Securing a New Way of Working: Who Let the Data Out?
As humans, we instinctively feel more empowered when operating in our own physical environment (i.e. home) as opposed to the office. In some cases, this might lead to risky behavior — not always underpinned by malicious intent. As an example, an employee might feel it is easier to copy some data onto their USB or print confidential documents. Potential detections there include Data Exfiltration after Data Staging, Multiple DLP events by User, and more. In the next section, we will be showcasing how the Data Loss Prevention (DLP) data source can be used for detecting this type of behavior.
Let’s observe the approach of implementing the relevant detections through the lens of one of the most commonly used cybersecurity frameworks, MITRE ATT&CK.
One of the Tactics defined in the framework is Exfiltration (TA0010). According to MITRE “Exfiltration consists of techniques that adversaries may use to steal data from your network.” There are 10 Techniques defined under Exfiltration ranging from Automated Exfiltration to Transferring Data to a Cloud Account. SSE provides all relevant Security Content and guides to help you get started.
Let’s start by searching the available Security Content filtering on the Exfiltration Tactic:
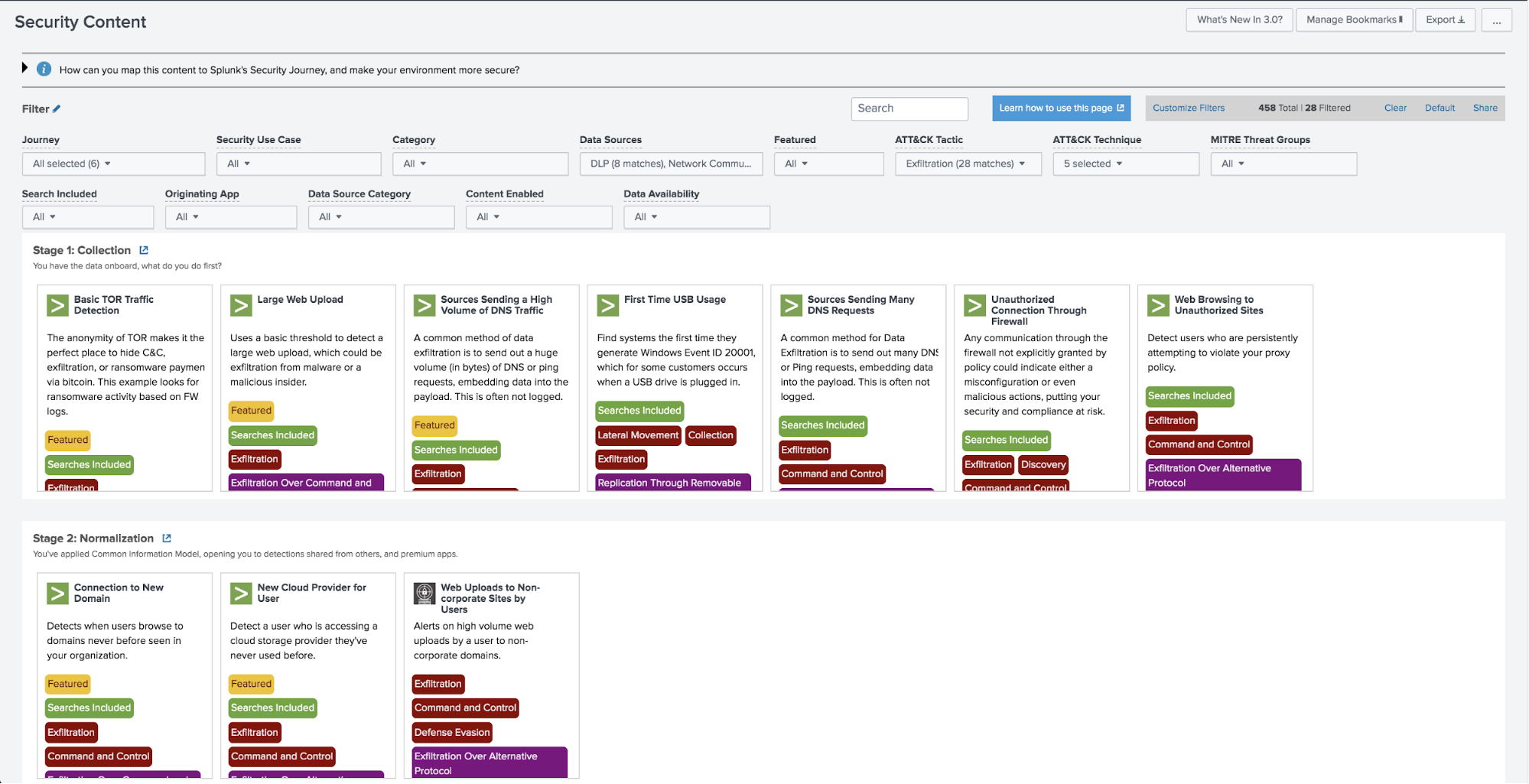
There are 28 Detections returned in total but let’s focus on two for now:
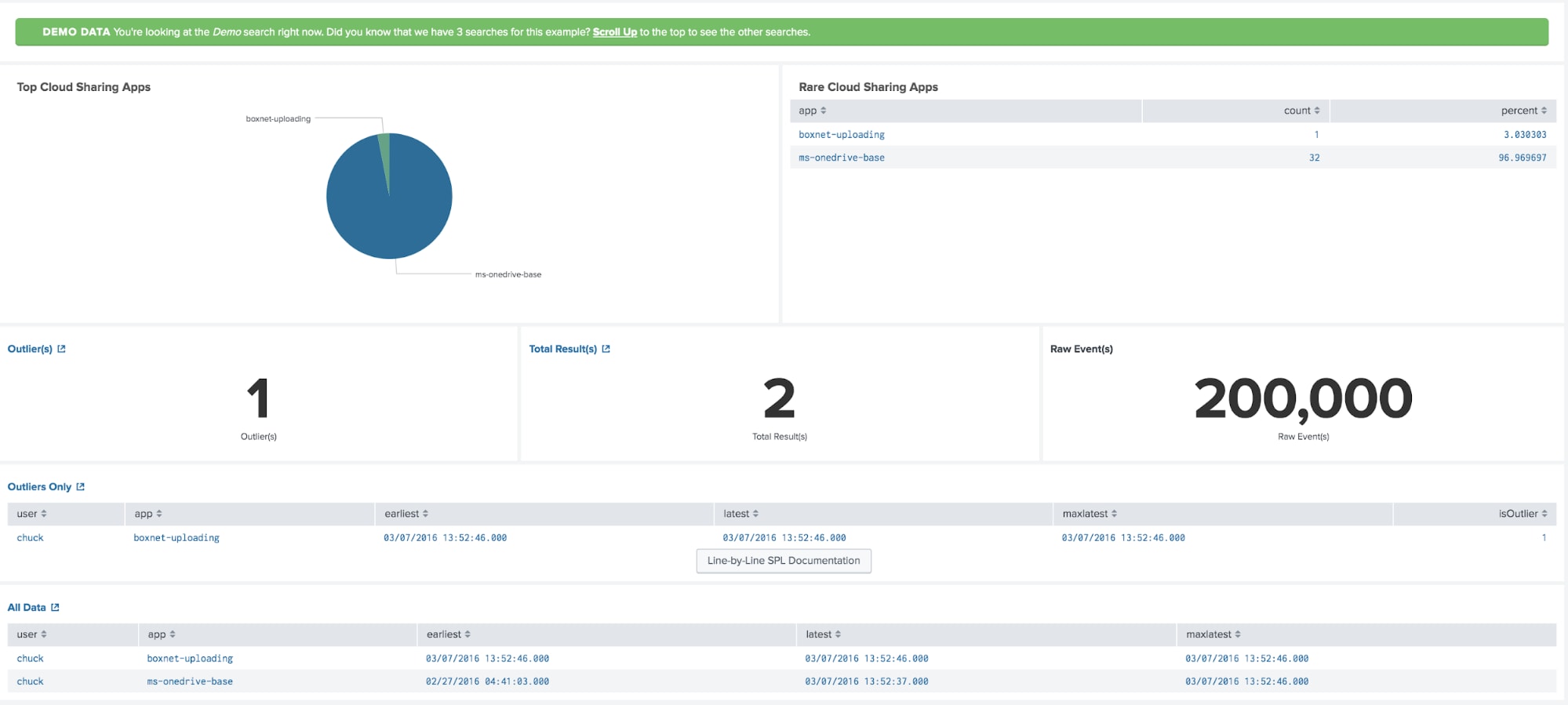
New Cloud Provider for User: Detect a user who is accessing a cloud storage provider they’ve never used before. (Data source: Web Proxy)
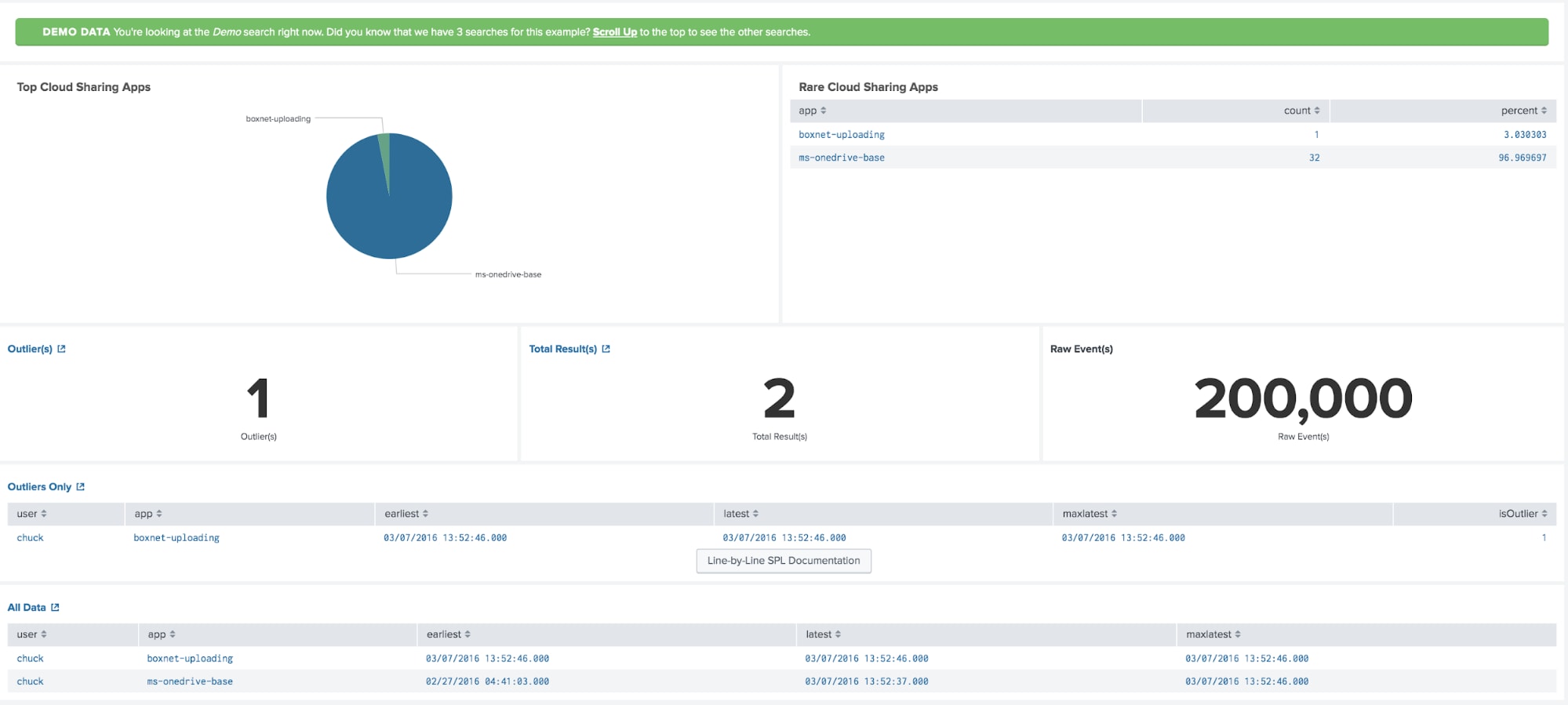
This is useful to detect cloud providers that the users haven’t used before. Be aware that the change in work-from-home mode might actually mean that you will have to tune the thresholds.
