Three Reasons It’s Time to Re-Evaluate Your Approach to Security Operations

If you struggle to keep up with the volume of alerts you receive daily, you’re not alone. According to one SC Magazine article, more than 79% of information security professionals report that their teams are negatively affected by alert fatigue. Organizations of all sizes and across the globe are realizing that in order to effectively mitigate risk, they need new strategies for detecting, triaging, investigating and responding to the growing volume of security alerts they receive.
According to Enterprise Strategy Group (ESG), there are three major drivers fueling the need for a new approach to building/maintaining Security Operations Centers (SOCs): disconnected security tools, manual security processes and a growing skills shortage.
Disconnected Security Tools
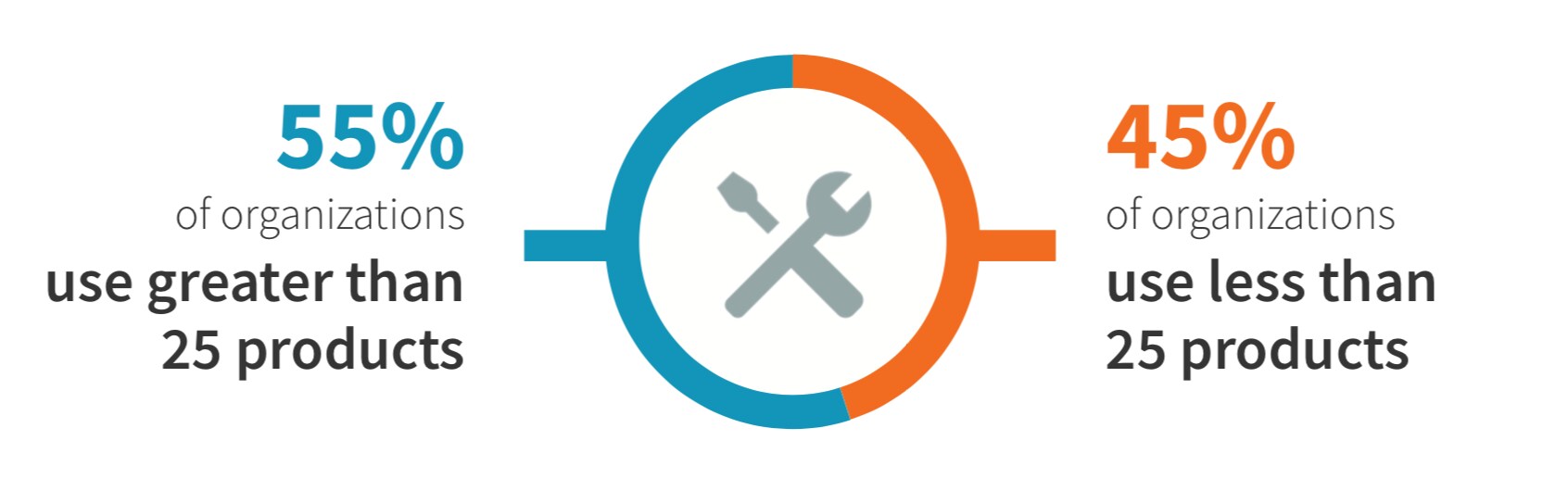
ESG research indicates that 55% of organizations use more than 25 security tools (e.g. firewalls, malware sandboxes, endpoint security, threat intelligence services, etc.) today. These security tools, with little-to-no integration between them, create silos of data. This hampers visibility within the SOC and contributes to organizations missing critical attacks. The high number of tools also adds complexity to the overall environment and slows the speed of a manually-executed response.
Manual Security Processes
Far too many organizations use manual processes for triage, investigations and remediation activities. These manual processes rarely scale as volume increases. Moreover, the speed of the response is often not fast enough to keep up with the pace of today’s threats.
Growing Skills Shortage
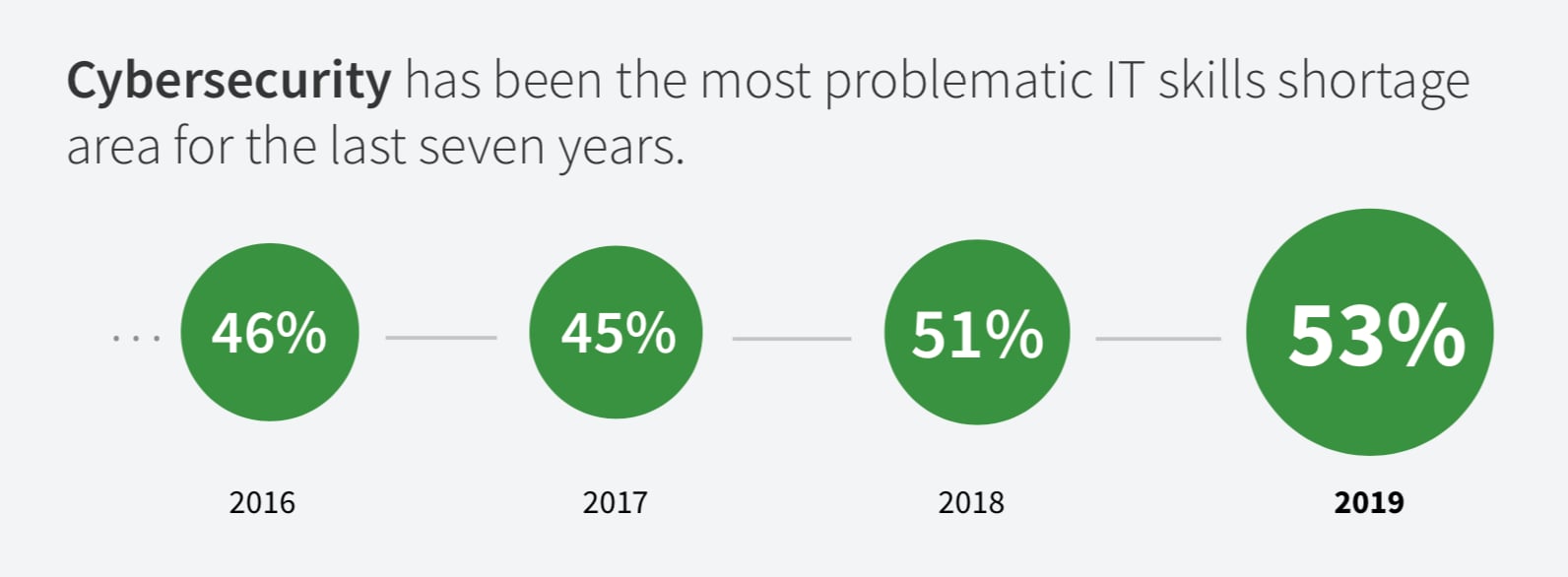
53% of organizations report having a problematic shortage of cybersecurity skills, according to ESG. This shortage leads to further drains on SOC effectiveness and creates additional opportunity for threats to become successful attacks.
Strategies for Improving Security Operations
ESG offers its Security Operations and Analytics Platform Architecture (SOAPA) model as one way to improve efficiency and scale within a SOC while maintaining a multi-vendor security operations technology stack. In it, products share data, cooperate with analytics engines, and take automated remediation actions that address security incidents or mitigate changing cyber risks.
Splunk also offers a strategy for modernizing security operations. The Splunk SOC 2020 initiative was introduced at the Splunk .conf18 user conference last October, and outlines ten capabilities of the modern SOC.
Learn more about ESG’s SOAPA architecture and Splunk’s SOC 2020 initiative in the white paper, The Present and Future of Security Operations.
----------------------------------------------------
Thanks!
Chris Simmons
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




