Splunk Your Phantom Events

One aspect of the synergy between Splunk and Phantom that many have yet to uncover is Splunk’s ability to provide metrics and insights on the day-to-day operations of your SOAR activities, whether it's automation and orchestration tasks or the efficiency of your incident and case resolution.
Starting from Splunk Phantom 4.0, you have the ability to leverage your existing Splunk deployment as the datastore for Phantom. This integration is as native as it gets and allows you to investigate and report on your Phantom data.
To make it easier to gain insights from your Phantom data, we're happy to introduce the Splunk App for Phantom Reporting, available now for download on Splunkbase to provide you with out-of-the-box visualizations for Phantom data.
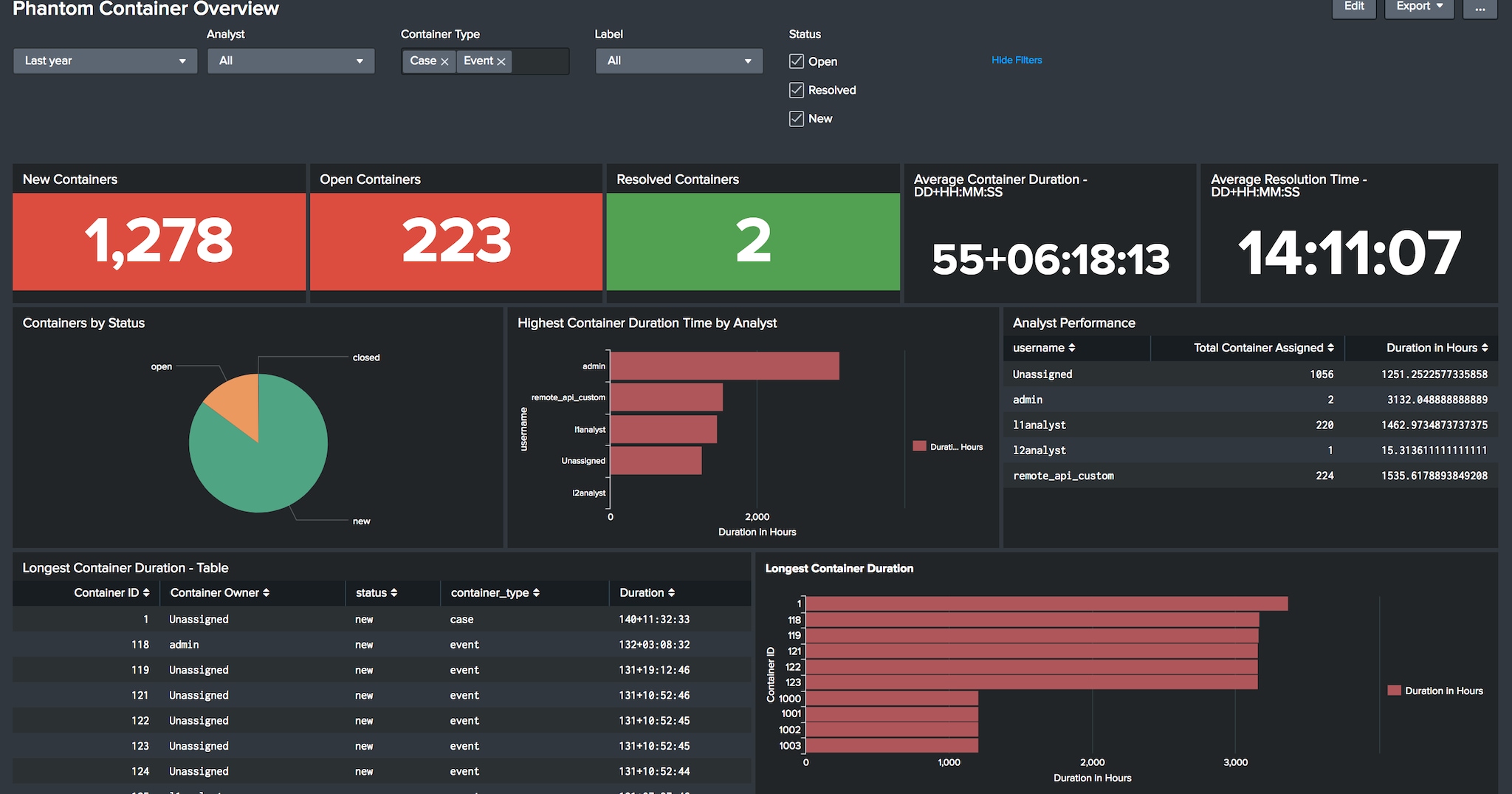
Interested in measuring case/event resolution times? Tracking unassigned cases? Monitoring cases that have exceeded their SLAs? You got it. You can track those metrics at the aggregate level, or slice and dice the measurements by analyst, by label, or by container type.
