Using Automation to Defend Against the Emotet APT at McGraw-Hill Education
The security team at McGraw-Hill Education, like many security teams, strives to balance the volume of alerts they receive with the available resources they have to investigate them. In recent years, however, the team came to a conclusion increasingly common among their peers—the only way to adequately defend their organization is to employ automation, just like their adversaries have been doing for years.
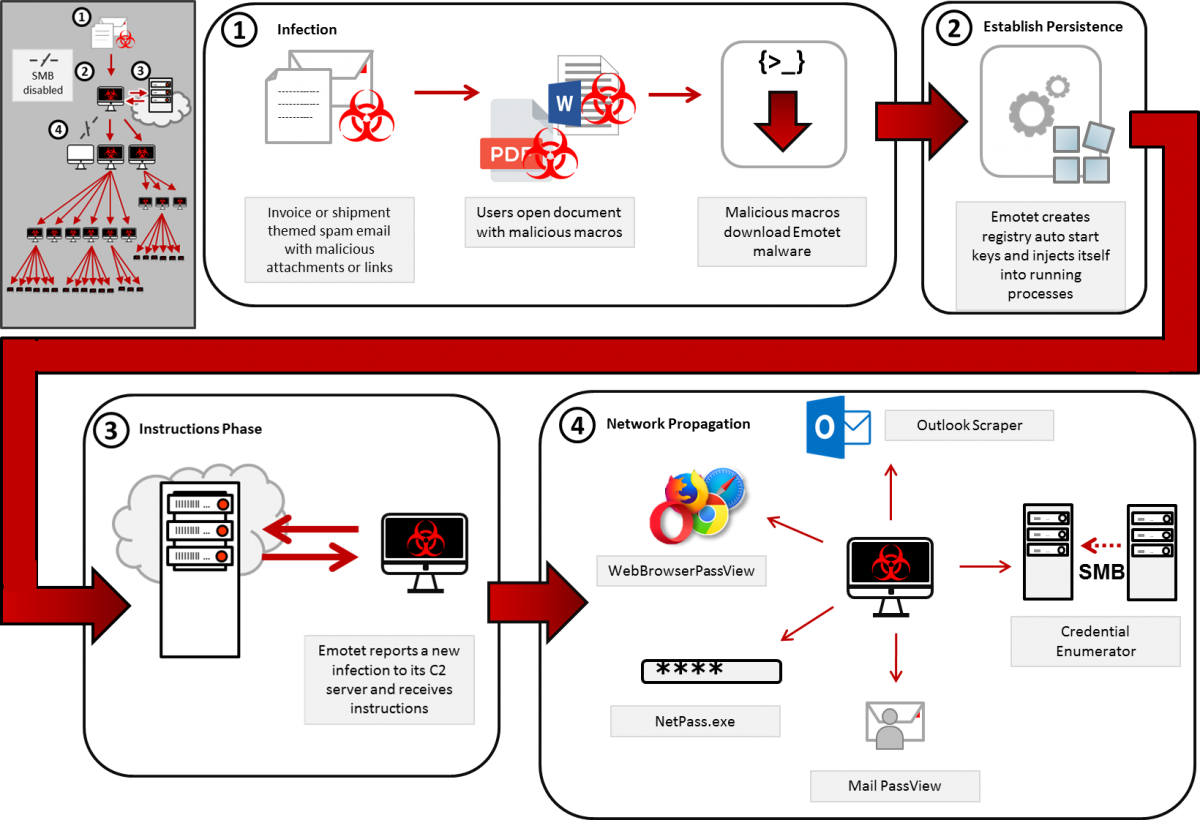
The automation realization was confirmed by the team during a recent bout with the Emotet Advanced Persistent Threat (APT). Emotet is a banking Trojan family that is modular, uses advanced persistence techniques, and propagates laterally using worm-like behavior. It’s commonly distributed through spam campaigns with malicious attachments. The Trojan often downloads, or drops, additional payloads to further the attack campaign.
Emotet Trojan Lifecycle (Source: US-CERT)
Eradicating the malicious emails and their attachments from their environment before users could open them was of utmost importance to the McGraw-Hill team. Yet, during these increasingly common burst attacks (like the Emotet example), the small security team became overwhelmed with shear volume. With 200-300 extra phish a day—on top of their numerous other security tasks—they turned to automation to supercharge their efforts and secure their organization.
The team used a popular email security system and malware analysis system (or sandbox) to detect known and unknown phish with malicious attachments. They connected the two systems—along with their mail server, endpoint detection and response, and even their Customer Relationship Management (CRM) system—together using the Splunk Phantom Security Orchestration, Automation, and Response (SOAR) platform.
The Phantom platform was able to orchestrate and automate complex decision making, containment, and remediation logic for the resource strapped team. In the scenario, Phantom retrieved suspicious emails from a mailbox queue the team setup, then programmatically submitted file attachments to the team’s sandbox for analysis. With the results in hand, the team embedded custom threat scoring logic into Phantom using the playbook they created to deal with phishing threats. If the threat score exceeded the threshold the team defined, then containment and remediation steps were executed next.
Since the team integrated Phantom with their mail server, the first step was to delete any instances of the malicious payload from the server. This prevented any unopened emails from becoming successful attacks. For malicious payloads that did make it to users’ devices, their endpoint detection and response system was the next layer of defense. By searching for indicators of compromise (IOCs) on the endpoints and removing them, damage from the threats was contained.
A particularly interesting aspect of the contain and remediate phase involved the CRM system. Emails sent to particular mailboxes were immediately forwarded into the CRM. Luckily, Phantom was able to help here as well by hunting and finding malicious objects in the CRM and removing them before employees had the chance to open them.
The results were impressive. In one single day when the team observed burst activity, they estimated they were able to scale their operations force using Phantom, augmenting their team with the power of an estimated 7.5 additional analysts.
The team is excited about expanding their Phantom use cases in 2019, with extra focus on Proactive Playbooks that will identify other malicious objects in their environment and remove them before the threat becomes a successful attack.
----------------------------------------------------
Thanks!
Chris Simmons
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




