Not All SIEM Solutions Are Created Equal
Many organizations rely on security information event management (SIEM) solutions to protect against cyberthreats ranging from insider threats to advanced threats. But not all SIEM solutions are created equal.
And this is important to know since the adoption of SIEM solutions is only growing. As per Gartner Forecast Analysis: Information Security, Worldwide, 3Q17 Update, the SIEM market spending is expected to be $2.163 billion in 2017 and is predicted to grow at 9.6 percent CAGR.
Additionally, this is highlighted every year when Gartner releases its Magic Quadrant (MQ) for Security Information and Event Management where Splunk was named a leader in the SIEM market for the fifth year in a row.
The fundamental difference comes down to comparing modern, analytics-driven SIEM technology versus legacy systems, while also keeping an eye on open source solutions and new entrants.
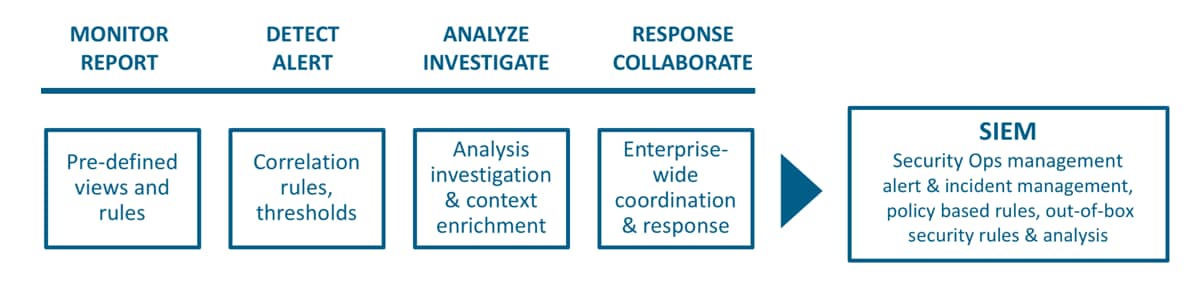
Splunk’s analytics-driven SIEM solution goes beyond the simple information and event management made commonplace by legacy SIEM solutions, to instead tackle real-time security monitoring, advanced threat detection, forensics and incident management.
With an analytics-driven SIEM you can build a stronger security posture and improve cross-department collaboration.
Are You Sure a Legacy SIEM Isn’t Good Enough?
Finding a mechanism to collect, store and analyze security only data is relatively simple. There is no shortage of options for storing data. Collecting all security relevant data and turning all that data into actionable intelligence, however, is a whole other matter.
A legacy SIEM solution can’t keep pace with the rate at which security events need to be investigated. The continued adoption of cloud services expands the threat vectors and enterprises need to monitor user activity, behavior, application access across key cloud and SaaS services, as well as on-premise services, to determine the full scope of potential threats and attacks.
Some of the known issues with legacy SIEM solutions include:
- Limited data ingestion capabilities
- Complex deployment and maintenance
- Inflexible search, correlation and visualization capabilities
- Lack of scalability
- Limited analytics capabilities
A modern, analytics-driven SIEM solution needs to have the following qualities:
- Big data solution (can handle volume, variety, variability and velocity)
- Create a rule (or correlation search) directly from forensic investigation
- Does not require separate relational DB for reporting
- Does not require data normalization at collection time
- Support for hybrid environment (cloud and on-prem)
- Supports data correlation
- Provides out-of-the-box content (reports, correlation searches, dashboards)
- Known to support IT Operations and Application Management use cases
- Ticketing/case management workflow
- Alerting (email, RSS)
- Does not require proprietary hardware devices
- Re-analyze old data with new information (cold case use case)
- Support for statistical analysis on raw data
So What’s the Difference?
