Splunk Security Essentials 3.1: Enhanced MITRE ATT&CK Matrix: Find the Content that Matters the Most to You, Faster
One of the great things about developing for Splunk Security Essentials is that most of the features and capabilities are requested from customers and the security community. If you don’t know what Splunk Security Essentials is, head over to this blog post that explains the app in detail: "Using Security Essentials 2.4: Analytics Advisor." Go ahead, read it, we’ll wait…
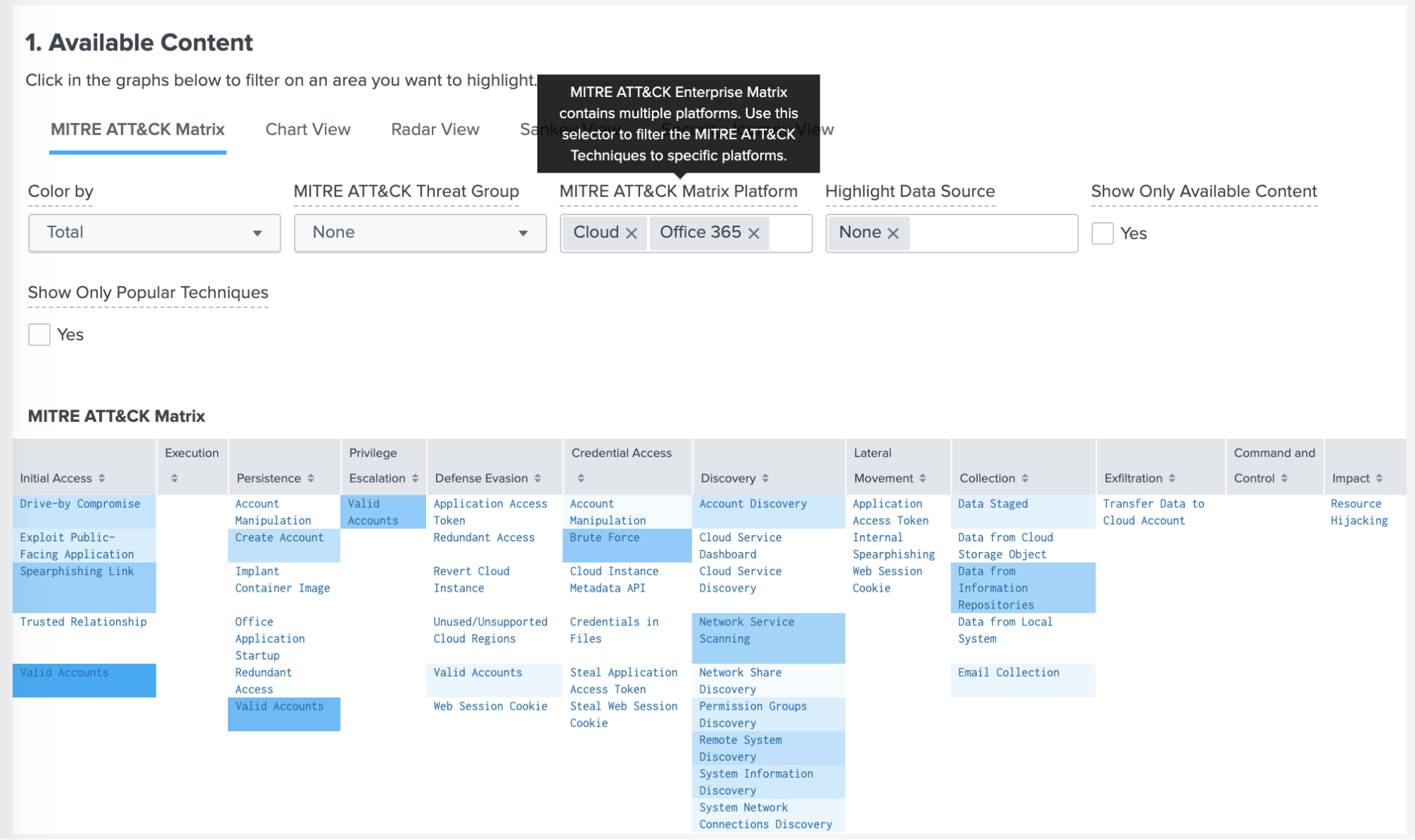
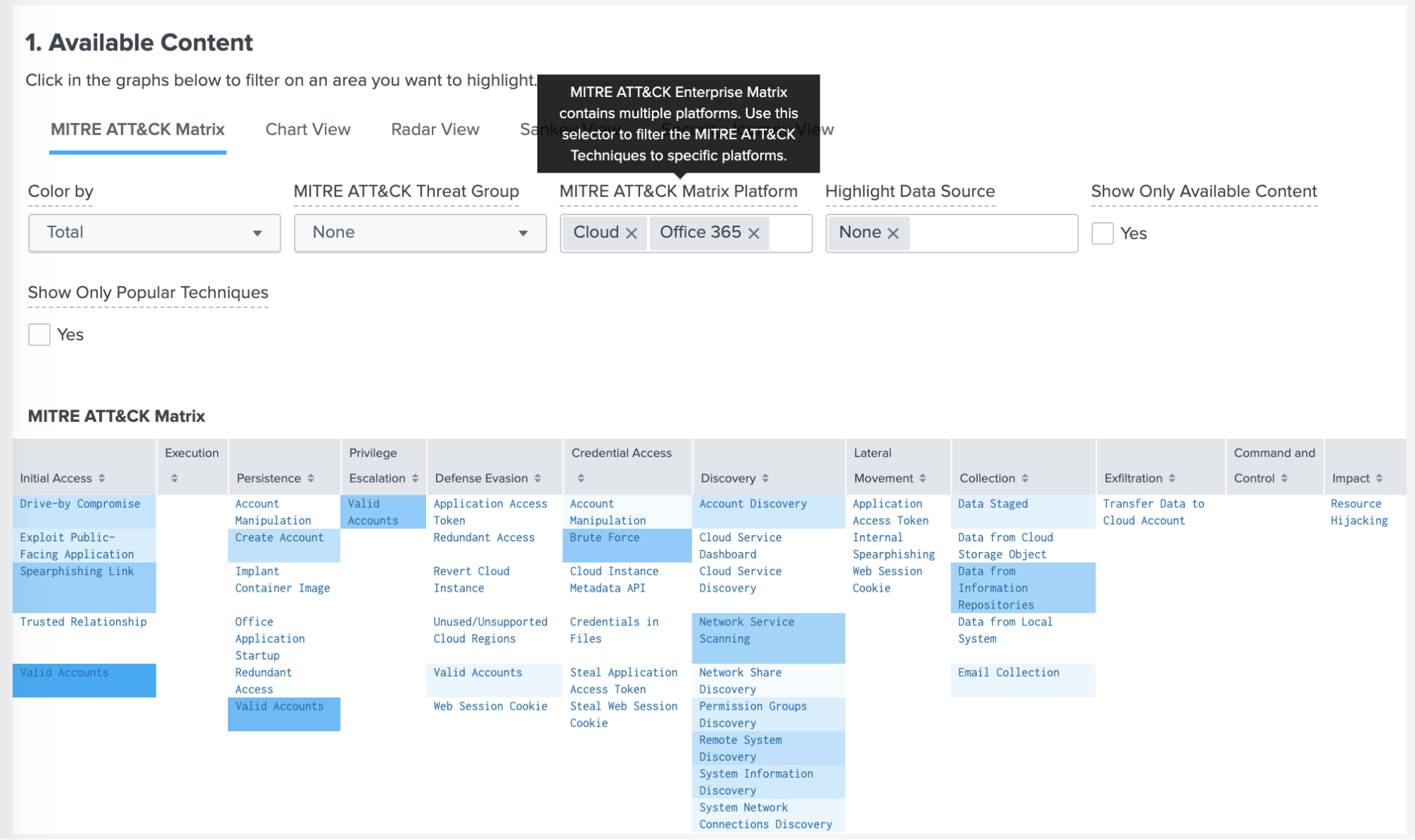
In this latest release (3.1), we added a feature that has been requested frequently: the ability to filter the ATT&CK Matrix for Cloud and SaaS Techniques. The MITRE ATT&CK Framework consists of multiple matrices such as Enterprise, Mobile, and ICS. The biggest matrix is Enterprise, which is subdivided further into smaller groupings such as Windows, Linux, AWS, Cloud, Saas, Office365, etc.
