Splunk BOTS: Gamification in Cybersecurity - What Blue Teaming looks like with over 270 Teams across EMEA
 Hey There,
Hey There,
Whenever your friends say cybersecurity is boring and that it involves sitting in front of large screens all day - tell them about Splunk Boss of the SOC EMEA 2020!
Splunk is the leader in the security operations field empowering the best and brightest security teams, enabling them to ask as many questions as they want on the ever-growing amount of data generated by any application, cloud service or IoT device in our digital world.
Splunk security customers know that there is no such thing as that single correlation search or machine learning algorithm that solves cybersecurity. It’s a constant learning process, it’s a maturing process but it does not have to be boring!
I’m so proud that Splunk is not just another SaaS/software vendor - Splunk invests in the community and people - which is where everything begins and security is no different!
Splunk Boss of the SOC is an Important Part of a Detection and Response Training Plan
“Splunk Boss Of The SOC is our favorite blue team exercise and highlight of the year. We consider BOTS an important part of our detection and response training plan. It’s also just a lot of fun, very competitive and it lets us compare our skill to other similar teams."
- Jarand Nikolai Jansen, Security Engineer, Norwegian Tax Administration
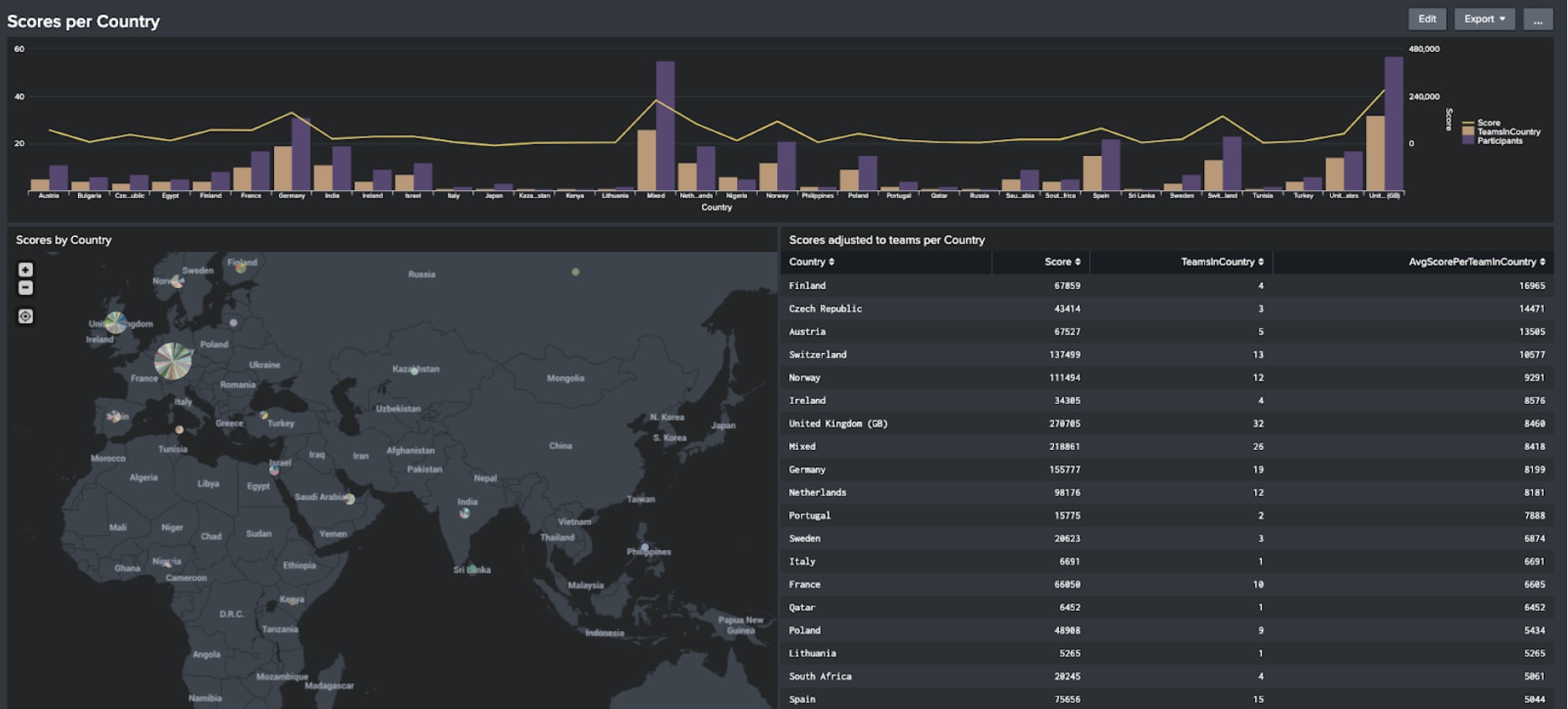
273 Participating Teams, 732 Active Players from over 40 Countries
Recently we executed an EMEA Boss of the SOC. As we had to do it virtually - we were able to go BIG - with over 273 participating teams from over 40 countries.
