
Digital Resilience Pays Off
Download this e-book to learn about the role of Digital Resilience across enterprises.
The 2019 RSA Conference kicks off in San Francisco this week. I’m always excited to hear all the different ways people use and even rely on Splunk for so many different use cases and challenges; every year brings enthusiastic discussions around the Splunk platform and new ways customers and partners have figured out to leverage Splunk, that the possibilities are truly only limited by our own imaginations.
As much as I love these discussions, I might possibly enjoy talking more with those who haven’t had their first, second or even third "AHA!" moment with Splunk.
For every Splunk enthusiast, there are those unsure how to get started using Splunk for security, how to get the most from their data or expand into new use cases. The conversations always start with general questions that everyone should be asking (no matter what level of maturity):
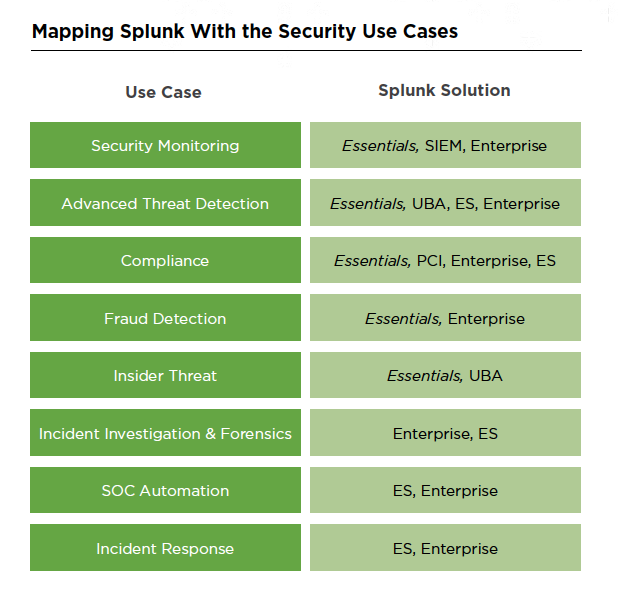
 You might be surprised how many aren’t able to answer these questions. This is why we put together "The Essential Guide to Security." It’s a quick primer that tells Splunk’s security story, in clear and simple terms. It shows what common security challenges can be solved using Splunk and what software solution maps to each challenge with a clearly laid out six stage maturity journey.
You might be surprised how many aren’t able to answer these questions. This is why we put together "The Essential Guide to Security." It’s a quick primer that tells Splunk’s security story, in clear and simple terms. It shows what common security challenges can be solved using Splunk and what software solution maps to each challenge with a clearly laid out six stage maturity journey.
Below, we have included an excerpt of the book to whet your appetite. For those looking to get a bit more hands-on, download the free app Splunk Security Essentials on Splunkbase, which showcases many working examples of use cases from insider threats to security monitoring to advanced threat detection and more. Find your next "Aha!" moment by using the data you have to expand into new use cases and solving new challenges.
What’s your plan for cybersecurity? Are you simply “planning for the worst, but hoping for the best?” With digital technology touching every part of our lives and new threats popping up daily, it is imperative that your organization is precise, informed, and prepared when it comes to defending your assets and hunting your adversaries.
Recent high-profile breaches, global ransomware attacks and the scourge of cryptomining are good enough reasons why your organization needs to collect the right data. You also need to implement the right processes and procedures early on, often alongside new technologies, and with an ever-increasing velocity and variability of machine data.
So how can you best defend your organization and hunt down new adversaries? Ultimately, by taking a holistic approach to your defense system across the enterprise. This is why Splunk believes every organization needs a security nerve center, implemented by following a six-stage Security Journey that we will describe for you.
Let’s break down what that means.
Organizations can better optimize their people, process and technology around security with a nerve center. The Splunk platform can act as this nerve center, as it brings multiple cybersecurity areas, and others outside of security, together to foster collaboration and implement best practices for interacting with your data. From there, the platform allows for modern workflow, all the way to invoking actions to address ever-changing cyberthreats and challenges.
Security teams can use Splunk to drive statistical, visual, behavioral and exploratory analytics that inform and execute insights, decisions and actions.
