Splunk's Attack Range Provides a Simple Framework for Generating Attack Data

Security has always been a sophisticated cat-and-mouse game and a creative one at that. Attackers' techniques constantly mutate and evolve, like biological viruses, forcing security professionals to continuously evolve their strategies to combat them. In an ideal world, companies could and would be able to devote a sufficient number of resources to ensure that they keep pace with the bad guys. But there is no such thing as an ideal world.
While Internet resources can be helpful for analysts as they endeavor to stay abreast of new attack trends and techniques, deeply understanding and replicating public exploits requires capabilities beyond those of the common SOC. Unfortunately, the security industry isn't much help. Companies tend to protect their defense artifacts updates (such as antivirus or firewall signatures) so they can monetize them. Even in groups or organizations that share such information, it comes in very specific forms that won't reveal the whole picture (i.e., a compiled binary that may contain malicious code instead of the actual exploit source code, for example). Further, in most enterprises, the simulation or replication of attack code is simply banned.
In an effort to address this problem, the Splunk Security Research Team recently released a framework for replication, verification, and data production of attacks in a shareable, community-friendly fashion. It is instrumented to send data to a Splunk server. The Splunk Attack Range framework allows the security analyst to quickly and repeatedly replicate and generate data as close to "ground truth" as possible, in a format that allows the creation of detections, investigations, knowledge objects, and playbooks in Splunk Phantom.
