Between Two Alerts: Phishing Emails – Less Ocean, More Aquarium

 When we discuss Splunk Phantom with customers here at Splunk, we end up talking about phishing pretty frequently. As discussed in a recent blog post, "Phishing Emails — Don’t Get Reeled In!," phishing is a super common issue that almost everyone deals with ad nauseum. It’s also a nuisance to investigate. The good news is that automation excels at dealing with repetitive, mind-numbing workflows like phishing investigations. As Tim and Olivia demonstrate in this "Between Two Alerts" webinar, Splunk Phantom can take a pesky, monotonous process like phishing email triage, and make it easy.
When we discuss Splunk Phantom with customers here at Splunk, we end up talking about phishing pretty frequently. As discussed in a recent blog post, "Phishing Emails — Don’t Get Reeled In!," phishing is a super common issue that almost everyone deals with ad nauseum. It’s also a nuisance to investigate. The good news is that automation excels at dealing with repetitive, mind-numbing workflows like phishing investigations. As Tim and Olivia demonstrate in this "Between Two Alerts" webinar, Splunk Phantom can take a pesky, monotonous process like phishing email triage, and make it easy.
At Splunk, we frequently use the term GDI, or “get data in.” When it comes to phishing emails in Phantom, getting the data in is particularly powerful, and ultimately what builds the foundation which facilitates easy investigation.
Splunk Phantom is a little bit different from products like Splunk Enterprise Security (ES) or Splunk IT Service Intelligence (ITSI). Rather than deployed as a premium application on top of Splunk Enterprise, it’s actually a standalone application, and can be tightly integrated with the rest of the Splunk suite. This means that getting data in, or “ingestion,” is a bit different than the other Splunk products. We’re not looking to ingest supporting information like raw logs of every web