LogMeIn Accelerates Detection Use Case and Reduces Manual Analyst Workflow by Using TruSTAR

A pioneer in remote work technology and a driving force behind today’s work-from-anywhere movement, LogMeIn has become one of the world’s largest SaaS companies with tens of millions of active users, more than 3,500 global employees, over $1.3 billion in annual revenue, and approximately 2 million customers worldwide who use its software as an essential part of their daily lives. They offer a wide range of products and services including Unified Communications & Collaboration, Identity & Access Management, and Customer engagement & support.
pioneer in remote work technology and a driving force behind today’s work-from-anywhere movement, LogMeIn has become one of the world’s largest SaaS companies with tens of millions of active users, more than 3,500 global employees, over $1.3 billion in annual revenue, and approximately 2 million customers worldwide who use its software as an essential part of their daily lives. They offer a wide range of products and services including Unified Communications & Collaboration, Identity & Access Management, and Customer engagement & support.
Read on for more in this Q&A with LogMeIn's Threat & Vulnerability Manager, Mike Rennie.
"TruSTAR allowed me to play out my use cases for free. Seeing the value that even the free version provided, and then seeing what the paid version could do with allowing us to bring in indicators from other sources was a no brainer for our organization.”
– Mike Rennie, Threat & Vulnerability Manager, LogMeIn
How did you manage intelligence before you partnered with TruSTAR?
We didn't have a TIP before TruSTAR, so that's been a whole world of difference. Prior to TruSTAR, we were only using Splunk's built-in threat intel where intel feeds could be fed directly into Splunk. The challenge came when you had multiple intel feeds. If you have 10 feeds coming in, you're not going to be able to manipulate or correlate that data visually. Since we use feeds from multiple sources, including the IT-ISAC, each investigation meant that I needed to separately access intelligence feeds and then attempt to manually correlate and analyze the data, which is very time intensive.
How did TruSTAR solve your challenge?
TruSTAR allowed LogMeIn to combine our threat intel feeds into one centralized, cloud-native platform, addressing the gap in point to point intel. Our internal and external data sources are automatically ingested, normalized, and correlated which helps us prioritize investigations for faster triage. I was able to see all of our data sources in one place, which helped to capitalize our data and save me tens of man hours each week by cutting down on redundant workflows. The ability to manipulate indicators, add notes and tags, and correlate data through our membership with the IT-ISAC makes it incredibly simple for us to manage our tools.
How do you use TruSTAR and what use case are you solving for?
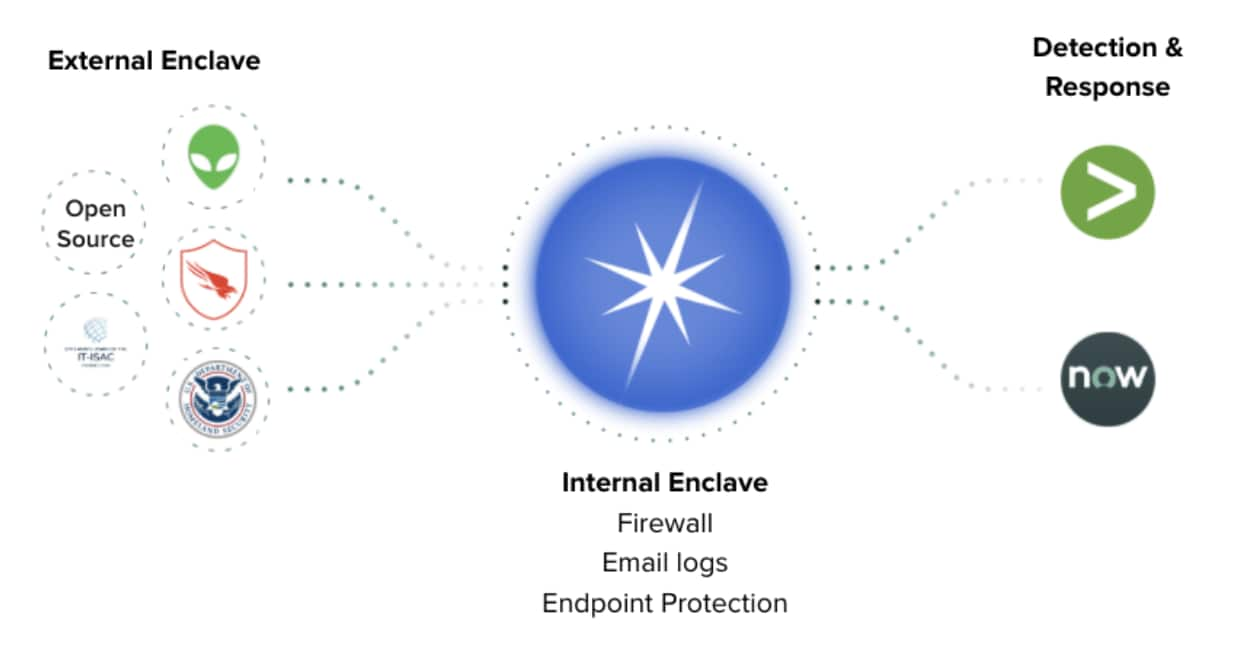
We use TruSTAR and the premium intel and open source feeds that come into TruSTAR through the different integrations to populate Splunk for alerting. We have three premium intel feeds, CrowdStrike, AlienVault, and DHS. We also have our own enclaves, one being for external intelligence and one for internal.
