Find Malicious Insiders Before You Become a Headline

 The media is filled with reports of Russia’s possible influence over the U.S. presidential elections. While American security agencies are investigating the Kremlin’s possible involvement in a hack of the Democratic National Committee, a U.S. Intelligence Service unclassified report suggests the Russians motive, at least in part, may have been retaliation for the U.S. working with a malicious insider to leak news of a Soviet Olympic athlete doping scandal.
The media is filled with reports of Russia’s possible influence over the U.S. presidential elections. While American security agencies are investigating the Kremlin’s possible involvement in a hack of the Democratic National Committee, a U.S. Intelligence Service unclassified report suggests the Russians motive, at least in part, may have been retaliation for the U.S. working with a malicious insider to leak news of a Soviet Olympic athlete doping scandal.
Regardless of whether the report is true, it reveals a growing concern over insider threats for foreign governments everywhere. Countries such as Canada are heavily investing to protect its citizens against insider and foreign attacks, while the U.S. Department of Defense Inspector General found in a recent audit that the U.S. was had several cybersecurity vulnerabilities, including insider threats.

So how do governments and organizations alike reduce the risk of a malicious insider? One way is to employ a security information and even management (SIEM) solution that has the ability to monitor user activity.
User activity monitoring that includes user and data context is needed to discover the origins of a security breach or to find out if a privileged user misused his or her credentials, as is alleged to be the source of the Russian doping scandal leak.
Privileged user monitoring is also a common requirement for compliance reporting. This capability includes the ability to correlate and analyze access and authentication data, establish user context, and to alert and report on policy infringements and suspicious behavior, for example brute forcing of user accounts or changes in rights and roles. Functions include integration with IAM infrastructure to obtain user context, as well as the inclusion of user context in correlation, analytics and reporting.
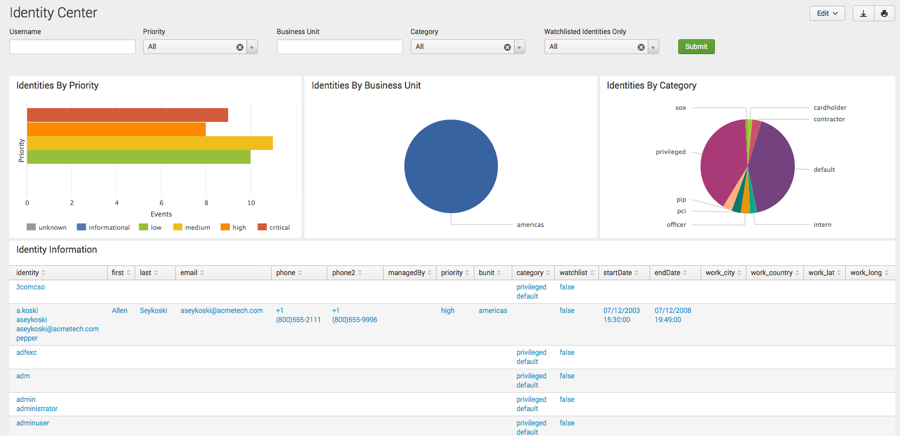
An analytics-driven SIEM solution gives both organizations and governments alike the power to monitor users with identity-centric and real-time views of what users are doing on an enterprise. A modern SIEM also provides reporting capabilities leveraging a variety of identity mechanisms including AD, LDAP compliant directories and IAM solutions, such as Okta. Today’s SIEM solution also provides identity-oriented monitoring for enterprise SaaS applications and native user and entity behavior modeling via a compatible user and entity behavior analytics solution.
According to Gartner, organizations are failing at early breach detection, with fewer than 20 percent of breaches detected internally.* Most companies learn about breaches within their organization from external sources. Traditional defense-in-depth approaches and deployments of preventative controls are no longer effective as criminals have found ways of circumventing these controls. Furthermore, the time to detect a compromise takes days, or even months.
 Want to learn more? Join a webinar with Gartner research analyst Kelly Kavanagh as he provides best practices on how to detect targeted attacks leveraging the SIEM as a focal point — a nerve center – for security monitoring and threat detection.
Want to learn more? Join a webinar with Gartner research analyst Kelly Kavanagh as he provides best practices on how to detect targeted attacks leveraging the SIEM as a focal point — a nerve center – for security monitoring and threat detection.
*Gartner; Use SIEM for Targeted Attack Detection; by Kelly Kavanagh, Toby Bussa and Oliver Rochford; June 30, 2016.
Thanks,
Girish Bhat
Related:
Three Ways Machine Data Makes Your SIEM Better at Security
Stop Security Threats With Real-Time Data Monitoring
Make Security Incidents Less Scary By Organizing Your Response
Gartner named Splunk a leader for the fourth consecutive year.
----------------------------------------------------
Thanks!
Girish Bhat
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