request — we can automatically go get that later. Instead, the data we look to “ingest” is data that you want to use to kick off a process: alerts from your SIEM, threat intelligence from your threat intelligence platform (TIP), tickets from your ticketing system, or in this case, phishing reports from users.
The vast majority of data ingested into Phantom is ingested using its “apps,” which are essentially the integration points and translation tools between Phantom and the various products and services in a security team’s environment. The app works with the APIs of the external products, collecting alerts (notables, tickets, IOCs, emails, etc.), and turning them into “events” within Phantom.
For email, Phantom has an IMAP app that allows it to ingest emails from any provider that supports IMAP, which is just about all of them. For certain services, like Exchange, Office365, and Gmail, Phantom also has service-specific apps that implement additional “actions,” or commands such as “run query” or “delete email.”
Many of our customers make use of a phishing report inbox for users to forward suspicious emails manually or use something like the PhishMe button. As you can see in Figure 1, we’re automatically pulling from this type of mailbox using the built-in IMAP app.
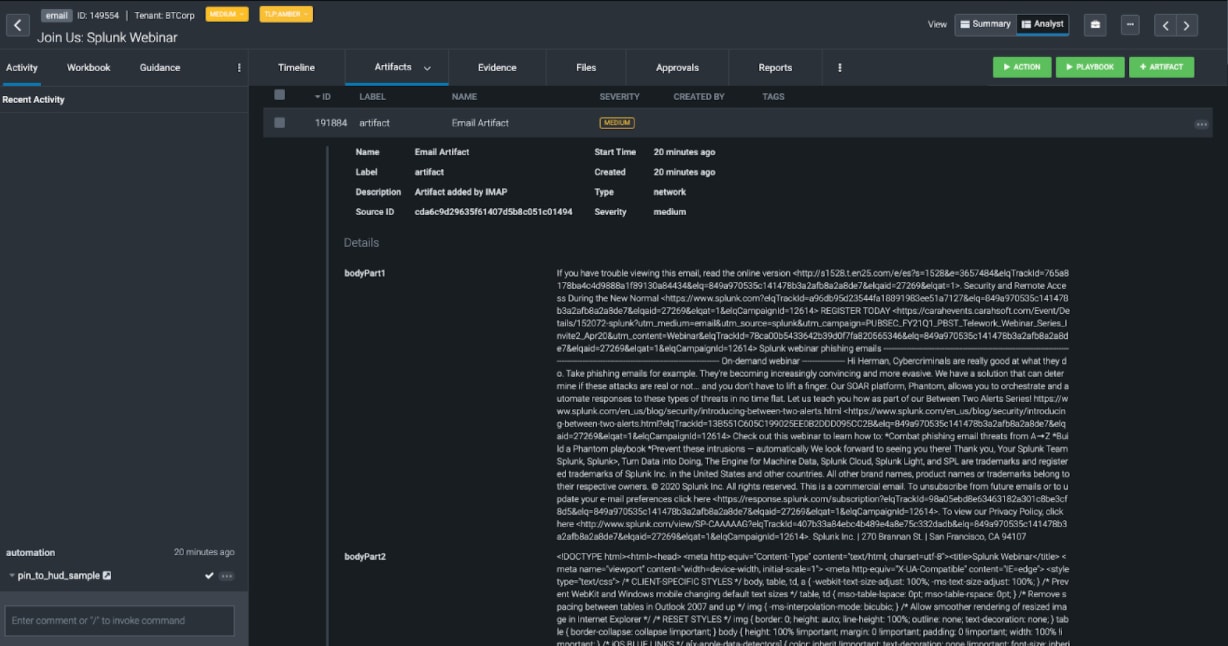 Figure 1
Figure 1
The first thing we see (in Figure 1) is that an event was created where the email in question was brought in as an “artifact,” or piece of technical information. For starters, the email itself.
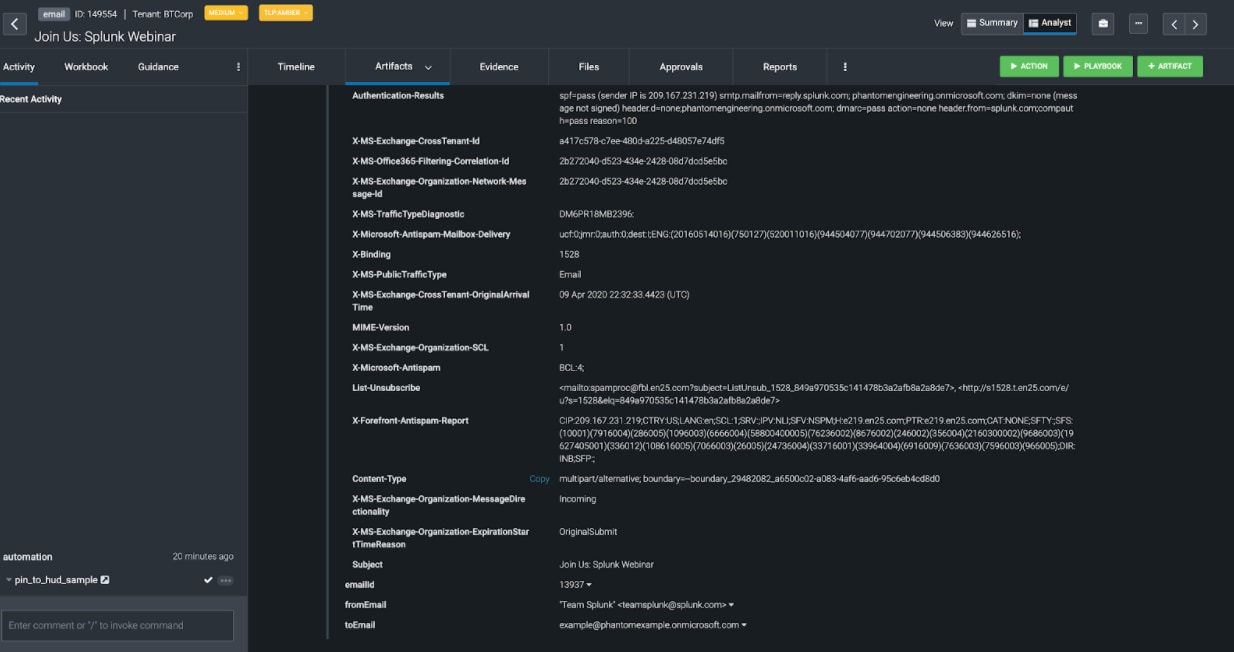 Figure 2
Figure 2
Scroll down a little bit further (see Figure 2) and we see that not only was the email brought in, but all of the headers are individually parsed out as well. Artifacts are basically a set of related key-value pairs. That means that all of these fields are trivial to use in a playbook (as demonstrated in this webinar). But the out-of-the-box ingestion capabilities don’t stop there!
