How Do I Add COVID (or Any) Threat Intelligence From the Internet to Splunk Enterprise Security?
Dear Buttercup,
My dog catching company has been targeted multiple times by ransomware using COVID domains. 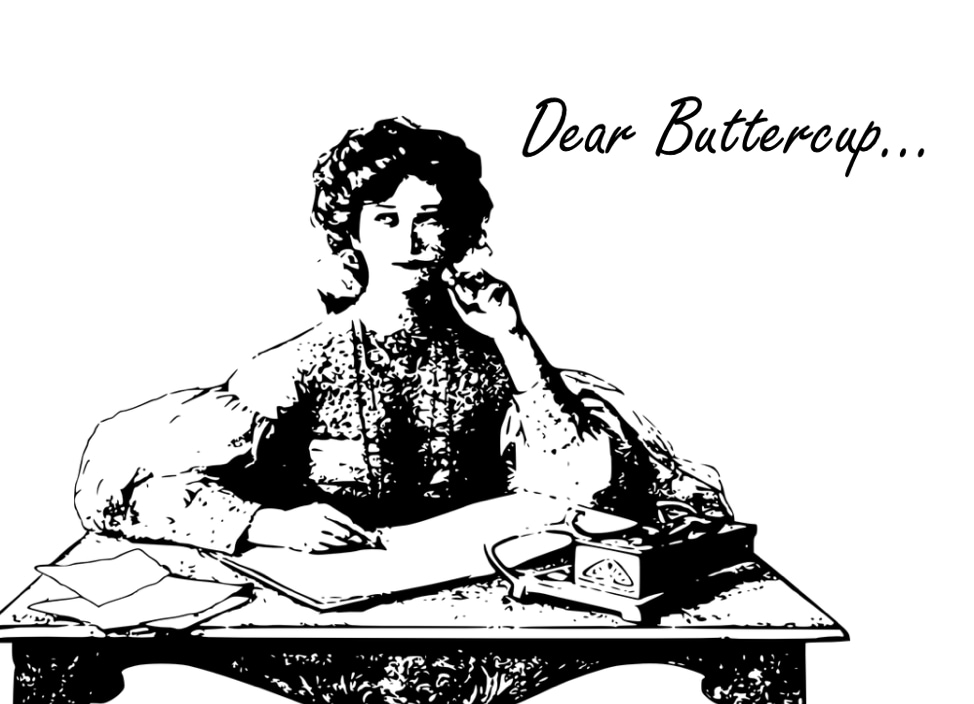 We have Splunk Enterprise Security installed, but we can't afford any of those fancy Threat Intelligence data feeds. I just want to get threat intelligence data into ES without having to have a vendor feed. Can you help me add threat intelligence data to find and detect domains, URLs, and hashes about COVID, without paying any money?
We have Splunk Enterprise Security installed, but we can't afford any of those fancy Threat Intelligence data feeds. I just want to get threat intelligence data into ES without having to have a vendor feed. Can you help me add threat intelligence data to find and detect domains, URLs, and hashes about COVID, without paying any money?
Sincerely,
Old Man Kensey from Athens, Georgia
I'm happy to help you out, Mr. Kensey! Many organizations struggle with buying or affording threat intelligence to plug into Enterprise Security. In fact, the dapperly handsome Ryan Kovar wrote about how to pick the best threat intelligence for your company back in 2016. But if you are facing a budget crisis and/or don’t have time to develop your own threat intelligence data for COVID, we can help you out. The recent crisis has brought the best (and the worst as evidenced by your issues) out of people. Several self-organized groups have stood up MISP servers that are full of vetted and reviewed intelligence that you can gain access to†. The most prominent perhaps is https://cti-league.com/. However, before you go down that route, let's get you some COVID related Indicators of compromise into your SIEM!
Recently one of my good friends told me about a collated GitHub repo that was full of collected threat intelligence data about COVID. This repo was created by Mr. Parth D. Maniar and has thousands of IPs, domains, hashes, and newly created domains that are COVID-19 related.