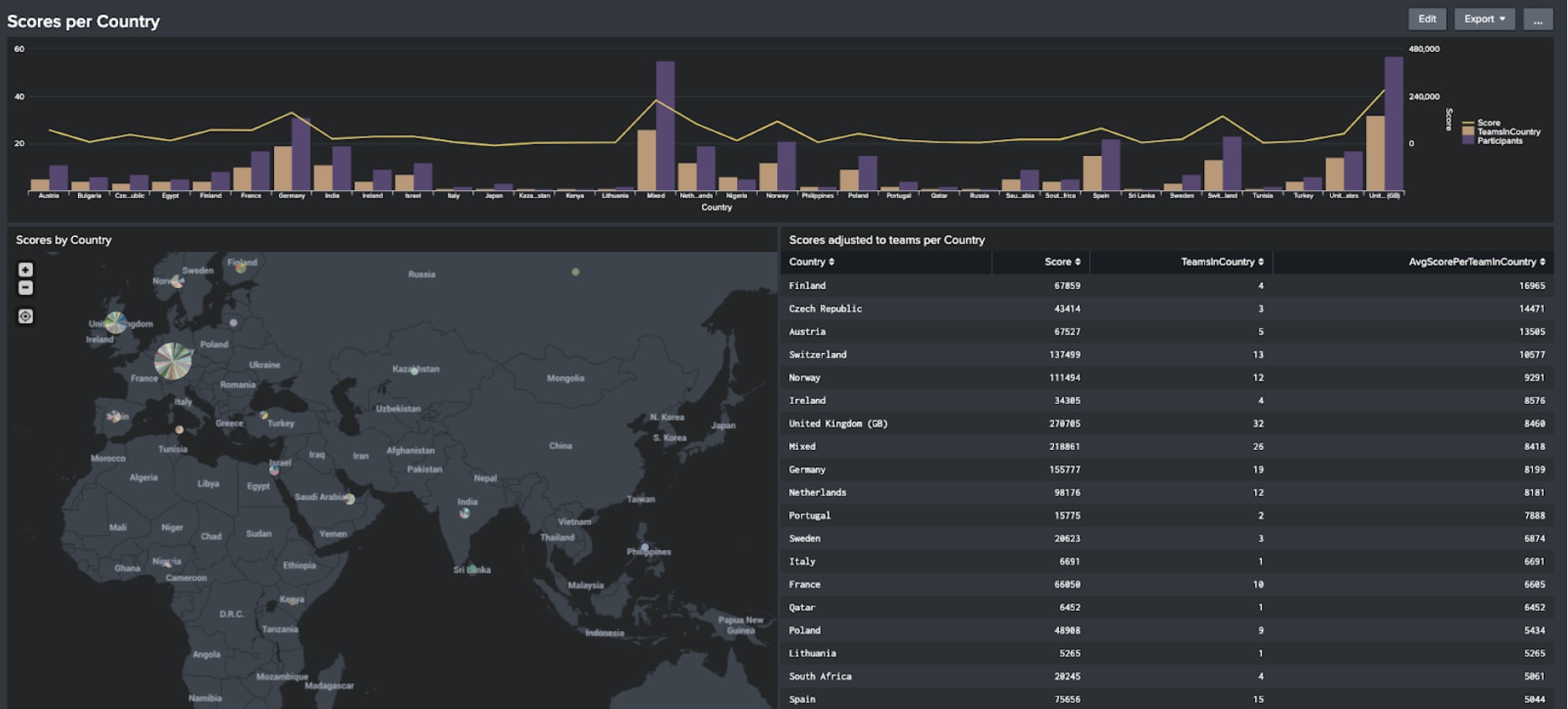
Though it may not be representative research on cybersecurity maturity within SOC’s, we put together some fun stats as key takeaways from the event:
- Finland, with 4 teams participating reached a 3x higher average score than the 15 teams participating from Spain.
- The UK with the highest number of participating security teams seems to invest most into cybersecurity in EMEA.
- Germany made it into the top 10 (#9), but for a leading country within EMEA cyber defense maturity seems low when compared to Finland, Czech, Austria, Switzerland, Norway Ireland and the UK, suggesting there’s still room for improvement.
During the EMEA BOTS, there were 4 scenarios: Toolchain, Red Team activity Detection, defending an APT group and investigating an Industrial Control Systems (ICS) breach.
Just like in the real world, the teams are thrown into different kinds of situations to find answers to over 90 questions in 4 hours. The teams have to investigate and research data spanning from well-known cloud providers through to lesser-known software solutions. The exercise even included an investigation of an ICS breach that could happen at any given time in our digital world.
Here is some insight into how the teams from various countries performed:
- Generally, the APT scenario was scored lowest compared to other scenarios;
- Finland scored highest on the ICS scenario, Austria scored one of the lowest, while having a similar amount of teams playing.
- Teams from Poland scored higher than the Dutch teams on toolchain (with a similar amount of teams);
- Switzerland scored highest on detecting the Red Team activity;
- Austria scored highest in the APT scenario, whereas France scored one of the lowest while having a similar amount of teams playing).
How Have We Done? Where are the full results and score lists of all teams?
- The winning team was “spof” from France.
- Second place goes to “IndexEqualsStar” from the UK.
- Team “Needle” from Switzerland.
It was literally a photo finish between numbers 3, 4 and 5! You can find the full results table here.
Where Can We Play Next and What Will be the Scenarios?
The next BOTS you can play is built into .conf20. You can sign up here - and spoiler alert: Alice Bluebird and Frothly GO REMOTE! New Scenarios, New Data!
I Liked the Music Playlist During the Event - Where Can I Find It?
Our security ninja and EMEA BOTS presenter Filip, put it up on Spotify - here it is! Enjoy the beats!
Matt also put together a blog post on an alternative BOTS playlist and included some serious dad jokes. You can find it here.
Last: Disqualified Teams Through Cheating
Many of you have flagged some cheating activities both during and after the event... Thanks again for pointing them out. While we wouldn’t want to divulge the techniques and tactics used to cheat - we wanted to let you know that we looked carefully into them, investigated them, and disqualified the respective teams. Within BOTS v5 we have put in even more measures to make cheating harder.
See you at the next BOTS! Stay Safe!
Richard and the BOTS EMEA Team - Mikael, Kirsty, Johan, all the coaches and BOTSFather Dave (without you we wouldn’t have come this far).
----------------------------------------------------
Thanks!
Richard Hensen
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