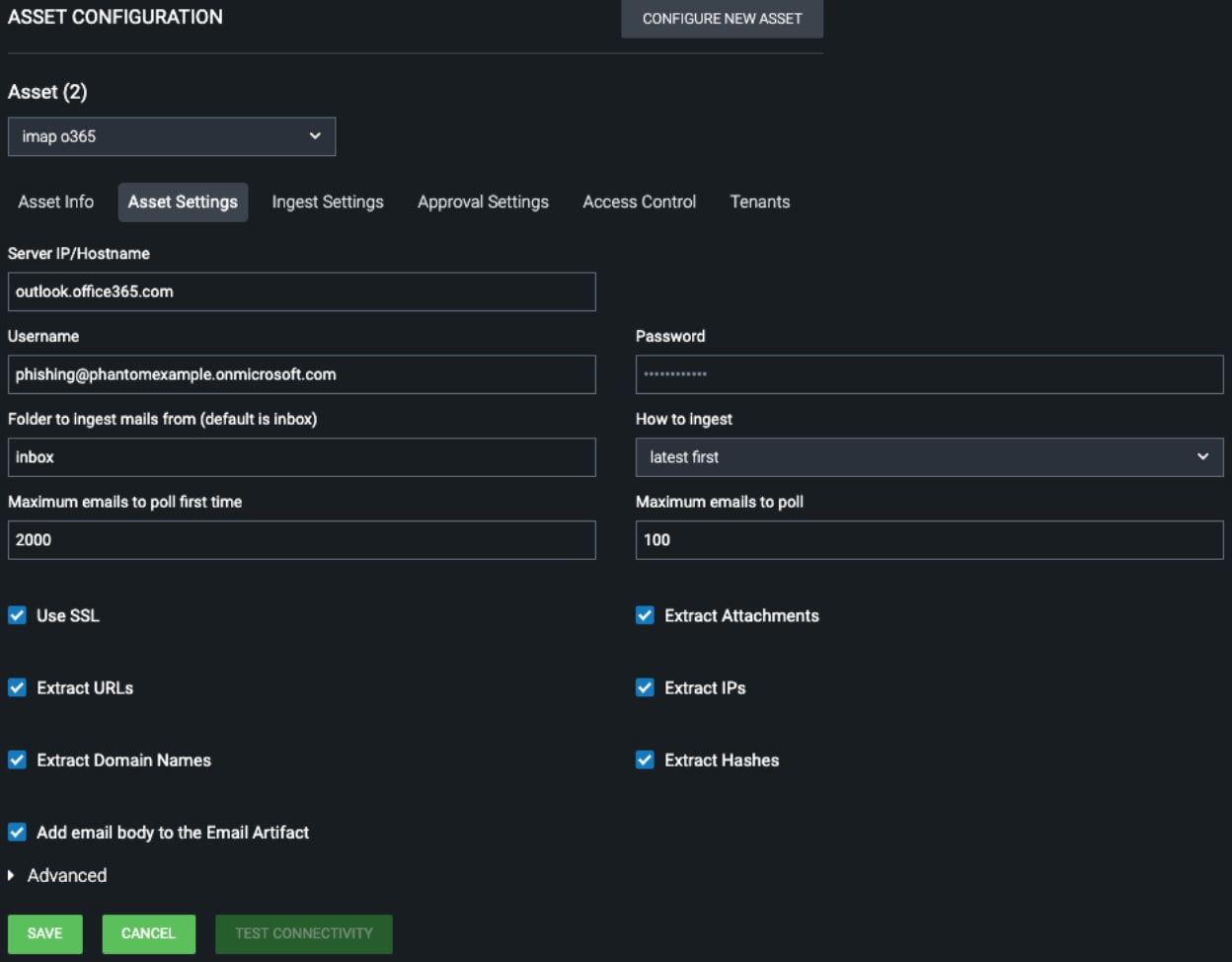 Figure 3
Figure 3
In Figure 3 above is an example of an “asset” configuration. An asset is an individual configuration of a tool, so while Phantom can support multiple IMAP configurations alongside each other, this is an individual configuration. Down at the bottom of Figure 3 you can see a bunch of checkboxes telling the IMAP app to extract indicators.