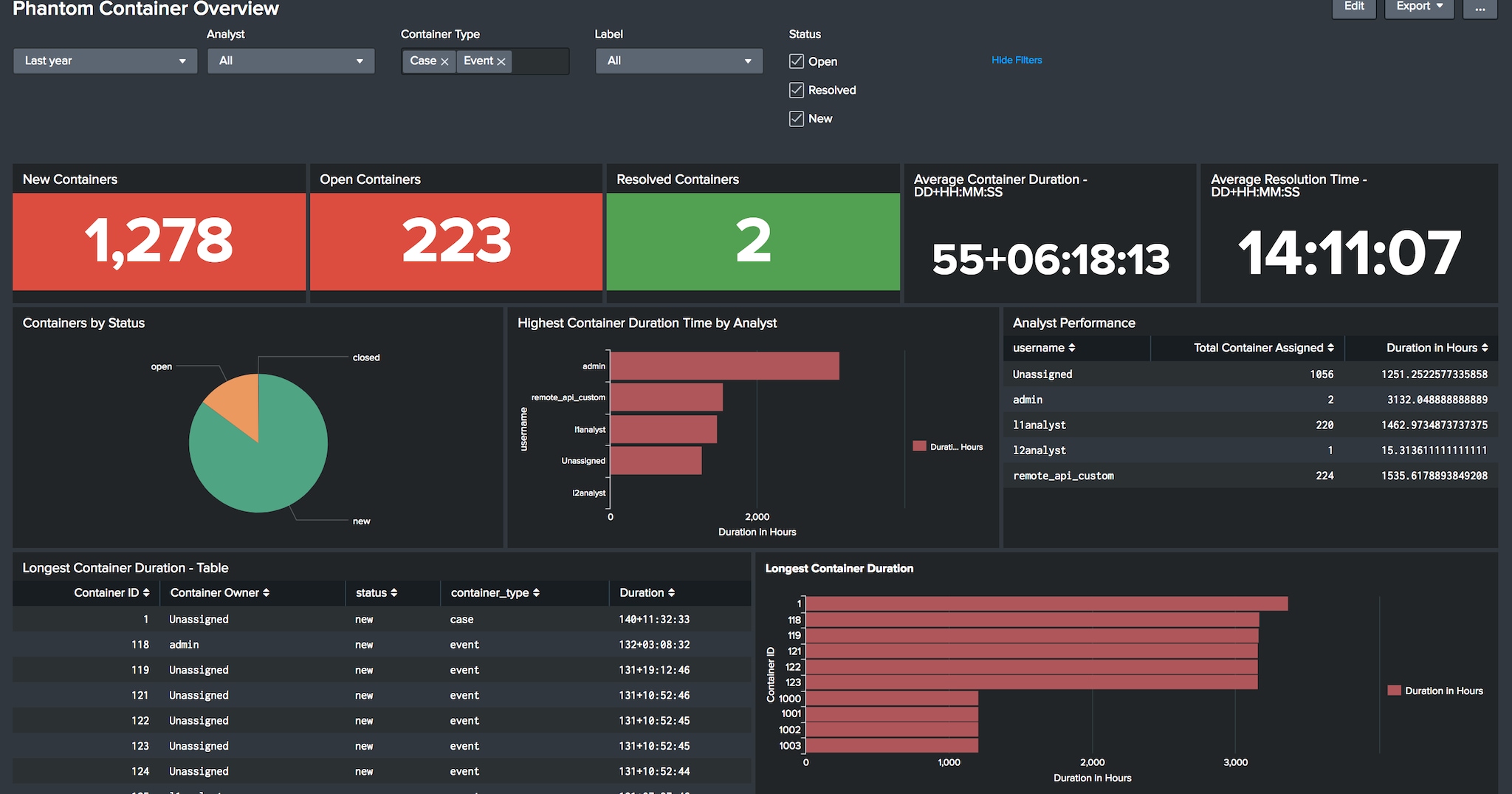
How about measuring activities by individual case or event? You’ll find that in the app too.
