Dear Buttercup, To SIEM or not to SIEM; that is the Question
 Dear Buttercup,
Dear Buttercup,
I have so many questions about CIM, SIM, SIEMs. Is Splunk a SIEM? Do I need one? I have Splunk Core and Splunk Security Essentials… is that enough? What does a SIEM give me that Splunk Core doesn’t?
Your Devoted User,
Bugged Bret from Binghamton, NY
Dear Bugged Bret,
Oh dear. I can see you have worked yourself into quite the bother. There are quite a few questions in that brief paragraph, and some are difficult to answer without seeing your environment and workflow, but I will do the best I can. Let's start by explaining what a SIEM is, what Splunk’s SIEM product (Enterprise Security) provides, and what you can use it for in your organization.
First off, SIEM stands for “Security Information and Event Management. Gartner defines a SIEM as a technology that “supports threat detection and security incident response through the real-time collection and historical analysis of security events from a wide variety of event and contextual data sources." Well. That sure sounds like Splunk doesn't it? Gartner goes on to say "[SIEMs] also supports compliance reporting and incident investigation through analysis of historical data from these sources. The core capabilities of SIEM technology are a broad scope of event collection and the ability to correlate and analyze events across disparate sources." This is where people get confused about Splunk and SIEMs. Out of the box, Splunk is just a search bar for logs. You have to build out the SIEM capability. Lucky for you, we did. We call it "Enterprise Security" or ES.
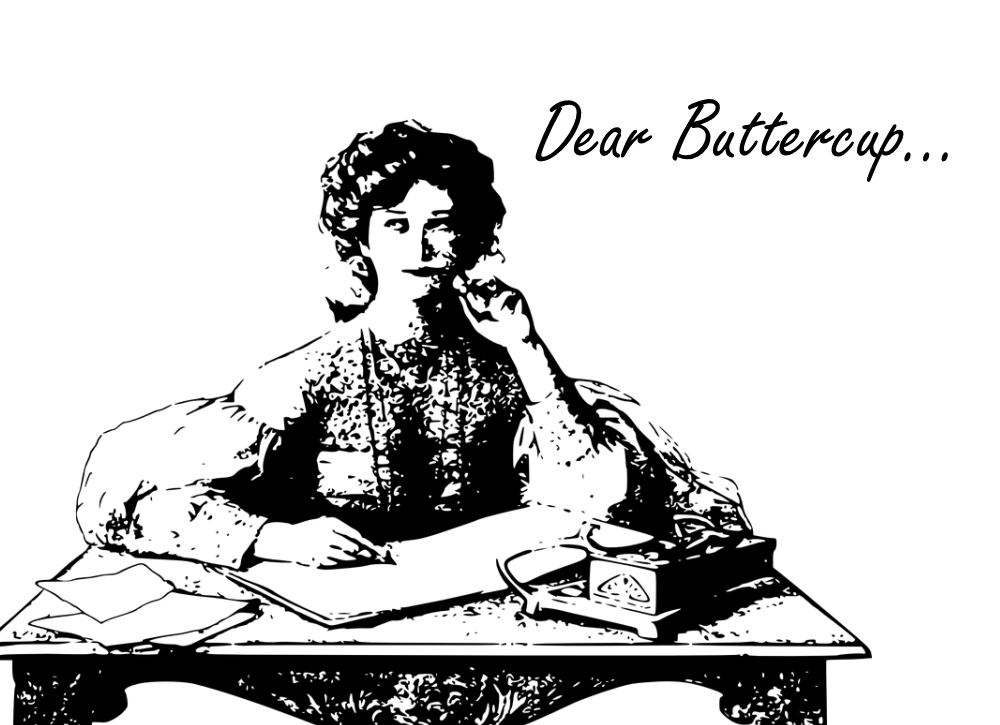
Enterprise Security is basically core Splunk with lots of fancy JavaScript and 20k hours of development time from top tier Splunk developers :-). So to answer your first question, "Is Splunk a SIEM?": Yes. Splunk is many things, and we call our SIEM offering with Splunk "Enterprise Security."
Your second question is around using Splunk Core and Splunk Security Essentials as a SIEM. You certainly could whack together a solution with Splunk core that would approximate many of the features of ES, but inevitably people have issues with upkeep, maintenance, extensibility, and function. Frankly, it is often easier to buy instead of build, and this is one of those cases. Splunk’s SIEM is more than just a collection of static searches like Security Essentials. It has an out-of-the-box notable event framework comes with searches that create “notable events” that your analysists can work on via a shared incident review page.