Some of the information and IOCs in the repo were self-gathered, and other IOCs were sourced from COVID-19 data sources from VirusTotal, DomainTools, Anomali, and other vendors. You could go through a lot of work and create a Technology Add-On to pull those indicators off of the GitHub repo and put them into lookup tables OR you could click four buttons in Enterprise Security. I mean you paid for the product, you might as well use it!
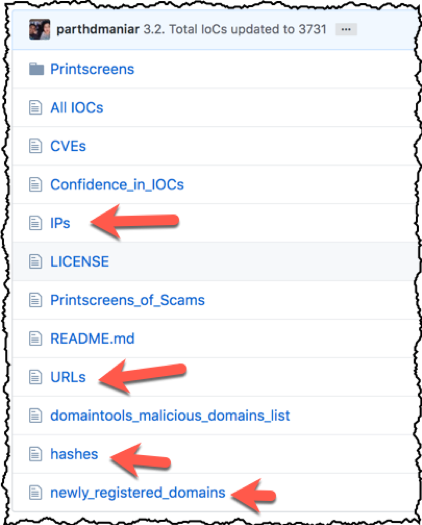
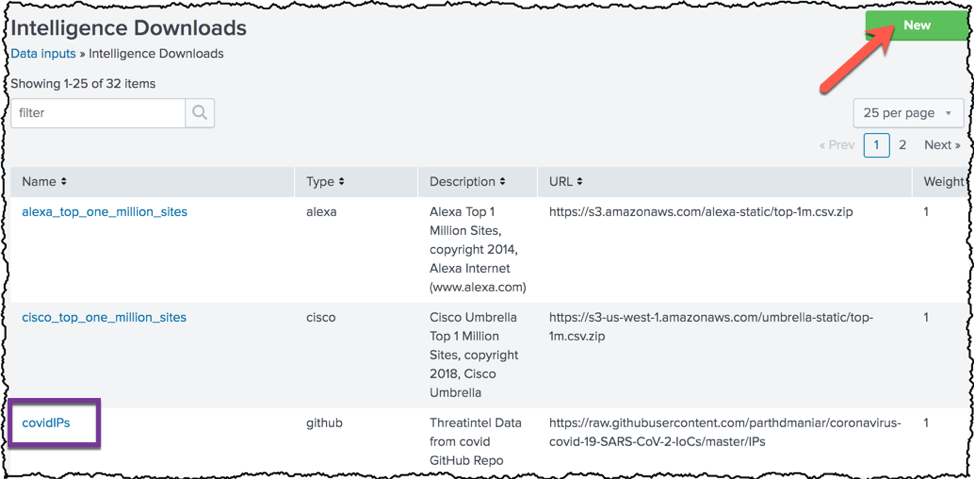
First off, I’ll assume you have the correct privileges to do all of this. If not, find an adult… err Admin. Secondly, I am going to be walking you through how to add a source of threat intelligence off the internet into Enterprise Security. The good news is that how to “Add a URL-Based threat source" is pretty clearly defined in our documentation! Feel free to refer to that if I confuse you, or you would rather read something from a professional. OK, now let's get busy. Click on Configure>Data Enrichment>Intelligence Downloads. Why? Because we are going to paste in some URLs that will be downloaded frequently by Enterprise Security. If you want to just paste in threat intelligence on an ad-hoc basis, check out the Threat Intelligence Uploads menu item, but I digress.
Unless you deleted or disabled them, you will see that Enterprise Security comes pre-loaded with many “Intelligence Downloads” out of the box. The purple box shows where I’ve already added the IPs from the COVID GitHub Repo. Let's add some hashes to the mix, though. Click on the New button on the top right, as indicated by the arrow.
