What’s New in Splunk AppInspect?

It might be a bit hard to spell out which product or solution is the best inspection software in the market. However, if you are a Splunk developer, partner or customer, you can’t miss Splunk AppInspect, which evaluates your Splunk app against a set of Splunk-defined criteria so that you can be assured of its quality and robustness.
As part of the evolving journey for Splunk AppInspect, I am so pleased to announce the general availability of the April 2019 AppInspect release, which consists of two updated AppInspect interfaces:
AppInspect CLI 1.7.0
- Accelerates the automation of Python code inspection as a repeatable and proven way to assure optimized performance as well as lower risks. It should also further increase the Splunk app vetting efficiency and improve its quality.
- Detects the use of deprecated or removed Splunk features in apps. It not only raises app developers‘ awareness that deprecated or removed Splunk features are being used in their apps, but also articulates any replacement Splunk features if exist so that app developers can update their apps to achieve required compliance.
AppInspect API 2019.04
- Is now decoupled from AppInspect CLI (an on-premises version) and going forward we will update the API more frequently than the CLI.
- Includes several improvements, e.g. better handling of repeated API requests, integration with Google Safe Browsing API service, etc.
With that, let’s deep dive into the feature details.
AppInspect CLI 1.7.0
Python Automation
As we all know, the Python programming language is quite flexible so automatically inspecting Python code against a set of predefined security and quality criteria is not an easy task. Hence, our deliberate design for the Python Automation solution, which aims to automate Python code inspection, consists of both “Python Check” and “Python Analyzer”, as illustrated below.
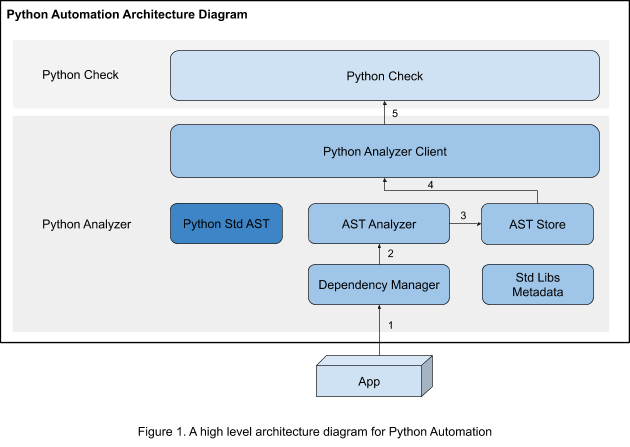
At the top layer, “Python Check” is where all Python checks are managed and executed. These Python checks inspect code against relevant security and quality criteria such as file-system manipulation, insecure HTTP connection, thread security, etc.
Underneath, the layer for “Python Analyzer” feeds required app information to “Python Check”, and it contains the following parts:
- Python Standard AST: An official Python Standard AST module, which is a powerful tool to parse Python code.
- AST Analyzer: On top of Python Standard AST, a specific AST analyzer is built up to fit for use of Python code analysis.
- Dependency Manager: It analyzes the dependency affiliation of Python files, which facilitates searching sensitive code patterns across files.
- AST Store & Standard Libs Metadata: Utilities for Python code analysis.
- Python Analyzer Client: An interface between “Python Analyzer” and “Python Check”.
Let’s take an example of Splunk DB Connect, and figure out how the Python Automation solution automatically inspects Python code during the app vetting process, as illustrated in the Figure above.
- All Python files in the app first enter Dependency Manager to analyze dependency relationships among the files/modules.
- Then, AST Analyzer analyzes the Python files in a topological order, namely, independent files are processed first and then dependent files come later.
- The analysis result from the step above is saved into AST Store.
- AST Store further delivers the analysis result to Python Analyzer Client.
- Finally, Python Check uses the analysis result to perform automated inspection, some important checks are listed as follows and check descriptions can be found out at AppInspect check criteria.
- check_built_in_function
- check_built_in_import_function
- check_for_udp_network_communications
- check_for_unencrypted_network_communications
- check_for_plain_text_credentials_in_python
Checks for deprecated/removed Splunk features
Besides the Python Automation solution, we have added quite a few new AppInspect checks to detect the use of deprecated or removed Splunk features in apps, which facilitates evaluating Splunk version compatibility. Some typical checks implemented in this release are listed below, and a full list of checks can be found out at AppInspect check criteria.
- Add a check for eventtype auto-discovering, which is deprecated in Splunk 5.0.
- Add a check for static/app-packages endpoint usage, which is deprecated in Splunk 6.6.
- Add a check for literals.conf, which is deprecated in Splunk 7.2.
AppInspect API 2019.04
In addition to the app inspection functionality provided by AppInspect CLI, the AppInspect API service further extends the inspection coverage for security check and app run-time validation. It is highly recommended to use AppInspect API to evaluate app quality when connected to the Internet. In this release, two typical features have been delivered as follows, and more information is documented at What's new in Splunk AppInspect API.
Request Deduplication
Previously, the AppInspect API service scheduled an app inspection task for each submitted request. In the latest release, with the Request Deduplication feature available, when a duplicate request is submitted, the user doesn’t need to wait for extra processing time but can quickly fetch a recent valid AppInspect report if it exists. The criteria for request deduplication is based on several factors, e.g. submitter identity, app package digest, validation tags and an interval threshold (by default 60 minutes). This feature also optimizes the service performance for AppInspect API.
Google Safe Browsing Service Integration
Using the previous AppInspect API, Splunk app reviewers had to manually identify suspicious or malicious URLs specified in apps and then assess the risk. Now, this manual process has been simplified and automated by leveraging Google Safe Browsing, which constantly updates and maintains the unsafe web resources, including social engineering sites (e.g. phishing and deceptive sites) and sites that host malware or unwanted software.
Conclusion
I hope you are excited to learn about the features and improvements we have implemented for AppInspect CLI 1.7.0 and AppInspect API 2019.04. Visit the Overview of Splunk AppInspect website, share your feedback at the public AppInspect slack channel, and take advantage of AppInspect to improve your app quality!
P.S. I want to take this chance to extend my sincere appreciation to my colleagues listed below, who provided technical information in this blog
- Shen Han, AppInspect software engineer
- Roman Li, AppInspect software engineer
----------------------------------------------------
Thanks!
Leo Chen
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