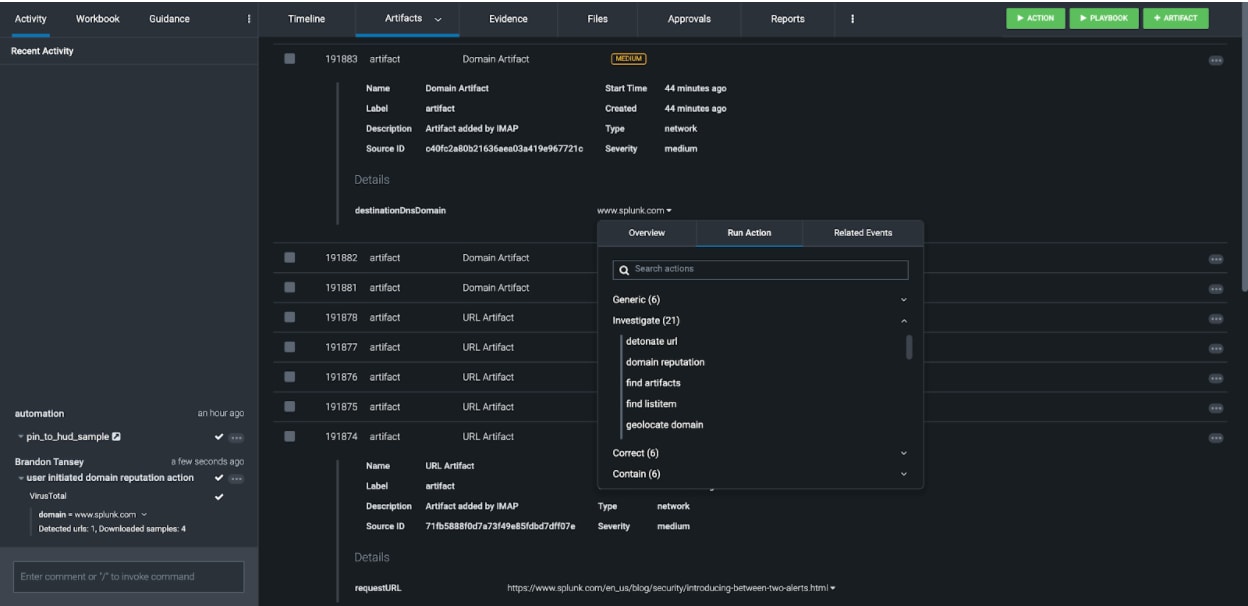 Figure 4
Figure 4
As simple as that, we can see all of the domains, URLs, etc. parsed out of the email into individual artifacts, which makes them trivial to investigate via the GUI (as seen in Figure 4) or automatically via a playbook.
See It in Action
When it comes to triage and investigation, whether automated or not, having all of your ducks phish in a row is the foundation of a quick and solid investigation. Phantom’s out-of-the-box email ingestion lines them up so you can knock them all down as easily as possible. To see some of the next steps in action, tune in to our Between Two Alerts webinar episode, "Phishing Emails — Don’t Get Reeled In!"
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