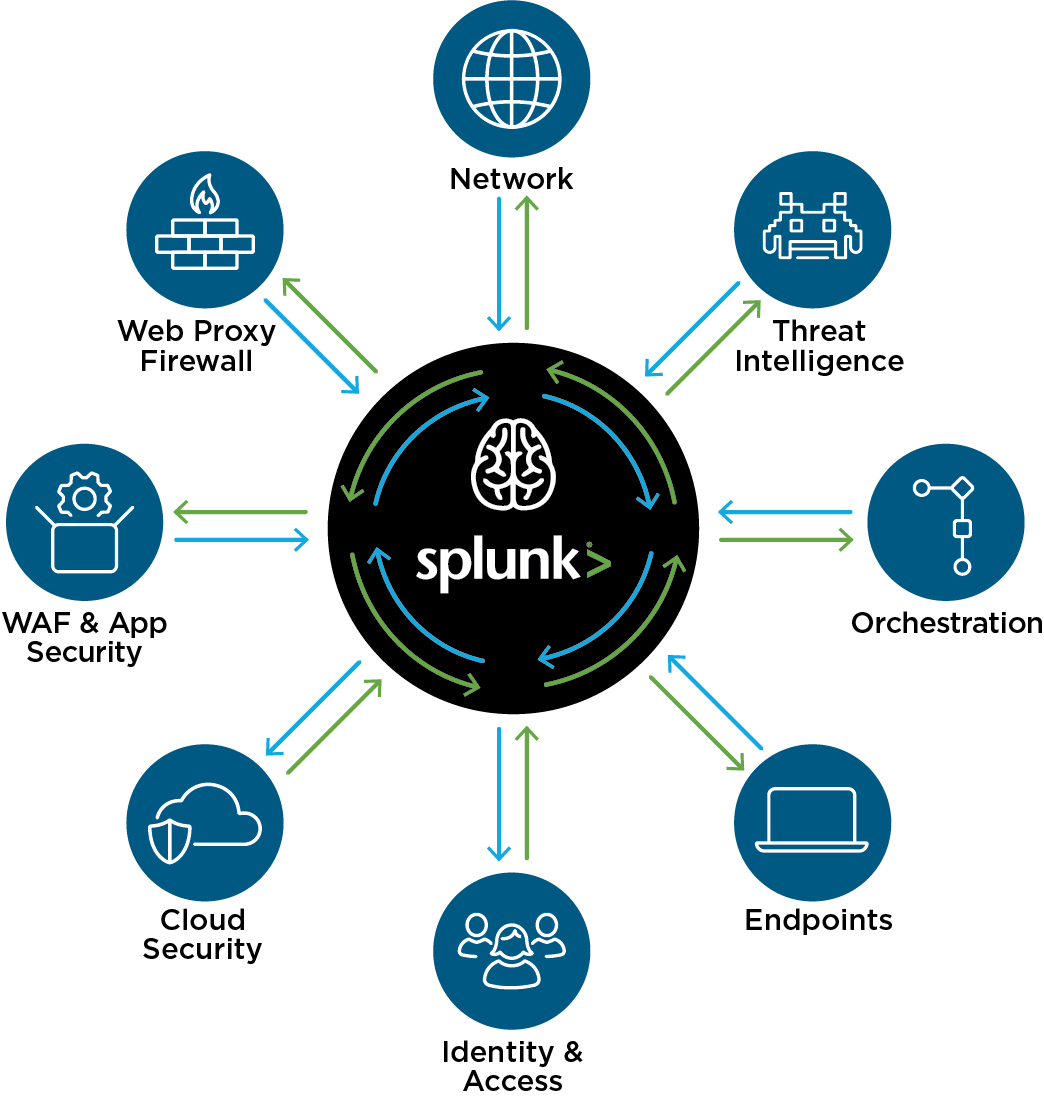 The nerve center model includes using all the data from the security technology stack, which can help you investigate, detect, understand and take rapid, coordinated action against threats in a manual, semi-automated or automated fashion. Establishing a nerve center allows organizations to advance their security and focus on the real challenges within. When teams invest in their security infrastructure, their security ecosystem and skills become stronger, making it possible to expand into new areas, proactively deal with threats and stay ahead of the curve.
The nerve center model includes using all the data from the security technology stack, which can help you investigate, detect, understand and take rapid, coordinated action against threats in a manual, semi-automated or automated fashion. Establishing a nerve center allows organizations to advance their security and focus on the real challenges within. When teams invest in their security infrastructure, their security ecosystem and skills become stronger, making it possible to expand into new areas, proactively deal with threats and stay ahead of the curve.
Sound good?
Great. So how do I make all of this happen in the real world, you ask?
First, you must understand your environment and find a place to begin. Ask yourself—what are you trying to protect? How will you protect it? What data do you need and how will you respond to the threats?
Want us to show you how to get started? Sure.
We’ve put together this short book to introduce you to the top security use cases organizations face. We’ve also outlined and mapped them into a six-stage security “data journey” that will help you create a kick-ass security practice. Take a look:
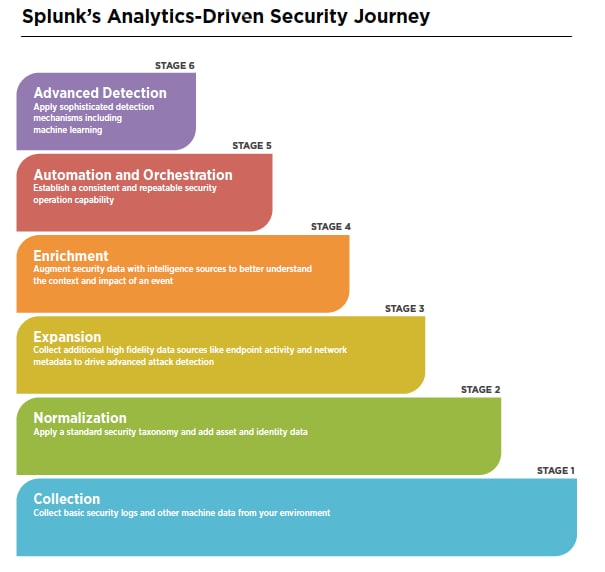
Next, you will find the specific security use cases we’ve mapped to the journey. Go ahead. Choose your own adventure, or security challenge. The purpose of this book and the app is to teach you how Splunk's analytics-driven platform can help solve your security challenges and advance your security journey, including:
Want to read more? That’s the end of the excerpt but it doesn’t have to be the end of your journey. Download your free copy of "The Essential Guide to Security" and we’ll see you at RSA this week.
You can also download the Splunk Security Essentials app for free to see working examples of security use cases and map your security journey.
Editor’s note: This post was updated on March 4, 2019
----------------------------------------------------
Thanks!
Jade Catalano
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.