When you say internal and external enclaves, can you explain those?
Our external enclave [secure data repository] gets pushed into Splunk for alerting and is then enriched in ServiceNow. TruSTAR enables us to correlate our intel feeds with one another easily. A ticket gets created in ServiceNow, and our Incident Response team works the ticket to resolution. We also have what we call an internal enclave, which we use for correlation. So, all of our firewall events, email events, endpoint protection events, all things that may or may not have our IP in them, IP addresses or domain names --- we don't necessarily want to alert on those, but we want to correlate those against the other intel in the TruSTAR platform.
Did you look at other TIP-like solutions while you were considering going with TruSTAR?
We did. ThreatStream and ThreatConnect were two of them. We also considered a couple of open source solutions. I had previous experience working with CSIRTs and of course, there's also MISP. From an open source perspective, I did not want the burden of building and maintaining an open source platform so that was out. As far as other commercial solutions, I didn’t want another portal that required analysts to tag and curate. I wanted a cloud-native, API-first platform where I could leverage both internal and external intelligence. TruSTAR’s platform with the Enclave model was the only fit.
How did you come across TruSTAR?
We became a member of the IT-ISAC. At that time, IT-ISAC was partnering with a different solution but then switched to TruSTAR. TruSTAR offered each member a Community Plus version of the platform which allowed me to really test out TruSTAR with my current use cases. That was a blessing to be able to do that. TruSTAR’s enterprise platform offered integrations with premium intel sources, multiple enclaves for multiple use cases, and unlimited users. This was critical since we have 12 people in our CSIRT team that I wanted to give access to. We were also investing in Crowdstrike intel and wanted to operationalize this. Again, another reason why it made sense to use TruSTAR. TruSTAR’s Marketplace has these pre-built integrations so it was really easy to turn on applications or intel sources.
Is there an ROI you are seeing from the platform?
Reducing manual cycles and time-spent for detection and response is the most important metric for me and our team. For example, it just doesn’t make sense for me to do, what I call, the manual way of getting prioritized threat intel into Splunk. It was going to be too noisy. I came from a very mature CSIRT threat intel program and I knew what worked and what didn't work. I knew I had to get an intelligence management solution in order to scale, because I'm only one person and my team only has so many cycles that we can’t afford to spend them on ‘data-wrangling’.
Because it's central to your security operation team, are you sharing this intelligence among other folks in the security organization by leveraging TruSTAR?
99% of what I do in TruSTAR is integrated with the incident response team and security operations. For example, TruSTAR pushes the enriched intel directly to our detection tools, such as Splunk and Crowdstrike. Now, we also have an offensive security team that I work closely with. They are always looking to simulate adversaries and they will occasionally ask “can you tell me what the TTPs are or some IOCs from that particular adversary?” And of course, I can seamlessly provide that through TruSTAR when needed.
Outcomes
- Improved visibility across intelligence sources.
By utilizing a bi-directional data flow and a uniform tagging system, LogMeIn was able to have a wider view of information enrichment opportunities. - Faster investigation time.
By cutting out manual, point to point investigations, LogMeIn now has a central place to coordinate their response efforts. This eliminates redundant analyst workflows across multiple tools. - Scalability.
LogMeIn was able to scale, since the work one person was having to handle was now being automated through the TruSTAR platform.
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




