Defining indexes for release with your app
Recently I’ve heard a lot of chatter regarding how to segregate your data with indexes, especially if you have created an app (or multiple apps). Maybe it is just me, but personally I like to create a separate index per app or custom dataset that I work with. In my previous post, I held all CDR data (from 2 different sources) within one index, VOD and CDN in another, and operational data in yet another. For some this may seem like overkill, but this allowed me to work with the data in separate sets, and no matter what I did with that data, it wouldn’t affect data residing in other indexes (clean eventdata -index foo). This is especially important when working on enterprise apps.
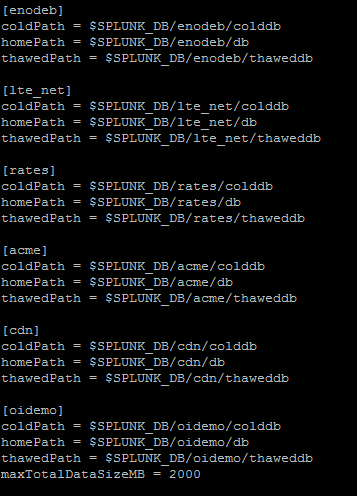
So how exactly do you control indexes, particularly if you are writing an app for release into the wild. You can do this with an often overlooked file, indexes.conf. In the screenshot below I’ve defined several indexes:
Notice that the path is relative ($SPLUNK_DB). When this file is included within the app packaging ( under default/), it will automatically create the indexes required when a Splunk administrator installs it.
But what about searching these new indexes? Best Practice would dictate that my searches should include index=foo, but in this case we’re going to alter Splunk’s settings to allow our users to search without specifying a particular index. The only thing I need to do is ensure that this index is searchable. Unfortunately there is no easy way to do this on an app-by-app basis. The easiest way to accomplish this is by editing capabilities by role within the setting menu (“settings -> Access Controls->Roles->WhichEverRoleYouWishToEdit->Indexes searched by default“). So long as my new indexes are searched by default, I no longer need to specify an index.
----------------------------------------------------
Thanks!
Dennis Bourg
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