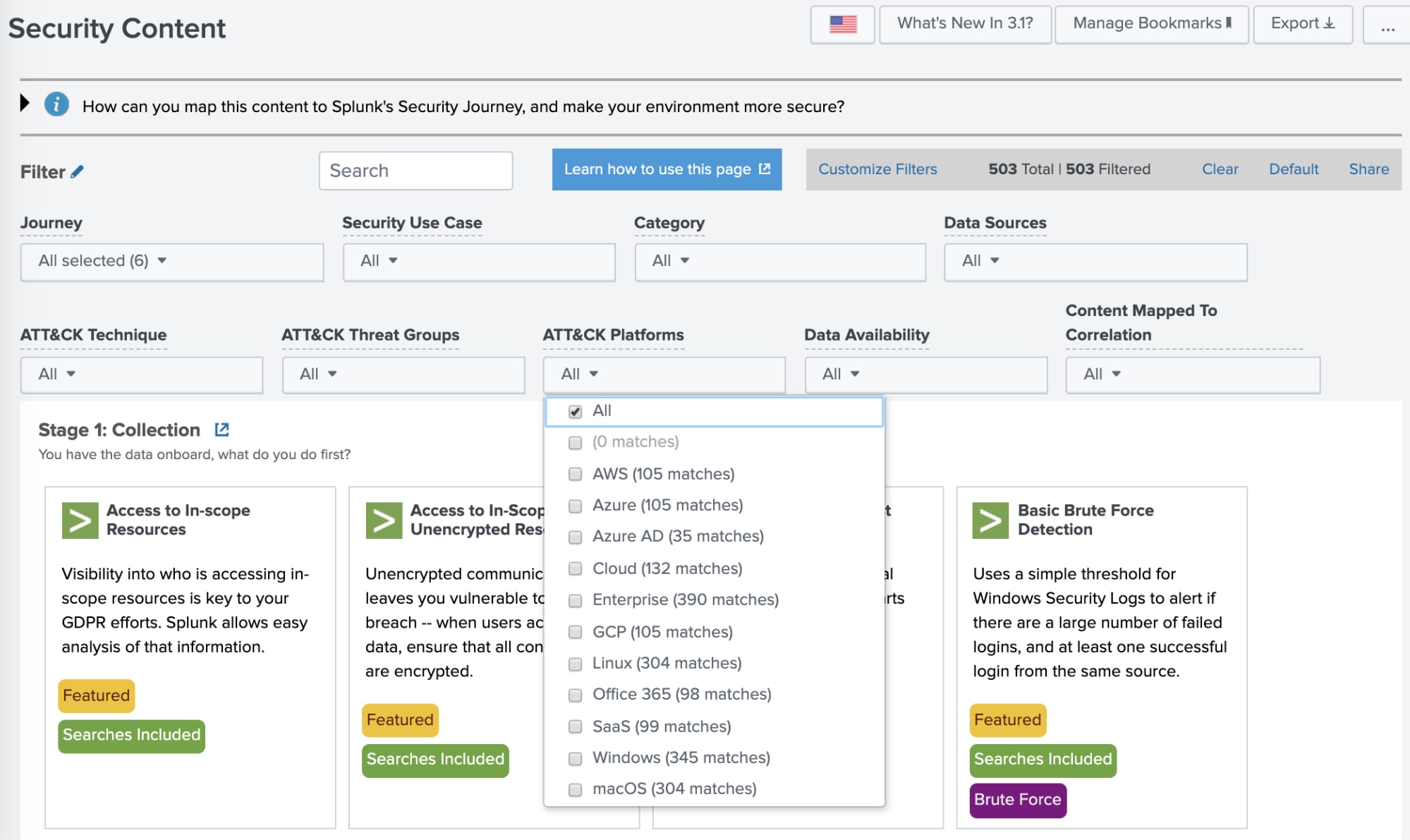
In previous versions of SSE, we only supported the main Enterprise Matrix. This new release, we are happy to announce that you can now subdivide your MITRE ATT&CK Matrix against any of the sub-matrices. This new capability allows you to determine your coverage against ATT&CK Techniques associated with GCP or AWS or any of the other matrix groupings that exist in the framework. Similarly, you can quickly find detections in the SSE repository that map to Office365.
This new capability is located via a filter in the “Security Content” dashboard called ATT&CK Platforms.
The same filter is available on the “Analytics Advisor — MITRE ATT&CK Framework” dashboard and will narrow down the matrix to only techniques associated with the platform you select.
This dashboard contains an often missed feature of SSE that I would like to highlight.
One of the criticisms I hear about the ATT&CK Framework is that the techniques don’t have any weighting. They are all treated as equals. But every day, we all make decisions around techniques to focus on based upon an intuition or some other factor. Ideally, we would choose the techniques that pose the greatest amount of risk to our organization. But how do you know which techniques are associated with the highest risk?
The SSE team here at Splunk have hypothesized that one way to quantify the “riskiness” of a technique is to determine how many Threat Groups are known to be using it. If a technique is popular, i.e. used by many Threat Groups, it is very likely that it works well for the attackers and is likely to have been shaped into a ready-to-use exploit that has been productized and distributed in one of the many attack libraries and Linux distributions. Once an exploit has reached this state, the barrier to entry is extremely low and the risk to your organization is much greater of a particular technique to be utilized.
