Analytics Stories for Splunk Enterprise Security, Part 1: Organizing My Security Use Cases
Dear Buttercup,
I have been using Splunk Enterprise Security for about a year and I have built a number of correlation searches. So far, so good. My concern now is that as I continue to broaden the use cases I am monitoring for, it is becoming challenging to organize my correlation searches and separate out my compliance, ransomware, advanced threat content from one another. Do you have anything to help me solve this issue?
Sincerely,
Sterling from State College
Sterling,
It’s great to hear from you, thank you for your note! I’m pleased to hear that you are making good progress with Enterprise Security. As you are well aware, due to the responsibilities of the SOC, the SIEM can have a large repository of correlation searches and organizing them and sharing them can be challenging. To help you with this, I want to highlight a capability in Enterprise Security called Analytic Stories. When we’re done here, there will be golden lights displaying your name!
As we look through the sands of time, the concept of an analytic story was first introduced with Enterprise Security Content Updates (ESCU). At that point, the Splunk Security Research team had released the framework within their ESCU app and with it, the ability to take searches and bundle them together as analytic stories around specific topics, like AWS Cryptomining or Windows Log Manipulation. These continue to be updated and released to Splunkbase on a regular basis. If you have not yet taken a look at the content updates for ES, take a moment and do that, I'll wait!
In Enterprise Security 5.2, the Use Case Library functionality was introduced for users to define their own use cases and organize their content within ES as well as provide a means to export this content. With that background, let’s look at a Use Case and what one might find within.
It is important to keep in mind that the Use Case Library is an abstraction layer that helps group your searches. The easiest way to access the page is to navigate to Configure - All Configurations and select Use Case Library from the list.
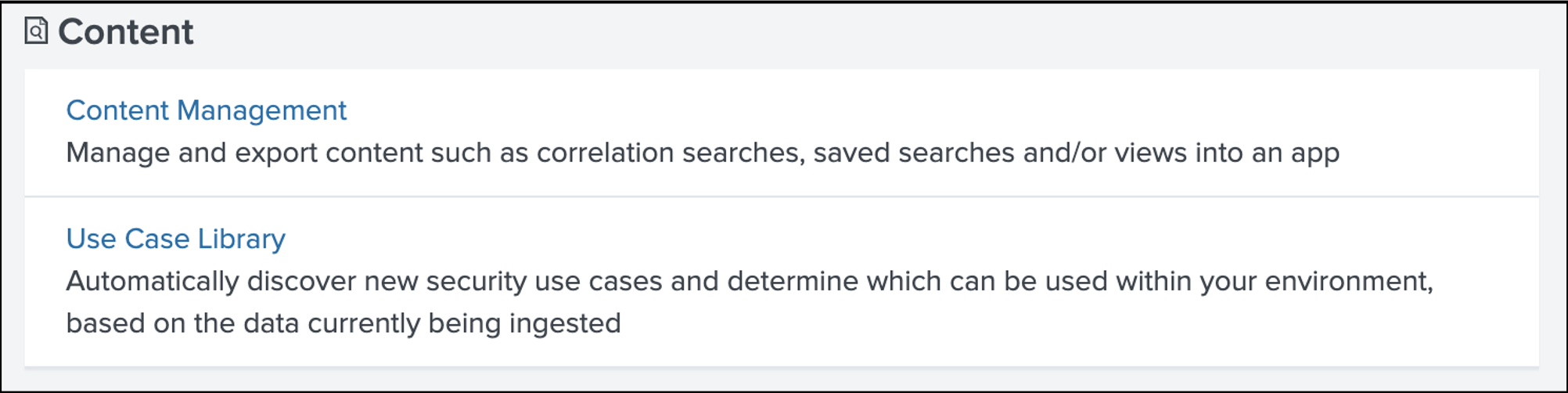 When you initially open the library, you will likely notice three use cases already pre-populated. These use cases utilize default correlation searches that are installed during every ES install and are broken out by authentication, endpoint, and network. If you have many more, you likely have also installed the ESCU app because all of the content in that app uses the analytic story framework and will populate this view as well.
