SplunkTrust Q&A with Ryan O’Connor

Ryan O’Connor’s path to becoming a SplunkTrust member began when he was a student and early Splunk user, eventually leading to his role as a partner, educator and active Splunk Community member. Ryan is an asset to the Splunk Community; his contributions to Splunk Answers and his efforts teaching university students using Splunk have been invaluable.
 |
Tell me about your background and your transition from liberal arts to tech.
When I was a sophomore at the University of Connecticut, I got an IT help desk role, which grew into a full-time position, and I ended up being fortunate enough to receive a tuition waiver. I had the freedom to choose a degree, something that I was pretty passionate about. I ended up choosing Women’s Studies. I think [a liberal arts degree] is something that you can take to any job and have a holistic perspective of where people are coming from.
Did you start working with Splunk when you were at the University of Connecticut or was that later?
At first, in the help desk role, I was resetting passwords or handling whatever trouble tickets we might get. But then I wanted to find out why we were getting the same problems all the time. Someone in the security department at UConn told me, “Oh, we have this tool called Splunk that's great for log analysis.” At that time, years ago, I don't think Splunk even had a graphical user interface. But, I was fascinated with it, and it helped me solve a lot of problems. So, after I finished up my Women's Studies degree, and I had seen Splunk, and what big data could do, I ended up pursing a Master of Science in Business Analytics and Project Management, also at the University of Connecticut. Needless to say, I've been chasing Splunk for a long time.
What was one of the first problems you solved with Splunk?
When there was a successful phishing scam, one way for our Exchange admin to limit the impact was to set up rate limiting on the Exchange server. People could only send X amount of messages in X amount of time. I challenged that admin to forward me over the ID of the user anytime he saw one of those events and then I would dig into Splunk and see what I could find about activity related to that ID. I figured out that the precursor to someone performing one of these phishing scams in our environment was that they were logging in from Nigeria. Anytime someone logged in from Nigeria I would be proactive and forward our Exchange admin the event. Eventually, we were able to stop these attacks and notify users more effectively who may have been affected.
You were at UConn, and now you're at Jacobs. Were there any steps in between?
I was at the University of Connecticut for about seven years, I had barely finished grad school, and Hurricane Labs picked me up. It was cool working for a managed security services provider (MSSP) because you get to see so many different customers and their varied use cases. I’m now just heading into a new opportunity with Jacobs, and I can’t wait to see what’s in store for me there.
What was it like working at an MSSP focused on security?
My primary role was to engineer, design, and build Splunk Enterprise Security (ES) deployments for customers—ranging from those who wanted to host everything on-premises, all the way to customers who wanted to leverage Splunk Cloud. I also functioned as a Tier 3 layer of support for all customers. I loved when I got to build out specific Splunk (ES) use cases for our customers. There is an infinite number of use cases you can do with ES and a seemingly infinite amount of data out in the world. One of my favorite parts of working at an MSSP was the people. I was able to meet other Splunk partners, Splunkers, and so many different customers—all passionate about Splunk.
Tell me a little bit about some of the surprising things you discovered or solved with Splunk Enterprise and Splunk ES.
At Hurricane, we designed the DomainTools App for Splunk, which was so cool. This is a tool where you can feed domains out to be analyzed. If you run a search in Splunk ES that returns a domain name in the results, you can use this App to pipe those domains directly out to DomainTools to be analyzed. From there you can get data back on all types of information about those specific domains. I think the coolest part is that this can happen on such a massive scale.