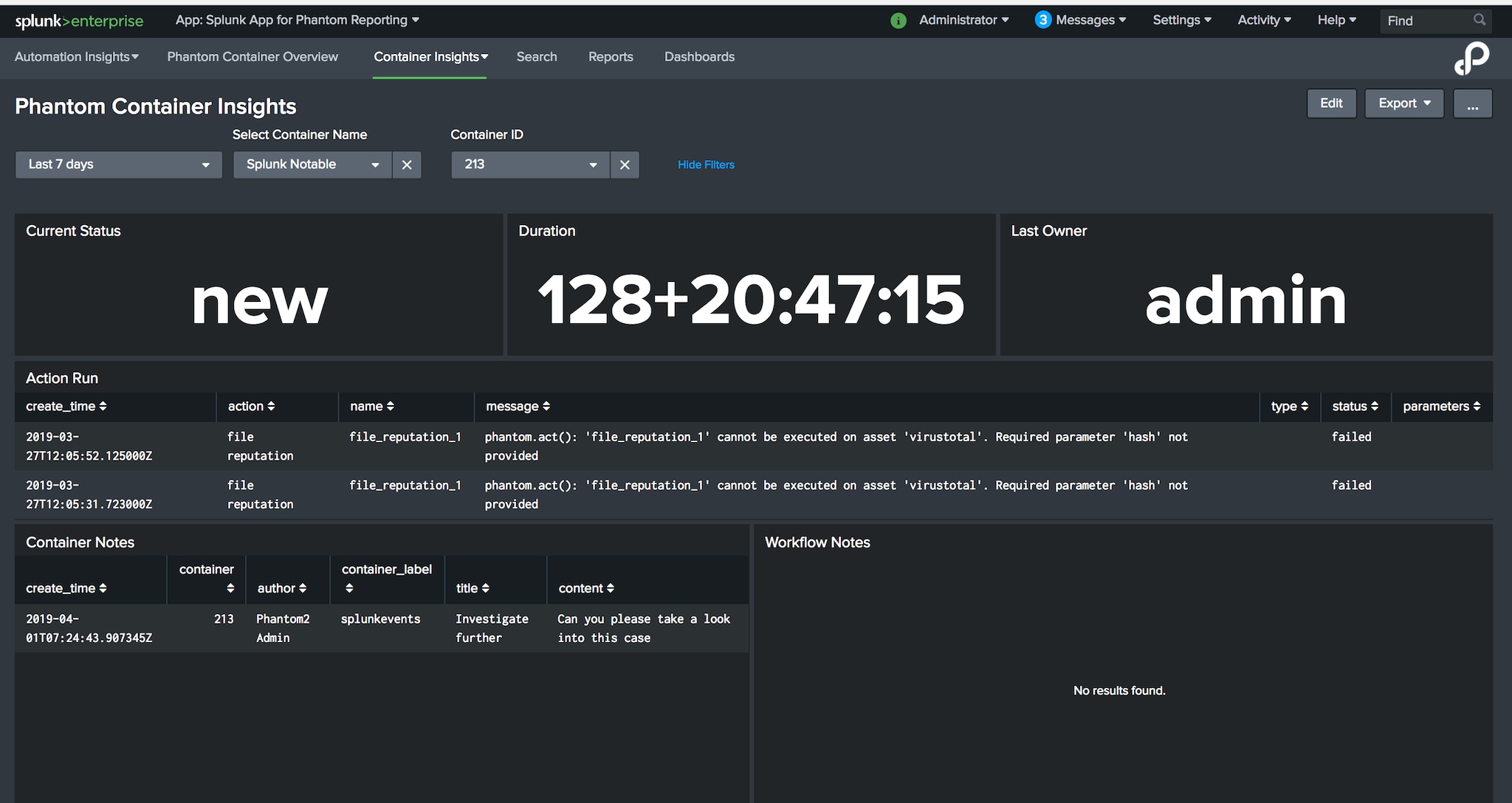
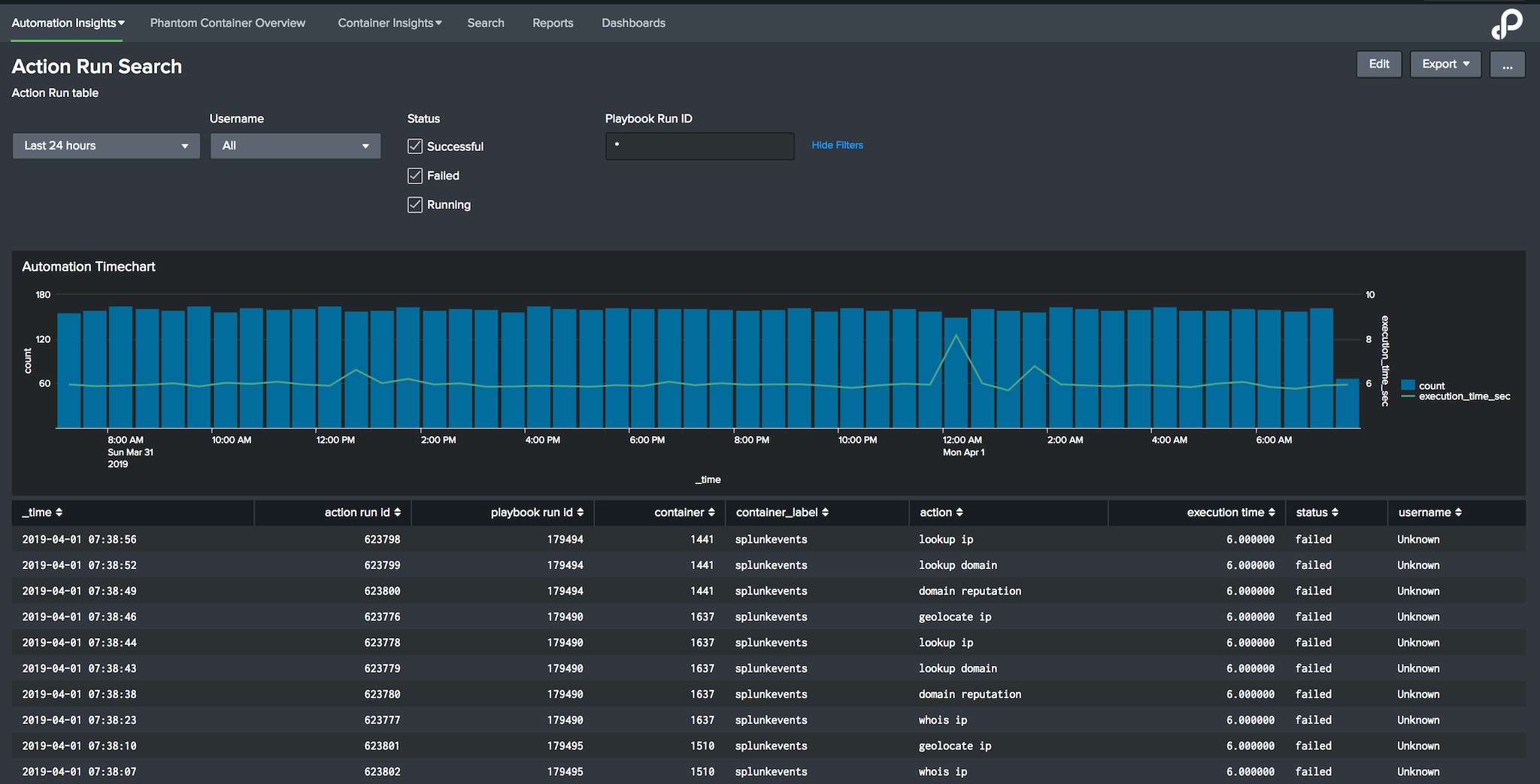
How about measuring the execution time or failed runs of actions or workflows? You now have the ability to get insight into the status of your automation and calculate various related metrics.