When you initially open the library, you will likely notice three use cases already pre-populated. These use cases utilize default correlation searches that are installed during every ES install and are broken out by authentication, endpoint, and network. If you have many more, you likely have also installed the ESCU app because all of the content in that app uses the analytic story framework and will populate this view as well.
 Across the top of the page, there are a number of ways to filter down this data, whether it is based on frameworks, data models, a class of use case or even if the use case is being utilized currently. There is a flag to indicate the use of the specific analytic stories as well and both the flag and the drop-down are based upon if a search in a use case is enabled.
Across the top of the page, there are a number of ways to filter down this data, whether it is based on frameworks, data models, a class of use case or even if the use case is being utilized currently. There is a flag to indicate the use of the specific analytic stories as well and both the flag and the drop-down are based upon if a search in a use case is enabled.
For our example, we have a new use case that was just created in support of a new workshop we introduced in February 2020 around building correlation searches in Enterprise Security. In support of this workshop and to highlight use case functionality, we built an app with the correlation searches from the workshop into an analytic story. This app can be downloaded from Splunkbase. By clicking on the > next to the Building Correlation Searches in Splunk Workshop Content, we can expand the use case and see that we have eight detection searches as well as some additional metadata pertaining to what is required for these searches to operate.
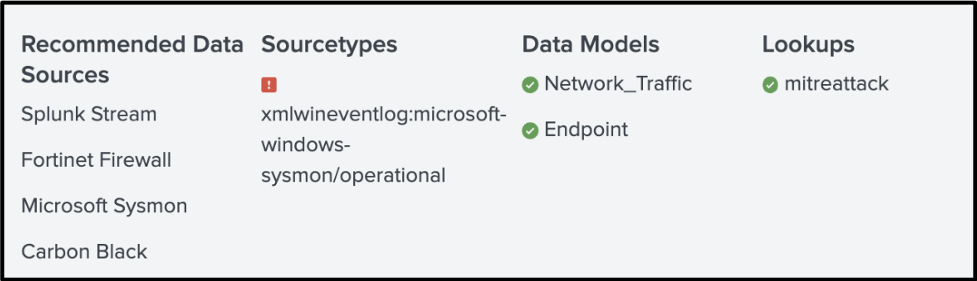
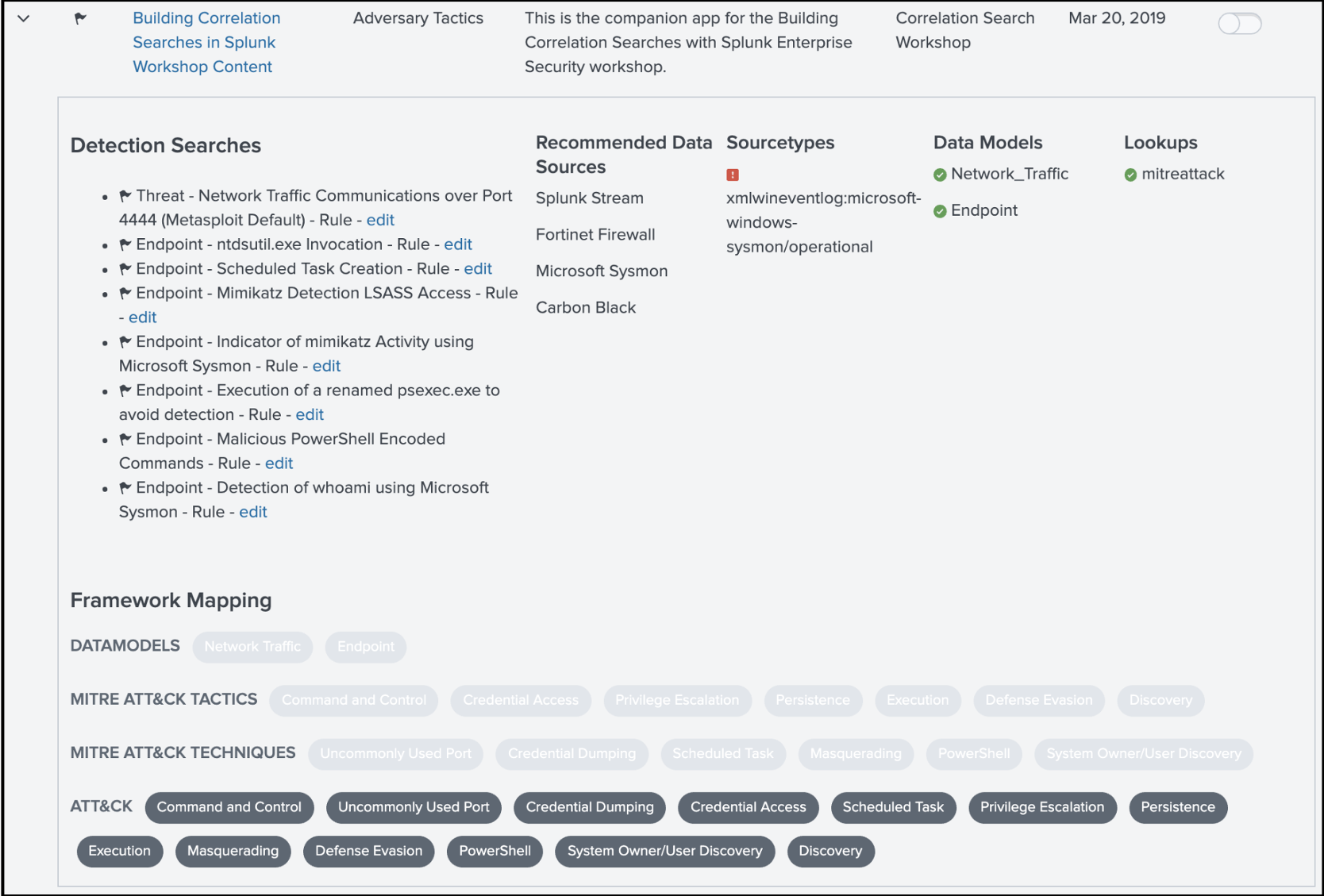 While the author of the use cases recommended a set of data sources, that isn’t to say these are the only data sources that will work with these searches. This is very important as we look at detection searches that leverage data models. In these cases, we can leverage those searches if we have events in the data models, in this case, Network_Traffic and Endpoint. One other note, the reason that there is a red mark next to the one sourcetype listed is that the system has not seen that sourcetype in the past 24 hours. You can hover over those visual cues and get information around your data set before you even run your search!
While the author of the use cases recommended a set of data sources, that isn’t to say these are the only data sources that will work with these searches. This is very important as we look at detection searches that leverage data models. In these cases, we can leverage those searches if we have events in the data models, in this case, Network_Traffic and Endpoint. One other note, the reason that there is a red mark next to the one sourcetype listed is that the system has not seen that sourcetype in the past 24 hours. You can hover over those visual cues and get information around your data set before you even run your search!
