Get Your Role On with the Splunk Platform
F
Let’s step right into our next topic: Demystifying the configuration of roles, search indexes for roles, and indexed fields. This has long been a pain point for Splunk administrators, and we recently took steps to rejigger the Splunk Web interface to make this portion of user management a lot more accessible.
Historically, it was agony to understand how a Splunk role affected the dataset a user could search. With the enhancement that we’ve made starting in Splunk Enterprise version 7.3, it’s easier now more than ever to get your role on.
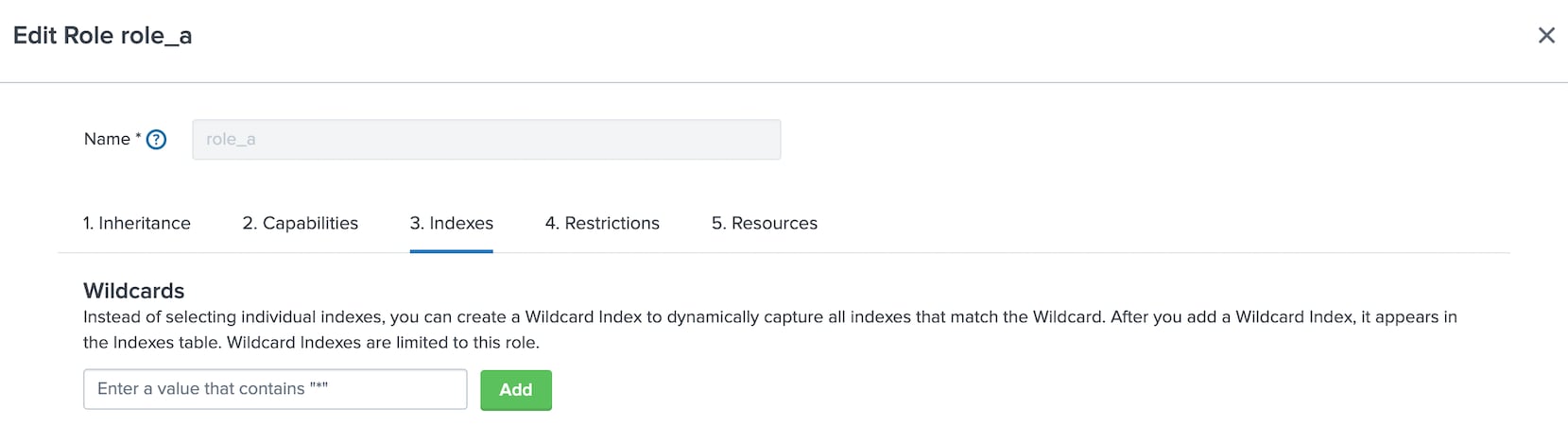
With the updated interface, you get a view into what indexes are accessible, depending on how indexes are inherited from other roles. Prior to version 7.3, there were two panels that let you choose indexes that were searchable for a role. This has now been collapsed into a single pane. The pane also shows whether indexes are inherited from another role. You can use the filter to type in a string and the page updates to show only indexes that match the string you typed.
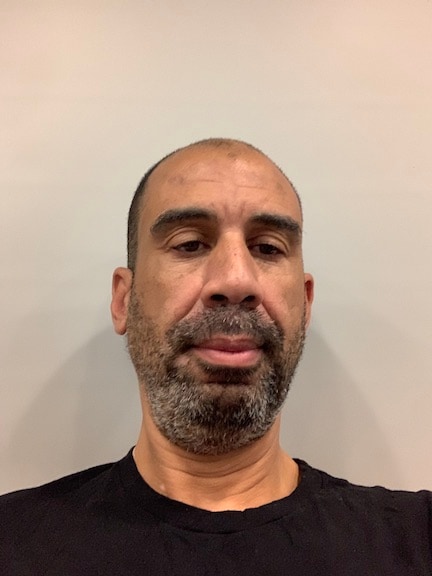
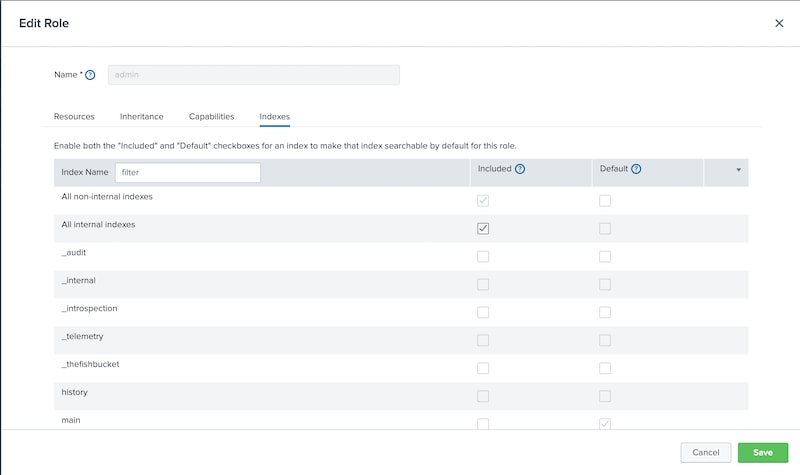
Another new feature we added is the wildcard index. Picking and choosing a few (or a few dozen) indexes for a role is one thing - but what if you have hundreds, or thousands? That’s where Wildcard Indexes come in to save the day. Type a string in the “Wildcard Indexes” field and click Add, and boom — you now have a “wildcard index” that applies to every index that begins or ends with that string, depending on where you put the “*”. You can then assign it as a default or an included index like any other, and bonus! Any index which matches your wildcard gets the same treatment that the wildcard index gets. In fact, Splunk Enterprise comes with two wildcard indexes by default enabled for each role (“*” and “_*”).
Of course, I would be remiss if I didn’t mention the updated documentation on the subject. We have made significant updates there to help guide you through the configuration process.
Another cool new feature we’ve added for indexed fields is the Search Filter Generator. But that deserves its own topic so we’ll save that for a future episode.
Until next time, stay secure, everyone...particularly during this pandemic!
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.