 You developed the Nest App for Splunk?
You developed the Nest App for Splunk?
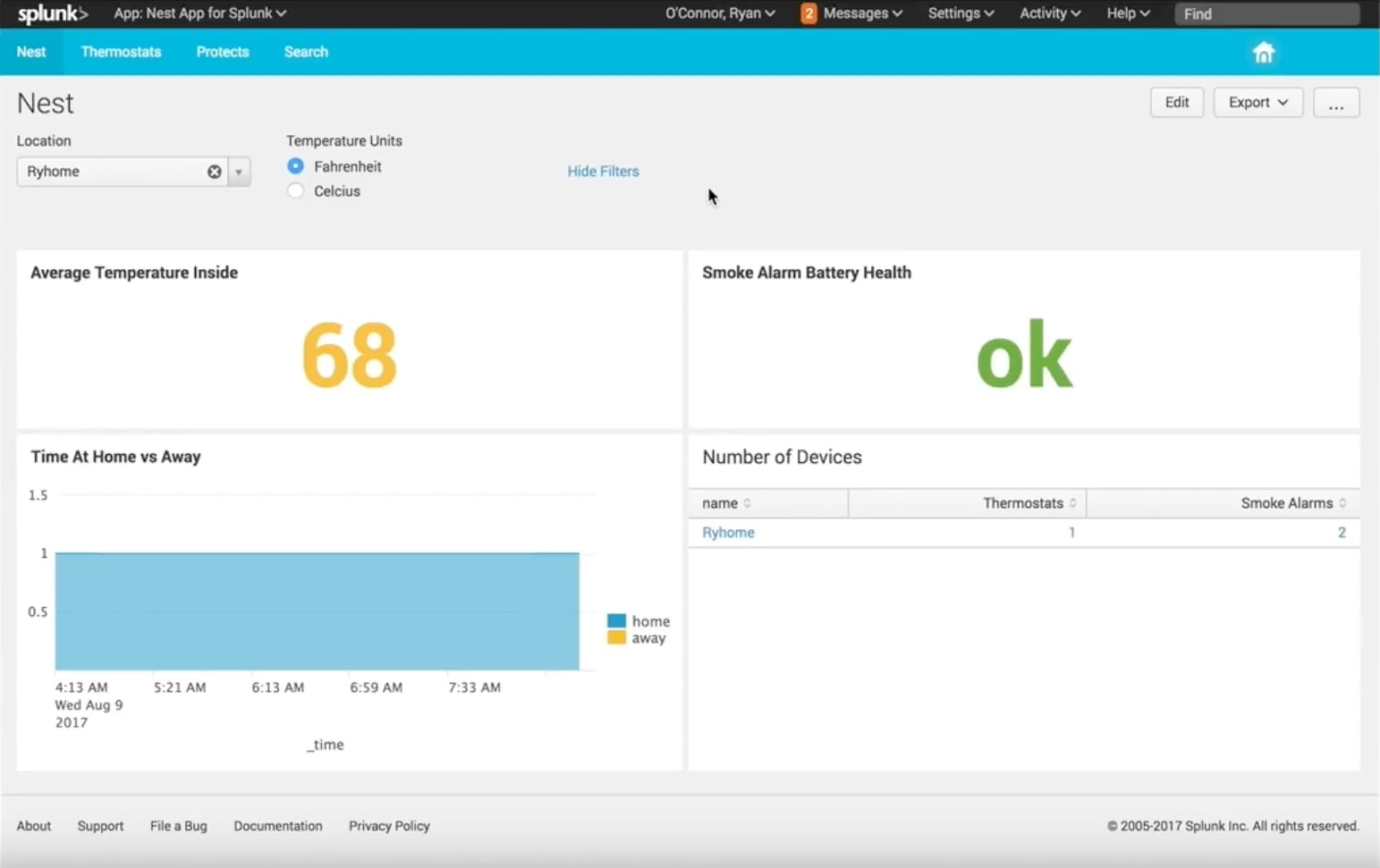
Yes, that's one of the many IoT use cases I have for Splunk. Nest has a whole family of products, including home thermostats. The Nest Add-on for Splunk is in the Works with Nest store and on Splunkbase. We spent time getting this App and Add-on to a point where users can set them up easily—I think the setup takes about five minutes—and then they can analyze their data. When we designed that app, we also spent a lot of time making sure the security was as secure as it could be while still balancing the user’s ability to have an easy setup process. I ended up looking into things like AWS Lambda. I think that's one of the coolest features of that app. To a user, it may not seem that flashy, but from the security perspective, it's awesome.
Is there one thing that people should check out in Splunk?
If it's a new customer, I would look into Splunk Education. I might be seen as someone who is somewhat of an expert in Splunk, but I still take those courses and still learn something new every time. I just feel education is the key to success.
Can you tell me about some people you’ve worked with in the Splunk world?
I’ve worked with people in many sectors—retail, education, technology, security, healthcare, banking and financial services, and probably many more that I can’t think of off the top of my head. Healthcare is a really interesting space for IT in general, but especially for Splunk. I think healthcare is going to start moving into a lot more connected devices and home healthcare. For example, people can monitor and do things from their homes. It's similar to the challenges that IoT is going to be met with, but at a more sensitive level because it involves patient data and HIPAA.
How is SplunkTrust?
 It's only been a couple months, but it's been so exciting. Even though I've been around Splunk for a long time, .conf2017 was my first .conf ever, I gave my first talk, and I presented “Taking Splunk Inside the Classroom." Some people from different universities were pretty interested in the talk so that was awesome. I love the SplunkTrust—it makes me truly realize the importance of the Splunk community.
It's only been a couple months, but it's been so exciting. Even though I've been around Splunk for a long time, .conf2017 was my first .conf ever, I gave my first talk, and I presented “Taking Splunk Inside the Classroom." Some people from different universities were pretty interested in the talk so that was awesome. I love the SplunkTrust—it makes me truly realize the importance of the Splunk community.
I'm also an adjunct professor at the University of Connecticut and leverage Splunk for my class. I’m teaching one course at UConn on data analytics and predictive modeling. I think the new Splunk Machine Learning Toolkit (MLTK) is exciting. This semester, I'm working with Andrew Stein from Splunk’s Machine Learning Toolkit team. We’re going to show some cool new features of MLTK.
Through Splunk Pledge, I also have my UConn students signed up for a couple of courses. They can be on their way to a Splunk Power User cert before they graduate. In fact, the entire University can register for these courses and get that certification for free if they haven’t yet.
Have you checked out the Splunk Bucketlist yet?
I think it's a great site and a quick way to get information to people about Splunk and the community. You sign up for challenges, win points, and it's awesome. Everyone needs to get on board with this site if they want a quick way to learn about Splunk.
Do you have any interesting items on your bucket list?
I’m pursuing my Divemaster certification, which has been a really fun journey so far. That’s where the idea for the Subsurface App for Splunk was born. I volunteer SCUBA Diving at the Mystic Aquarium in my free time and can even be found in the piranha tank!
Thanks,
Jason Hupka
Community & Advocacy
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




