Protecting Your Assets: It’s Not Just About Servers and Laptops!
In most of our blogs, we spend a TON of time going on about protecting our endpoints, looking at sysmon, checking the firewall, correlating IDS data and the like…
Today, we're going to shift gears a bit and look at security from a different angle. Recently, there has been a tremendous focus on the shifting paradigm of a workforce that primarily resides in corporate offices, to a highly virtual workforce sitting at their kitchen tables. This completely changes how you collect and monitor security events. While this is certainly something that can be accomplished, another aspect that needs to be considered is how physical security monitoring of your now empty or nearly-empty office space and virtual employees is addressed during this shift as well.
Collecting events for physical security has been discussed for a good long time now. I recall sitting in briefings over 15 years ago reviewing the correlation of virtual and physical events concurrently and building use cases off of the data. Unfortunately, many organizations have chosen not to integrate physical security events into their use cases or, due to the way organizations are structured, physical security does not align with cybersecurity, making this data silo-ed. Our goal today is to demonstrate why you should collect and incorporate physical security events into your overall monitoring strategy.
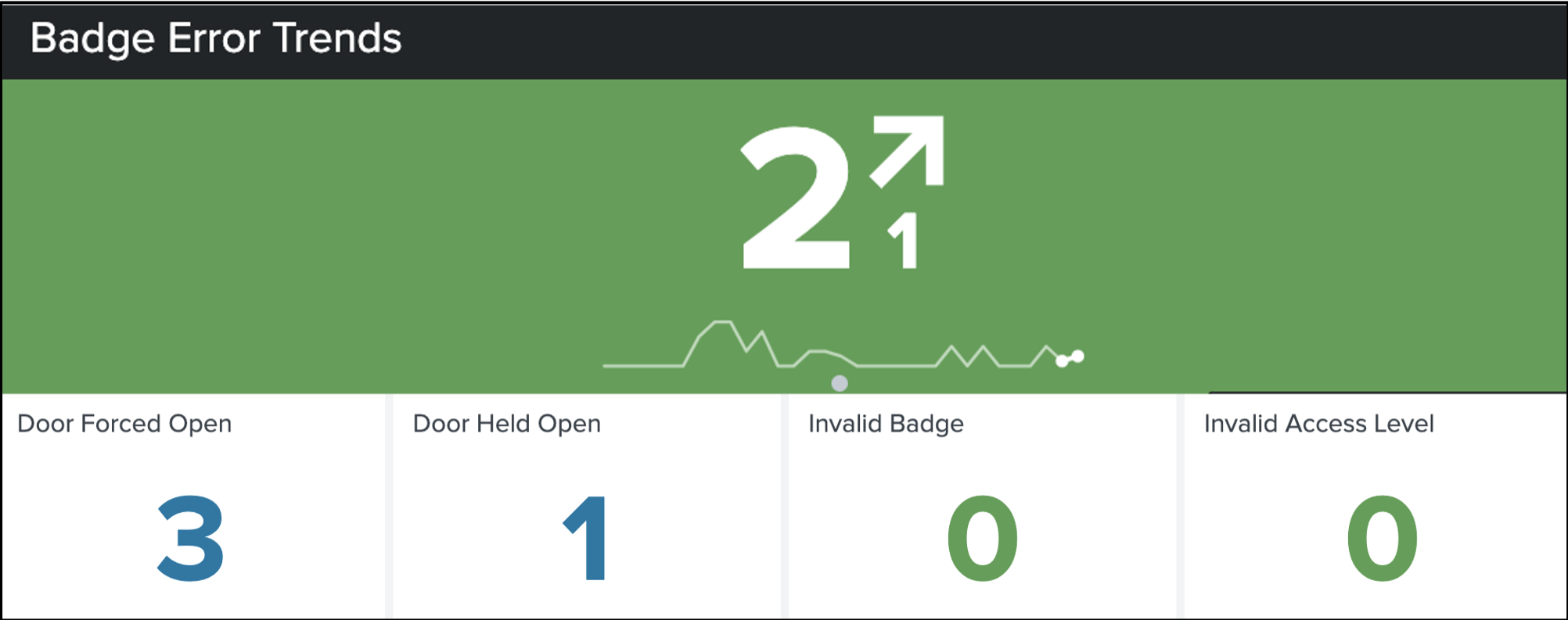
The most basic use case that jumps to mind whenever physical security is mentioned is badge activity. Monitoring badge activity can provide you with a view of who is accessing facilities, as well as who is attempting to access facilities without authorization. The timing and frequency of these events can be of value to the security team and can be useful to both monitor user activity, as well as system health, to determine if the card readers and sensors are working properly.