Lots of boxes here in the Intelligence Download Settings window after you click New, but you don't need to make it complicated. This is a pretty simple task. One note, since you are going to add in four of intelligence downloads (IPs, Hashes, Newly Registered Domains, and URLs) just keep your naming conventions consistent:
- Provide a name for your data feed. Choose a name that is concise and doesn’t contain spaces. I’d suggest covidHashes
- Click the box “Is Threat Intelligence” because this is Threat Intelligence
- Don't click the box "Sinkhole." Or do if you want to delete the file later on. I don't really care. I prefer to keep the data so I know where things came from, but if you are worried about space, go ahead and sinkhole it
- You’re gonna need to add a "Type." Since it is coming from GitHub, I put in GitHub
- Add a relevant description, in this case, I point out it is ThreatIntel data from COVID GitHub Repo
- Add the URL. We are going to use the “RAW” link from the GitHub repo of https://raw.githubusercontent.com/parthdmaniar/coronavirus-covid-19-SARS-CoV-2-IoCs/master/hashes. This JUST provides the ascii and no webpage formatting
- I put in a weight of "1" because some of these IOCs are not vetted. There might be some false positives. I want to SEE alerts, but I don't want people scrambling
- For Interval, I put in "3600" (1 hour worth of seconds). The author of the GitHub repo doesn't have a specific time where he updates, so I'm just gonna look every hour
- The final field in the form I edit is “Fields” and it looks like this “file_hash:$1,description:covidThreatIntel”
THIS IS IMPORTANT. IF YOU DON’T DO THIS THEN THINGS WON’T WORK LATER ON. The beautiful thing about using a CIM field is I don't have to define if it is an MD5, SHA1, SHA256, or SHA512 cryptographic hash. It will apply the threat intel data against ALL fields that are CIM compliant with the "file_hash” field then I add the “description:covidThreatIntel” to help clarify later on when you are looking at the indicator.
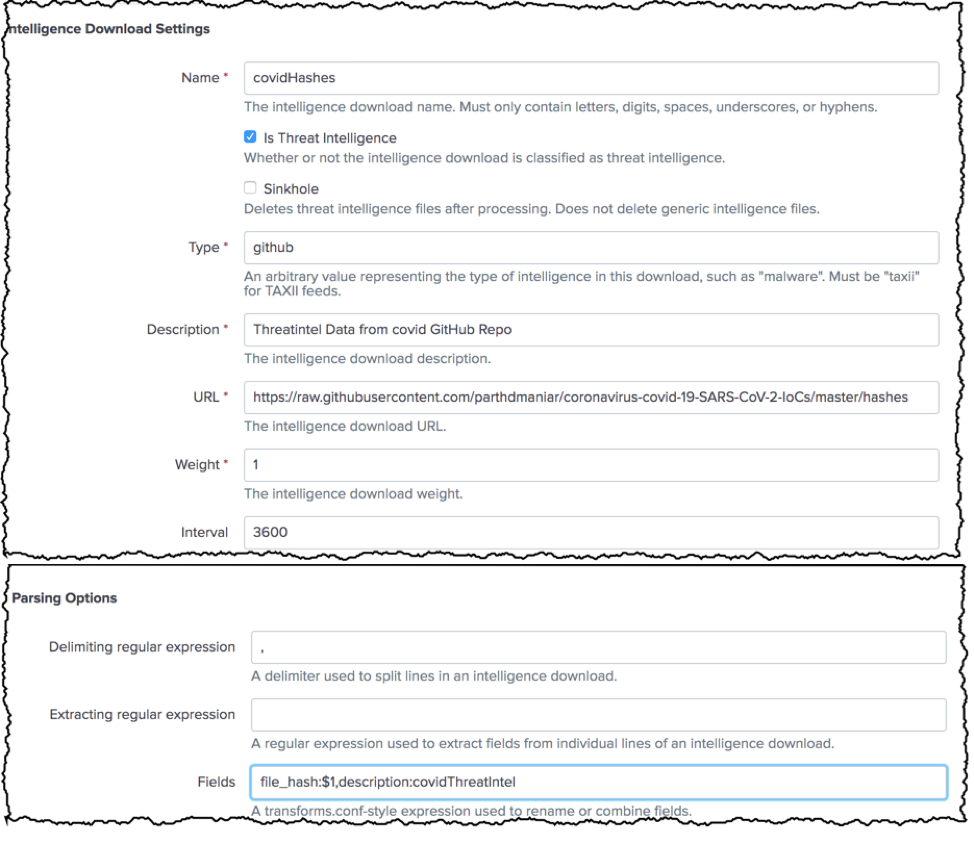
Notice I had to bridge the screenshot to show everything. Loooong form, but here is everything we covered above.