Many USB File Copies for User: Build a baseline of how many file copies each user does to USB media, and detect when a user copies an uncharacteristically large number of files. (Data source: EDR, DLP)
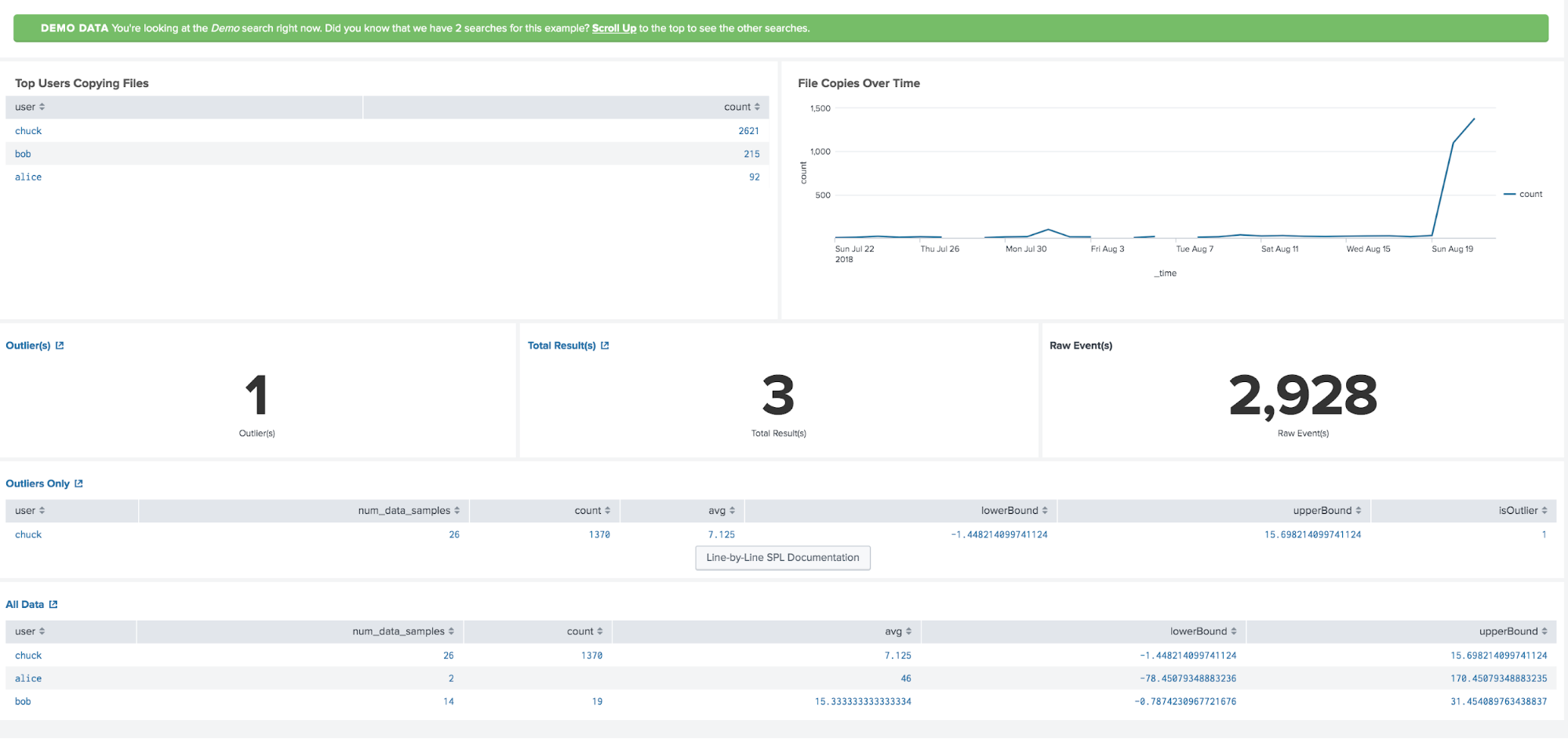
This is focussed on copying files to USB media, again special attention should be given on the new operating model. If on the other hand there is a clearly defined No-USB policy, then you would want to be alerted with low thresholds.
Check here for more practical guides on how to secure your organization in the new work-from-home era.
Thanks to the contributors of this blog post, Bryan Sadowski, Lily Lee, Rene Aguero, James Brodsky, Chris Simmons.
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