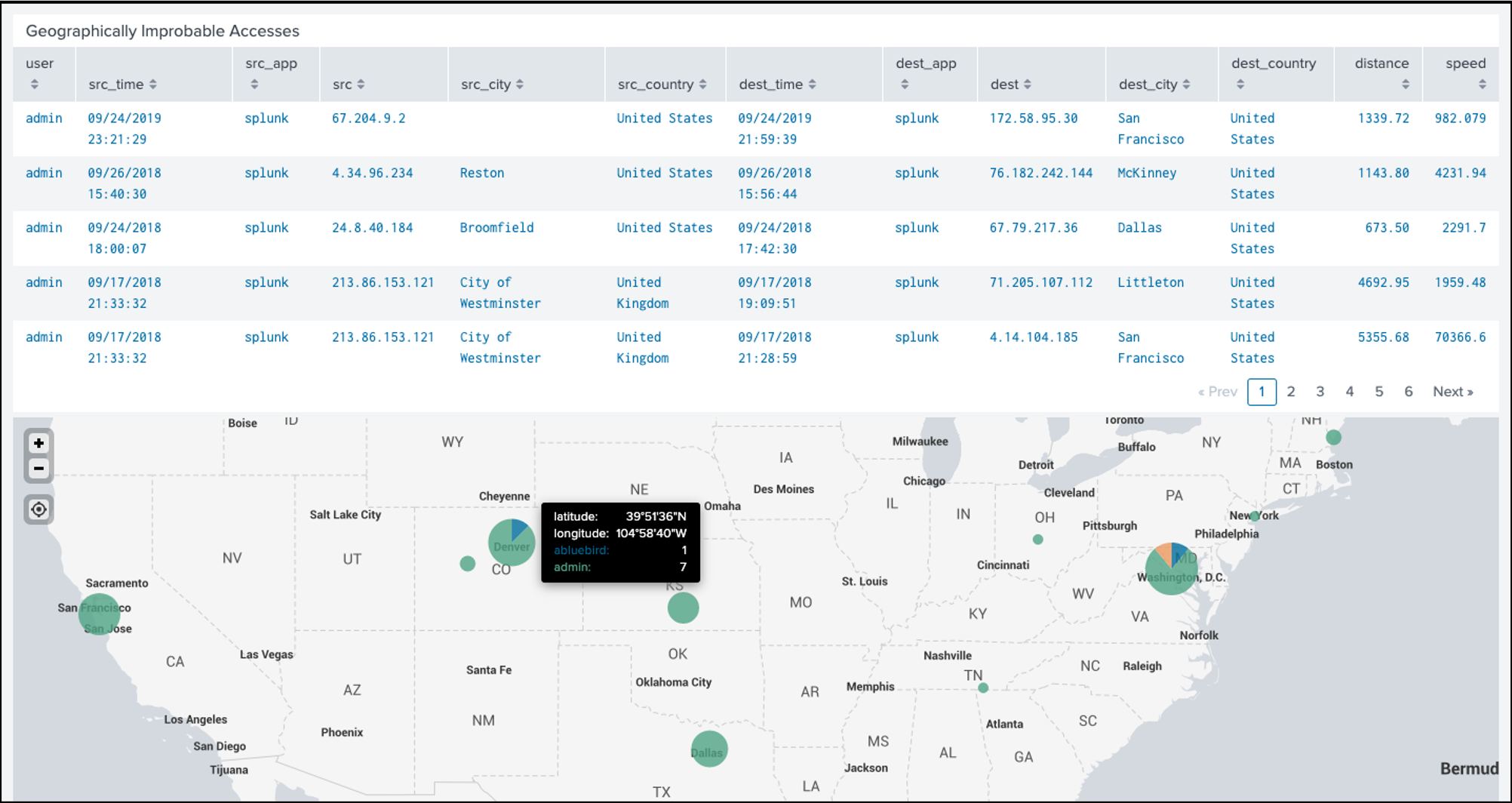
Another common use case is to combine VPN logs and physical access events to determine if individuals are connected to the corporate infrastructure while being physically badged into a workplace. A variation of this use case is to look at the location of authentication activity and compare it to the last known location of this user, based on their badge data, and determine if the time to have physically traveled that far is possible. While we are on the topic of authentication events, if you don’t have badge data yet, (even though you should), another variation of this is to look for authentications in geographically disparate locations with a small amount of time between them. We refer to this as the “superman” rule because there are limitations in how quickly one could login from Reston, Virginia and travel to McKinney, Texas and then login again. This rule is a dashboard and a correlation search and is default content in Splunk Enterprise Security.
