaving major opportunities for cyber-protection and threat tracking untapped.
Making Sense of the Data
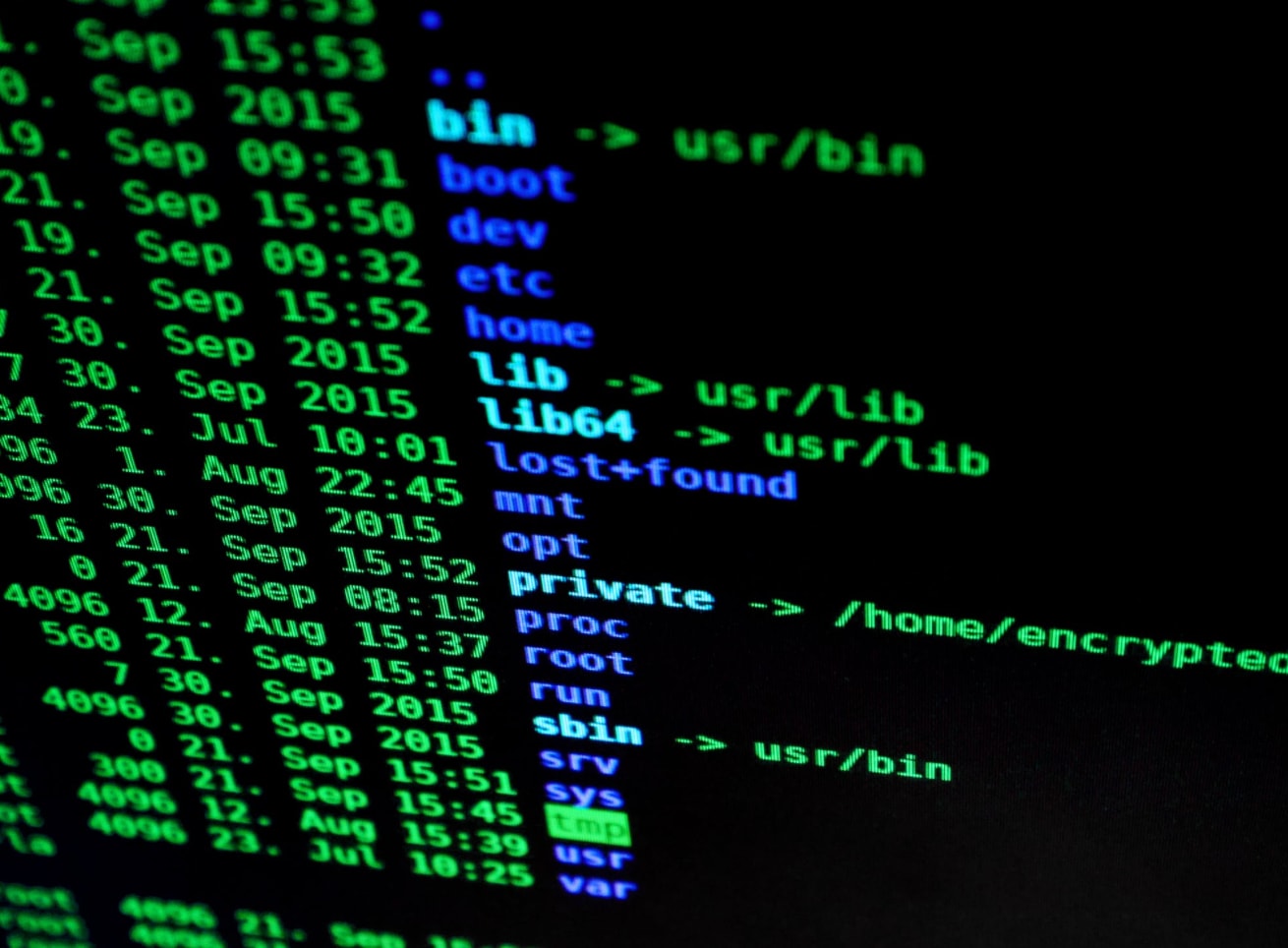
From the outside in, the integration layer looks like the electronic hub that simply transfers raw data from one level of the organization to the next.
From the inside out, it’s so much more.
As IT systems become orders of magnitude more sophisticated, and cyberthreats become vastly more numerous, a successful data protection system must consume mountains of incoming information, spot patterns across multiple sources, and identify and respond to potential attacks. That means moving far faster than human operators can keep up, using state-of-the-art analytics and Artificial Intelligence to distill the deep insights that are available in the data stream — but only if you know where and how to look for them.
That added value is something U.S. government agencies have to be able to count on to get the job done. And it’s exactly what happens at the integration layer, with Splunk serving as the crucial Point of Filtration that turns raw data into practical results and action.
The good news is that the federal government is already set up for success. The Department of Homeland Security has invested in the tools and sensors in Layer A. But if the goal now is to make best use of the data and get the best return on that investment, it’s time to give Layer B the attention and priority it deserves.
That’s how a CDM stack delivers breakthrough results that are greater than the sum of its parts. And that, in turn, is exactly what a high-stakes U.S. cybersecurity environment needs, at a time when the incoming threats are becoming more serious by the day.
 Take a deeper dive into CDM with Splunk!
Take a deeper dive into CDM with Splunk!
Join us at the FCW CDM Virtual Summit on November 19, 2020 for our session at 10:45 a.m.
----------------------------------------------------
Thanks!
Michael Guercio
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