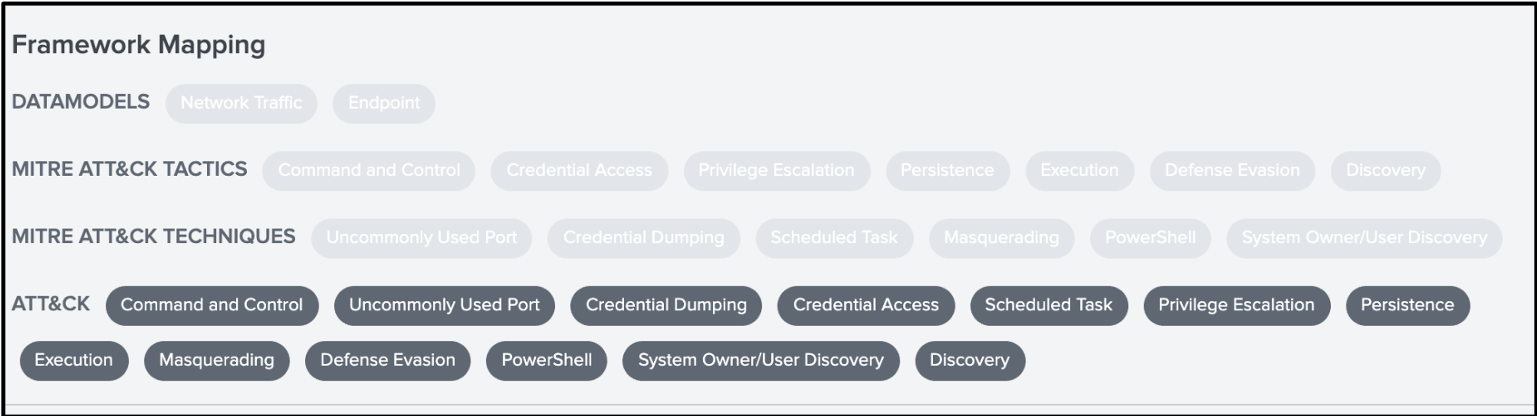
 At the bottom of the use case, we can also see that there are framework mappings listed. It is important to note that there are a set of pre-defined frameworks, including MITRE ATT&CK, CIS 20, NIST, and Kill Chain that will color-code stories and searches to the framework. You have the ability to add additional frameworks to this layout. In the example below, you can see that this could be anything, including datamodels or even further abstraction of MITRE ATT&CK into separate groups of tactics and techniques, but it is important to note that because they are not one of the aforementioned frameworks, they will show in a much lighter grey since they are not predefined. Not a big deal though, you can still filter by any of these frameworks!
At the bottom of the use case, we can also see that there are framework mappings listed. It is important to note that there are a set of pre-defined frameworks, including MITRE ATT&CK, CIS 20, NIST, and Kill Chain that will color-code stories and searches to the framework. You have the ability to add additional frameworks to this layout. In the example below, you can see that this could be anything, including datamodels or even further abstraction of MITRE ATT&CK into separate groups of tactics and techniques, but it is important to note that because they are not one of the aforementioned frameworks, they will show in a much lighter grey since they are not predefined. Not a big deal though, you can still filter by any of these frameworks!
 If we click on the use case itself, we are taken to the Analytic Story Details. This provides a description of the analytic story itself, any narrative that can be shared with the consumer of the use case as well as any relevant links. Scrolling through the use case, we can see all of the searches that are associated with this use case. In our case, we just have detection searches, but there are three additional classification of searches. They are investigative, contextual, and support.
If we click on the use case itself, we are taken to the Analytic Story Details. This provides a description of the analytic story itself, any narrative that can be shared with the consumer of the use case as well as any relevant links. Scrolling through the use case, we can see all of the searches that are associated with this use case. In our case, we just have detection searches, but there are three additional classification of searches. They are investigative, contextual, and support.