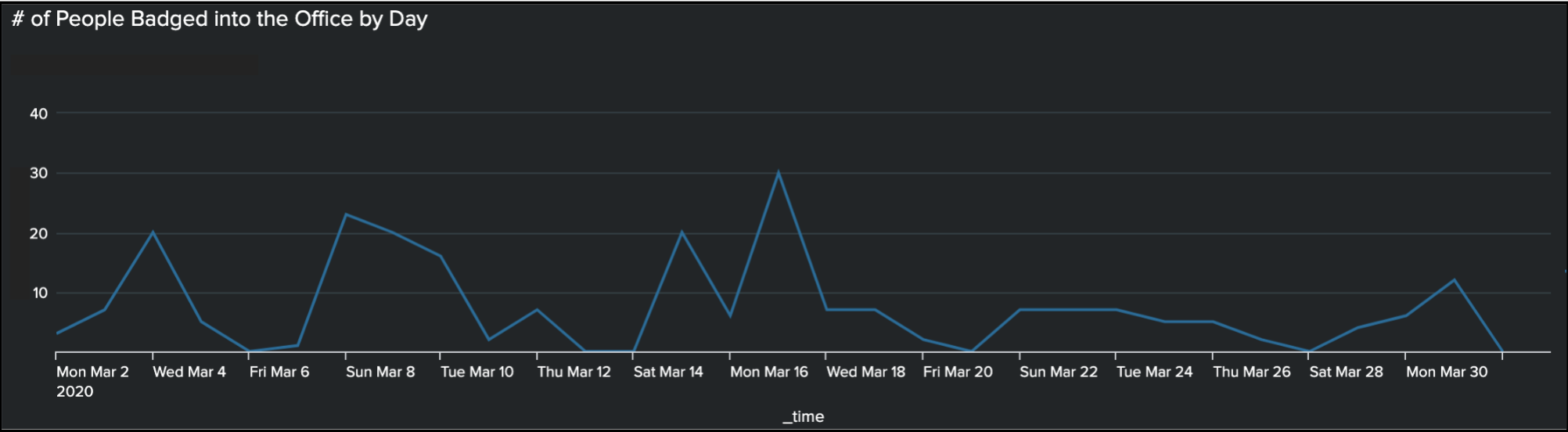
Another interesting correlation to look at is the discrepancy in the number of people badged into an office versus the number of people logged in to the network. This could help identify the volume of people who may have tailgated into the office, rather than swiping their badge upon entering.
OK, Delia and John. You’ve just overflowed my buffer... Help me out with the here and now...
A great reason to collect physical badge data may sound basic but really makes loads of sense, particularly as events transpire around the world. Quite simply, having access to badge data can be helpful in gathering a list of employees in an impacted geographic area to better communicate information to that specific audience directly. It also allows you to have a more accurate idea of how many people you are accountable for. Rather than trying to account for all 500 employees assigned to an office after an emergency, you can focus on the 350 that you know badged-in that day.
What I want to highlight now, are some interesting use cases that Splunk has been performing, up to and throughout the current COVID-19 pandemic.