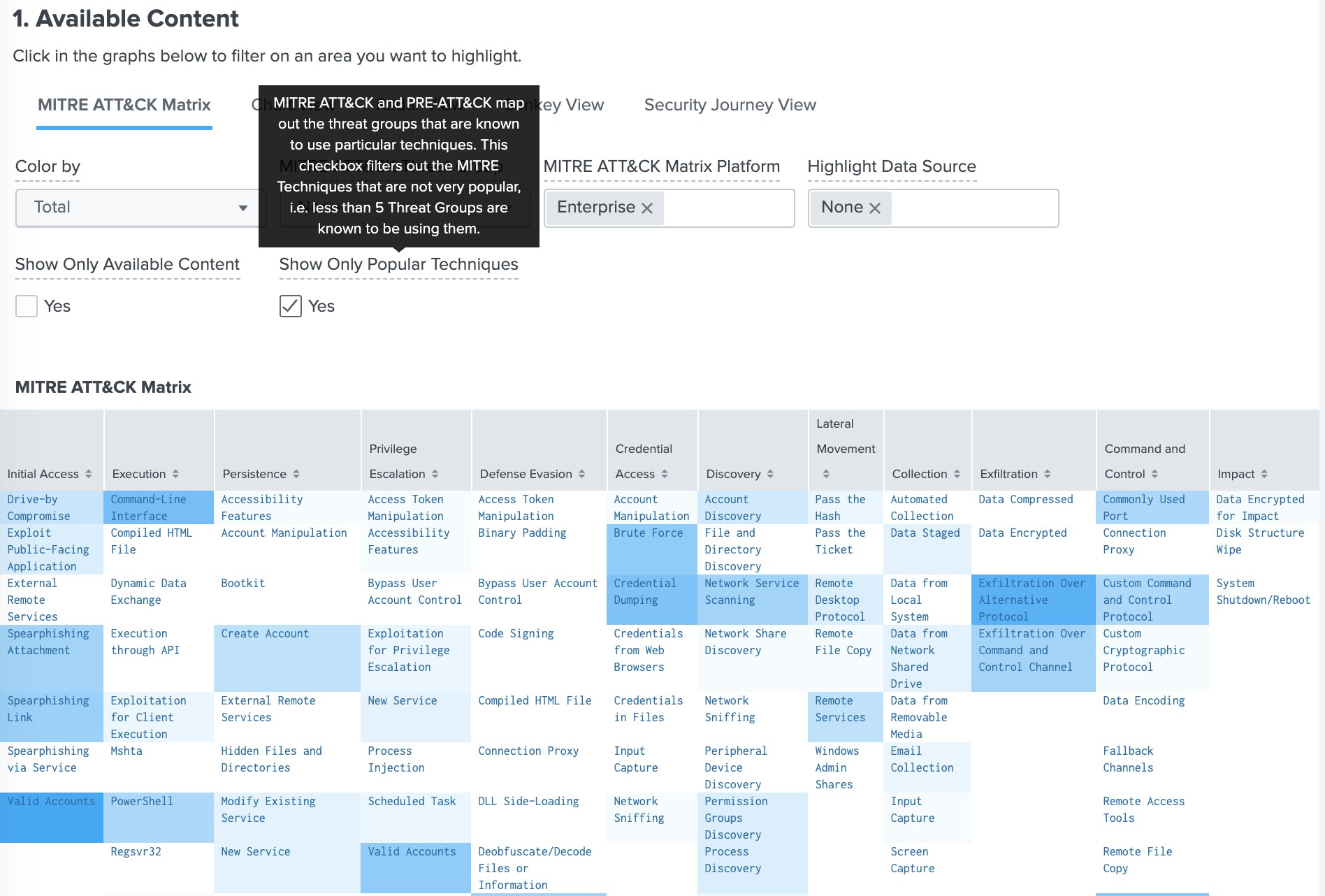
In this screenshot, we have ticked the checkbox “Show Only Popular Techniques.” This filters the ATT&CK Matrix to display the techniques that 5 or more Threat Groups are associated with. This is a good way of finding the techniques that pose the greatest risk. Minimally this method will provide a great “bang for your buck” for reviewing where to build your defenses especially if you don’t know where to start.
For full details on this exciting new release, head over to the Splunk Security Essentials page on Splunkbase and grab the latest version.
Happy Splunking!
Related Articles
About Splunk
The Splunk platform removes the barriers between data and action, empowering observability, IT and security teams to ensure their organizations are secure, resilient and innovative.
Founded in 2003, Splunk is a global company — with over 7,500 employees, Splunkers have received over 1,020 patents to date and availability in 21 regions around the world — and offers an open, extensible data platform that supports shared data across any environment so that all teams in an organization can get end-to-end visibility, with context, for every interaction and business process. Build a strong data foundation with Splunk.




