Using Splunk User Behavior Analytics (UBA) to Detect Malicious PowerShell Activity
Microsoft designed Windows PowerShell to be a powerful, flexible tool for efficiently automating and solving a lot of administrative tasks. It accomplishes this goal so well that for years bad actors have been leveraging it to penetrate both systems and networks, mounting difficult-to-defeat attacks. In 2016, Symantec analyzed 111 threat families that used PowerShell and found that 95.4% were malicious. It also concluded that these types of attacks were on the rise and that they represented a major threat to enterprises.

The first step to enabling detection is to begin logging PowerShell activity. Fortunately, Microsoft has gone a long way to improve the security transparency of PowerShell. PowerShell 5.0 has enhanced logging, which records executed commands and scripts and de-obfuscates code, output, and transcripts of attacker activity. (FireEye has links to detailed instructions on how to turn on logging.)
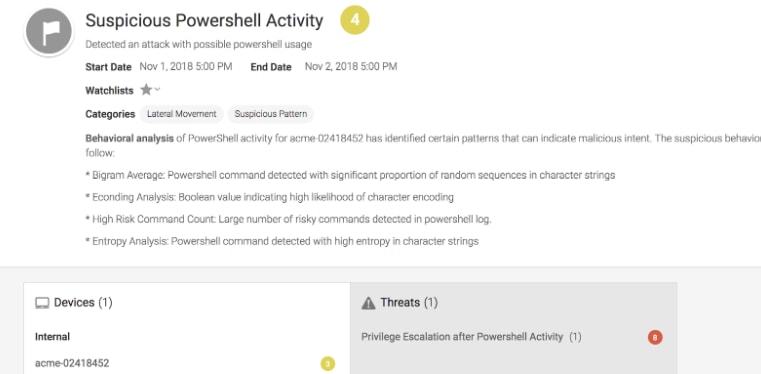
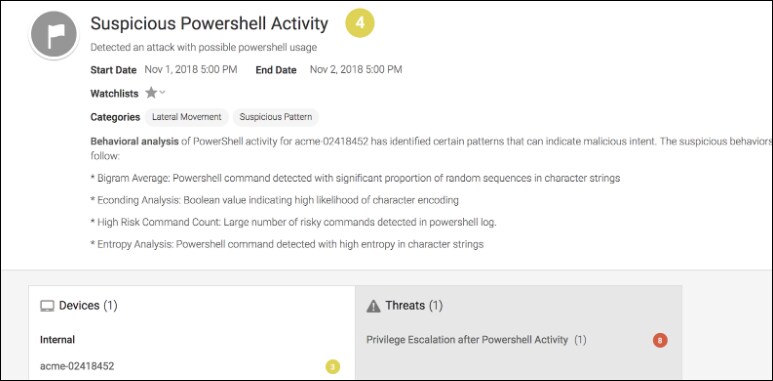
Once you’ve set up logging, you can take advantage of the following Splunk UBA features that look for indicators of PowerShell obfuscation:
- Unusually high number of tick marks (`) in a command: Tick marks are used in PowerShell to escape a character (nra0), but if they are used with other characters, PowerShell ignores the tick mark and executes the script as it is, making it an excellent tactic for obfuscating code.
- Raises an alert on 4104 event ID with the type warning: Microsoft constantly updates a list of risky or possibly malicious commands. When found in a script, these commands trigger a 4104 event ID with a warning.
Past PowerShell activity: Score/Importance is raised if PowerShell is being used for the first time by the user or their peers.
- Entropy: This function captures how random a script is. A high entropy value means that the script is made up of highly irregular sequences of characters; this could be an indication that the script is encoded, which could make it suspicious.
- Bigram Analysis: This function has a frequency table/distribution of all possible bigrams that is built from a set of known “good” PowerShell scripts, and then the function compares this known distribution of bigrams with the character distribution of a given PowerShell script. This comparison is to give us an idea of how different the new script is compared to the known good scripts.
The threat of malicious PowerShell running in your environment is anything but trivial. The good news is that Splunk UBA can help you detect the presence of bad actors that leverage this Windows tool, so you can prevent disaster. It does this by not relying on a single feature, but by using a combination of the above mentioned features.
Ready to learn more? Check out the Splunk User Behavior Analytics product brief!
----------------------------------------------------
Thanks!
Madhupreetha Chandrasekaran
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