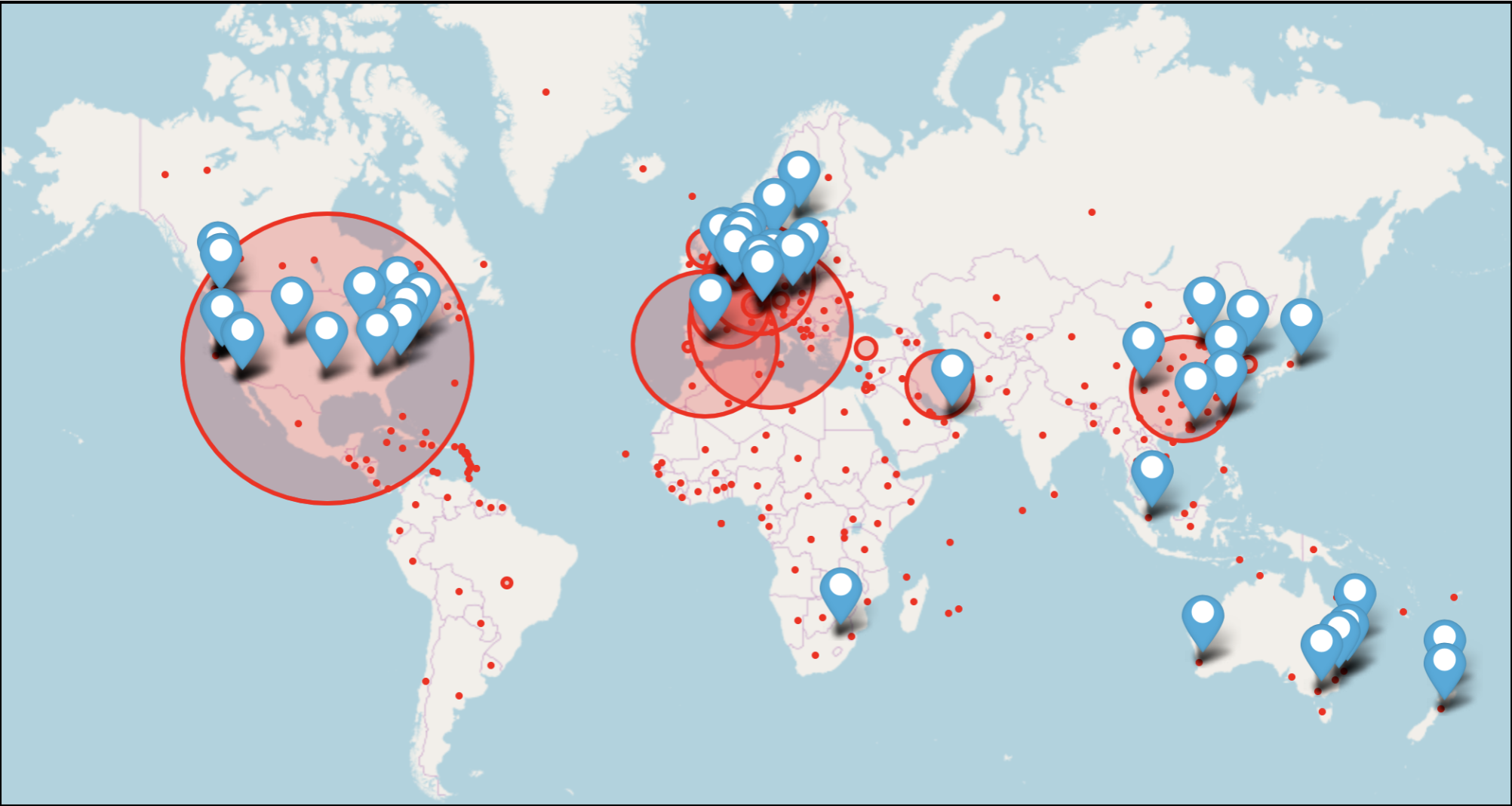
By monitoring the corporate travel system, the physical security team has the ability to identify employees who may be stuck in a specific area that has international travel restrictions in place or are about to be implemented. This awareness provides an opportunity to be proactive in reaching out to employees and providing assistance in extracting them. Most countries announce their border closures or quarantine efforts 24 hours in advance, so if your travel system is hooked into Splunk, you can quickly identify who is where and initiate extraction procedures.
