Playbooks: Automated Investigation & Mitigation for Apple macOS Root Bypass Issue

A critical flaw involving the ability, in certain situations, to exploit the root account on Apple macOS 10.13 (High Sierra) systems was reported on November 28, 2017 (CVE-2017-13872). By default, the root account is disabled in macOS. With vulnerable versions of the OS, attempting to login as root with any password will fail on the first try, but doing so will enable the root account and set the root password to be whatever was attempted, even if the attempt used a blank password. This allows an attacker to bypass administrator authentication without supplying the administrator’s password, enable and set the password for the root account, and then gain elevated privileges on the system. If Screen Sharing or Remote Management are enabled and the user has not set the root password, then this issue allows an attacker to remotely access the machine as root through the usage of freely available software. Apple issued guidance and made a patch available (Apple Security Update 2017-001) for this issue on November 29, 2017. Beyond the initial access as root, it could be possible for a skilled attacker to install a persistence mechanism, then disable the root user to disguise the unauthorized access.
Although Apple moved quickly to mitigate this vulnerability, a scenario like this presents an opportunity to improve upon existing security operations procedures. Toward this goal, we explore how the Phantom Security Automation & Orchestration Platform might help to hunt for and mitigate vulnerabilities like this in the future.
Playbook Methodology
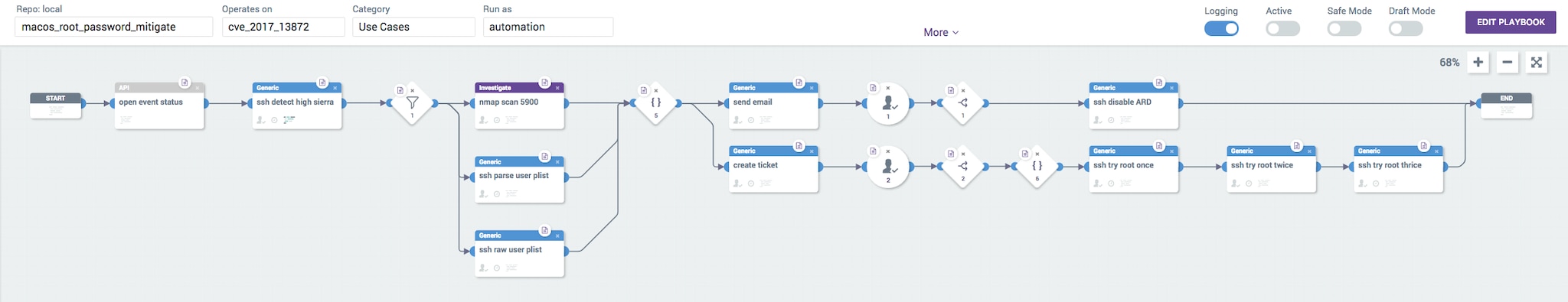
To respond to this vulnerability using the Phantom Platform, we present a methodology that prescribes the use of two playbooks: one to enumerate endpoints and another to mitigate the threat.
Enumerating macOS Endpoints
The first playbook is effectively a small utility playbook that will enumerate macOS High Sierra endpoints that are potentially impacted and populate a Custom List on the Phantom Platform. This playbook is designed to use a Nmap scan against port 5900 to enumerate endpoints. We will store this inventory as a list of IPv4 addresses in a Custom List called “macos_endpoints.” Other methods to populate this list might be a custom scan, a user survey, or an export and import from a pre-existing inventory system or spreadsheet.
Mitigating Affected Endpoints
Once our list of potentially affected endpoints is in place, the mitigation playbook can be started. The initial stages of this playbook will focus on categorizing the impact to each of the inventoried macOS endpoints. The two most important factors to consider are whether Apple Remote Desktop (ARD) services are enabled and whether the root password is currently set. Because of their wide availability, this playbook uses SSH and Nmap to determine both of those critical factors for each endpoint. SSH is also used to determine the timestamp when the root password was last changed.
By gathering this critical contextual information and making it available in Phantom’s Mission Control, an email, or a ticketing system, an analyst is empowered to categorize each endpoint and determine the appropriate response. Because of the potential impact on mission-critical systems, our sample playbook pauses to prompt the analyst before disabling ARD or setting the root password to a random 40-character string. Those mitigations are only a click away, however, and execute at machine speed when confirmed by an analyst.
Phantom has a variety of integrations that could be used to investigate and mitigate the impact of this vulnerability within an enterprise, but for this playbook we chose to use SSH and Nmap because they are widely available and SSH is installed by default on all macOS endpoints (SSH can be enabled under the setting “Remote Login” in System Preferences). Note that SSH is not vulnerable to this issue unless it is reconfigured to allow root access.
Playbooks Step-By-Step
Apps Used
- SSH
- Nmap
- SMTP
- Zendesk
Playbooks Workflow
- Trigger: This playbook is executed manually by a security analyst
- The event status is set to “open”
- SSH is used to detect High Sierra with the utility sw_vers
- Nmap is used to syn-ack scan against TCP port 5900
- SSH is used to run the plutil utility to parse the plist user database and determine whether the root password is set
- SSH is used to read the raw plist user database and parse out the last time the root password was set
- Format is used to aggregate the gathered data and present a unified report
- This report is emailed to the security team
- A service ticket is created with the report
- If the Phantom user responds positively to a prompt, ARD is disabled using the built-in Perl script called “kickstart.” Usage of this script is described here: https://support.apple.com/en-us/HT201710
- If the Phantom user responds positively to a prompt, the root password is set to a 40-character random string generated with urandom
Next Steps
You can download these playbooks from within the Phantom Platform by syncing with the Phantom Community Git repository or gain access to them directly from the Phantom Community site:
Given the ease of usage and level of access granted by this vulnerability, further investigation would be prudent even after mitigating the vulnerable conditions. Particular attention should be paid to endpoints that had ARD enabled and were exposed to public networks...
----------------------------------------------------
Thanks!
Philip Royer
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




