Break down silos between people and technology for a centralized fraud approach. Collect data from point solutions, consolidate the fraud scores they produce, and facilitate consistent, collaborative investigations into fraud events.
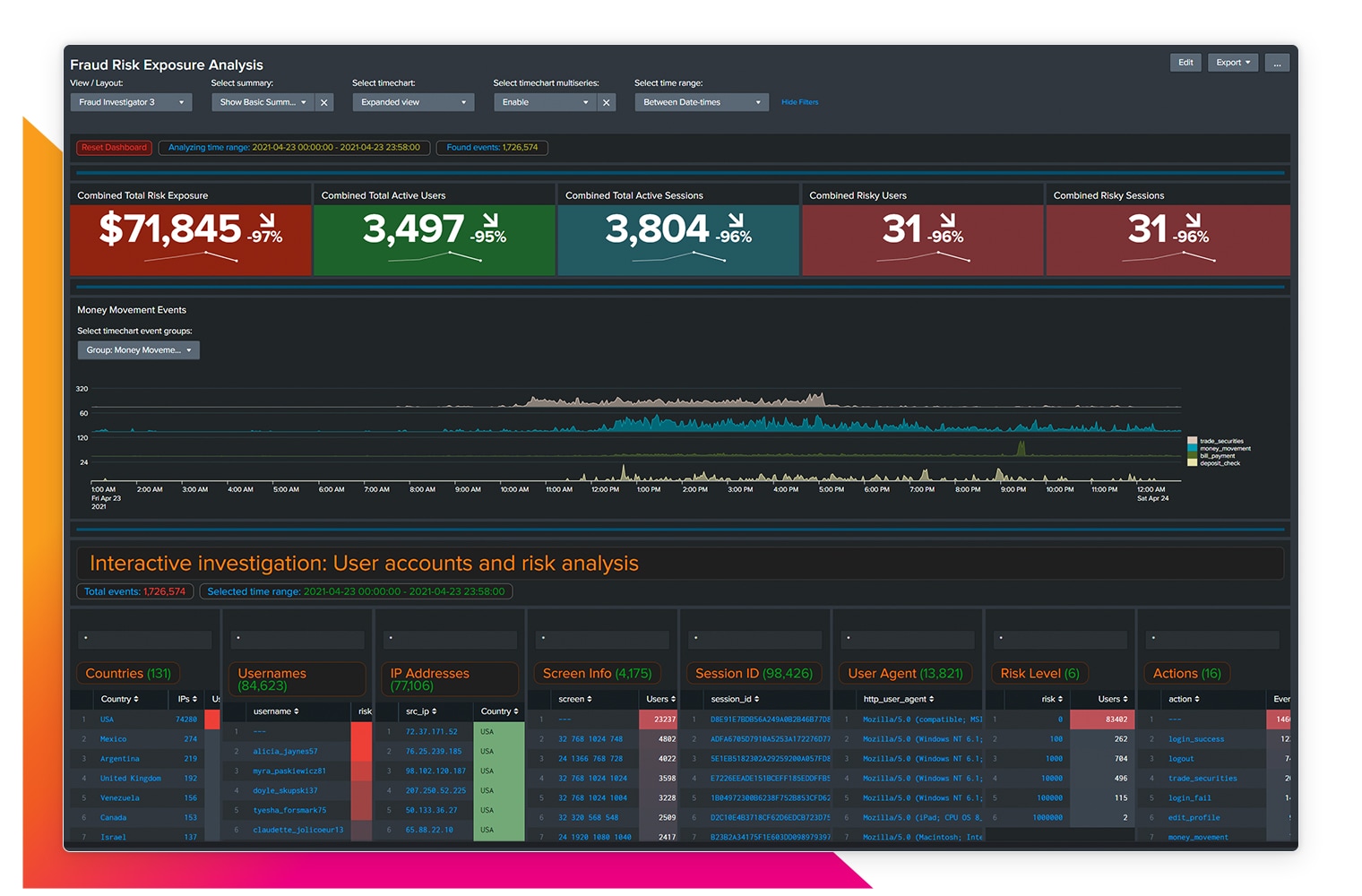
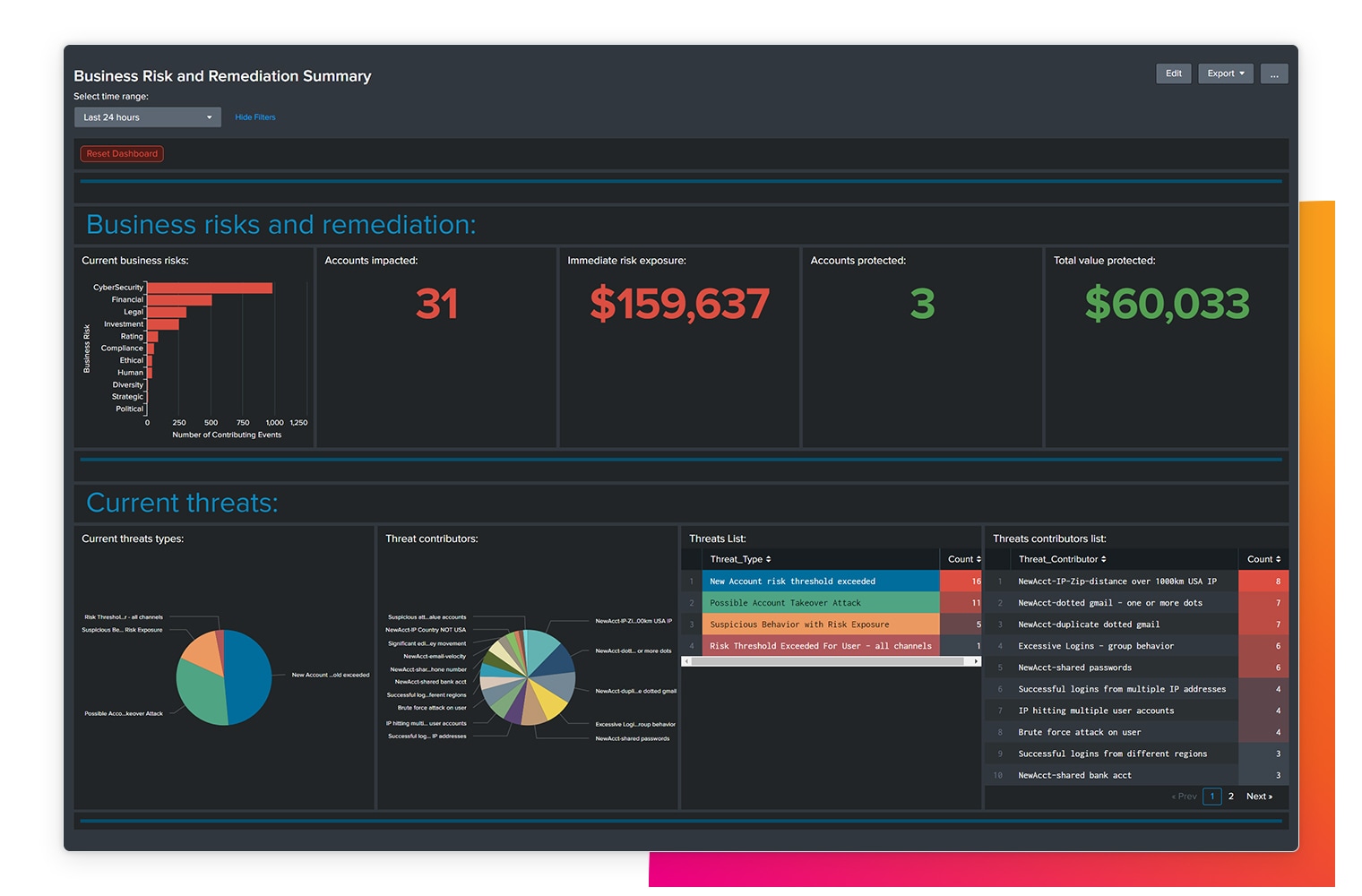
Understand the business-level impact of fraud threats and mitigation efforts. Flexible, advanced reporting and visualizations make it easy to analyze, measure, and manage fraud risk.
Splunk delivers integrated anti-fraud technology that can monitor any data to detect fraud patterns sooner
Proactively Monitor
Pre-configured correlation searches automatically monitor collected data and create notable events for potential fraud attempts, like account takeovers and new accounts fraud.
Find Outliers
Detect and investigate outliers via anomalies in machine data that will help pinpoint fraudulent activity
Determine Business Impact
With pre-configured dashboards, you can quantify real-time fraud risk and mitigation efforts down to the dollar amount and easily share summaries of business-level fraud metrics.


CUSTOMER STORY

PSCU
No matter what you do, you’re going to have failures out there. The sooner you know, the sooner you can repair it, and the better you protect your user experience.