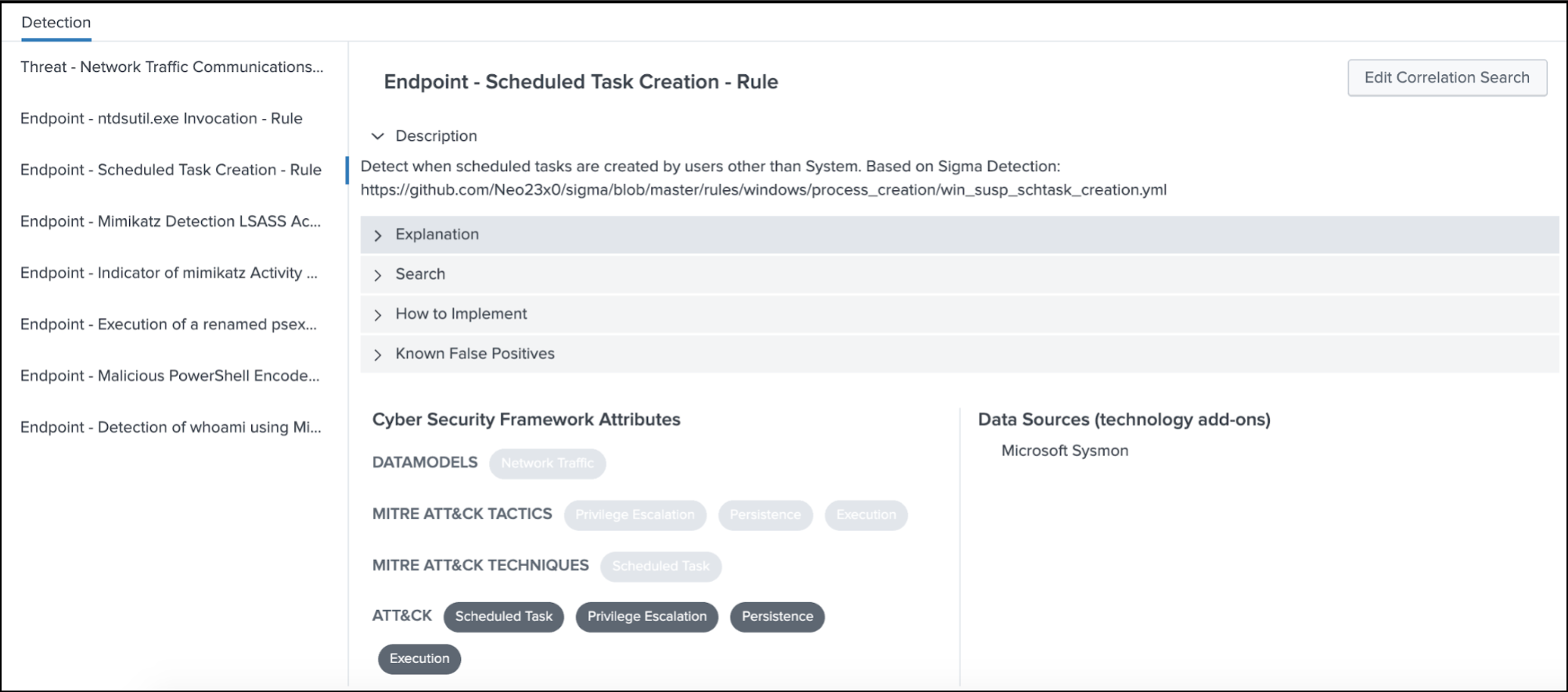 For each search, additional context can be provided to help the user better understand what the search is intended to find, provide a view into the search itself, as well as gain any additional guidance around how to implement it or if there are known false positives.
For each search, additional context can be provided to help the user better understand what the search is intended to find, provide a view into the search itself, as well as gain any additional guidance around how to implement it or if there are known false positives.
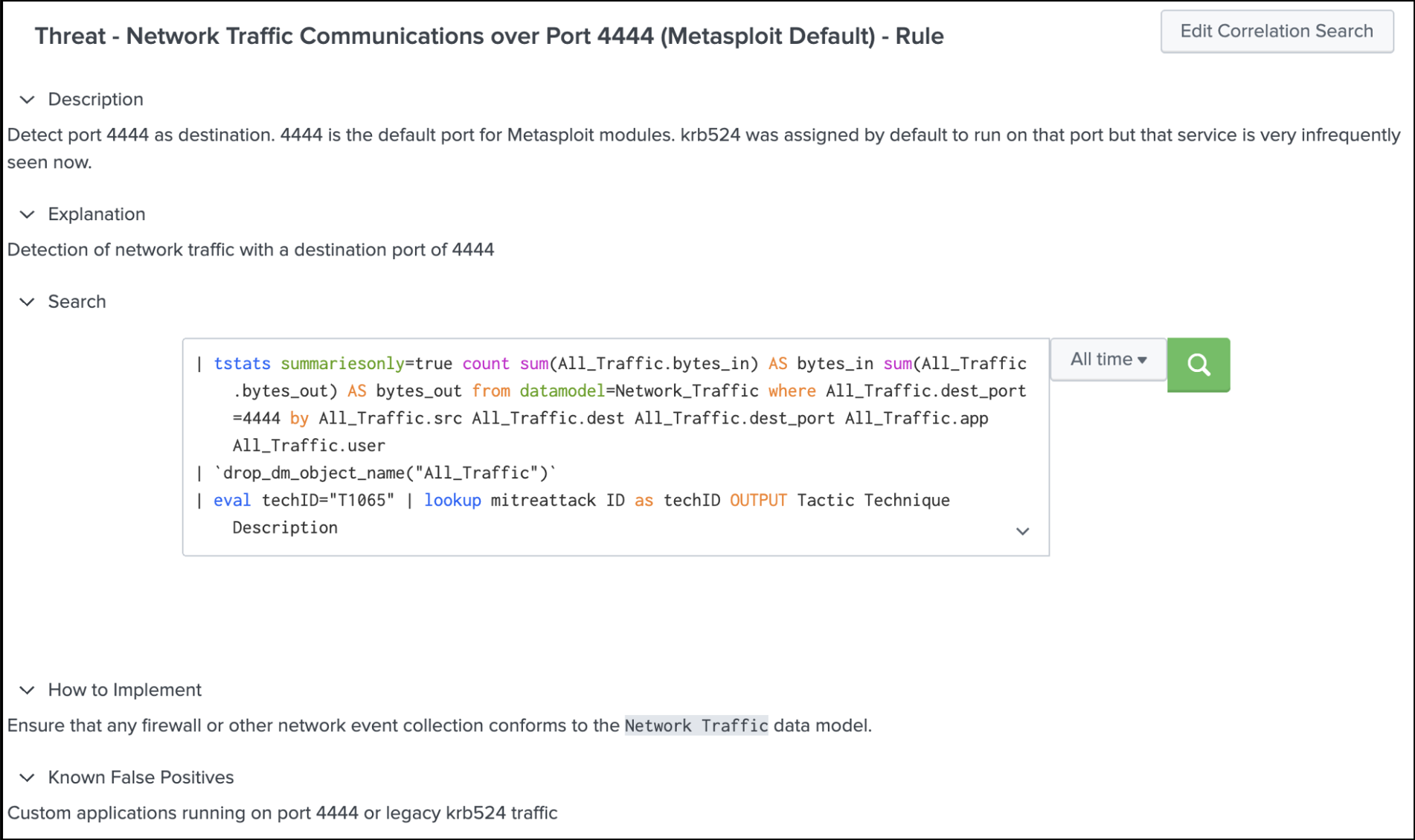 As we look at this specific detection search, we can see that this search leverages the Network Traffic data model and is called out as an important component of implementation. If you are not running this data model, the search will fail, which may seem obvious but it is important to call out, when sharing content with others. Also note that users with sufficient rights can edit both the analytic story and the correlation searches that are part of the story and just like every other modification, these get written to the local directory of the app that the use case and correlation search belong to, so you can revert back to the content in the default directory if required as well as not step on your modifications if the underlying app gets updated.
As we look at this specific detection search, we can see that this search leverages the Network Traffic data model and is called out as an important component of implementation. If you are not running this data model, the search will fail, which may seem obvious but it is important to call out, when sharing content with others. Also note that users with sufficient rights can edit both the analytic story and the correlation searches that are part of the story and just like every other modification, these get written to the local directory of the app that the use case and correlation search belong to, so you can revert back to the content in the default directory if required as well as not step on your modifications if the underlying app gets updated.
Sterling, I hope this provides some food for thought on how you can take all of the great content that you have created and organize it based on the use cases you are most focused on. Remember, make sure you document your searches and if you are mapping to data models, frameworks or specific sourcetypes, call those things out so that when specific searches are being considered for deployment, these things can be considered prior to moving something to production. Doing these things will help you free up time to enjoy a coconut chip cone at the Creamery while others review your content!
Until Next Time,
Buttercup
----------------------------------------------------
Thanks!
John Stoner
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