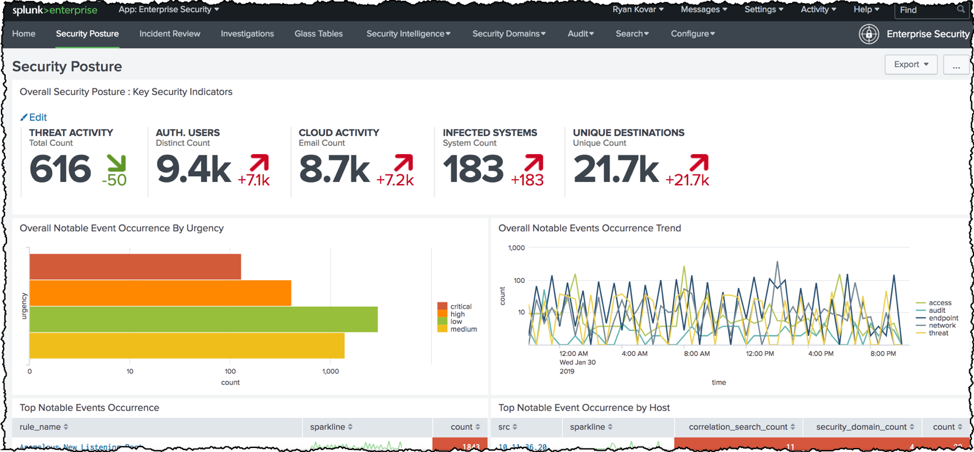
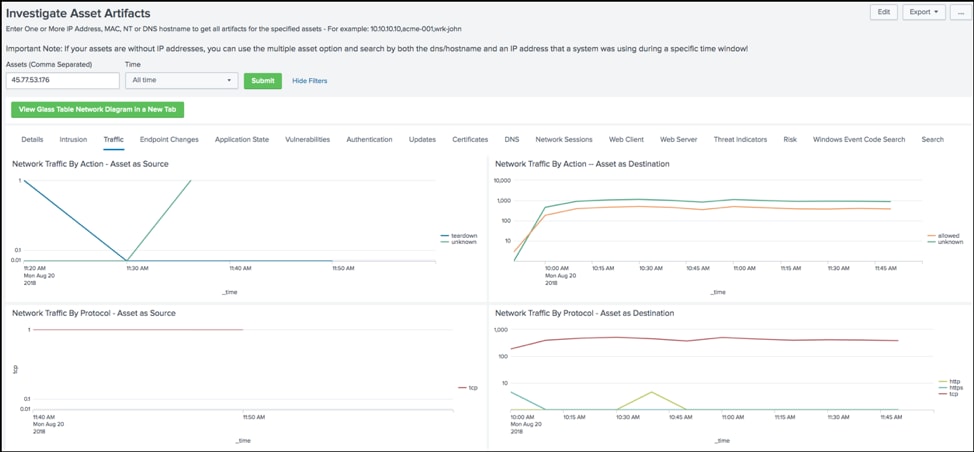
Moreover, not only does Splunk ES come with some out of the box searches, but it also has the concept of "Enterprise Security Content Updates" (ESCU) that come from Splunk's very own security research team. These are analytic stories comprised of informative prose, correlation searches, and mapping to models like ATT&CK and Cyber Kill Chain to not only detect badness but also better inform you while providing your team with the context of the threats! Not only that, these analytic stories are released on a bi-weekly-ish schedule. Once these searches run, you can use Enterprise Security’s tight integration with accelerated data models to quickly search months of data. ES has tools like Investigator Workbench and SA-Investigator that will allow your team to pivot from context filled events to groundtruth, raw data.
Finally, ES also has a flexible threat intelligence framework that allows you to integrate with threat intelligence feeds and sharing communities with a couple of strokes on your keyboard. From MISP to STIX you can feed it all into ES.
So is Splunk a SIEM? You bet your best tack and saddle it is. This reply doesn't even go into Splunk's ability to "action" the events in your data via Enterprise Security using adaptive response or Phantom or how you can build cases and collect evidence. Hopefully, this answered your question Bugged Bret from Binghamton.
Sincerely yours,
Buttercup
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