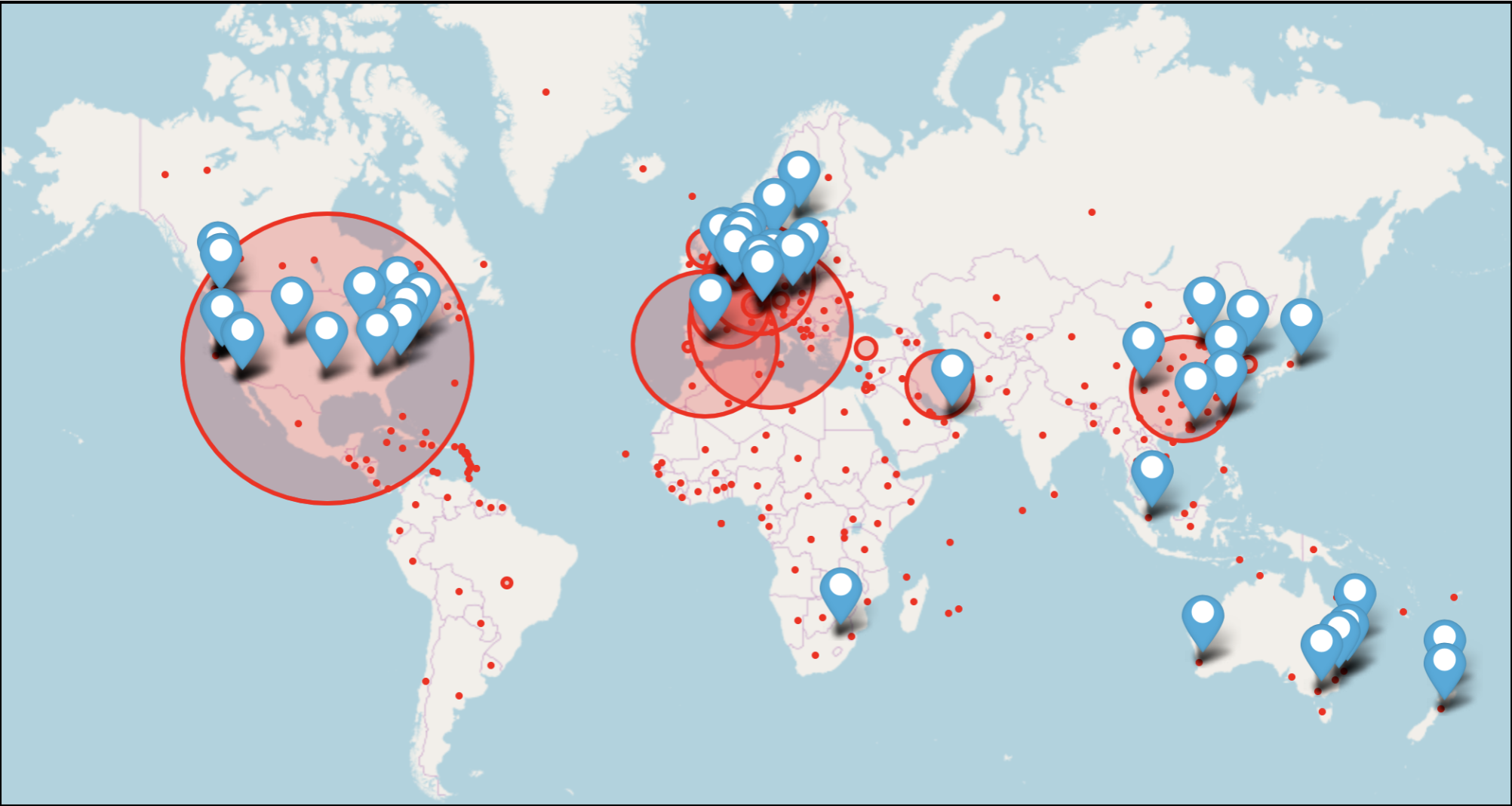
Another use case that has been developed internally is to correlate office locations with known COVID cases globally and use this to help in decision-making on when to close (or re-open) offices.
One final use case to mention; with specific offices being closed, it is important to be cognizant of who is attempting to enter these offices during a closure. Certain staff may need to be in these offices, so having visibility into the roles of those attempting to enter the buildings can be important to monitor.
We realize we threw a lot at you in a very short period of time. Some of these use cases may have applicability to you, however some may not. Larger organizations with a globally dispersed workforce are going to have different needs than a smaller regional based organization, but we hope we have provided everyone with a few physical security use cases that you can deploy.
As more employees are spending time working from home in these current times, we need to continue to have visibility into our brick and mortar assets, even if less employees are in them.
Thanks and happy Splunking!
Delia Olsen & John Stoner

----------------------------------------------------
Thanks!
John Stoner
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