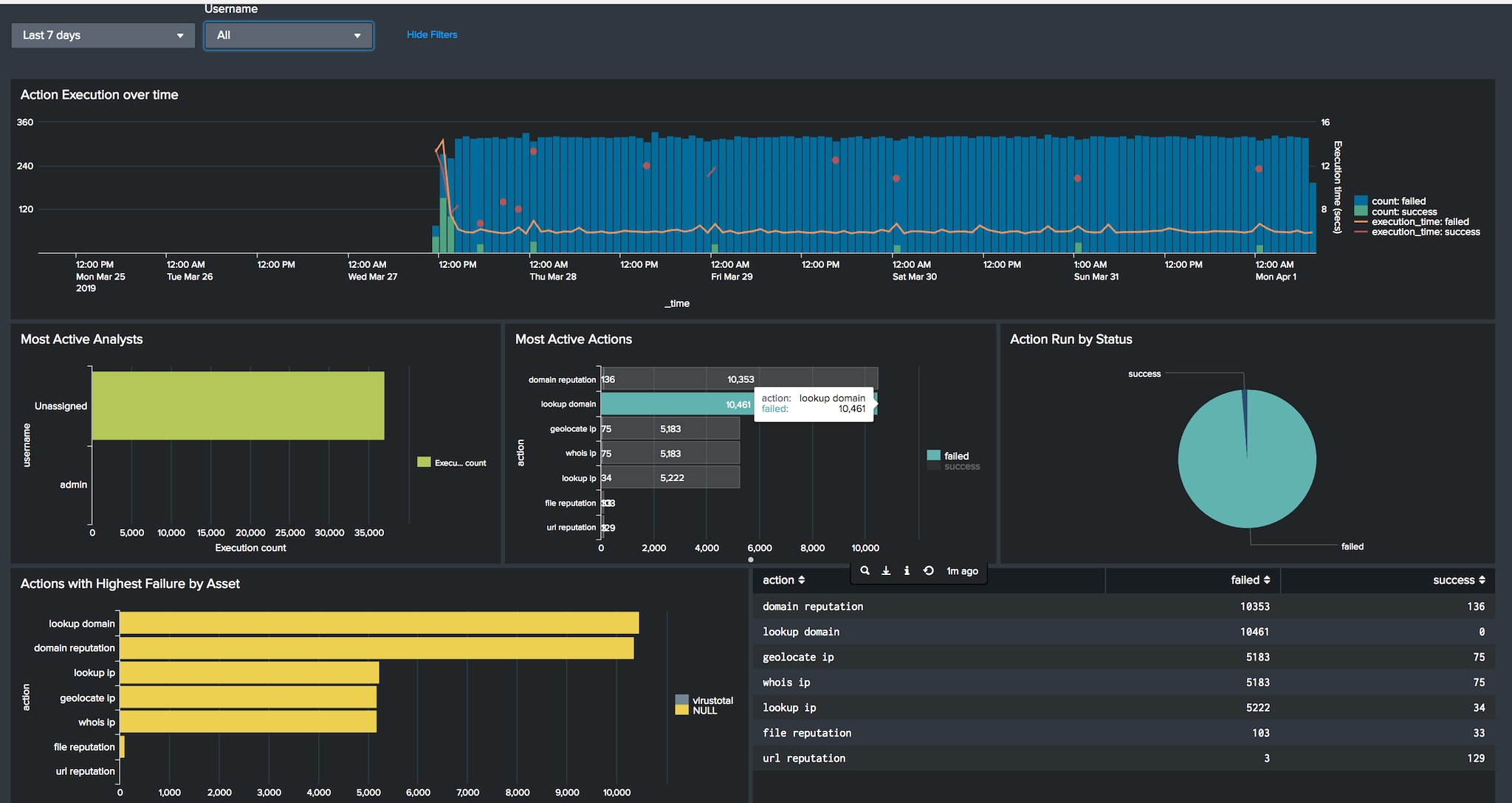
Want to filter individual automated tasks that failed, broken down by assets? Look up individual notes associate with any execution? You’ll find those answers as well.
