Working in the SOC with Power Tools: Splunk and Polarity

 Have you ever had to saw through a board by hand? I had to finish a partial cut by hand the other day while building a new mantle for my fireplace. It’s slow and difficult, and it often results in a lesser quality cut than one done with a power tool. It’s good exercise, though! We should all have to do it at least once so we appreciate our power tools more.
Have you ever had to saw through a board by hand? I had to finish a partial cut by hand the other day while building a new mantle for my fireplace. It’s slow and difficult, and it often results in a lesser quality cut than one done with a power tool. It’s good exercise, though! We should all have to do it at least once so we appreciate our power tools more.
In the Security Operations Center (SOC), we receive so much data per day that we can’t afford to cut through that data “by hand.” We have to use tools like the Splunk Security Operations Suite to identify and prioritize security events, and automate associated repetitive tasks. The Security Operations Suite itself draws additional power from Splunk’s expansive technology partner ecosystem in many ways. Especially relevant is how it simplifies the data you see and provides additional context for investigations.
Enter Splunk Technology Ecosystem Partner Polarity
Polarity works with the Splunk Security Operations Suite to give users the context needed for their data with superhuman thoroughness and speed. Polarity improves accuracy and reduces rework resulting from faulty or incomplete data, while also improving efficiency and collaboration when working with data. Ultimately, this all leads to faster decisions and action in the SOC.
Picture this. You’re a security analyst and you’re good at your job. But you can’t remember every IP address you’ve ever seen. Let’s say you’ve previously investigated an IP address,and created a ticket in your IT service management system to fix the misconfiguration. You even tried to mark it as “known good” in your SIEM rule, but it’s now showing up as a hit on a different correlation search. You don’t have a photographic memory, so you can’t tell it’s the same IP address that was previously investigated. You need to dig into your records to check if it’s a match.
With Polarity, your team only has to spend time investigating an IP address once, annotate it with a quick note, and link to your investigation details — “Misconfigured server. IT Ticket #123. More details here.” Every time that IP address flashes across your screen, it’ll be highlighted, and that context will be presented to you. No more time wasted re-investigating that IP address, or trying to remember to ignore it whenever you see it. For every investigation performed by your co-workers, you’re not duplicating the work. Polarity automatically highlights various IP addresses, file hashes, domain names, URLs and other indicators on your screen, and presents the corresponding annotations to you. You can see your co-worker’s investigation details, which informs your team as to what has already been done for those indicators. You can then build upon that work or move on to the next task.
You’re probably thinking, “That requires me and my team members to make those annotations in Polarity, right? That sounds like work.” Hmm, well, yes, our jobs do require work, even when using “power tools” to do the work. Using a circular saw is a heck of a lot easier than a hand saw, but I still have to cut the board.
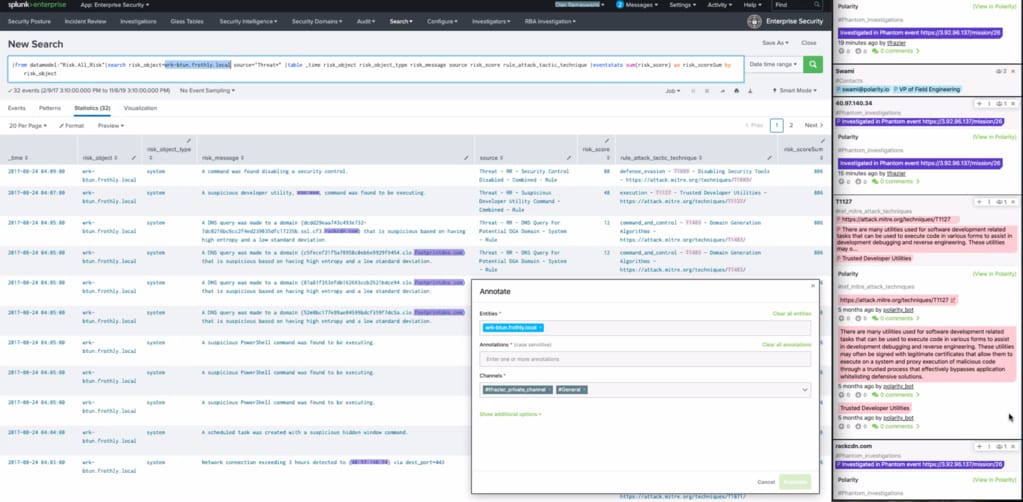
Polarity highlighting relevant text right in the Splunk interface and showing the annotations with links back to Phantom investigations.
Here’s where I bring in Splunk Phantom as the circular saw to cut through these tasks with ease. I wrote a Polarity app for Phantom that allows me to update an “entity” in Polarity with the proper “annotation.” I then built a playbook that will apply a standard annotation to all the artifacts/indicators in an event like “False positive. Event details here: <link to Phantom event>” or “Basic infection. Desktop re-image ticket #456. Event details here: <link to Phantom event>.” That way, if I see these indicators highlighted on my screen, I can either quickly determine if they are related to previous investigation(s), link to see what has been done previously and move much more quickly through the list of tasks I need to accomplish.
Now we have a full feedback loop. We can quickly build upon previous work through Polarity’s context presentation, and then update our annotations for our co-workers and our future selves with Phantom. You can take this one step further by using Phantom to automate your basic event triage/response, and then automatically add your annotations to Polarity for context anywhere else.
Keep cutting with power tools!
Join experts Tim Frazier of Splunk and Dan Ramaswami of Polarity for a Community Tech Tuesday on 10/13 @ 2 PM EST. They’ll share a live demonstration of the integration and answer your questions. Register here.
Get the Free Community Editions for Phantom and Polarity to follow along on the Community Tech Tuesday.
Have Phantom, but need Polarity? Get Polarity.
Have Polarity, but need Phantom? Get Phantom.
----------------------------------------------------
Thanks!
Tim Frazier
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