Once I’ve added all that information, I click “Save”. Now, if you found that confusing, I implore you to check the documentation. It is precisely what I followed and had no problems.
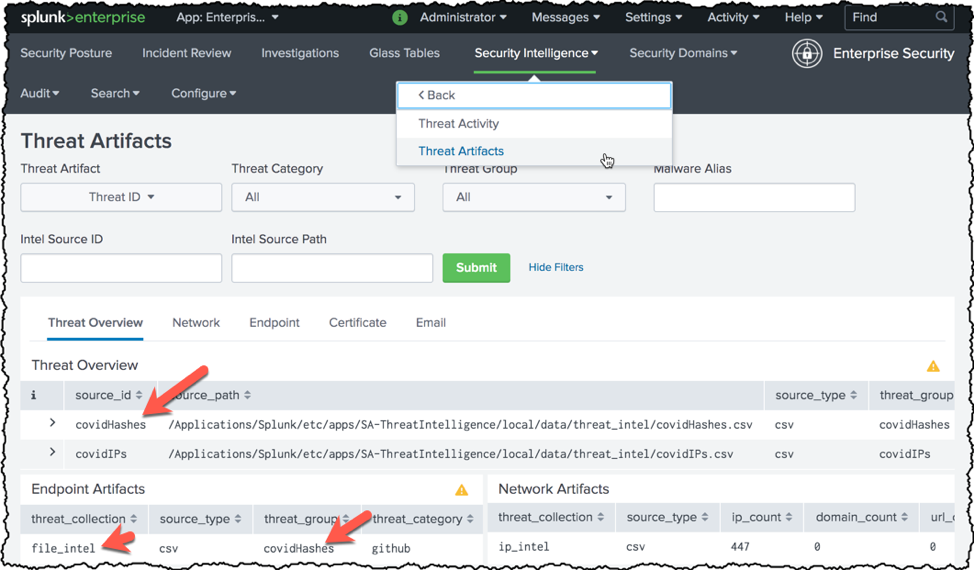
Now that we added our feed, let's make sure Enterprise Security is downloading and ingesting the data for use! In your Enterprise Security Menu, click Security Intelligence>Threat Intelligence>Threat Artifacts. This will show you what Threat Intelligence is currently in Enterprise Security. You can see below that we have covidHashes in our "Threat Overview" and also in our "Endpoint Artifacts." This is because we identified the IOCs in this threat intel feed as "file_hashes." You can see that the covidIPs is found in the "Network Artifacts," which makes sense as we identified that feed as being IOCs that mapped to the "ip” field
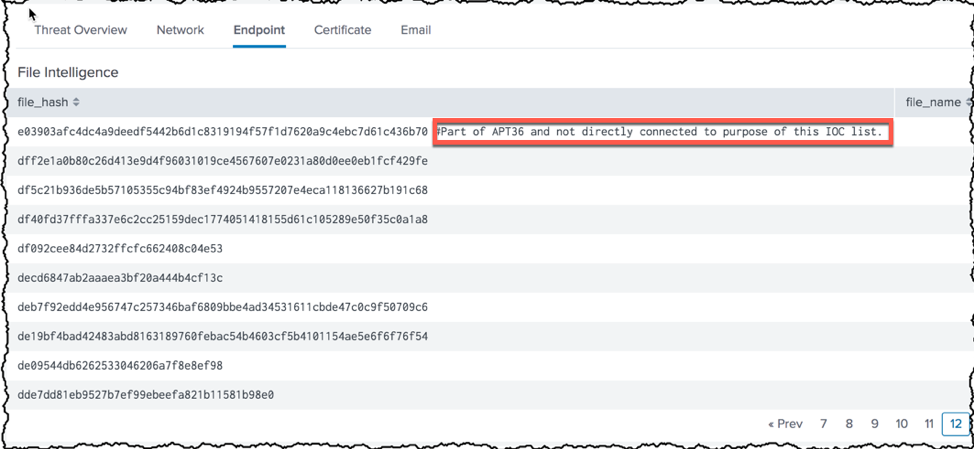
If I click on the "Endpoint" tab above, I can see the actual hashes that have been brought into Enterprise Security from the GitHub repo.