The Attack Range lets you streamline multiple facets of the attack cycle in a single framework, helping speed response and produce defense artifacts or countermeasures. It also helps shepherd the community towards developing common criteria for tactical SIEM application, so analysts and researchers can share information and collaborate when facing past, current, and future threats.
The screenshot below shows the cloud-building process via Terraform.
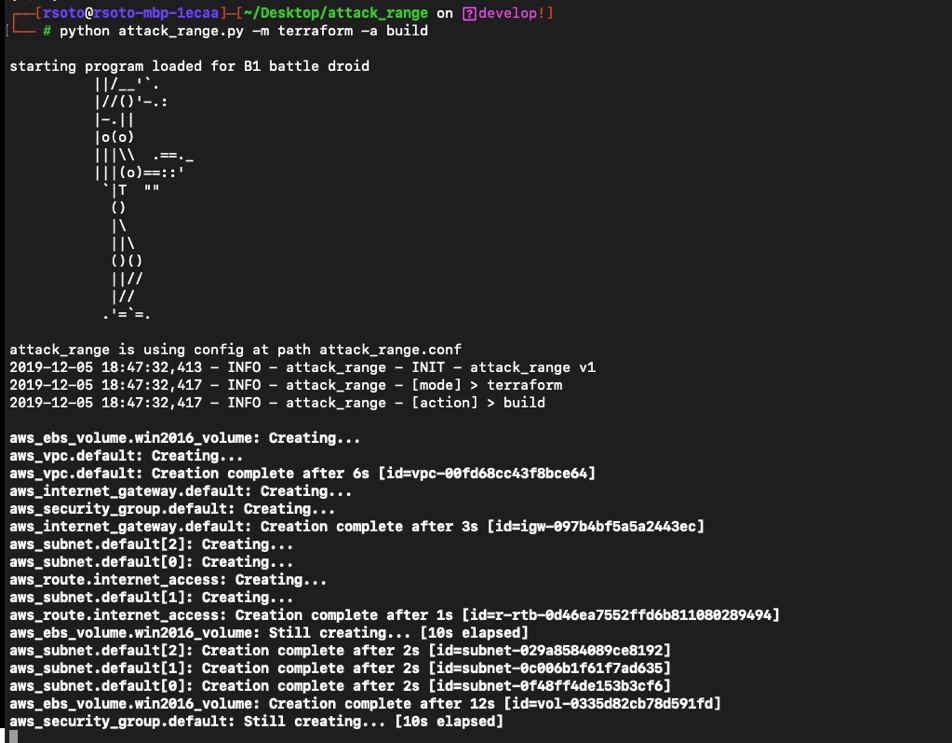
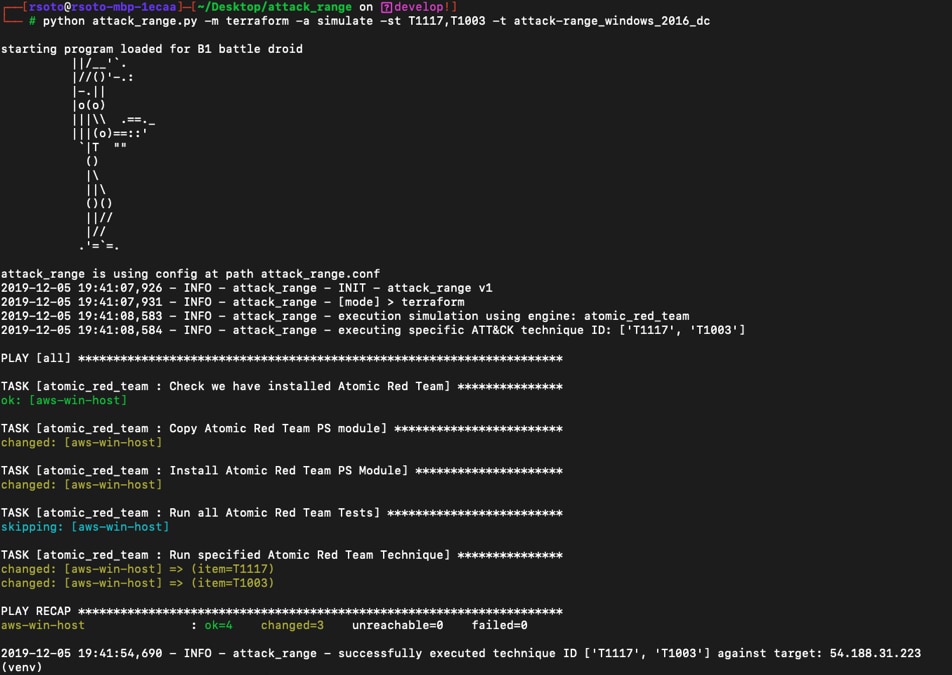
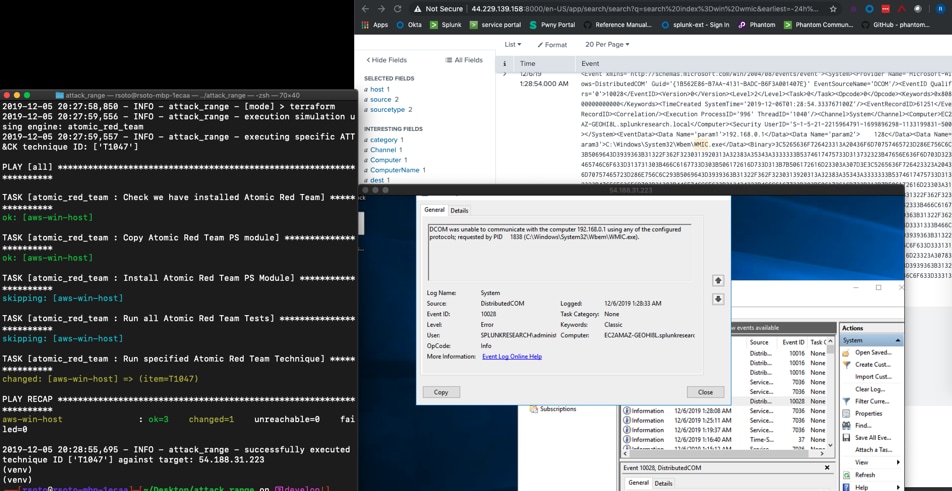
The data includes system logs, network captures, endpoint events, and so on, derived from either known attack-simulation engines (Atomic Red Team/AttackIQ) or recent exploit code on tailor-built local (Vagrant) or cloud environments (Terraform).
The screenshot below shows the cloud MIRE ATT&CK simulation techniques against a windows target.
The Splunk Attack Range helps analysts:
- Visualize and record attacks
- Translate attacks into measurable data
- Drive defense artifacts based on produced data (firewall, endpoint, Snort, etc.)
- Test malicious/exploit code in a safe and isolated environment
- Translate defense artifacts into the Splunk environment (detection, investigation, analytics, playbooks)
- Share artifacts (detection/investigation using Splunk Search Processing Language, Splunk apps and data models, both within the enterprise and the community)
The screenshot below shows the attack_range cloud setup with data collected from a MITRE ATT&CK T1047 simulation.
Recently, the Splunk Security Research Team published a whitepaper, "Using Splunk Attack Range to Simulate and Collect Attack Data," that delves deeply into the details of the new Attack Range app. It explains the architecture and design, requirements, contents of the repo, data models, and more. Once you've read more, head over to the repo and check it out!
We'd love to hear your comments and questions. Email us with either at research@splunk.com.
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.