Detecting Vulnerable and Compromised Certificate Use/Abuse with Splunk Enterprise Security and Stream
Recently, we have received a number of questions about compromised SSL certificates. One of the challenges this problem presents for analysts is how to gain insight into what these compromised SSL certificates are transporting and with whom are they communicating.
If you were to encounter this situation, you might find yourself being asked the following questions:
- How would you identify which assets in your organization are affected?
- How could you arrive at a strategy to prioritize what to remediate first?
- How do we start looking for these certificates being used in communication across our networks and systems?
Detecting and Remediating
For users of Splunk, many of you know that the Splunk App for Stream can capture wire data. Stream can capture many different protocols, including TCP, UDP, HTTP, DNS, and FTP, to name a few. Within specific protocols, like HTTP, we capture the SSL/TLS version and the time it took to negotiate the handshake. When you look at TCP data, we capture those attributes as well as the SSL/TLS Session ID, MD5 of the certificate, Issuer, Common Name, Serial Number, and Start and End dates for the certificate.
Detection Using Splunk Stream App
- Capture wire data using Stream
- Search for the issuer name of the compromised cert
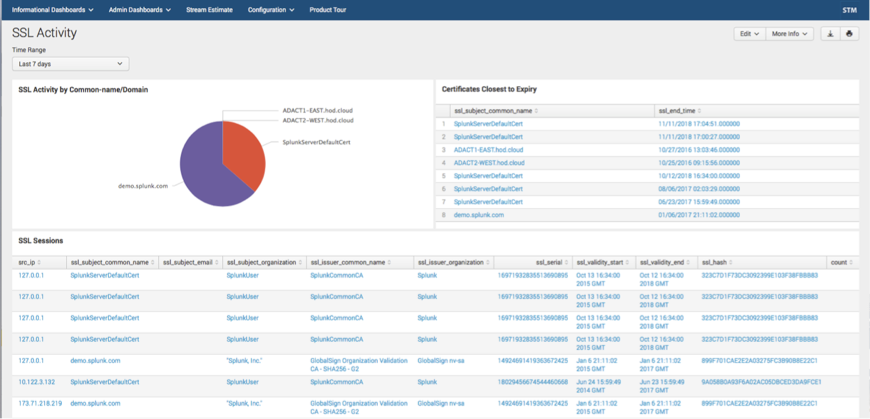
Below is a screenshot from the Stream App’s SSL Activity dashboard:
Detection Using Splunk Enterprise Security
Another way to gain greater insight into this issue is to leverage Splunk Enterprise Security. Enterprise Security provides the ability to execute correlation searches and generate notable events that analysts can triage and investigate. Alongside those core incident response activities, Enterprise Security can also provide analytics around threats of interest to the analyst.
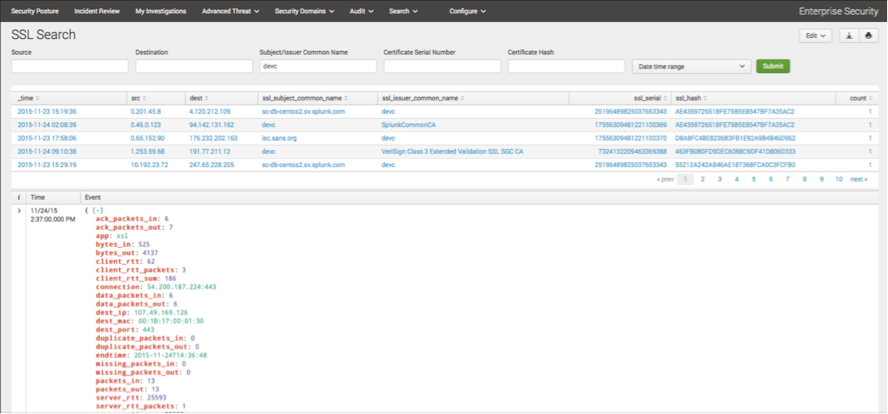
We can use Enterprise Security’s Protocol Intelligence dashboards, specifically the SSL Search Dashboard and search the Subject/Issuer Common Name field. Any results that return would indicate communication using this certificate along with information pertaining to bytes in/out, source and destination IP, port and other meta data collected.
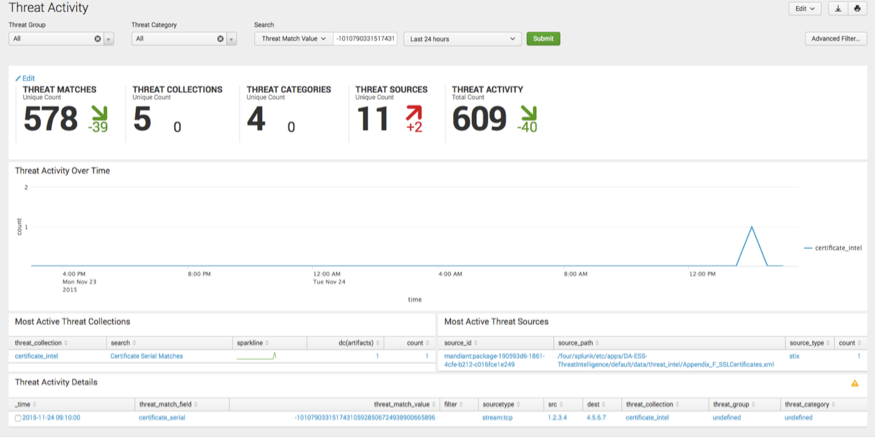
Another action we might want to take is to load that certificate into my local certificate threat intelligence list. From there, we can search Threat Activity for the serial number of the certificate and establish where it was first seen, which systems are communicating with it and drill down to the underlying logs for greater clarity.
Enterprise Security can also correlate this threat intelligence. The threat artifact you created can be continuously mined against new data being collected and can trigger a Notable Event to your SOC if a match exists.
We hope this provides you with a better idea how Splunk Enterprise Security can gain greater insight into SSL/TLS Certificates and the communication that they are helping to facilitate.
Wire data can provide information beyond log files that exist on systems and can provide additional telemetry to the analyst for better insight into threats on your network.
Now that you have a list of IP addresses that contain the compromised SSL certificate, you can begin the remediation process.
John Stoner
Federal Security Strategist
Splunk Inc.
----------------------------------------------------
Thanks!
John Stoner
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.