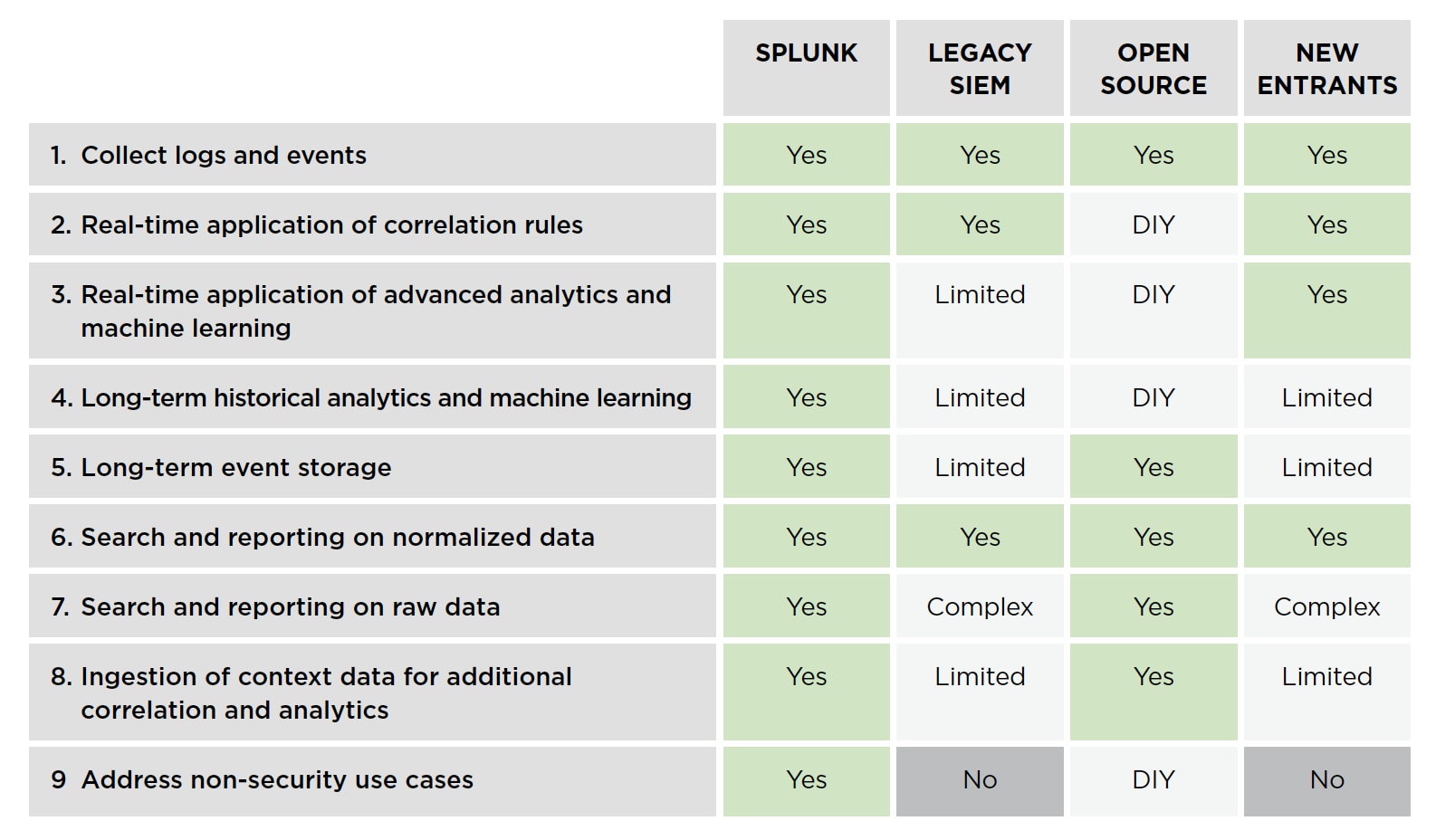
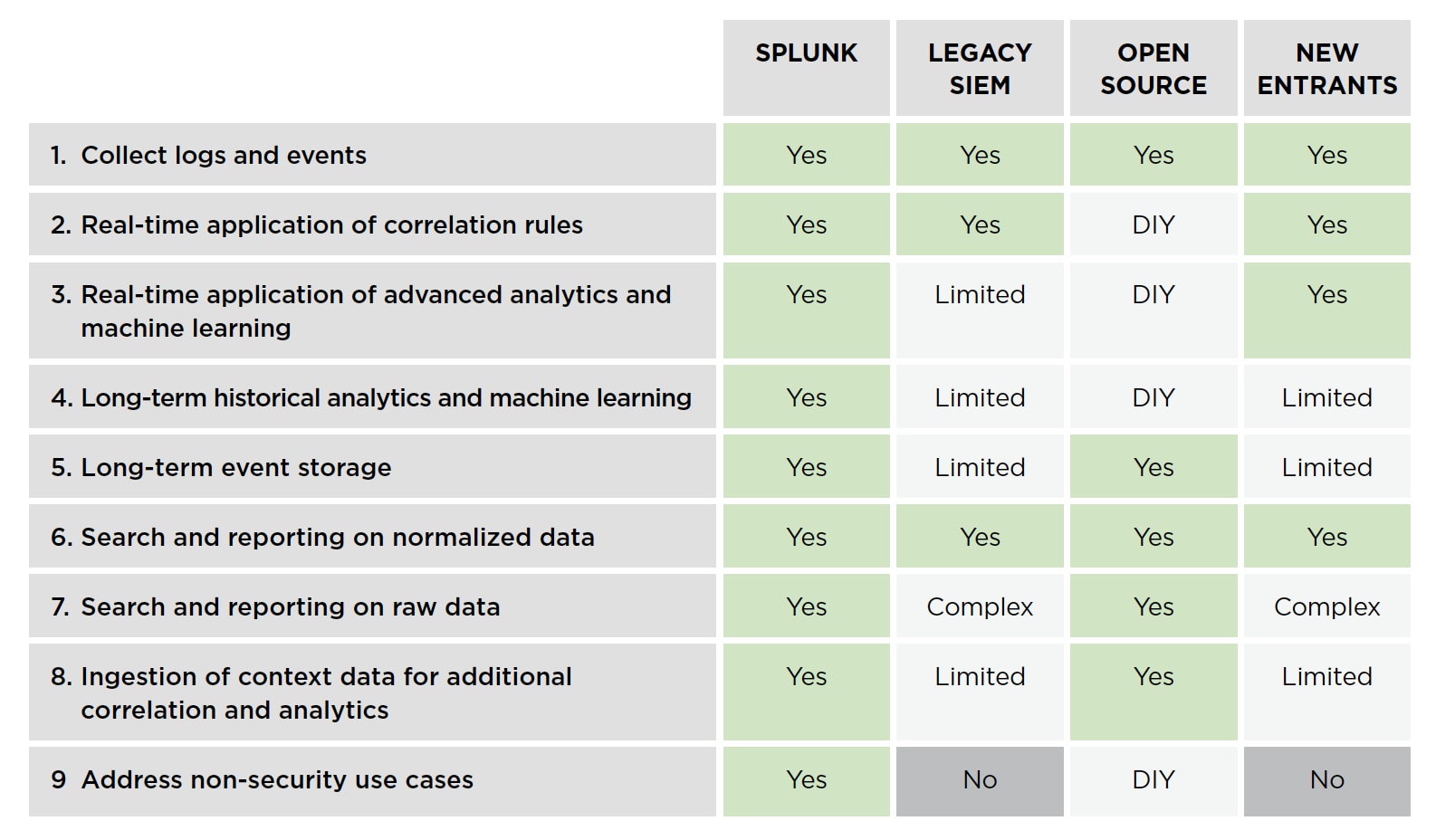
To highlight the differences between a legacy SIEM solution and an analytics-driven SIEM solution, such as Splunk, we put together this handy dandy comparison table to make the difference as clear as day. See below.
The chart also highlights clear as day the limitations of an open source SIEM solution or choosing the infrastructure of one of the new entrants, such as a UBA vendor, to the SIEM space—summed up in a nutshell: Open source solutions often require complex DIY setups to achieve the limited results of a legacy SIEM, let alone the more advanced capabilities of an analytics-driven SIEM solution. New entrants often have limited or complex setups to achieve the necessary capabilities of that come naturally to an analytics-driven SIEM solution.
We based the technology comparisons on an unbiased third party report: Gartner’s nine technical capabilities of a modern SIEM.
Want to learn more about what differentiates Splunk’s analytics-driven SIEM solution and know what your organization needs to consider before investing in a SIEM solution? Download your complimentary copy of our SIEM Buyer’s Guide.
----------------------------------------------------
Thanks!
Girish Bhat
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