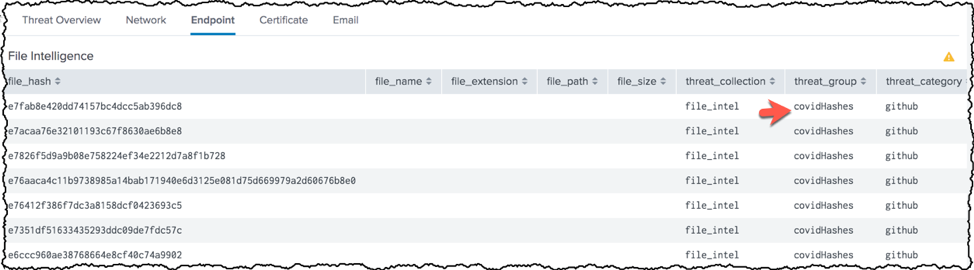
This is a great time to point out that your data is only ever as good as what comes into Enterprise Security. You can see in the red box below that the creator of this threat intelligence put a note by a hash. Both the hash and the comment are now ingested into Enterprise Security and located in the file_hash field. Since the field file_hash contains both the hash and comment, it will not actually match any hashes. Since this file is downloaded every hour, even if you delete it, the value will re-appear. You have two primary ways of dealing with issues like this. Either extract the IOC and manually load it into your threat intel feed via the local threat intel files OR doing a push (and a request to the author) to the GitHub repo to keep comments out of the repo. Or you can do what I did, which is leave it… because I am just giving you examples ☺.
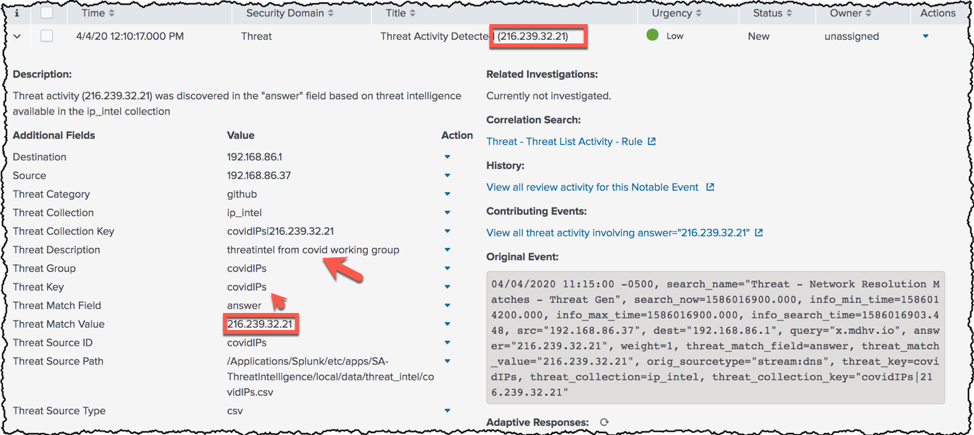
Now I don't have any examples of malicious COVID files hitting my network. Still, I did do a quick wget to a nasty IP address to see if my previous threat intelligence data would do anything. Thankfully (and after a long teaching moment with my beloved colleague John Stoner) I had a notable event generated from my COVID threat intelligence list derived from a GitHub repo.
Well, Old Man Kensey from Athens, I hope this answered your question, and you haven't lost your religion as you waited for me to meander through the topic. I'm not gonna lie, this one really put me in the spotlight. Hopefully, I have said enough and haven’t said too much about the subject, and you are perfectly prepared to succeed at adding timely threat intelligence from internet sources into your Enterprise Security!
† Since this blog was originally written the Cyber Threat Coalition has published much of its intelligence on GitHub repos. You can use the same methods above to add those files to Splunk ES! Check it out here: https://github.com/COVID-19-CTI-LEAGUE/PUBLIC_RELEASE.
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