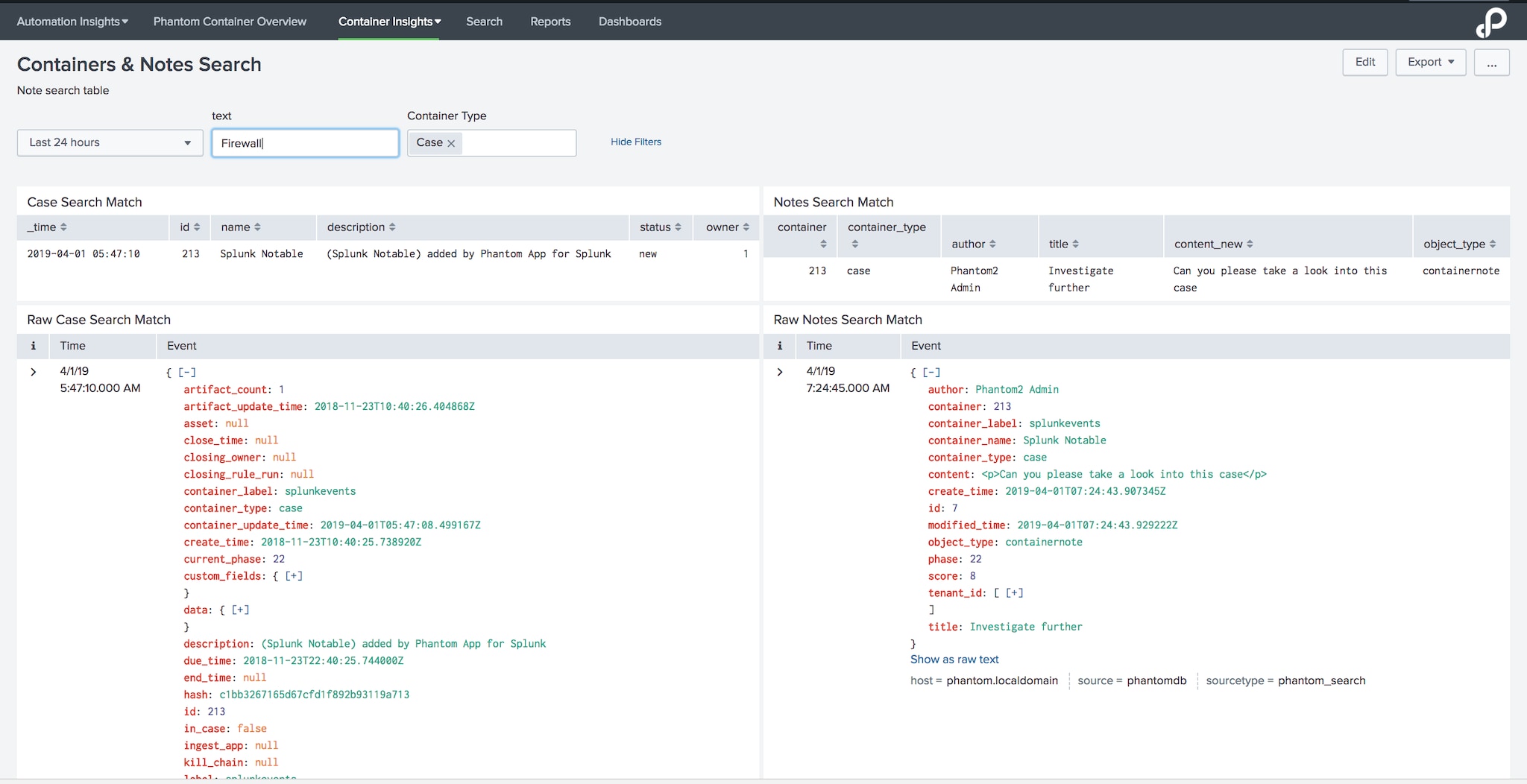
Last but not least, this app ships with an easy-to-use dashboard that lets you run free-form searches against container events—including all notes.
Just like any app you download on Splunkbase, this app is a template to be used as a starting point to build your own custom visualizations. Needless to say, with Splunk’s alerting capabilities, you can turn any of the dashboard items shipped within this app into an actionable alert. For instance, trigger an alert to your SOC manager when a case hasn’t been updated for a given period of time, or even trigger an alert to your Phantom system admin when an action is constantly failing against a specific (and likey misconfigured) asset.
Please give the Splunk App for Phantom Reporting a try and let us know of any feedback you. Happy Splunking!
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




